Criminals have developed a component of the ZeuS Trojan designed to run on Google Android phones. The new strain of malware comes as security experts are warning about the threat from mobile malware that may use tainted ads and drive-by downloads.
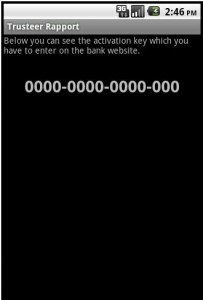
Researchers at Fortinet said the malicious file is a new version of “Zitmo,” a family of mobile malware first spotted last year that stands for “ZeuS in the mobile.” The Zitmo variant, disguised as a security application, is designed to intercept the one-time passcodes that banks send to mobile users as an added security feature. It masquerades as a component of Rapport, a banking activation application from Trusteer. Once installed, the malware lies in wait for incoming text messages, and forwards them to a remote Web server.
Trusteer published a lengthy blog post today that mentions an attack by this threat “that was used in conjunction with Zeus 2.1.0.10. The user was first infected with Zeus on their PC and then Zeus showed the message requesting the user to download the Android malware component.” In a phone interview, Trusteer CEO Mickey Boodaei said crooks used the Trojan in live attacks against several online banking users during the first week of June, but that the infrastructure that supported the attacks was taken offline about a month ago.
Boodaei offers a bold and grim forecast for the development of mobile malware, predicting that within 12 to 24 months more than 1 in 20 (5.6%) of Android phones and iPads/iPhones could become infected by mobile malware if fraudsters start integrating zero-day mobile vulnerabilities into leading exploit kits.
The last bit about exploit kits is key, because almost all mobile malware developed so far uses some type of social engineering to install itself on a device. Boodaei predicts a future time when crooks begin incorporating mobile phone vulnerabilities into automated exploit kits like BlackHole and Eleonore, which use security flaws to install malicious software when the user visits a booby-trapped site with a vulnerable device.
Trusteer’s prediction is timely: jailbreakme.com, which allows users to jailbreak their iPads or iPhones by browsing to the site, leverages an unpatched, critical vulnerability in Apple iPhones and iPads. Experts are warning that such exploits could also be used to download and install malware. Meanwhile, the folks that devised the exploit used by jailbreakme.com have issued a program that lets jailbreakers patch the flaw — meaning that until Apple issues an official fix for the bug, people who have jailbroken their iPhones or iPads are potentially more secure than regular users.
Kevin Mahaffey, co-founder and CTO of Lookout Mobile Security, called the Zitmo variant a notable development, but said it is somewhat unsophisticated. Mahaffey said that a more disturbing class of malware is emerging for Android that convinces users to install the application by disguising itself as an in-app advertisement . Dubbed “GGTracker,” this Android Trojan is automatically downloaded to a user’s phone after he or she visits a malicious Web page that imitates the Android Market. According to Lookout, the Trojan is able to sign up victims for a number of premium SMS subscription services without the user’s consent.
GGTracker is a reminder that mobile users need to be just as vigilant about mobile phone threats as they are with a personal computer. That doesn’t mean mobile users need to install antivirus software; common sense and some basic street smarts will suffice. For example, Trojans like GGTracker can be avoided by paying attention to the URL in a browser’s address bar — something users should already be trained to do to avoid phishing scams. The first two rules from Krebs’s Three Basic Rules for Online Safety also apply to the mobile world: If you didn’t go looking for it (in this case Zitmo), don’t install it; if you installed it, update it (let’s hope that Apple will quickly issue a patch for its vulnerability).




After my first experience with a Premium Text on my wife’s cell phone (for something she signed up for on Facebook and provided her number) I disabled this feature with the cell phone carrier. I only noticed it because the $9.95 charge seemed odd on the bill. In this case Verizon. Check with your cell phone company or dig into your account settings if you want to disable Premium Texting services.
My father-in-law is very good at accidentally signing up for such services. Our carrier (Sprint) assured us that we could disable Premium SMS on just his line, but after a year of asking almost every month and being assured that it’s done right *this* time, it’s still disabled on all 5 lines.
This may be a good problem to have for most of the lines on our family plan. Unfortunately, some free services (Google Calendar text reminders) are also blocked.
I’m glad that I have NEVER attempted to use any kind of a ‘cell phone’ to check bank balances, etc.
After all, if I am ‘mobile,’ I would rather trust an ATM for a balance if I need one.
Better slow than dead. LOL
this is NOT about mobile banking with a smartphone, it’s about home banking with your computer… and as an additional security feature your bank sends you an extra SMS code to your mobile which you have to enter into your home banking software for every transaction. this malware tries to catch THESE SMS codes on your phone, so they can manipulate your homebanking software on YOUR PC….
NB I’m not a fanboy… it does remind us that sometimes closed gardens can be a little safer!
Not meaning to be rude but probably doing it anyway… You did see the part where Apple’s walled garden has had an unpatched vulnerability for months, allowing root access to anyone who a) wants to jailbreak their phone b) needs a new codec to watch the dancing bunnies.
You missed the many security problems with the iPhone/iPad banking apps I guess.
@Michse Selba – “this malware tries to catch THESE SMS codes on your phone”
If the malware can do this, it can do anything else.
Regardless, what is the fundamental difference now between a phone and a PC that can prevent the same well known triks in PC world on a smartphone?
We’re disabling all this “premium services” by default for our company mobiles.
Are there any serious companys using this stuff for billing?
Im not aware of any.
greetings
Again Krebs seems to be largely alone in highlighting these problems and we find that particularly frustrating given the gravity of these issues. We wrote to Trusteer on multiple occasions in the last 2 years offering our solution to fix their interface however our communications have been ignored. We think Trusteers’ and other vendors systems that use these mechanisms can work if they implement proper authentication. We note Krebs arguments in previous articles against Virtual Keyboards however it is possible to defend against screen capture by disabling onscreen feed back our interface is designed to allow this to be done. We have released a demo on our site for the windows 7 phone which we have just completed. The key issue is that interfaces need to be proprietary in nature to render the costs of attacking far higher than they now are and the important issue with that is to automate the process of making the interface proprietary so that the costs of implementation are kept to a minimum.
“…Krebs seems to be largely alone in highlighting these problems and we find that particularly frustrating given the gravity of these issues ….”
Seriously? Maybe you only read this blog but even then I just counted 4 different websites linked in this post to people other than Brian that are “highlighting these problems”.
And sorry to inform you of this (well, not really actually as you seem a little … amatuerish) but most interfaces where attacks on virtual keyboards have been proprietary in nature. Perhaps this is why Trusteer just ignores you, who knows.
Well I didn’t say completely I said largely I have read a lot of media commentary globally and this has not been reported elsewhere in the mainstream media but in any case I wonder what your motive is in attacking someone who is actually endeavouring to do something about the problems good luck with that attitude I am sure you are really proud of your efforts.
Another issue with your comments is that you appear to fail to understand the meaning of proprietary. In fact contrary to your assertion the majority of attacks occur on interfaces that use either ascii or unicode number sets which are in the public domain and the main source of the problems.
I have news for ya: infected android and iphones are already sold on ebay with the virus PRE INSTALLED!
Not just eBay. Maybe you remember the scare a couple years ago with electronic picture frames coming from *the factory* with viruses.
It’s “in the news” again. I’ve never tried posting a link here before, but here goes nothing:
Homeland Security: Devices, Components Coming In With Malware (informationweek)
http://www.informationweek.com/news/government/security/231001333
DHS: Imported Gadgets Possibly Include Malicious Software (pcmag)
http://www.pcmag.com/article2/0,2817,2388361,00.asp
(I take exception with this one in the very first paragraph. “A Homeland Security official confirmed … popular American gadgets, are often infected with malicious software.” — not supported by the quote a few lines later.)
A list of all infected official marketplace apps is here: http://insan-it.blogspot.com/2011/08/android-security-year-in-review.html