The Internet of Things is coming….to a highway sign near you? In the latest reminder that much of our nation’s “critical infrastructure” is held together with the Internet equivalent of spit and glue, authorities in several U.S. states are reporting that a hacker has once again broken into and defaced electronic road signs over highways in several U.S. states.
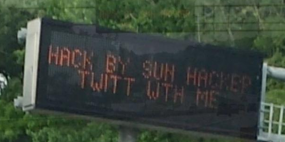
Earlier this week, news media in North Carolina reported that at least three highway signs there had apparently been compromised and re-worded to read “Hack by Sun Hacker.” Similar incidents were reported between May 27 and June 2, 2014 in two other states, which spotted variations on that message left by the perpetrator, (including an invitation to chat with him on Twitter).
The attack was reminiscent of a series of incidents beginning two years ago in which various electronic message signs were changed to read “Warning, Zombies Ahead”.
While at least those attacks were chuckle-worthy, messing with traffic signs is no laughing matter: As a report by the Multi-State Information Sharing and Analysis Center (MS-ISAC) points out, changes to road signs create a public safety issue because instead of directing drivers through road hazards, they often result in drivers slowing or stopping to view the signs or take pictures.
That same MS-ISAC notice, obtained by KrebsOnSecurity and published here (PDF), points out that these incidents appear to be encouraged by sloppy security on the part of those responsible for maintaining these signs.
“Investigators in one state believe the compromise may be in part due to the use of weak Simple Network Management Protocol (SNMP) community strings. Investigators in another state believe the malicious actor used Telnet port 23 and a simple password cracker to gain remote access. In one state the malicious actor changed the modem passwords, forcing technicians to restore to factory default settings to regain access.”
That report goes on to profile the attacker as “a Saudi Arabian actor who is also responsible for several SQL injection compromises of databases in foreign countries over the past several years and has demonstrated an interest in the ‘Internet of Things’ by posting compromises/instructions on compromising light bulbs and car radios, in addition to the road signs.” Government reports like this one have a tendency to make these guys sound a lot scarier and skilled than they really are: Near as I can tell, Sun Hacker is an unremarkble script kiddie who enjoys defacing Web sites.
In a portion of the report that is sure to set off video game enthusiasts who tire of their favorite medium being blamed for many of society’s ills, the MS-ISAC report states that the activity last week …
“…likely coincides with the May 27, 2014 release of the video game ‘Watch Dogs,’ in which game play revolves around ‘hacking,’ with a focus on hacking critical infrastructure-based electronic devices in particular. Watch Dogs allows players to hack electronic road signs, closed-circuit television cameras (CCTVs), street lights, cell phones and other systems. On May 27, 2014, the malicious actor posted an image of the game on his Twitter feed, demonstrating his interest in the game, and the compromise of road signs occurs during game play. CIS believes it is likely that a small percentage of Watch Dog players will experiment with compromising computers and electronic systems outside of game play, and that this activity will likely affect SSLT [state, local, tribal and territorial] government systems and Department of Transportation (DOT) systems in particular.”
We see a great deal of hand-waving and public discussion about the possibility that foreign cyber attackers may one day use vulnerabilities in our critical infrastructure to cause widespread problems in the United States. But my bet is that if this ever happens in a way that causes death and/or significant destruction, it will not be the result of a carefully-planned and executed cyber warfare manifesto, but rather the work of some moderately skilled and bored cracker who discovered that he could do it.





Well it is North Carolina. They just rewrote a law on Fracking chemical composition disclosure so health workers and first responders will not be changed with a federal crime if they disclose the chemicals involved. It reminds me of the water contamination in that state.
http://www.publichealth.va.gov/exposures/camp-lejeune/
Really nothing to do with hacking interstate bill boards in the state unless they are going to try and hack the Fracking formula.
FARO – So your ignorance turns it political. Grow up son.
Seriously? People hacking signs is as old as dirt. I can remember stories from people doing it to IR programmed signs in subway stations, and then there’s the older highway signs which could be wardialed, and then there’s the more modern signs which also use the default password.
If anything, it’s a case of laziness for not securing a machine.
I understand what you are saying and it probably is a kid’s prank. I have been reading up on this Anonymous hacking group, a loose confederation of hackers who attack specific targets. The group appears to not be a strong as they have been but they would go after a company if they had an agenda. When I first came to this board a guy named anonymous made some derogatory comment to my first post. He seemed to imply by visiting the site he could capture my IP address. So if you are listening, I hope you have a nice day.
Yes, we are.
I am not disappointed by your comment
“He seemed to imply by visiting the site he could capture my IP address.”
Watch out if they do = they’ll use the super powerful Low Orbit Ion Cannon. That is if the particular amomymoose can figure out how to use it.
Low … orbit … ion cannon? That sounds dangerous. :/
If the drivers are an actual hazard (more than they usually are) with distracting signs causing additional traffic chaos, you could desensitise drivers to the ‘funny’ sign messages by using a lot more ‘funny’ sign messages. The playful hacker may lose interest without the special attention they are probably after as payoff. And throw in some adds for revenue and extra ‘ignore me’ factor. It could actually be that the signs serve no real positive purpose at all, just some misguided public servants ‘good idea’ that ‘isn’t’ and just adds distraction and traffic chaos. Could be a point to re-look at the underlying research basis for these signs instead of whipping the system admins for doing something fundamentally the norm for the whole history of IT in providing a system that meets the defined business requirement (at a guess which excluded any consideration of security).
Omg really!?, this has been going on long before watch dogs even came out. In fact there are articles online everywhere about DOT machinery having the same credentials used by utility workers every day. This is retarded accusations by made by security analysts who haven’t made their part in publications because they are too ignorant to come up with something plausible.
You really simlpy cannot blame video games on these kind of things. Films, and novels maybe, but in video games they satisfy an urge they do not GIVE you one 🙂 for example my favorite game series is Harvest Moon, a farming simulator. I do not run outside to start working on my yard after xD. If I read a book or article on farming on other hand I may be tempted to farm or like I said, satisfy the urge by playing Harvest Moon.
wow such hack very criminal
“Near as I can tell, Sun Hacker is an unremarkble script kiddie who enjoys defacing Web sites.”
Yet you’re writing about him. Why don’t guys like you have a term for the people who get hacked? Because after all, if he’s some no talent, dummy, then what does that make the other guys? He’s a teenager doing this in his spare time. A guy like you, is employed to stop it and usual at a large salary.
I keep pressing the “X” button on my phone to hack gas pipes and traffic signals but it’s not working.
Do I need a PS3 cellphone or something?
You have to use a jailbroken iPod touch. Make sure to install the terminal app.
By showing how easy it is to hack those signs at least Sun Hacker gets the authorities attention, so that maybe they will fix these ridiculous security holes that they have allowed. You could almost describe it as a public service. It surely gets their attention better than if he had sent an email complaint telling the state DOT’s that they are idiots for making it so easy to hack. They would not have paid attention to his email. Embarrassing them in front of the public usually gets the quickest action.
@Aztec – I agree with the statement that this will at least bring it to the DOT’s attention, but it’s not fair to too assume that the “DOT’s are idiots for making it so easy to hack”. In this case, chances are the over head VMS is owned by the DOT but was probably installed by a contractor, maintained by a contractor, and possible operated by a contractor. In the case of the portable VMS units often seen in construction zones, the MAJORITY of those are NOT owned by DOT but are owned (or leased) by contractors. HOWEVER, this is not an excuse for the lack of security that allows such a breach to happen but it is not fair to blanket all DOT’s as “idiots”.
respectfully submitted,
a DOT network engineer ( different state though).
Not wishing to call anyone an idiot, but if you are contracting out services and systems, you really ought to make sure the SLA with the contractor includes looking after stuff appropriately (like securing electronic road signs so they don’t get hacked).
Otherwise, you risk losing control of it, and that would be idiotic.
@ Matt – you are absolutely correct!!! Unfortunately network engineers don’t get to review or have a say in most of these half billion dollar contracts. The guys that are making the money are only worried about getting the project done on time or early ( for bonuses). WE are trying all we can to make it happen though.
Coverage of events like this help with the cause!!