Pavel Vrublevsky, the embattled co-founder of ChronoPay — Russia’s largest online payments processor — has reportedly fled the country after the arrest of a suspect who confessed that he was hired by Vrublevsky to launch a debilitating cyber attack against a top ChronoPay competitor.
KrebsOnSecurity has featured many stories on Vrublevsky’s role as co-founder of the infamous rogue online pharmacy Rx-Promotion, and on his efforts to situate ChronoPay as a major processor for purveyors of “scareware,” software that uses misleading computer virus infection alerts to frighten users into paying for worthless security software. But these activities have largely gone overlooked by Russian law enforcement officials, possibly because the consequences have not impacted Russian citizens.
In the summer of 2010, rumors began flying in the Russian blogosphere that Vrublevsky had hired a hacker to launch a distributed denial of service (DDoS) attack against Assist, the company that was processing payments for Aeroflot, Russia’s largest airline. Aeroflot had opened its contract for processing payments to competitive bidding, and ChronoPay was competing against Assist and several other processors. The attack on Assist occurred just weeks before Aeroflot was to decide which company would win the contract; it so greatly affected Assist’s operations that the company was unable to process payments for extended periods of time. Citing the downtime in processing as a factor in its decision, Aeroflot ultimately awarded the contract to neither ChronoPay nor Assist, but instead to Alfa-Bank, the largest private bank in Russia.
According to documents leaked to several Russian security blogs, investigators with the Russian Federal Security Service (FSB) this month arrested a St. Petersburg man named Igor Artimovich in connection with the attacks. The documents indicate that Artimovich — known in hacker circles by the handle “Engel” — confessed to having used his botnet to attack Assist after receiving instructions and payment from Vrublevsky. The same blogs say Vrublevsky has fled the country. Sources close to the investigation say he is currently in the Maldives. Vrublevsky did not respond to multiple requests for comment.
The allegations against Artimovich and Vrublevsky were supported by evidence collected by Russian computer forensics firm Group-IB, which said it assisted the FSB with the investigation. Group-IB presented detailed information on the malware and control servers used to control more than 10,000 infected PCs, and shared with investigators screen shots of the botnet control panel (pictured at left) allegedly used to coordinate the DDoS attack against Assist. Group-IB said Artimovich’s botnet also was used to attack several rogue pharmacy programs that were competing with Rx-Promotion, including Glavmed and Spamit (these attacks also were observed by security firm SecureWorks in February).
This DDoS saga is the latest chapter in a fascinating drama playing out between the two largest rogue Internet pharmacies: Vrublevsky’s Rx-Promotion and Glavmed (a.k.a. “Spamit”), a huge pharma affiliate program run by Igor Gusev, the man who co-founded ChronoPay with Vrublevsky in 2003.
Gusev has been in exile from his native Moscow since last fall, when Russian authorities named him the world’s biggest spammer and lodged criminal charges against him for operating an illegal business. Spamit was forced to close shortly thereafter, and Gusev blames Vrublevsky for using his political connections to sabotage Spamit. Late last year, Gusev launched redeye-blog.com, a blog dedicated to highlighting alleged wrongdoing by Vrublevsky. In one post, Gusev charged that Artimovich agreed to DDoS Spamit.com because he believed forum members fleeing the program would join his own budding spammer forum: the still-active but largely dormant program Spamplanet.
Both ChronoPay and Glavmed/Spamit suffered hacking attacks last year that exposed internal documents, financial dealings and organizational emails. The data leaked from Glavmed/Spamit includes a list of contact information, earnings and bank account data for hundreds of spammers and hackers who were paid to promote the program’s online pharmacies. Those records suggest that for most of 2007, Artimovich was earning thousands of dollars a month sending spam to promote Spamit pharmacy sites.
The document that the FSB used to lay out the case for criminal proceedings against Artimovich, a.k.a. “Engel,” states that he was paid for the DDoS services with funds deposited into a WebMoney account “Z578908302415”. According to the leaked Spamit affiliate records, that same WebMoney account belonged to a Spamit affiliate who registered with the program using the email address “support@id-search.org.” Web site registration records for id-search.org show that the name of the registrant is hidden behind paid privacy protection services. But historic WHOIS records maintained by DomainTools.com reveal that for a two-month period in 2008 those registration records were exposed; during that brief window, records listed the registrant as Igor Artimovich from Kingisepp, Russia, a town 68 miles west of St. Petersburg.
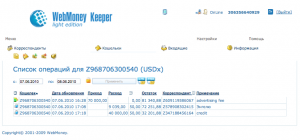 The emails and documents leaked from the hacking intrusion into ChronoPay last year show that Artimovich and Vrublevsky exchanged numerous emails about payment for unspecified services. Among them is an email receipt from WebMoney showing a transfer of more than $9,000 from an account Vrublevsky controlled to Artimovich’s Z578908302415 purse on July 6, 2010, just days before the DDoS attacks began. The notation listed next to the payment receipt? “Engel.”
The emails and documents leaked from the hacking intrusion into ChronoPay last year show that Artimovich and Vrublevsky exchanged numerous emails about payment for unspecified services. Among them is an email receipt from WebMoney showing a transfer of more than $9,000 from an account Vrublevsky controlled to Artimovich’s Z578908302415 purse on July 6, 2010, just days before the DDoS attacks began. The notation listed next to the payment receipt? “Engel.”





After charging these two cybercriminals you will have no information to posts in your blog, except such popular topics as ‘how to choose strong password’ and ‘how to not infect your computer by software cracks’
Unfortunately, there will always be somebody to take their place – even assuming that Vrublevsky will finally be arrested and jailed.
That would be nice. As Wladimir notes, not gonna happen.
Even if Vrublevsky is jailed that will not be the end of internet crime. Krebs will always have plenty to report on.
So I’m guessing his bribe money to the Russian government ran out?
It’s kind of bizarre to see them taking cybercrime seriously.
Bulletproof server facilities for the military are drawing too much attention due to the presence of financial criminal activity in those same facilities.
Ok – I may be being picky or completely missing the point… but you say,
“Group-IB said Artimovich’s botnet also was used to attack several rogue pharmacy programs that were competing with Rx-Promotion, including Glavmed and Spamit ”
But after that statement Glavmed and Spamit are referred to as one entity. Are they really two or just one?
Other than my confusion over that – I think it’s a great article! It’s good to hear that there’s a possibility action will be taken. It’ll be an interesting story to follow and see what happens. If more people start having negative consequences perhaps the pool of people trying to do such shadey things will shrink… there will always be someone I’m sure – but I’d love to see it be less.
@T.Anne — The leaked Glavmed database was enormous, and it was split up into two big bases: One called Shop , and another Shop_IT. It appears (although it’s not certain) that the affiliate info and sales in the Shop database were from Glavmed, which primarily consists of affiliates who are using black SEO techniques, creating doorway domains, and hacking sites to promote pharma pages. The other subdatabase is thought to be connected with sales and affiliates from Spamit.com, a far more exclusive program under Glavmed whose members more frequently promoted pharma sites via spam.
The spamit.com forum (under a variety of domains) is not longer active. However, the Glavmed program and user forum continues, albeit as a shadow of its forum self.
Hope that helps.
Thanks for the clarification Brian!!
I was kinda interested to see “what’s being talked about on https://spamplanet.org/ but later i came to know that its an invite only board. still, nice information as always.
Daily I come to the site to read the new articles and this saga has been fascinating to watch unfold. Truly this has the makings of a Hollywood movie with the seedy hacker underworld, the gangster mentality and cut-throat competition of once business partners, now turned enemies bent on destroying each other.
Brian I suggest you start writing the book/script today!
It worked pretty well for “Middle Men”, a movie just might work here too.
I wouldn’t want to be Vrublevsky’s attorney, trying to explain to him about “the right to remain silent.” 😉
vrublevsky is taken off a flight and detained
What’s your source for that?
redeye arrested in SVO (Moscow)
http://ko-shirshov.livejournal.com/12936.html
I received word from a highly reliable source that Pavel returned to Russia today and was arrested.
http://translate.google.com/translate?js=n&prev=_t&hl=en&ie=UTF-8&layout=2&eotf=1&sl=auto&tl=en&u=http%3A%2F%2Flenta.ru%2Fnews%2F2011%2F06%2F24%2Farrest%2F
My source was from a senior official in the FBI.
Another point of view
http://dmitryart1985.livejournal.com
While I am as happy as anyone that Russian law enforcement is finally taking action against internet crime, I don’t want to see it done in such a manner as to make the validity of any verdicts questionable. Isn’t there any right like “habeus corpus” in modern Russia?
Krebs, you are down.