The FBI has scrubbed some 19,000 PCs that were infected with the Coreflood bot malware, the agency told a federal court last week. The effort is part of an ongoing and unprecedented legal campaign to destroy one of the longest-running and most menacing online crime machines ever built.
In April, the Justice Department and the FBI were granted authority to seize control over Coreflood, a criminal botnet that enslaved millions of computers. On April 11, 2011, the U.S. Attorney’s Office for the District of Connecticut was granted authority to seize 29 domain names used to control the daily operations of the botnet, and to redirect traffic destined for the control servers to a substitute server that the FBI controlled. More significantly, the FBI was awarded a temporary restraining order allowing it to send individual PCs infected with Coreflood a command telling the machines to stop the bot software from running.
In a declaration filed with the district court, FBI special agent Kenneth Keller said the bureau has issued approximately 19,000 uninstall commands to infected computers of two dozen identifiable victims in the United States. The FBI said it obtained written consent from all 24 victims, and that none reported any adverse or unintended consequences from the uninstall commands.
Keller said the FBI has directly notified hundreds of identifiable victims, and that it has provided information to approximately 25 of the largest Internet service providers in the United States, enabling them to notify their infected customers.
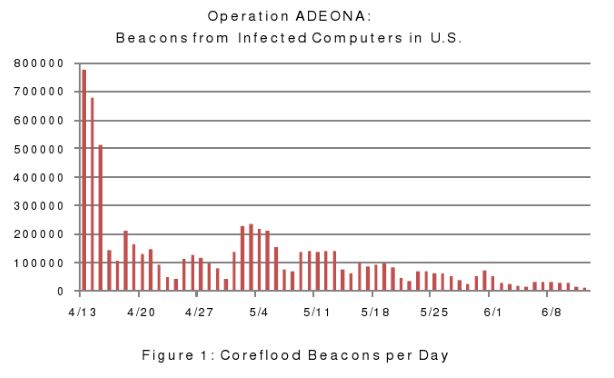
“The FBI has also provided information about infected computers to law enforcement agencies overseas,” Keller told the court. “While it has not been possible to notify the owner of every infected computer, due in part to the difficulty in identifying the computer owners and obtaining accurate contact information for them, the decline in the size of the Coreflood Botnet is likely attributable in large part to the success of the victim notification efforts.”
Keller said that the continued operation of the substitute server was no longer necessary to prevent the as-yet unidentified defendants from using the Coreflood botnet to commit further wire fraud and bank fraud, or to eavesdrop on victim PC communications.
“The continued operation of the substitute server is consuming considerable law enforcement resources, because the server is being closely monitored to ensure its proper operation,” Keller wrote. “Those resources can be better allocated to other law enforcement investigations, now that the decline in the size of the Coreflood Botnet has leveled off. Also, while the Coreflood software will begin to run on still-infected computers once the substitute server is taken out of operation, the seizure of the Coreflood domains will continue reasonably to prevent the Defendants from obtaining access to those computers or to data stolen from those computers.”
A copy of Keller’s declaration is available at this link (PDF).




again and again you provide us with excellent articles!!xxx
Is this why I constantly get the “some errors have occurred when sending this email” with, of course, no errors ever listed. I get this when trying to send an image from Picasa via Windows Live Mail which is my default…..do you think I could have this infection? The same maddening popup appears when trying to email a “Snipping Tool” image.
If so, then, how do I get rid of this if I’ve got it?
Hope this isn’t “off topic”……
You 14 “Dislikers” are a buch of self important jerks taking yourselves much, much, too seriously.
My comment was posted here in good faith as by coincidence I was getting a lot of “error” messages without any explanation. Reading Kreb’s article piqued that quey……you guys go soak your heads in cold water……maybe take a cold hip bath, simultaneously….a new experience.
Hey! #15!…..yer included!…..add any subsequent “Dislikers”.
May each of you “Dislikers” of my Comment here have noxious, sulphuric, gaseous emissions in important, confined Committee Meetings, may your lower intestines bloat painfully, matched in size only by your strainng cranial vacuums. May your ears ring with barely perceived piercing peer condemnations.
Come Period End, and other approaching deadlines, may all your toner cartridges be found leaking, and half depleted by mid-day this next fiscal Friday.
Lastly, may your pocket protectors be found protruding provocatively.
Without an in-depth analysis of your system it is difficult or impossible to tell if you are infected, and even more difficult to tell what type of infection might be responsible.
If you have concerns I would recommend taking your PC to a competent PC repair place, and have it re-imaged just to be safe.
The increasing number of my “Dislikers” accumulating here confirms that a very shallow sore spot and vulnerable sensitivity has been stepped on, or, overstepped by their revealing misreading of my inocuous initial posting.
Krebs’ past and continuing superb in-depth coverage here of this dangerous subject matter certainly deserves more thoughtful, adult, comment.
Even in an AA or NA meeting sharing off topic is OK [occasionally] so I am just wondering how surprised everyone was to get a notice to upgrade to Firefox 5 when Firefox 4 just came out only a couple of months ago?
It would be nice if these upgrades would warn us what won’t work with the new upgrade [like Google Tool Bar] BEFORE we choose to download it … or am I being too picky in my expectations maybe?
There now, that wasn’t too bad, was it?
It feels good to read about bots and bot-masters and the best place you get to know about the insights is no doubt “KrebsonSecurity”. also, after reading this blog post i am kinda relaxed to see the decline in the number of core flood victims.
I am told that the government (via reports to US-CERT) is often aware of citizens who are or were victims of keyloggers, malware and whose non-federal but personal credentials have been compromised. Unlike here where the FBI actually acted on this (and not without some controversy) I’m told that this malware/keylogger/compromised credential data is shared but if it does not impact a federal computer or system it is effectively ignored. Not sure what the legal, moral or ethical issues are, but if organizations of the US government somehow know that my IDs (or, not me, I’m pretty good security-wise, but let’s say my grandmother..) have been hacked, should they not do something to try and tell me? The risks of harm to people who have been hacked are obvious, should government agencies ignore proof of being hacked if they come into their possession? I applaud the FBI for tackling this head on, do wish that were the approach with this other information.
Any public options to check and or remove coreflood from personal computers? Which Malware or AV programs remove known strains, which rootkit scans are effective, which files to check for on a computer, etc?
To the off-topic folks asking about how to check/clean their own computers: There are forums where this service is offered free. The volunteers go through a significant amount of training, and I wouldn’t suggest anyone trying to do it just by looking up what the names of the suspicious files are. Malware can choose the same names as critical system files, and you could turn a slow computer into an unbootable brick if you delete the wrong thing.
One forum I recommend is SpywareHammer.com:
http://spywarehammer.com/simplemachinesforum/index.php
Be sure to read the instructions on how to post, then follow the instructions you are given in the order you are given them. (Also, note the forum defaults to public email addresses for some reason, so be sure to change yours to hidden.)
Thanks, Alpha. Bleeping Computer and DSL Reports also have very good and helpful security help forums, both linked in the blogroll on the right sidebar of this blog.
Just follow their instructions to the letter, answer questions promptly, and you should be able to get help with a variety of PC problems.
The affidavit says:
“…the FBI has issued approximately 19,000 uninstall commands to infected computers of approximately 24 Identifiable Victims, none of whom have reported any adverse or unintended consequences from the uninstall commands.”
I’m confused by this wording. Did the FBI send 19,000 uninstall commands to 19,000 infected machines or to just 24 identifiable victims? The latter doesn’t really make any sense but maybe I’m just reading something wrong here.
That is confusing and Brian should perhaps clarify it. As I read it they sent 19,000 automated uninstall commands but contacted 24 of the victims directly due to perhaps them being in the government or them consistently saying know and the FBI knowing who they were.
May major concern about it being done this way is the following scenario. What is to prevent some hacker from impersonating the FBI and instead of uninstalling the bot software actually using this as a mechanism to infect clean machines and make them bots? Unless some attempt is made to prevent this from happening you are going to have some pretty bad problems.
Oops, I meant “no” rather than “know.”
The only real legal winners here are the banks. Consumers lose their money and sometimes they complain and the bank issues a charge back. If the bank issues a charge back and refunds the customer the bank does not lose any money. If the customer does not complain the bank does not lose any money. In fact you could ask about the amount of money banks do make on fraudulent charges!