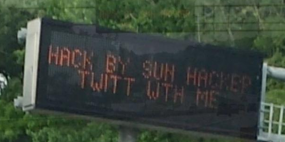
The Internet of Things is coming….to a highway sign near you? In the latest reminder that much of our nation’s “critical infrastructure” is held together with the Internet equivalent of spit and glue, authorities in several U.S. states are reporting that a hacker has once again broken into and defaced electronic road signs over highways in several U.S. states.
Earlier this week, news media in North Carolina reported that at least three highway signs there had apparently been compromised and re-worded to read “Hack by Sun Hacker.” Similar incidents were reported between May 27 and June 2, 2014 in two other states, which spotted variations on that message left by the perpetrator, (including an invitation to chat with him on Twitter).
The attack was reminiscent of a series of incidents beginning two years ago in which various electronic message signs were changed to read “Warning, Zombies Ahead”.
While at least those attacks were chuckle-worthy, messing with traffic signs is no laughing matter: As a report by the Multi-State Information Sharing and Analysis Center (MS-ISAC) points out, changes to road signs create a public safety issue because instead of directing drivers through road hazards, they often result in drivers slowing or stopping to view the signs or take pictures.
That same MS-ISAC notice, obtained by KrebsOnSecurity and published here (PDF), points out that these incidents appear to be encouraged by sloppy security on the part of those responsible for maintaining these signs.
“Investigators in one state believe the compromise may be in part due to the use of weak Simple Network Management Protocol (SNMP) community strings. Investigators in another state believe the malicious actor used Telnet port 23 and a simple password cracker to gain remote access. In one state the malicious actor changed the modem passwords, forcing technicians to restore to factory default settings to regain access.”
That report goes on to profile the attacker as “a Saudi Arabian actor who is also responsible for several SQL injection compromises of databases in foreign countries over the past several years and has demonstrated an interest in the ‘Internet of Things’ by posting compromises/instructions on compromising light bulbs and car radios, in addition to the road signs.” Government reports like this one have a tendency to make these guys sound a lot scarier and skilled than they really are: Near as I can tell, Sun Hacker is an unremarkble script kiddie who enjoys defacing Web sites.
In a portion of the report that is sure to set off video game enthusiasts who tire of their favorite medium being blamed for many of society’s ills, the MS-ISAC report states that the activity last week …
“…likely coincides with the May 27, 2014 release of the video game ‘Watch Dogs,’ in which game play revolves around ‘hacking,’ with a focus on hacking critical infrastructure-based electronic devices in particular. Watch Dogs allows players to hack electronic road signs, closed-circuit television cameras (CCTVs), street lights, cell phones and other systems. On May 27, 2014, the malicious actor posted an image of the game on his Twitter feed, demonstrating his interest in the game, and the compromise of road signs occurs during game play. CIS believes it is likely that a small percentage of Watch Dog players will experiment with compromising computers and electronic systems outside of game play, and that this activity will likely affect SSLT [state, local, tribal and territorial] government systems and Department of Transportation (DOT) systems in particular.”
We see a great deal of hand-waving and public discussion about the possibility that foreign cyber attackers may one day use vulnerabilities in our critical infrastructure to cause widespread problems in the United States. But my bet is that if this ever happens in a way that causes death and/or significant destruction, it will not be the result of a carefully-planned and executed cyber warfare manifesto, but rather the work of some moderately skilled and bored cracker who discovered that he could do it.





“instead of directing drivers through road hazards, they often result in drivers slowing or stopping to view the signs or take pictures.”
Not sure how we can blame a script kiddie for that unless photos are being put on there. (I’m thinking breaking into digital company signs, the fancy color ones.) It doesn’t take much to distract drivers.
Yeah, and god forbid we slow some drivers down…
You’re unjustly trivializing the number of drivers affected and the effects of the slowdowns. If the increased carbon emissions and fuel consumption don’t concern you, at least have a little sympathy for those who have long commutes and feel increased stress when traffic slows down considerably.
In pretty much every congested mess, it was some slow driving causing an impediment to dozens of cars around them that lead to traffic and accidents. Cars going a good speed and getting clear of that intersection aren’t there to bog it down 5 minutes later are they?
You are now aware that a car traveling 15 miles an hour slower than the rest of the traffic on a highway is more likely to get hit than a car traveling the same speed as all other cars, even if all the other cars are speeding.
A car randomly slowing down to a crawl with a severely distracted driver at the wheel (fishing around for their phone so they can then take a picture) is a recipe for an accident.
Stop paying attention to your speedometer, start paying attention to the cars around you.
Those road signs must connect to the internet via a secure WIFI network or a 3/4G network
I know the F.P.L electric meters in central Florida are monitored every fifteen minutes through the 3/4G cellular networks. I often wonder how secure the power companies network is and at any time some hacker in another country could shut of the power to many neighborhoods or even entire cities
skileld than they really are, ….. skilled
Just editing
As one who has an hour commute one way… I can confirm it does not take much to distract drivers…
Hence why companies are now using electronic signage for advertising purposes on major routes.
They don’t care if the distraction causes an accident, as long as their product remains in your subconscious.
Hopefully this is (another) wake up call to address the security of these and other devices/infrastructure.
Telnet? SNMP? Seriously, when are infrastructure owners going to start applying the most basic controls to the ‘things’ on the Internet? The days of taking ‘things’ out of the box an just plugging them in is over. Every single ‘thing’ that you put on network now has to be hardened, because every other ‘thing’ is a potential attack platform. Ohhh…the humanity of it all.
Totally agree. Basic security safeguards – these need to be standards that the state governments require from their vendors to build to and from their deployment folks configure to.
re: “Seriously, when are infrastructure owners going to start applying the most basic controls to the ‘things’ on the Internet? ”
When they start hiring security people. Most of these government agencies have squat for a IT security budget. You can blame that on those people who refuse to understand MMT.
Infrastructure Owners will only start to secure these devices when it is economically unsound to not do so. (Yes, I am aware of the double-negative.)
Organisations will spend the time, effort & cost to secure these devices IF (and only if) leaving these devices unsecured has a specific (and significant) cost.
The costs to secure the devices must be less than the costs to leave them insecure (the free market model requires this).
The costs to secure these devices should not be underestimated. They include costs to:
– change tendering & procurement guidelines
– re-write process & implementation guides
– implement testing and auditing systems
– train operators, implementers & support staff
– operate & maintain credential repositories
– secure, audit, test & monitor credential repositories
The Industrial & Process control sectors (particularly energy & health) have been working their way through those steps for the last few years. Even in health, finance & energy, where the costs are quite evident, the level of engagement with these basic security controls varies widely.
Costs related to Exploitation of Security vulnerabilities is a lagging cost – usually lagging by several years. Thus they are NOT (and can not be) captured in the implementation project costs, risks and learning registers.
They are operating costs, not implementation costs – therefore security (if any) is retrofitted (at substantially higher expense), not design-fitted.
This also explains why the government investigators always try to make the attacker out to be some foreign super hacker rather than a bored teenager. The cost of implementing any kind of security after the fact is expensive (it’s so much cheaper to just build a relatively secure system in the first place). They try to gloss over how many holes there are in their security by making the script kiddie sound like a badass who could crack any lock without a key. That way it doesn’t make them seem negligent, and when things really do get bad enough that they have to take action, they can lobby for entirely new agencies (DHS, TSA) with massive budgets and a mostly useless crop of employees whose authority is so overwhelming that no one can question them.
It’s a perfect storm of existing government employees seeking to avoid blame while expensive security consultants (and future agency directors) are looking for bullet-proof pork projects. Combine that with clueless legislators who just want to look like they’re “doing something”, and then stir in a couple bored teenagers whose youthful rebellion plays right into the hands of the people they think they’re rebelling against. In a few years, we’ll have a new arm of DHS tasked specifically with protecting “digital infrastructure” (not referring to actual network infrastructure, but digital signs, public announcement systems and street lights essentially) that spends most of its time harassing anybody who uses a terminal window on a laptop in public because “they matched the profile of a hacker. And… uhhh… I think I saw that traffic signal flicker for a second.”
“Take your shoes off!” they’ll scream at passersby anytime a street light burns out.
That free market stuff sounds great…yet there are a few holes in the theory.
first,there never has been, isn’t, and never be a free market, in anything. a free market is an abstract construct where there is a seller, a buyer, no speculator, and no regulations. neither buyer or seller is compelled to enter the market. i hear a lot of talk about free market this, and free market that, but i suspect few people know what they are talking about.
however, given that one could have the fantasy free market, the economic lag time between action and consequence would create arbitrage; a business takes risk and profit now, and when it’s time to pay up, just closes up shop, ending that game. this points out a second falicy of those that often talk about ‘free market’ this or that, namely that unless the participants are forced to continue to ‘play’, there will always be temporal speculation. inthis case a company speculates that thet won’t get hacked, and while their gamble is ‘winning’ they take money off the table, but when they lose, they disengage from the ‘market’ and leave society and the remaining participants holding the bag.
as concrete example, target executives, have now retired rich, while grandma still has to deal with their gamble with her data.
so free market is great in some ideal abstract, indeed the very term stirs up emotions and pride of self sufficiency , independence, and greatness. the reality, is the big money cleans up and leaves grandma holding the bag when it comes time to pay up. and if there is a nonzero chance of a breach, an infinite time horizon makes the probability equal to certainty. the question, is how long can they gamble with grandma’s data before they lose it. how much can be taken off the table before that event?
given we get a free market generational ‘reset’, the cycle of exploitation via gambling with other people’s data repeats. it doesn’t, as one would hope, become extinct. true, the target execs are done gambling, but they are simply replaced with a fresh set. that’s not what the fancy free market talkers envision, is it? a constant cycle of exploitation?
i suspect the internet generation’s love affair with mechanistic darwinism as economic theory is driven by assumptions such as discounting lag times as well as confusing correlation and causation. yet the reasons why so many have such seriously flawed thinking is beyond the scope of my post, so i’ll leave it there.
on a positive note, requiring a company to carry insurance based on how many people’s lives they put at risk may address some of the moral hazard and place some downward pressure on the infinite scaling, infinite time horizon gambles that are going on. sadly however there is little appetite to avoid a big data crash despite having opportunity to learn from the similar housing crash that we are still recovering from. oh well…i suppose we will hear about, how nobody could have known, or it was unavoidable, or we will do x,y,z and we have it figured out this time..etc.
or maybe even more talk about how if we only had a free market. if someone ever finds such a mythical beast, i would love to hear about it.
good luck.
to add to my already long rant, the choice to protect systems is entity centric. it’s based on harm to the entity that holds the data, not the harm to others. thus data is valued as worthless when stolen, yet billions when kept. eg. we hear how fb and google data is so valuable, but when it’s stolen then we will hear how worthless it is.
the valuation of systems and data is faulty, a dual monetization value, and legal liability value. unfortunately, the two are not even close, so it’s not a surprise to see the kinds of choices being made.
Remember the early days of the net included a cam of a coffee pot at Cambridge, a simple greyscale image so you could see if it held coffee. Big Bang Theory made fun of stuff like this by putting a bunch of robots cars with webcams on the web. Look I can make it move!
I believe – professionally believe – that Brian is dead-on right about all this. The worst hits are going to come from the bored “kid” fooling around for entertainment, not state directed action.
Like I said back in the ATM malware thread: These folks do what they do because they *like* doing it. It actually short-sells things to say that they merely “get a kick” out of what they do, and that’s because they really feel that “hacking” (password cracking, systems intrusions, etc.) a part of who they are and how they go about their lives. It’s literally part of many of these persons’ identity. And because of that, the aggregate effect is a constant probing and analysis of any system out there for vulnerabilities they can exploit. Even if it’s just to prank drivers about zombies.
Remember: Many years back some magazine (“2600: The Hacker Quarterly”, I think…) talked about some guys hacking the timer on exercise businesses treadmills so as to allow for more time *just for the heck of it*. It wasn’t like those guys were so athletic themselves they were looking to extend workouts. No, it was just the challenge, however simple, of compromising yet another system people wouldn’t ever think in terms of being “hackable”. And therein lies the problem: They’re the ones thinking “How can I get into this system”. And finding them. I’m waiting for the day when the parking garage’s ticket system gives me a fortune cookie printout instead of a ticket just because these guys exist. And that would be a great prank that’s right up their alley.
Brian is totally right. It’s not the state actors who’ll really screw up our infrastructure. It may be the criminal gang, but I think they’d rather put their effort elsewhere. It will end up being the bored 20-something fooling around who’ll find a way into something we never thought about before. And it’ll only be in hindsight that everyone will say “Why wasn’t that protected?”
Bored 20-something if we’re lucky. It’ll probably be a bored teenager. “It can’t happen to me” is their mantra, and I say this as someone who remembers all too well what I did as one.
Back then computer security was such an afterthought you could sometimes type “help” at a login prompt to get a valid username/password. Other times they dispensed with the prompt altogether… just dump you straight in with elevated privileges after a connection was established.
Heh… yeah, you’re likely right. Back in the days of the old Commodore 64s (Hey, I don’t *feel* old!) we all too often took to trying to wardial just because we wanted to see what we could find. We had no idea what we were looking for beyond a pickup and the handshake screech through the speakers. God knows what we could’ve done without realizing it.
And later, when I was in college in the days of wide-open FTP services, Gopher, Archie, and Veronica (for those unfamiliar: The last two were search engines for the first two, respectively), I often downloaded anything I found that I felt was interesting. My rationale back then was “it must’ve been public on purpose”; I simply didn’t think that some folks had no idea how wide open they were making their computers and never intended for whatever they had on them to be touched by someone else. It was nuts, but back then there was simply no monitoring it, nor were there any rules against it. I’d bet if I had simply looked in the right places, I could’ve messed with important research or something else pretty critical; thank goodness I didn’t. I simply had no conception of these things being open because the owners didn’t realize what they were doing.
When doors are left open, sometimes the curious will walk through believing that they were open for a reason.
Nowadays, we have a totally different conception on how to approach networked resources, but back then, man…
My second IT job was at a company that didn’t believe they needed a firewall because nobody knew who they were. Desktops and servers (using publicly accessible IP addresses) would just randomly reboot and this was accepted as normal. And, low man on the totem pole, all I could do was to keep bailing water out of the boat. We did eventually get a firewall…
An ex-coworker, who’s since passed away, once relayed a story from his teenage years. He gained access to a bank, created an account called the Richard Nixon Election Fund (post-Watergate, obv), and transferred money from random accounts into it. It took them the better part of two years to figure out what happened. Since he didn’t do anything with the money, the criminal code was behind the times, and he was (common thread here) a teenager, he got off with a slap on the wrist. I think he documented how he got in so they could prevent it from happening again.
While an amusing tale, he certainly never did anything that warranted a visit from, and detention by, the Secret Service ever again.
Agreed. I advocate security at my company, which has anonymous consumer data. I have often heard, who will hack us, our data is basically worthless – e.g. its not a financial instrument like a credit card.
I try to explain that we have a brand name, and some bored 16yo script kiddie will hack us and brag about it 1. for fun and 2. to make a name in the hacking community and get more cred. Meanwhile our brand is damaged and our customers are unwilling to do business with us.
Fortunately (??) the latest news has changed thinking at the C-level. Now I say “Target breach” and the CEOs remember that their CEO got fired and half of their board resigned. Maybe it is worth a few more $10ks in the budget.
if it’s worthless, then it should not be stored. i suspect tghey are thinking ‘it’s only worth something to us’.
brian get’s close with the concept of hacking because they can. i think a common fault is the requirement to understand why some action or event would happen, rather than it’s simply possible. it’s similar to folks dismissing a large tsunami as unlikely and locating the backup power near ground level.
folks want to first understand all the ways the worthless data can become valuable before the take protecting it seriously. that often becomes a case of closing the barn door after the cow leaves.
anyway, when i hear worthless, i ask, then why is it kept? and do they really think they know every possible use of that data? are they really that arrogant? seems the saying pride goes before a fall may need more attention.
good luck in your efforts.
One point to consider is what was the electronic traffic sign message prior to being replaced? Hopefully not “Bridge Out Ahead” or “Workers In Roadway”. Yes, someone could get hurt.
Wonder if they bothered to check first… but if I came upon the “zombies ahead” one I’d definitely get a bit of a laugh out of it.
Sure you’d laugh… until you were attacked by zombies. 🙂
But there would be a zombie warning.. it would be dangerous if there really were zombies and someone changed it to read “all safe ahead” or something.
LOL
Or “No speed limit next 10 miles”
Be prepared to stop: Conga Line crossing ahead.
Definitely doesn’t take much to distract drivers but are they going to wait until it actually causes a serious problem (for instance someone getting injured) for them to take it seriously?
It’s really amazing how far these hackers will go..
“Definitely doesn’t take much to distract drivers but are they going to wait until it actually causes a serious problem (for instance someone getting injured) for them to take it seriously?”
As I was reading your post, I thought that the point you were going to make was more along the lines of “I can’t believe that they make these things so insecure”. But I can see your point too.
Ah yes The Internet of Things everything in your life/ home/work has a web connection and IP address, the microwave oven/shoe buffer/ window blinds/fridge-freezer/wok/door locks/shower/central heating/air conditioning/lawn mower/safe/toilet/tie rack/car/ the world very soon, looks like hell to me.
Reading the varied posts on this site I always wonder how they do these things. It seems the more you know the less you know. If someone were to bundle these bags of tricks into one consolidated listing, one would have a powerful weapon. Similar to exploit kits with the owners paying for new exploits to add to a software suite.
The “Warning, Zombies Ahead” and many other road sign attacks are based on physical access to the device, most of which have very pickable locks, default security PINs set, and keyboard ports with terminal access. Not IoT, since these ad-hoc signs aren’t internet connected, but still dangerous.
Er…that might have been the case back in 2011 or 2012, but it seems unlikely that this report by the MS-ISAC has somehow invented the idea that these things have a connection to the Internet.
If you read the advisory closely, you can see that (at least some of) the devices have modems, which means they are reachable via war dialing, if indeed they are not always connected. I’m guessing some are at least always-connected, since the report states that telnet and snmp were involved.
A growing number of environments are deploying large “public information” signs.
These signs have become cheaper and cheaper, and are now in a price range suitable for small-medium businesses as well as councils, schools, sports clubs etc.
These signs are typically deployed with an IP-connected 3G/4G wireless modem attached to a cheap USB/Ethernet/Serial bridge which is connected to the admin port of the Display Controller. (If you are really lucky, they have WEP-protected WiFi instead.)
A growing number of sales/service organisations have sprung up to sell “Managed Dynamic Signage Solutions” (which simply involves a Web Portal front-end for the 3G/4G modem).
From the systems that I have seen, security varies from negligible to non-existent – The “secret” is usually the serial number of the Display Controller – the auth is almost invariably trivial.
One popular range of “smart” Dynamic Signage uses the WZP2006 display controller. For this (and similar) controller(s), security was never a design requirement.
(Check this out for scary: http://ebookbrowsee.net/wzp2006-wireless-led-pdf-d203276692)
FYI:
I believe these signs were likely using RDS-TMC (FM broadcast of digital encode):
Very simple method (from sunhacker pastebin howto); going after forward facing encoders: http://pastebin.com/hiY6i0Ka
With default credentials:
http://dariusfreamon.wordpress.com/2014/01/28/audemat-fmb80-rds-encoder-default-root-credentials/
Bruce Willis’s Die Hard Movie, the last one where the hackers invoked chaos on stop lights, it numerical speed limit signs and all the other things that are electronic can easily come true to life.
It doesn’t take much to keep these people out. You just have to invoke the people in charge to take responsibility and make it happen with what they have or, buy some inexpensive controls to put in place. Transportation and IT may not make a match in most cases, but if it is IT related, tag it on them. Think of it this way, you don’t want the person filling potholes being an IT administrator, and you don’t want a “Road technician” managing the servers. Apply the right people and controls and it will work itself out. If it doesn’t, they will find a way, whether through new contracts, replacing/firing people and paying fines or jumping through hoops to avoid class action suits and individual suits due to personal injury invoked my something that was controlled by the state.
The right economic solution may be extensive cloud-based (AaaS or IaaS) services where the “pros” can manage 100k’s of servers for 100s or 1000s of companies, while those companies go about their business.
Computing responds to economies of scale.
No one expects a midsize accounting company to generate their own electricity or treat their own wastewater, but somehow we expect them to know how to securely and reliably deliver business applications. Let them focus on accounting.
My last submitted comment went into the vapor. Not sure why. So I thought a donation was appropriate since I seem to be on this site frequently.
My comment was on all the posts here contain a variety of methods by different individuals. I was thinking of the exploit kit articles of consolidating the methods into one location.
Most folks are also unaware that network printers come configured to put up a web page, and most are configured to not require a password, so if you know the printers IP address you could access it and change all sorts of parameters. Not to mention that you can also login to network printers using plain old telnet (also with no password). I reckon if a hacker wanted to cause some mischief with a company/school’s printers, they could have a field day.
I had to get my furnace replaced last fall. I insisted with the furnace guys that I wanted a furnace/thermostat that would NOT connect to the Internet. They said, “But you could use your smartphone to control your thermostat when you’re not at home!” I said, “And so can everyone else!” I also told them I would never own a “smart” phone. I do NOT want my household devices communicating with who knows who. Not ever.
Rusty
Technical term: air gapping.
What happens when they get around to hacking home refrigerators? I guess at the point the government gets alarmed and does something. Its logical that hacking will gravitate to the avenue of least resistance or security. It seems they’ve found it in highway signs. What has to happen is a rethink of how these systems are protected or it will be a learning ground for would be hackers in training.
Is it worth mentioning the old chestnut:
SNMP = “Security Not My Problem”
I love the pervasive use of Java as a platform for the M2M world to operate in… 😛
It doesn’t help that the government requires using the (1990s) NTCIP which uses SNMP as it’s base.
A friend of mine is too cheap to pay for his own broadband – no idea why as he is single and makes $100k+ in software.
So naturally he steals his neighbor’s wifi. The router was misconfigured so he logged in as admin and tuned it so it performed much better.
He made a couple of changes that required a restart but could not figure out how to make that happen – he isn’t the social engineer type to get the owners to do it. Fortunately it was springtime and a brief power outage took care of it for him.
Trust me, no hacker/cracker/script kiddie or what ever you want to call this guy can kill more than the government itself.
As long as we use IP address like 1.1.1.1 or 2001::1111, these kind of attacks will happen. I don’t know who is this 1.1.1.1 or 2001::1111 to control access to my system.
Surprisingly, there is no DMV ID card equivalent in Internet World. Then I would ask for “show you id” before I accept or deny access to my system.
Government I.T. infrastructure outside of spy agencies is like child’s play for these script kiddies … amusing in more ways than one.
How are these distracting, shouldn’t people be reading (be distracted) by them anyway? Anyone with half a brain shouldnt have a problem with driving effectively while reading a sign. Signs are everywhere and are meant to be read.
If all it takes is a change of words on a sign for people to mess up driving you have bigger issues.
Seriously?
That’s like saying naked women walking down the footpath aren’t distracting because clothed people ordinarily walk down the footpath and well, hey, they aren’t distracting.
Can’t put a naked woman up on those LED signs, but maybe those new advertising billboards they’ve started putting up everywhere?
Brian, thought you might like to know that when I went to access your website today through IE, I got a Microsoft warning that your site is “Unsafe”. I think this is a round about way to prevent people from visiting your site, probably one of the people you have written about has contacted Microsoft to say that your site is a security risk!
This might have been a SmartScreen warning. If so, there’s a way for that to be corrected: Since SmartScreen is partially reputation based, anyone getting the error can to the “”More information” link and click the “Report that this site does not contain threats” link, then follow the prompts.
Brian himself, if he starts getting it, can also do this and report in as the owner of the site.
For the record, I’m not getting the warning myself, even after doing a SmartScreen “Check this website” test.
And yes, if someone did report Brian’s site as unsafe, I have little doubt it’s either someone he wrote about, or a fan of one of those people. That’s just what they do: They go out of their way to mess with people who don’t let them have their way. It’s childish, and sad given that most of those folks are not children at all (at least not by age), but rather tend to be at least college aged if not older.
Internet freedom has made some folks forget how to be polite and have good manners.
We have all seem pictures of these “hacks” but in most case, variable message signs ( like the orange units in work zones) are not on networks, they are stand alone and are programmable using a hand held keyboard at the unit. The “hack” in those case is simply beating the lock on the cabinet.
However, most of the overhead units do have network connectivity and the hack is often the default password.
The signs I’ve (legitimately) worked with have been secured with the electronic equivalent of a torx screw :-/. They are all serial devices at heart, just with a socket/telnet wrapper, and that’s all assuming the RS232 connection is actually in the locked part of the case. Permanent signs over freeways etc… tend to have had a bit of thought put in regarding tamper protection (assuming the roadside network is not breached), but the mobile units are a bit of a joke really.
I don’t know if this has been addressed here, but the Dept of Homeland Security Infrastructure Reports says;
8. June 5, Nextgov – (National) Flaw lets hackers control electronic highway billboards. The U.S. Department of Homeland Security advised transportation operators June 4 of a hard-coded password vulnerability discovered in Daktronics Vanguard highway notification sign configuration software which could allow hackers to gain unauthorized access to the highway signs. The vendor was notified and is working to fix the issue.
Source: http://www.nextgov.com/cybersecurity/2014/06/flaw-lets-hackers-control-electronic-highway-billboards/85849/
Great…googly-moogly! Thanks for the link. Another hard-coded password flaw. When will these vendors learn?
You’re welcome there Fellow CISSP.
They probably will never learn. Talk about a hackers paradise. if those signs were networked you could have your own advertisement campaign.
It could be worse I suppose. if they hack the big 40 feet by 20 feet Billboards and throw porn up at rush hour, the insurance companies would go bankrupt for sure.
Great now have to choose between overhead porn or naked women on the walkways. Gotta love IT security blogs.
but there are SO MANY more vendors, most VMS signs are not Daktronics. Like Piers7 said, the majority of these signs still use rs 232/422 etc… just like the signal controllers that control traffic signals. Lots of old technology out there with no security other than physical security.
Target, ebay, and 1000 others. Same cause — passwords. Passwords are inherently insecure, and nothing can be done about that. Even “one time passwords”, which are getting popular as “second factor authentication” (from “old good” and hacked RSA SecurID to Google Authenticator, Duo Security, PhoneFactor and zillion others) can’t protect systems from hacking. There are few strong systems available, but it looks like until a disaster of 9/11 proportions strike, nobody cares. Credit card industry prefers to pay ransom to fraudsters rather than search for strong solutions. It’s so easy to do nothing and blame rogue foreign intelligence or bad teens…
Extremely complex problem can always be solved with a very simple solution.