A new crimeware kit for sale on the criminal underground makes it a simple point-and-click exercise to develop malicious software designed to turn Mac OSX computers into remotely controllable zombie bots. According to the vendor of this kit, it is somewhat interchangeable with existing crimeware kits made to attack Windows-based PCs.
KrebsOnSecurity has spilled a great deal of digital ink covering the damage wrought by ZeuS and SpyEye, probably the most popular crimeware kits built for Windows. A crimeware kit is a do-it-yourself package of tools that allow users to create custom versions of a malicious software strain capable of turning machines into bots that can be remotely controlled and harvested of financial and personal data. The bot code, generated by the crimeware kit’s “builder” component, typically is distributed via social engineering attacks in email and social networking sites, or is foisted by an exploit pack like Eleonore or Blackhole, which use hacked Web sites and browser flaws to quietly install the malware. Crimeware kits also come with a Web-based administration panel that allows the customer to manage and harvest data from infected PCs.
Crimekit makers have focused almost exclusively on the Windows platform, but today Danish IT security firm CSIS Security Group blogged about a new kit named the Weyland-Yutani BOT that is being marketed as the first of its kind to attack the Mac OS X platform.
The seller of this crimeware kit claims his product supports form-grabbing in Firefox and Chrome, and says he plans to develop a Linux version and one for the iPad in the months ahead. The price? $1,000, with payment accepted only through virtual currencies Liberty Reserve or WebMoney.
The CSIS blog post contains a single screen shot of this kit’s bot builder, and references a demo video but doesn’t show it. I wanted to learn more about this kit, and so contacted the seller via a Russian language forum where he was advertising his wares.
The author said he is holding off on including Safari form-grabbing capability for now, complaining that there are “too many problems in that browser.” Still, he was kind enough to share a copy of a video that shows the kit’s builder and admin panel in action. Click the video link below to check that out.
ZeuS and SpyEye are popular in part because they support a variety of so-called “Web injects,” third-party plug-ins that let botmasters manipulate the content that victims see in their Web browsers. The most popular Web injects are designed to slightly alter the composition of various online banking Web sites in a bid to trick the victim customer into supplying additional identifying information that can be used later on to more fully compromise or hijack the account. According to the author, Web injects developed for ZeuS and SpyEye also are interchangeable with this Mac crimekit. “They need to be formatted and tagged, but yes, you can use Zeus injects with this bot,” he told me in an instant message conversation.
 Fans of the movie series “Alien” will recognize the name Weyland-Yutani as the fictional corporation that was sent ahead to establish habitable bases and dwellings on extrasolar planets in advance of the arrival of new human colonies. If this crimekit takes hold, or is an indicator of a broader interest in attacking Mac users, we could soon witness cyber crooks starting to colonize the Mac user community as well. The author of this Mac crimekit said he knows of several other independent coders who are working on Mac malcode projects that aren’t quite ready for prime-time, although he declined to elaborate on that claim.
Fans of the movie series “Alien” will recognize the name Weyland-Yutani as the fictional corporation that was sent ahead to establish habitable bases and dwellings on extrasolar planets in advance of the arrival of new human colonies. If this crimekit takes hold, or is an indicator of a broader interest in attacking Mac users, we could soon witness cyber crooks starting to colonize the Mac user community as well. The author of this Mac crimekit said he knows of several other independent coders who are working on Mac malcode projects that aren’t quite ready for prime-time, although he declined to elaborate on that claim.
Each time this subject comes up, I am struck by how fervently the Mac community denies that Mac users might ever have to deal with anywhere near the level of malware that currently besieges the Windows world. The Mac, these apologists explain, is far more secure than Windows, and that is why we have not seen malware writers attack the platform with the same vigor and interest. As one commenter on this blog reasoned, OS X simply doesn’t allow programs to be installed without user permission. My response is, assuming for the moment that the above statement about the Mac’s superior security is true, the operating system does nothing to stop the user from being tricked or cajoled into installing malware. What’s more, social engineering attacks are one of the primary ways that Windows users get infected today, so why would it be any different for Mac users?
Consider the scourge of rogue anti-virus attacks: Each day, thousands of Windows users are tricked into running and installing a bogus security “scanner” foisted on them by some hacked Web site. The attackers’ goal with these “scareware” muggings is to not only trick the user into installing malicious software, but also paying for it with their credit cards!
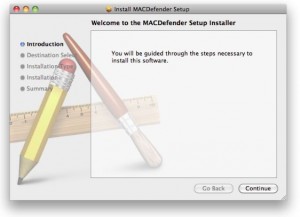
Earlier today, MacRumors.com carried a story about a new threat discovered by Mac security software vendor Intego that uses social engineering in a bid to install scareware known as “MACDefender.”
The nice thing about social engineering attacks is that defending against them doesn’t require buying or installing some type of security software. As I noted in a column last week, it merely requires the user to accept the notion that “security-by-obscurity is no substitute for good security practices and common sense: If you’ve installed a program, update it regularly; if you didn’t go looking for a program, add-on or download, don’t install it; if you no longer need a program, remove it.”





In cyber-space, no one can hear your account get owned…
Great article, no surprise that where there is money to be made the malware authors will follow.
And once it gets owned, I say you nuke it from orbit. It’s the only way to be sure! 😛 :::sorry, couldn’t resist::::
On a serious note, I recently read somewhere (can’t remember where right now) that this year is expected to see a sharp increase in malware attacks on the Mac platform. This may be the opening salvo.
To me, in the end, it always comes down to Law #10 of the 10 Immutable Laws of Security:
Technology is not a panacea
No matter how sophisticated the hardware and software become, they’ll never replace common sense and sound security policies and practices.
Well said, xAdmin: “No matter how sophisticated the hardware and software become, they’ll never replace common sense and sound security policies and practices.”
I teach this to my students first and foremost when discussing the topic of security, be it a PC or Mac class.
…And they don’t like it when I point them to this site:
http://en.wikipedia.org/wiki/There's_a_sucker_born_every_minute
This was an inevitable development.
Microsoft has actually been forced to implement a lot of security because it has been such a big target: the Security Development Lifecycle process, and memory protections such as DEP, ASLR, etc. In some ways they are ahead of the game. But third party app developers have been slow to follow although Adobe seems to have belatedly seen the light.
But as you say, all this is to naught when social engineering is involved. You can train users, with some difficulty, about the dangers but a well-researched targeted attack is almost guaranteed to succeed regardless of the operating system. Better patching of vulnerabilities would make it harder but users aren’t very good at that either.
Thank you for this post!
I look forward to further details as you learn them.
Thanks for taking a deeper look at the kit than most of the other outlets had! Quite interesting, though certainly not surprising.
I’m not sure how difficult it would be to provide an html5 version of content in addition to flash, but if it wasn’t too tough it could be nice. I know that most people have flash installed, but not all of us do – and it’s becoming increasingly possible to live without as more sites start offering both. With the possible security advantages of skipping having flash installed at all being made rather obvious lately, perhaps it’s worth a consideration given your subject matter. You’d also have the added benefit of support on iOS devices. Just a thought!
Interesting that this story didn’t break earlier, since the initial actual PR / new release posting by the alleged author of the information and two demonstration videos (1.avi and 2.mp4, one of which is listed here) occurred on two major Russian forums on 4/28/11.
@freed0mfight3r
“I know because I’m in the business of knowing”
Karl, thanks for your comment, although I’m not sure what the thrust of it is. I was clear to point out that I learned about this from the CSIS post, and then went to the underground forums to see if I could get more information. When I went to the forums that were hosting this guy’s ads, I saw that the admins there had already blocked his videos, since he was a new member and didn’t have the minimum number of posts necessary to post videos. So i followed the guy’s contact info that he left on those sites and contacted him via IM to get the videos and additional information straight from the purported author of this program.
hi brian
I am curious — don’t you use a MAC ? :O 🙂
Yes, and Windows, and Linux.
Brian which version of Linux do you prefer?
Brian,
Thanks for the comment. Certainly no offense in reporting to you or others. It’s amazing how popular, stealthy, and damaging these DIY crimeware kits have become. I look forward to future analysis of this kit.
@freed0mfight3r
I’m curious to see if this is limited to IPV4 and if the implementation of IPV6 will cause problems for kits of this nature.
@Fuzzy,
I’m curious why you think the implementation of IPV6 will make any difference at all. As far as I can tell, this type of attack “piggy backs” on the user’s browser. If the user’s browser can navigate to IPv6 (or from IPv6), the tool can and will follow.
But maybe there’s a subtlety somewhere that could trip up the tool. Please explain.
DeborahS,
To be honest, I don’t know much about IPV6 other than it is far more complex than IPV4, and my limited knowledge about it has made me want to study its complexity even more.
To answer your question:
I was pondering that maybe the additional encapsulating information provided by IPV6 will be able to “flag” IPV4 based software (as it can already identify an IPV4 address and convert it to an IPV6 address). Lets face it most of the software out in cyberspace is not developed for “Appropriate use” and is intermingled with “Appropriate use” software. So with that in mind my idea is not to combat the software that is created (by the crime kits) but combat the connection or backbone it relies on. my thought is maybe security consultants within IEEE and software developers (Microsoft, Apple, etc) might be able to develop browser integrated software that will identify friendly registered IPV4/6 addresses and thus negate the use of the many (but not all) potential security vulnerabilities, but still allow a user to access the internet, a Digital version of FOF.
It stands to reason that when (not if) IPV6 is rolled out that the change will occur first in environments that will want to conform to regulations on software (such as businesses and govt agencies) and will have to register their IPV6 address with some form of regulatory (cue IEEE or other IP Registrar). It also stands to reason that they will want to be kept confined to a realm in which they need or want to operate. Using this, a regulatory group could group like businesses, or private users. then use the group registration as a template other groups such as PC manufactures, industries, and eventually the public at large. they can then impose restrictions that require the groups to conform to before they can be granted access to a IPV6 address.
In essence it is a way that internet can be subnetted and turned into a gigantic vlan. This so that groups with legitimate business can access and freely interact with (legitimate business or education or whatever) without fear (aside from the general corporate rivalry) and those with more liberal intent can continue to freely communicate without the hassle of interacting between the two.
that was my thought anyway on how IPV6 might be used to thwart crime kits….
@Fuzzy,
An impressive analysis about how IPv6 could be rolled out (and I’m not disagreeing with any of it), but you still don’t explain how this crime kit, once installed, couldn’t navigate to the same sites as the computer its installed on can navigate to. Seems to me that once you successfully piggyback a browser, you can go anywhere it can go.
Unless I’m grossly misunderstanding something, and that’s always possible :0)
I think the thinking was that even if the malware found its way somehow onto the user’s computer, as long as the user’s computer is in the ‘trusted’ vlan then the malware could not transmit the user’s details out into the ‘untrusted’ vlan zones..
surely though, someone within the trusted vlan zone who is able to receive these details would stand to make a killing?
@Jerry Mkaranga
Well that’s an interesting view. The malware, if it’s going to succeed in its purposes, has to send its data somewhere. If it can’t find its IPv4 or IPv6 home server’s address from where it is, then where is it going to send its data?
Good catch!!!
Jerry Mkaranga,
That was one of the possible security issues that came to mind was if the security was breached by someone behind the trusted vlan it would have to be someone within that particular group.
The hope is that the IT Sec officer for that group would be able to find and eliminate the malware threat before any data could be used (but as we all know it does take a while for breaches to be found and a plug to be placed)
DeborahS
Pretty much Jerry summed up what I was planning to say. It all can go back to Routing 101. If the bot cant communicate with the admin, then what good does the data it has collected do? it sits there waiting to be transmitted, but never will until its owner joins the vlan (and fat chance will the owner turn legit)
Excellent concept Jerry.
There is no difference. It could be IPX or Token-Ring, or FDDI, or over a modem… IPv4, IPv6, Decnet, regardless….
If the communications to the end server is allowed, VLAN or not, it will traverse the network and be delivered. Secure VLANs are a crock, unless they are completely isolated without any incoming or outgoing network traffic, and then, what’s the point?
Assuming that a computer was segregated and on a secure network with some mysterious protocol, (or IPv6 for that matter), it wouldn’t get infected in the first place, AND, you really wouldn’t need a browser, since you’re not browsing the web. All of this speculation of protocol being an issue, or secure VLANs is simply that, speculation without understanding.
As a Mac Instructor at Lambton College I show students why they should have protection software. As for the Mac, this is not a new thing at all. It is mere media hype to help sell ads, nothing more, nothing less.
Let’s face it “a fool and his money are soon parted, as is a foolish computer user and his operating system and maybe money.
A well maintained computer does not get a virus, malware, or spyware; people do. Computer users who are click happy run into problems.
As for the Mac one would have to give away their Admin password or download a program that is malicious in nature. As you clearly point out in this article, “it merely requires the user to accept the notion that “security-by-obscurity is no substitute for good security practices and common sense” and I will add that most people NEVER take the time to read ANY manual or do an online review on software that they plan to download – they just click away as if the mouse was a TV remote.
Amazing how much attention a topic this old gets immediate attention these days – Just shows how little people care to know…
“As for the Mac one would have to give away their Admin password ”
As an attacker, I wouldn’t see that as a big challenge. After all, thousands of phishing victims gave away their password and banking codess..
With some javascript and dash of creativity you can easily re-create the OS X password dialog.
-Roland
“With some javascript and dash of creativity you can easily re-create the OS X password dialog.”
Easy to say, but let’s see some. If this were the case it would be WIDE spread and HEADLINE NEWS.
This is how hype is spread.
Roland you missed the point by this statement:
As an attacker, I wouldn’t see that as a big challenge. After all, thousands of phishing victims gave away their password and banking codess..
We all know this is the case for online suckers, but MOST Mac users know enough not to give out their admin password. The ones that don’t suffer just as PC users have.
Gregory wrote: “a fool and his money are soon parted….Computer users who are click happy run into problems.”
I agree but not being a fool or click happy is no guarantee of protection. A lot of the new malware is targeted. The victim is researched and the e-mail and links or attachments (e.g. PDF) sent to one or a small number of people. There may be few if any clues. You will click if the e-mail is convincing enough because it won’t look any different from a normal and expected business e-mail from a trusted correspondent. As has been discussed here many times, the only real protection is to isolate critical systems: have a dedicated system for banking (or whatever) and don’t use it for e-mail, web browsing, etc.
“the Mac Community” consisting of 10s of millions of users, is not represented by a few people who post on this, or any other single blog.
OMG, this is getting like politics where you choose the single most idiotic member of your opposition, and claim he speaks for everyone in the opposing party.
” the operating system does nothing to stop the user from being tricked or cajoled into installing malware.”… Safari does warn users when they they tread into suspected malware sites (and has done this for a year longer than explorer) And OSX warns you when you install software from the internet, that you really might not want to do that if you don’t trust the source… And I could go on, but that does seem like more than nothing.
Please, Mac users are a diverse group, and many of us use systems from MS and even Linux. Quit stereotyping and baking it up with false statements. Ask any anti-virus company how many PC viri their programs look for. They passed a million years ago. How many mac viri signatures do they look for? 50 or so if you count the ones back from the 80s. Does that make the Mac perfectly safe? No. Does it mean the PC is equally safe. No.
Wait…, you posted a video that you obtained from a guy who sells malware that hijacks browsers ?!?
It’s a recording of a recording.
Brian,
the date for the article is shown as May 11. May 1 is more likely (Maybe your finger got stuck on the number key) .
Thanks for all the informative articles.
Please disregard my comment above.
One consideration that I meant to mention in the story is that most of these Web injects for Zeus et. al. are not free, and if you want to use them you need to buy them a la carte. Which makes bot kits for the Mac that allow the use of these same Web injects a good investment, since the attacker who expands from botting Windows systems to Mac machines is merely trying to get more out of his already-invested dollars.
Is Safari on a Mac more difficult to hijack than Chrome or Firefox?
No. Safari is just as vulnerable as the rest. I’m guessing it just hasn’t been as widely explored as IE, and this time I’d guess the reason is usage. Even Mac users can/have/maybe still use IE.
I’m not sure on browser market share, but it’d be interesting to see.
All the Mac users I know run Firefox, which is a lot faster than Safari.
MacOSX has surely as much holes as linux does.
But Apple is very slow with patches. Its not rare, that holes stay open for months.
While Windows is by now a real hard to hack, because they added so much different layers of security(DEP, ASLR), MacOSX is still very open.
Hacking windows is more like work than fun 😉
Still we see Windows exploits way more often(or by now exploits for software running on windows. looking at you adobe …!!)
Im absolutely sure, if MacOSX had as much users as Windows, they would have the same share of exploits.
(and a lot more, if they keep their security efforts low)
Christian says “MacOSX has surely as much holes as linux does.”
You gotta love these types of blatant statements tossed out there like bread crumbs for pigeons.
Christian can you back up this statement and let us know where these “holes” exist?
The only holes I am aware of on a Mac is the human factor, in careless operations online.
Someone speculated that holes exist because MacOS is based on *NIX variants that have security holes – parts bsd and mach. It’s a safe assumption to make. In fact, there have been many holes on the Apple platform, especially its drivers. It’s just that relatively few people use these machines or are researchers that want to deal with Apple and their legal hordes. Or their sysadmins, really.
http://www.securityfocus.com/news/11445
Apple, like other vendors, is constantly patching security holes in OS X and iOS as well as applications like iTunes, Safari, etc. Here some (not all) posts from ZDnet’s ZSero Day blog that referenced apple vulnerabilities and patches over the last 6 months or so.
http://www.zdnet.com/blog/security/apple-patches-pwn2own-flaw-in-massive-mac-os-x-update/8471
http://www.zdnet.com/blog/security/pwn2own-2011-on-cue-apple-drops-massive-safari-ios-patches/8348
http://www.zdnet.com/blog/security/apple-plugs-57-major-security-holes-in-itunes/8275
http://www.zdnet.com/blog/security/apple-patches-man-in-middle-vulnerability-in-os-x-106/7886
http://www.zdnet.com/blog/security/apple-plugs-15-gaping-security-holes-in-quicktime/7809
http://www.zdnet.com/blog/security/mac-os-x-security-flaw-publicized-after-apple-fails-to-patch/7712
http://www.zdnet.com/blog/security/apple-plugs-mac-os-x-information-stealing-hole/7376
Over the last few years Apple products are usually the first to go at the CanSecWest hacking competition, Pwn2Own. Apple has a reputation for being slow to patch.
In their favor they do appear to know they have a problem. They’ve made a number of high profile security hires over the last couple of years and seem to be in the process of trying to implement something like Microsoft’s Secure Development Lifecycle program:
http://www.cio.com/article/print/657673
@gregory “The only holes I am aware of on a Mac is the human factor, in careless operations online….”
Apple’s own list of vulnerability patches for OS X, iOS, and application software:
http://support.apple.com/kb/HT1222
The November 2010 OS X update patched 131 vulnerabilities. Some of these had been around for 2 years.
Hey Gregory,
sorry for the late reply, but i think k and Alan gave you enough proof, that MacOSX in fact has a lot security issues.
Like any other OS….
Stating the “human factor” as the only way to exploit an MacOSX seems a very bold statement on the other hand.
That would suggest that MacOSX has perfect code.
Something every Programmer knows is impossible, as soon as you leave the “hello world” tutorial.
The same hype about MacOSX security happend with Linux, firefox, etc, pp.
In the beginning everybody said, Linux/Firefox is more secure than their competitors.
Now Linux is the major server OS in the internet, and you can find a new kernel exploit every few weeks.
Same with firefox, which is my now a much bigger target for exploits than the IE.
I really hope we can get over this security by obscurity concept.
Here ya go. This may be of interest:
http://www.youtube.com/watch?v=uu4b5Gjl2JQ
I love that when a Mac gets owned, the apologies fly, but when it’s anything but a Mac, it was expected.
Mac users need to grow up and accept that NO computer system is secure, as long as you connect it to other computers.
So, my question, How is the banking community dealing with this? How are all of those Mac users who “only use their mac for home finances” supposed to react?
And lastly, How long until they find a way to subvert the installation system? There have been MANY openings in the Mac software that allowed root access, yet they hadn’t been exploited for this… it’s just a matter of time…
I have to admit that the hype regarding Macs had recently made me think that I absolutely needed one. My budget said otherwise, however! This discussion is very interesting to me in that I am still considering purchasing a MacBook Pro in the future, and I want to make sure that if and when I do it is for the right reasons.
At any rate, heeding Brian’s advice to users appears to be as important as which system I choose.
A little late, but don’t forget the alternate suggestion of a LiveCD instead. I use a dedicated Live USB stick with KUbuntu instead of a completely separate PC.
If you’re a Windows gal, I want to mention my supervisor’s experience. She bought a Mac because of all the advertisement that it’s “easier” and “more intuitive” than Windows. She tells me that it wasn’t any easier to get started — it wasn’t intuitive until after she learned how to use it. 😉
Here is a link on an update to the crime kit availability
http://www.opensc.ws/malware-discussion-general-help/14553-weyland-yutani-bot.html
Hah! Someone bought the source? Perhaps to have it all to themselves…so that nobody else could use it? I wonder who that could have been…..?
Do you have any thoughts or suspicions on who would have bought the code?
Life is good when you are sitting on $65 billion U.S. 🙂
Does the author claim the iPad version work on stock ipads, or jailbroken only?
Come on, the video you list herein is terrible and should be removed. I has no value at all, even the comments on this video say so:
http://www.youtube.com/watch?v=lD3l_nqmE6w&feature=player_embedded