In July 2011, a customer at a Chase Bank branch in West Hills, Calif. noticed something odd about the ATM he was using and reported it to police. Authorities who responded to the incident discovered a sophisticated, professional-grade ATM skimmer that they believe was made with the help of a 3D printer.
Below is a front view image of the device. It is an all-in-one skimmer designed to fit over the card acceptance slot and to record the data from the magnetic stripe of any card dipped into the reader. The fraud device is shown sideways in this picture; attached to an actual ATM, it would appear rotated 90 degrees to the right, so that the word “CHASE” is pointing down.
On the bottom of the fake card acceptance slot is a tiny hole for a built-in spy camera that is connected to a battery. The spy camera turns on when a card is dipped into the skimmer’s card acceptance slot, and is angled to record customer PINs.
 The bottom of the skimmer device is designed to overlay the controls on the cash machine for vision impaired ATM users. On the underside of that space is a data port to allow manual downloading of information from the skimmer.
The bottom of the skimmer device is designed to overlay the controls on the cash machine for vision impaired ATM users. On the underside of that space is a data port to allow manual downloading of information from the skimmer.
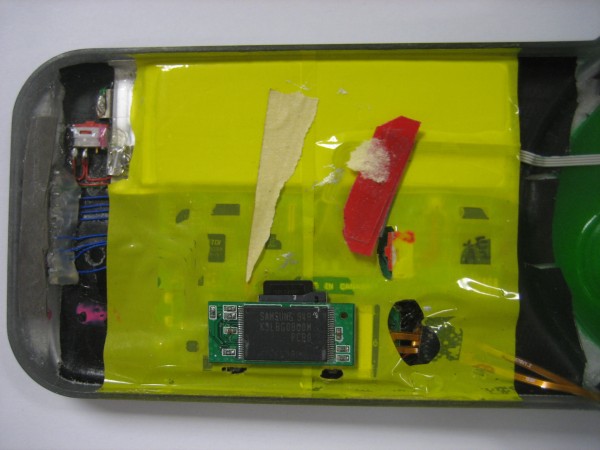
 Looking at the backside of the device shows shows the true geek factor of this ATM skimmer. The fraudster who built it appears to have cannibalized parts from a video camera or perhaps a smartphone (possibly to enable the transmission of PIN entry video and stolen card data to the fraudster wirelessly via SMS or Bluetooth). It’s too bad so much of the skimmer is obscured by yellow plastic. I’d welcome any feedback from readers who can easily identify these parts based on the limited information here.
Looking at the backside of the device shows shows the true geek factor of this ATM skimmer. The fraudster who built it appears to have cannibalized parts from a video camera or perhaps a smartphone (possibly to enable the transmission of PIN entry video and stolen card data to the fraudster wirelessly via SMS or Bluetooth). It’s too bad so much of the skimmer is obscured by yellow plastic. I’d welcome any feedback from readers who can easily identify these parts based on the limited information here.
Here’s a closer look at the circuit board on top, which looks like some type of Flash storage device:
Here’s another look at the electronic parts wedged into the back of the skimmer:
It appears from the following image that the data storage capacity on the device is connected directly to the mag stripe reader (top, silver wire), while the device’s video camera is wedged behind the pinhole (bottom, gold wires).
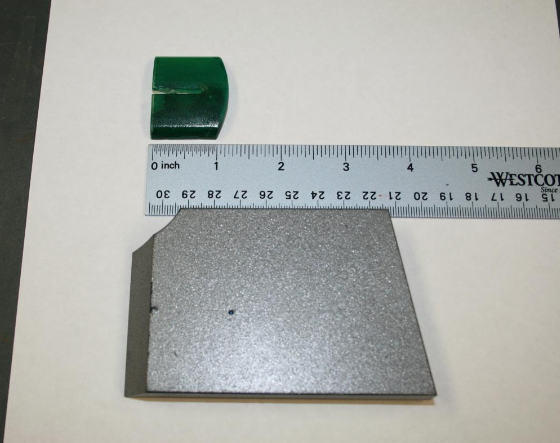
The investigator I spoke with about the incident didn’t know much about the innards of the device, and said that those responsible have not yet been caught. But he did have something interesting to tell me about the origins of the skimmer: “It is believed that the green skimmer was made with the Stereolithography process.” Translation: The cops think thieves produced the card skimmer molds with the help of 3D printers.
These hi-tech and costly machines take two dimensional computer images and build them into three dimensional models by laying down successive layers of powder that are heated, shaped and hardened. In September, I detailed how U.S. investigators had arrested four men in Texas who allegedly built their ATM skimmers using a 3D printer they’d purchased with the proceeds of their skimming business.
In related news, New York County District Attorney Cyrus Vance earlier this month announced an 81-count indictment against three men suspected of planting skimmers at ATM machines in Manhattan. The indictment alleges that the men used the skimmers to steal the debit card numbers of nearly 1,500 individuals, and then exploited the stolen debit card numbers to make more than $285,000 in fraudulent transactions.
In the press release that accompanied the indictment, the district attorney released several images of the skimmer devices allegedly planted by the Manhattan trio. While these devices relied on a separate façade that held a hidden video camera to record customer PINs, there is little question that the same Chase ATM design was targeted. In the picture below, the hidden camera is the squarish silver block mounted vertically to the left of the PIN pad. An enlarged picture of the camera façade follows this one.
If you visit a cash machine that looks strange, tampered with, or out of place, then try to find another ATM. And remember, the most important security advice is to watch out for your own physical safety while using an ATM: Use only machines in public, well-lit areas, and avoid ATMs in secluded spots. Also, cover the PIN pad with your hand when entering your PIN: That way, if even if the thieves somehow skim your card, there is less chance that they will be able to snag your PIN as well.
If you liked this post, consider checking out the other stories in my ATM skimmer series, All About Skimmers.










an astonishing level of sophistication that the Bernard Madoffs of Wall Street and big business couldn’t match on their best day.
According to Samsung’s website, the chip shown is a 32G Nand FLASH memory.
http://www.samsung.com/global/business/semiconductor/productInfo.do?fmly_id=672&partnum=K9LBG08U0M&xFmly_id=157
or
http://www.samsung.com/global/business/semiconductor/partnumberSearch.do?webpartnum=K9LBG08U0M&cdnpartnum=&ppmi=PartnoSearch
Now this is purely speculation, but I’d guess the chip with board were lifted out of a memory card, eg SD or microSD.
That board’s not from a memory card; memory cards don’t have TSSOP packages inside them (they’re too thin). Rather they use bare dice. This looks like part from a video camera that has internal flash; there appears to be an SD card slot on the other side of the PCB, with a card fitted.
So much for covering the keypad when using an ATM and tugging on the card slot to make sure it is legit….I just learned that despite these measures my ATM card was compromised and 10 withdraws were made over two recent days in Bogota, Colombia. I have used this ATM card in Colombia before, but the last time was in February 2011. I had also used it 3-weeks earlier in Buenos Aires and had problems with an ATM at Ezeiza and at another ATM at a hotel. Both ATMs were owned by the bank that issued my debit card and as mentioned above I always tug on the card slot and cover the key pad with my hand….not a great Christmas present….
Sorry to hear that BL!;
I guess that is why they use these new devices. They fit just like the original, and won’t be knocked loose. The 3D printing assures that.