A sprawling online company based in Georgia that has made tens of millions of dollars purporting to sell access to jobs at the United States Postal Service (USPS) has exposed its internal IT operations and database of nearly 900,000 customers. The leaked records indicate the network’s chief technology officer in Pakistan has been hacked for the past year, and that the entire operation was created by the principals of a Tennessee-based telemarketing firm that has promoted USPS employment websites since 2016.
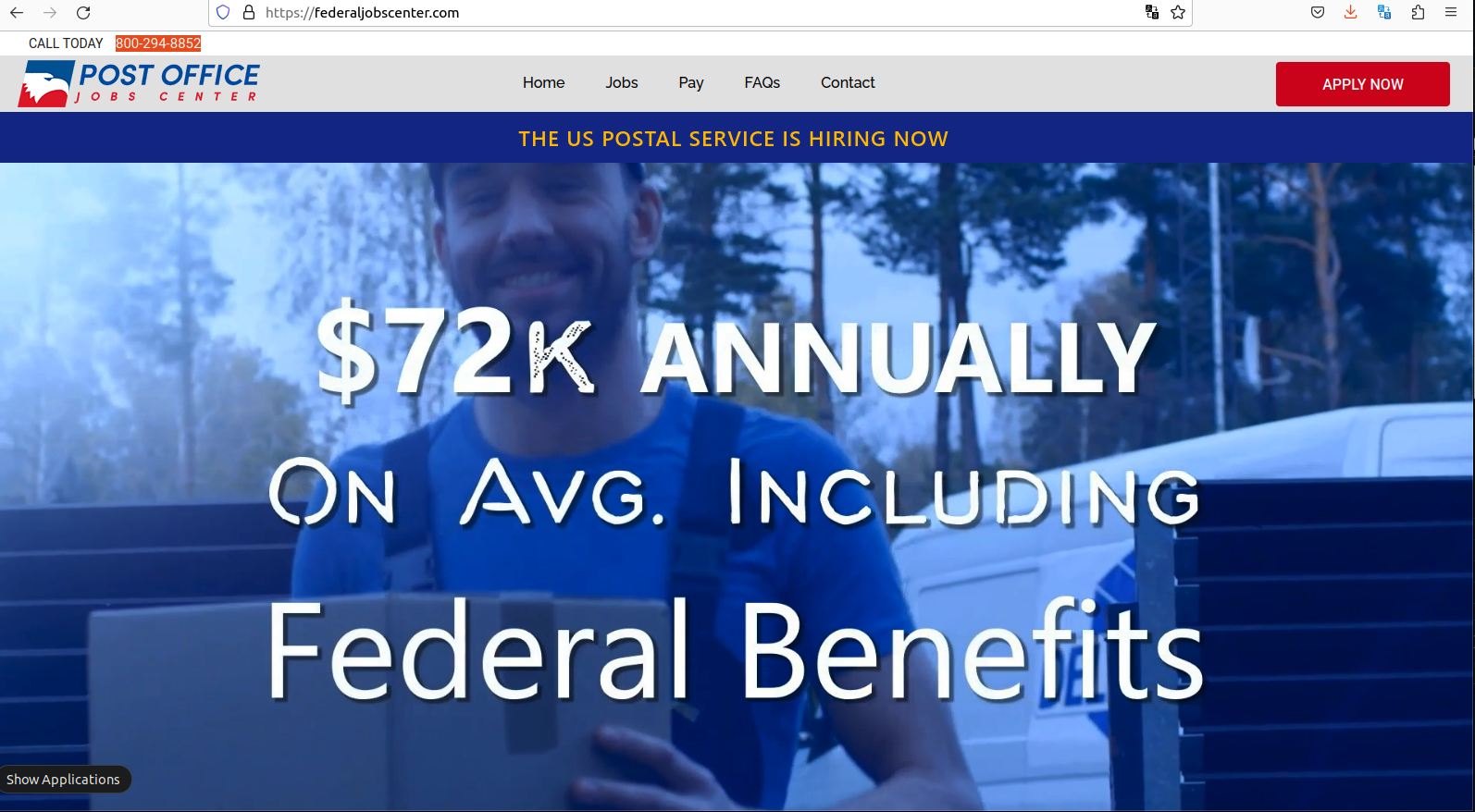
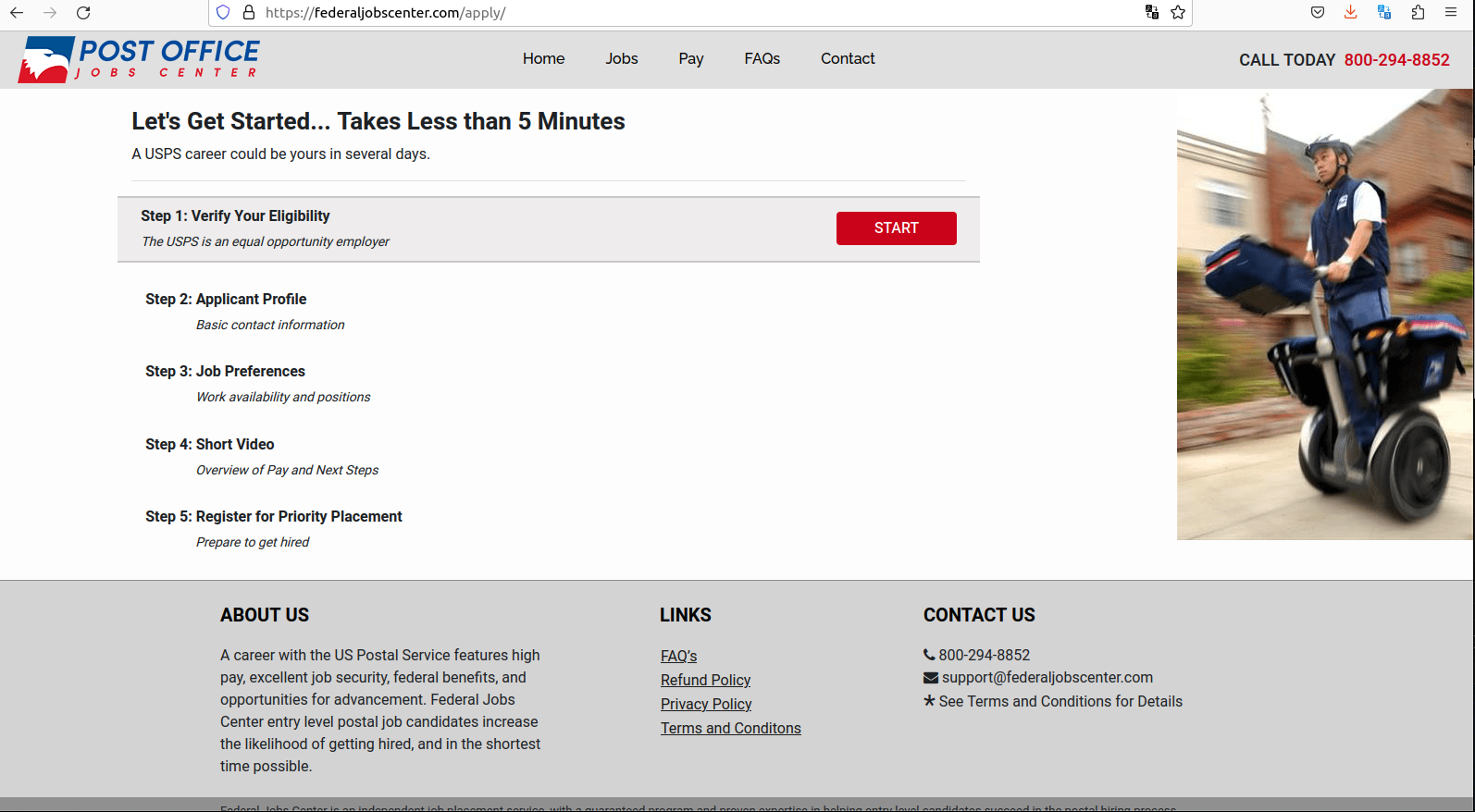
The website FederalJobsCenter promises to get you a job at the USPS in 30 days or your money back.
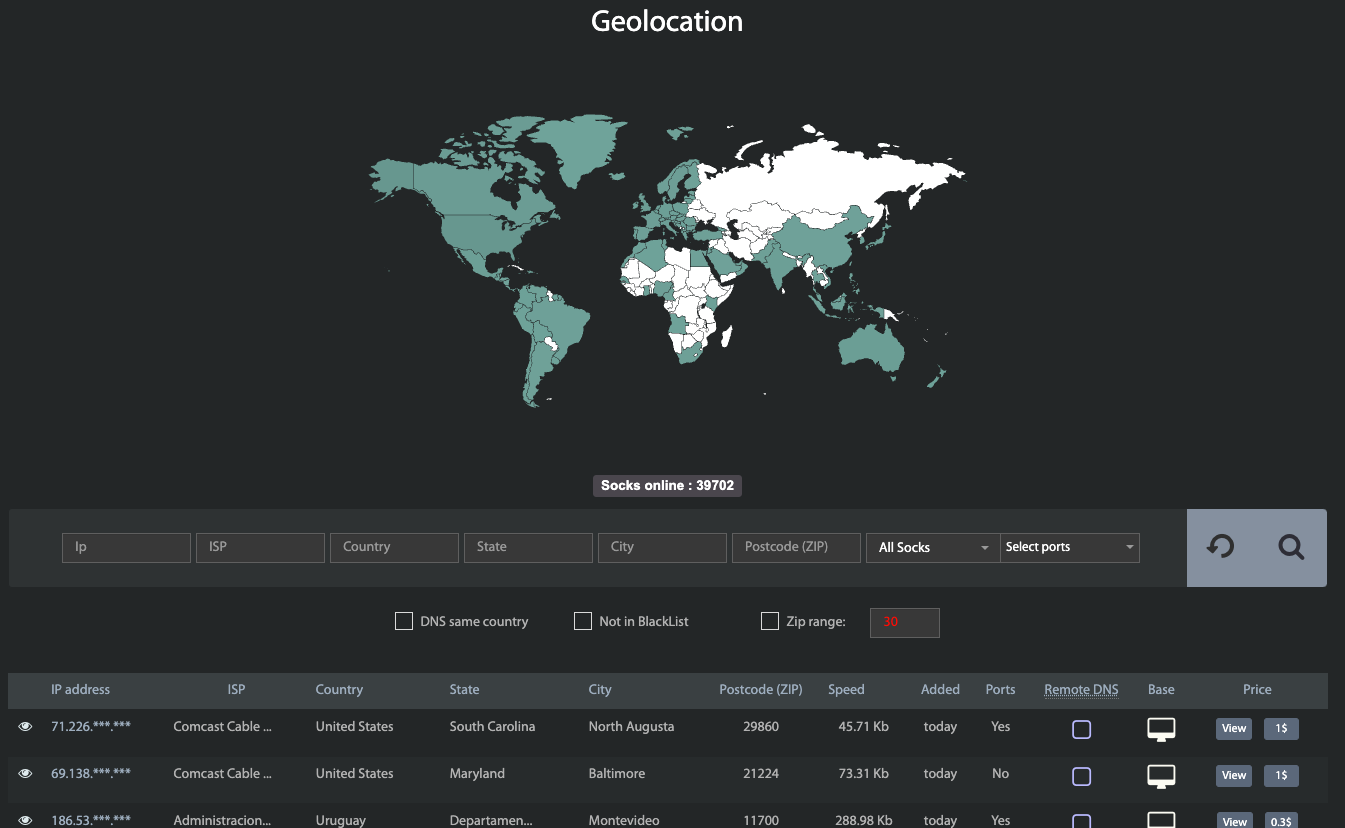
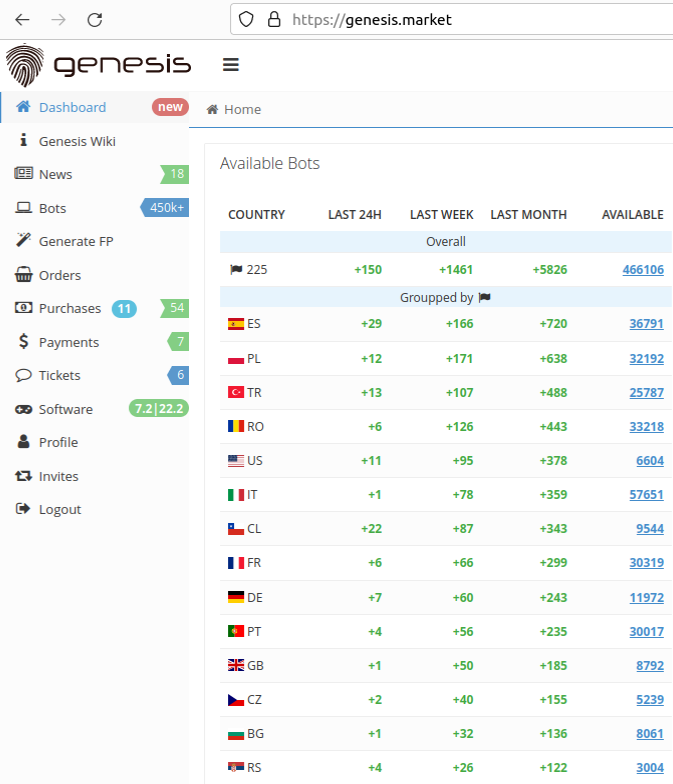
KrebsOnSecurity was recently contacted by a security researcher who said he found a huge tranche of full credit card records exposed online, and that at first glance the domain names involved appeared to be affiliated with the USPS.
Further investigation revealed a long-running international operation that has been emailing and text messaging people for years to sign up at a slew of websites that all promise they can help visitors secure employment at the USPS.
Sites like FederalJobsCenter[.]com also show up prominently in Google search results for USPS employment, and steer applicants toward making credit card “registration deposits” to ensure that one’s application for employment is reviewed. These sites also sell training, supposedly to help ace an interview with USPS human resources.
FederalJobsCenter’s website is full of content that makes it appear the site is affiliated with the USPS, although its “terms and conditions” state that it is not. Rather, the terms state that FederalJobsCenter is affiliated with an entity called US Job Services, which says it is based in Lawrenceville, Ga.
“US Job Services provides guidance, coaching, and live assistance to postal job candidates to help them perform better in each of the steps,” the website explains.
The site says applicants need to make a credit card deposit to register, and that this amount is refundable if the applicant is not offered a USPS job within 30 days after the interview process.
But a review of the public feedback on US Job Services and dozens of similar names connected to this entity over the years shows a pattern of activity: Applicants pay between $39.99 and $100 for USPS job coaching services, and receive little if anything in return. Some reported being charged the same amount monthly.
The U.S. Federal Trade Commission (FTC) has sued several times over the years to disrupt various schemes offering to help people get jobs at the Postal Service. Way back in 1998, the FTC and the USPS took action against several organizations that were selling test or interview preparation services for potential USPS employees.
“Companies promising jobs with the U.S. Postal Service are breaking federal law,” the joint USPS-FTC statement said.
In that 1998 case, the defendants behind the scheme were taking out classified ads in newspapers. Ditto for a case the FTC brought in 2005. By 2008, the USPS job exam preppers had shifted to advertising their schemes mostly online. And in 2013, the FTC won a nearly $5 million judgment against a Kentucky company purporting to offer such services.
Tim McKinlay authored a report last year at Affiliateunguru.com on whether the US Job Services website job-postal[.]com was legitimate or a scam. He concluded it was a scam based on several factors, including that the website listed multiple other names (suggesting it had recently switched names), and that he got nothing from the transaction with the job site.
“They openly admit they’re not affiliated with the US Postal Service, but claim to be experts in the field, and that, just by following the steps on their site, you easily pass the postal exams and get a job in no time,” McKinlay wrote. “But it’s really just a smoke and mirrors game. The site’s true purpose is to collect $46.95 from as many people as possible. And considering how popular this job is, they’re probably making a killing.”
US JOB SERVICES
KrebsOnSecurity was alerted to the data exposure by Patrick Barry, chief information officer at Charlotte, NC based Rebyc Security. Barry said he found that not only was US Job Services leaking its customer payment records in real-time and going back to 2016, but its website also leaked a log file from 2019 containing the site administrator’s contact information and credentials to the site’s back-end database.
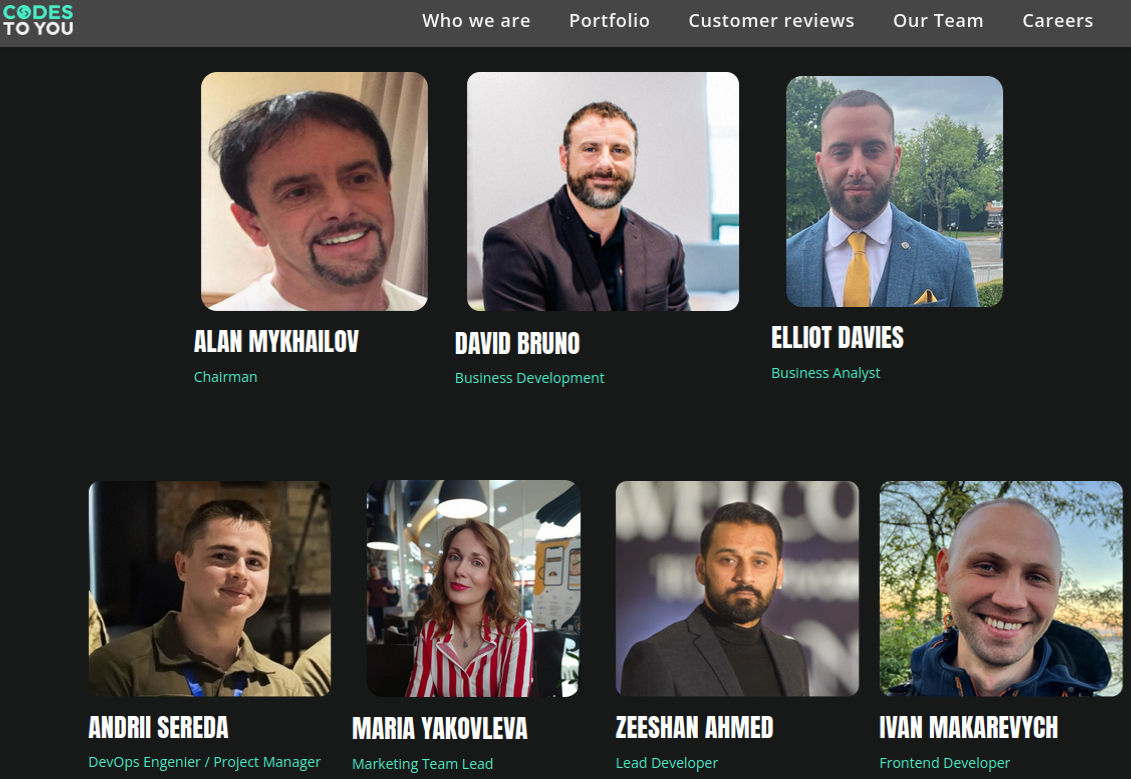
Barry shared screenshots of that back-end database, which show the email address for the administrator of US Job Services is tab.webcoder@gmail.com. According to cyber intelligence platform Constella Intelligence, that email address is tied to the LinkedIn profile for a developer in Karachi, Pakistan named Muhammed Tabish Mirza.
A search on tab.webcoder@gmail.com at DomainTools.com reveals that email address was used to register several USPS-themed domains, including postal2017[.]com, postaljobscenter[.]com and usps-jobs[.]com.
Mr. Mirza declined to respond to questions, but the exposed database information was removed from the Internet almost immediately after KrebsOnSecurity shared the offending links.
A “Campaigns” tab on that web panel listed several advertising initiatives tied to US Job Services websites, with names like “walmart drip campaign,” “hiring activity due to virus,” “opt-in job alert SMS,” and “postal job opening.”
Another page on the US Job Services panel included a script for upselling people who call in response to email and text message solicitations, with an add-on program that normally sells for $1,200 but is being “practically given away” for a limited time, for just $49.
“There’s something else we have you can take advantage of that can help you make more money,” the script volunteers. “It’s an easy to use 12-month career development plan and program to follow that will result in you getting any job you want, not just at the post office….anywhere…and then getting promoted rapidly.”
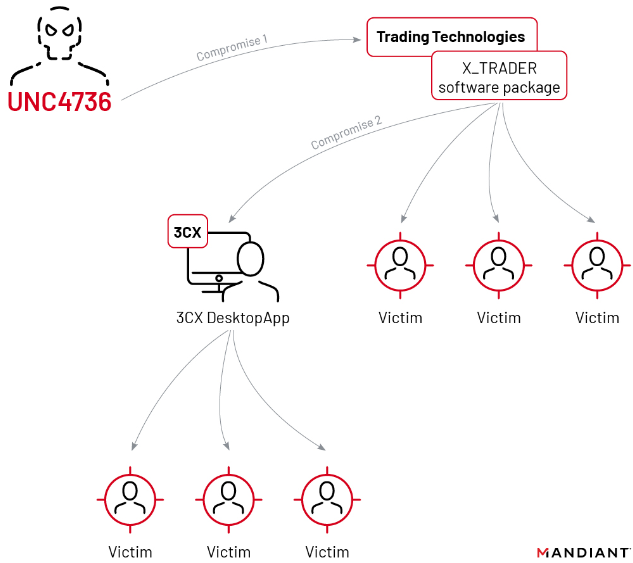
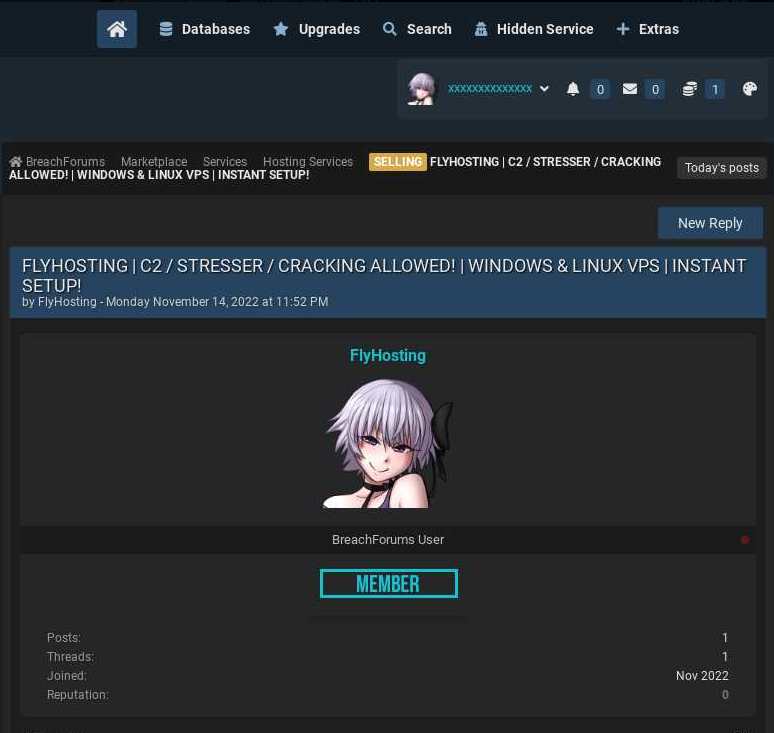
It’s bad enough that US Job Services was leaking customer data: Constella Intelligence says the email address tied to Mr. Mirza shows up in more than a year’s worth of “bot logs” created by a malware infection from the Redline infostealer. Continue reading