The recent data breach at Adobe that exposed user account information and prompted a flurry of password reset emails impacted at least 38 million users, the company now says. It also appears that the already massive source code leak at Adobe is broadening to include the company’s Photoshop family of graphical design products.
In a breach first announced on this blog Oct. 3, 2013, Adobe said hackers had stolen nearly 3 million encrypted customer credit card records, as well as login data for an undetermined number of Adobe user accounts.
At the time, a massive trove of stolen Adobe account data viewed by KrebsOnSecurity indicated that — in addition to the credit card records — tens of millions of user accounts across various Adobe online properties may have been compromised in the break-in. It was difficult to fully examine many of the files on the hackers’ server that housed the stolen source because many of the directories were password protected, and Adobe was reluctant to speculate on the number of users potentially impacted.
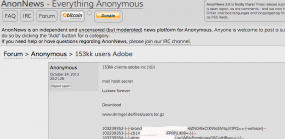
But just this past weekend, AnonNews.org posted a huge file called “users.tar.gz” that appears to include more than 150 million username and hashed password pairs taken from Adobe. The 3.8 GB file looks to be the same one Hold Security CISO Alex Holden and I found on the server with the other data stolen from Adobe.
Adobe spokesperson Heather Edell said the company has just completed a campaign to contact active users whose user IDs with valid, encrypted password information was stolen, urging those users to reset their passwords. She said Adobe has no indication that there has been any unauthorized activity on any Adobe ID involved in the incident.
“So far, our investigation has confirmed that the attackers obtained access to Adobe IDs and (what were at the time valid), encrypted passwords for approximately 38 million active users,” Edell said [emphasis added]. “We have completed email notification of these users. We also have reset the passwords for all Adobe IDs with valid, encrypted passwords that we believe were involved in the incident—regardless of whether those users are active or not.”
Edell said Adobe believes that the attackers also obtained access to many invalid Adobe IDs, inactive Adobe IDs, Adobe IDs with invalid encrypted passwords, and test account data. “We are still in the process of investigating the number of inactive, invalid and test accounts involved in the incident,” she wrote in an email. “Our notification to inactive users is ongoing.”
Part of the Adobe breach involved the theft of source code for Adobe Acrobat and Reader, as well as its ColdFusion Web application platform. Among the cache was a 2.56 GB-sized file called ph1.tar.gz, but KrebsOnSecurity and Hold Security were unable to crack the password on the archive. Over this past weekend, AnonNews.org posted a file by the same name and size that was not password protected, and appeared to be source code for Adobe Photoshop.
Asked about the AnonNews posting’s similarities to the leaked source code troves discovered by this publication in late September, Adobe’s Edell said indeed that it appears the intruders got at least some of the Photoshop source code. In both cases, Adobe said it contacted the sites hosting the data linked to from the AnonNews postings and had the information taken down.
“Our investigation to date indicates that a portion of Photoshop source code was accessed by the attackers as part of the incident Adobe publicly disclosed on Oct. 3,” Edell wrote.
FREE CREDIT MONITORING?
As many readers have pointed out in comments on previous KrebsOnSecurity posts, Adobe has offered a year’s worth of credit monitoring to customers whose encrypted credit card data was stolen in the breach. As it happens, Adobe’s offering comes through Experian, one of the three major credit bureaus and a company that is still reeling from a security breach in which the company was tricked into selling consumer records directly to an online identity theft service.
One of the most frequently asked questions I receive involves whether readers should take advantage of credit monitoring services, particularly those offered for free by the major credit bureaus in response to some breach. My response is usually that free credit monitoring generally can’t hurt, as long as you’re not automatically signed up for a non-free monitoring service after the free period expires. Monitoring especially makes sense if you’ve been the victim of ID theft before.
But bear in mind that having your credit card information stolen is not the same thing as identity theft — which generally involves the fraudulent opening of new accounts in your name. Some types of ID theft involve the creation of synthetic identities — using parts of your personal information combined with some aspects that are not yours — and credit monitoring services may have a hard time detecting these types of accounts.
For consumers reacting to news about their credit or debit card being compromised, it probably makes more sense to opt for placing fraud alerts and obtaining free copies of your credit report several times annually, as specified by law. And remember that the card associations all have zero-liability policies.
A big part of monitoring your credit involves checking your credit file for oddities and errors. The credit bureaus would prefer that you purchased a copy of your credit report from them (the annoyingly catchy commercials for freecreditreport.com, for example, are advertisements for Experian’s service). But this is completely unnecessary. U.S. consumers are entitled to a free credit report from each of the three major bureaus once per year, via annualcreditreport.com. That means that roughly every four months, you should be able to get an updated copy of your credit report from one of the three bureaus (calendar reminders come in handy here).
But back to the question about credit monitoring: Having been the recipient of a large number of attempts to open new lines of credit in my name, I have chosen to take advantage of a credit monitoring service, but it is not one of the services offered by the three bureaus (and I’ll leave it at that). The main reason for this is that if you run into a situation (as I am in now) where particular credit grantors consistently fail to remove fraudulent credit inquiries that negatively affect your credit score and file, you may eventually need to take that up directly with the credit bureaus.
While it may be tempting to believe that paying Experian or one of the other credit bureaus (Equifax or Trans Union) to monitor your file might make them more likely to help you in this situation, there is absolutely nothing in the fine print that says they will. Also, remember that these are the same companies that are tricking consumers into paying for free credit reports and making money hand over fist selling your credit information to would-be creditors and marketers (or in the case of Experian, even to ID theft services).
As mentioned earlier, consumers also are entitled to place a fraud alert on their credit files, and to require that potential creditors first get the consumer’s approval — such as via a phone call — before granting any new lines of credit. The protections are more strict if consumers can show they’ve been victims of identity theft – in that case the fraud alert stays in the files of identity theft victims for seven years. While a regular fraud alert expires after 90 days, consumers can simply renew the alert online when the old one expires. The credit bureau with which you file the alert is required by law to share it with the other two agencies.
Finally, consumers always have the option of placing a security freeze on their credit file — which blocks creditors from accessing your credit reports until the freeze is lifted. It generally costs $10 to place a freeze and another $10 to thaw it if you ever want to buy a new car or open a new line of credit. This may sound like a hassle, but it may ultimately make more sense than paying $15 a month for a credit monitoring service, or trying to remember to file new fraud alerts every 90 days.
Update: Oct. 29, 9:26 p.m. ET: Modified paraphrasing of Edell’s comment on completing the notification campaign, from “..to contact existing users whose login and encrypted password information was stolen,” to the current text.




What kind of hash was used for the passwords? Hope they were using some salted hash, otherwise this 150 million large dump will be a goldmine for many people …
mainly contact spammers. they will use this data in hopes that these people used the same name and password for their email accounts as well. if so – all of these email accounts with have spam sent to their contacts list (to make it seem the mail is coming from family/friends etc)
I stay on top of ID Fraud news and was not shocked when I got a letter notifying me of the Adobe hack.
Like you, I’ve opted to get my monitoring done by a company I trust, who remains outside the fray.
Adobe has become quite ubiquitous and it seems there are no easy alternatives to replace them with.
Brian, thanks for your digestible and informative straight talk for everyday consumers and families!
Dale wrote:
> I’ve opted to get my monitoring done by a company I trust
If Brian Krebs ever offered a monitoring service, he’d immediately have LOTS of business, maybe even rule the market!
Beyond the immediate value of the data – the prospect of accessing compromised accounts, security breaches like this gift hackers with other important information notably the strategies people are employing to generate passwords. Organisations should be discouraging the practice of generating human rememberable passwords, the secureness of such practices has expired. Instead we should be looking to the security industry for alternatives.
what do you know about security? you are just some webdesigner.
Nice.
And how does that articulate anything useful for the discussion ?
Whether a password is “human-rememberable” is irrelevant. People don’t crack passwords; machines do — and machines don’t care whether a password makes sense to a person.
A $5k computer/software combination can test every possible 8-character ASCII combination in minutes, whether it’s “human-rememberable” or not.
Length, not complexity, is the best password strategy.
That’s not exactly true. Length AND complexity is the best.
Look at this article. A sentence coming from the bible or Wikipedia is not necessarily stronger because it’s longer. The best combination is a long password with completely random characters.
Yep! Sure you’re not an expert? 🙂
One time passwords wont work. Everyone carrying around an RSA type device is not feasible and too technologically advanced for most IT personnel to manage.
PKI / CAC cards may be the way to go, but that too requires a lot of care and feeding as well…..
My point is simple, not matter the type of authentication, the machine needs to be 100% clean of anything malicious – known or unknown for it to work effectively.
There is too much emphasis on “security” when there are hundreds of thousands, if not millions of computers on networks and on the web that are poisoned. You have to control the bleeding before you can assess a new way of doing business.
I think the reason so much emphasis is placed on “security” is because most IT techs prefer to assume the worst case, and admit that they are working in an infected environment. So good kernel based solutions that can operate in that environment without giving in totally to that reality are preferred. I don’t know any system administrators who do not try to the up most to keep their systems squeaky clean – but in reality, they have to admit it is clean today, then probably dirty again in 60 seconds.
Just adding this here for interest.
http://www.experian.com/hitwise/press-release-adobe-hitwise-partnership.html
Experian and Adobe expand partnership to include Hitwise and Adobe SiteCatalyst data exchange
Adobe uses Recurly for triggering subscription billing, since the article says encrypted cards, was it Adobe’s servers alone that got hit? or was recurly susceptible too?
I got a nice letter from Adobe last week offering me credit monitoring services through Experian. Really? That seems like adding insult to injury.
“Doubling down” in a really bad way….
Thank you Brian for bringing up that crappy freecreditreport(scam).com. It’s just amazing to me in this day and age a clearly membership/paid service can be advertised with stupid jingles and described as “free” and that’s ok with everyone.
I hate those commercials and turn the channel when they come on.
interesting stuff re US legal necessities.
Anyone out there able to supply the same information for UK or EU areas. Same companies, but different legislatures
Like internet users should trust a one year credit monitoring from Experian after the reporting of their data breach which lead to giving P.I.I. to cyber criminals by way of a third party website.
A better site for credit monitoring is creditkarma.com which doesn’t cost anything to the user up front
I started to investigate a security freeze at Experian. https://www.experian.com/consumer/security_freeze.html says “If you want to place a security freeze on your credit file, select your State from the list below and follow the provided information.” The page for my state says “The fee for placing a security freeze on a credit report is $10.” followed shortly by ” If you are 65 years of age or older the fee will be waived. ” The age limitation does not apply to removing the fee. “The fee for temporarily removing a security freeze is $10. There is no fee for victims of identity theft who provide a valid copy of an identity theft report filed with a law enforcement agency. ” “The fee for permanently removing a security freeze is $10. There is no fee for victims of identity theft who provide a valid copy of an identity theft report filed with a law enforcement agency.” Freezing grandma’s and grandpa’s credit could remove them from this modern nightmare.
Also, remember that these are the same companies that are tricking consumers into paying for free credit reports and making money hand over fist selling your credit information to would-be creditors and marketers (or in the case of Experian, even to ID theft services).
The cynics among believe it’s just that Equifax and Trans Union haven’t been found out yet.
Brian – Thanks for reposting the link for the US free credit report site. It would be a great public service if you repost it frequently, any time credit card fraud, etc. is mentioned in your posts.
“The cynics among believe it’s just that Equifax and Trans Union haven’t been found out yet.”
I’ve been waiting for that update too. I followed Brian’s coverage of “The Secret Files”:
http://krebsonsecurity.com/tag/exposed-su/
http://krebsonsecurity.com/tag/exposed-re/
So, I know he saw that the credit reports came from all three bureaus.
It is very frustrating waiting for him to post everything he has learned.
For those considering doing a security freeze; you need to do it with ALL THREE of the credit places.
But the peace of mind it gives is awesome. I have no fear of someone opening any credit in my (or wifes) name and having to clean up that mess…
If you do need to get credit; you ask the place who they use for the credit check and then thaw your credit on just that provider for a short period of time.
In all reality I’ve only had to thaw my credit once with one provider in the last 5 or so years. Best $60 bucks I’ve spent in ages… (@Brian, since you are a target — you would be very well advised to do this — credit monitoring cant help clean up the mess, and if you get in a mess you can be dealing with it for years. Preventing it in the first place is much better idea.)
I’ve often wondered if/when “They” are going to realize how ‘convenient’ it would be to freeze somebody’s credit after taking over somebody’s identity — or just to mess with the person, like some sort of revenge plot twist? It’s my understanding that without releasing the freeze you can’t do much of anything?
I placed a 90 day freeze on my account with all 3 services the day my credit card was stolen. Took near a year to get the freeze removed. I was repeatedly USPS and email spammed with offers to sell all sorts of crap from all 3. They are, somehow, in tandem as I received identical offers from each around the same time.
Filing with the FTC and their respective BBB was a waste of time.
The big 3 do not want to be regulated – I would say that the best method of getting even with them is to lobby your congressman about how it is high time we started kicking butt at the credit reporting agencies. Many times in history I’ve read that our representatives say one of the saddest things in this world is that no one thinks of contacting their US congressmen. They have more time on their hands to help the voters, than a Senator does. I’ve had pretty good luck myself along this line.
Dropping a line at the CFPD may interest the Director of the Consumer Financial Protection Bureau too! I hear Richard Cordray is like a junk yard dog on consumer concerns! ]:)
I often counsel clients on the fact they can get free credit reports from the big three reporting agencies; but I’m lazy and bought monitoring from my password management company. I get alerts instantaneously the second they hit one of the agencies.
It would make this more redundant if they issued a short snail-mail report each time as well – in case your IT services(e-mail, etc.) have been compromised – however, none of the similar services I’ve investigated will offer both – only one or the other.
Similar situation here as JCitizen – I found out about the Adobe breach on the twitter feed of the password manager I use (PasswordBox – great, totally recommended), so I was able to be proactive about it and change the password right away.
They do make life easier! 🙂
How about using Password Haystack tool
https://www.grc.com/haystack.htm
Nice one . Here is the result for my password .Good luck to crack that .
Online Attack Scenario:
(Assuming one thousand guesses per second) 12.13 trillion trillion centuries
Offline Fast Attack Scenario:
(Assuming one hundred billion guesses per second) 1.21 hundred thousand trillion centuries
Massive Cracking Array Scenario:
(Assuming one hundred trillion guesses per second) 1.21 hundred trillion centuries
That’s nothing a $5 wrench couldn’t take care of in just a few minutes. 🙂
So True .Everything looks good on the paper . But In reality its a very different story .
I still prefer Iron on the face , it Works like magic every time , and its a very fast and officiant way to crack passwords , its only takes about 5-7 minutes max . Success rate is about 99.5 % 🙂
What exactly is a valid encrypted password and what is an invalid encrypted password? If they are encrypted then how do they determine whether they are valid or not?
There is none.There always a loopholes.
take all the software company’s and viruses scanners combined and there usely hours or days behind
Sadly, if a customer uses Adobe’s Software As A Service (“Creative Cloud”, they are required to store their credit credentials on the Adobe site. Sadder still, this is the only way they now offer their Creative Suite of products. I hope Adobe learns from this failing in their business and reverts to offerings of software I can download, install and use without the dreaded “Creative Cloud”. I’m still using the last “pre-cloud” version and have no plans to ever “upgrade”.
“And remember that the card associations all have zero-liability policies.” – it is true only in Americas, maybe only in USA. In Europe it is definitely False, in Europe cardhholder has limited or zero liability in case of fraud.
I have terrible credit. Not a good thing, but that brings a sort of peace of mind.
“You know your credit is bad when an identity thief sues you for ruining his life.” 🙂
This is the reason why I prefer commerce sites that have “guest” checkout.
Oh snap, Adobe “requires” you have an ID so they can bill you monthly for the bloated, monopolistic, creative storm cloud.
Never had to worry about this before…
Look, I got the email (to reset and update pwd) and the letter for Experian and LifeLock. How much will that cost Adobe… but why I have to pay to protect myself from someone’s failure to protect my information, because their EULA is BS?
I am an Adobe Creative Cloud subscriber who received the letter from Adobe saying I could have a free year of credit monitoring from Experian. When I went to the designated website to claim it, the site told me the redemption code in the letter from Adobe was invalid.
Is there any Adobe customer out there who has successfully obtained the “free” credit monitoring?
I think the same company that runs healthcare.gov is running that Adobe redemption program. Harhar
My redemption code worked.
I stopped dead in my tracks when ProtectM ID.com (Experian) forced me to enter my full social security number in order to register.
Umm….nope.
Am I the only one with “trust issues”?
Dale, I’m right with you on that. SS# is for tax purposes only (says so right on my card). It should never be used as an identifier.
Yes. Call them up and they will give you a different link. I had the same problem. Once you got the right link, you will be able to use the code. The link in the letter must be old.
A Chinese company should be releasing “Panda Shop” any day now. 100% compatible with Photoshop.
Adobe Shockwave Player 12.0.5.146 Flash Player : 11.9.900.149
😀
There was a new release of Shockwave Flash this morning with the version number as you indicated for it, but the version number referenced in your comment for Flash Player seems not to be correct, based upon Adobe’s general distribution webpage (below) with links to full installer files which still has v11.9.900.117 as the latest version for both AX and non-AX flavors.
http://www.adobe.com/products/flashplayer/distribution3.html
http://labs.adobe.com/downloads/flashplayer.html
beta version .better
Builds changes
Runtime Versions
Flash Player Desktop only: 11.9.900.149
AIR Runtime Desktop: 3.9.0.1200
AIR Runtime Android: 3.9.0.1200
AIR SDK & Compiler (now includes iOS7 support): 3.9.0.1200
Authoring
Authoring for Flash Player 11.9
To use the new Flash Player, you will need to target SWF version 22 by passing in an extra compiler argument to the ASC 2.0 compiler:
-swf-version=22.Directions are below:
Download the new playerglobal.swc for Flash Player 11.9
Download and install Flash Builder 4.7 from Creative Cloud: -https://www.adobe.com/products/gaming/tools.html
Backup the existing AIR SDK if you need to restore it later then replace the bundled AIR SDK with the AIR 3.9 SDK. To do this, unzip the
AIR 3.9 SDK to this location:\
MacOS–: /Applications/Adobe Flash Builder 4.7/eclipse/plugins/com.adobe.flash.compiler_4.7.0.348297/AIRSDK
Windows: C:\Program Files\Adobe\Adobe Flash Builder 4.7 (64
Bit)\eclipse\plugins\com.adobe.flash.compiler_4.7.0.349722\AIRSDK\
In Flash Builder, create a new project: File -> New -> project.\
Open the project Properties panel (right-click and chose ‘Properties’). Select\ ActionScriptCompiler from the list on the left.
Add to the ‘Additional compiler arguments’ input: \swf-version=22. This ensures the outputted SWF targets SWF version 22. If you
compile on the command-line and not in Flash Builder, you need to add the same compiler argument.
Some really good ideas, really need to be proactive in this
I have to wonder what kind of firewalls/AVs Adobe uses…..So I can avoid them.
Their products have been known to have security holes in them for a long time. Shouldn’t be surprised their own network does as well. At a every company I’ve been at we do a pentest.
Sometimes it’s a well built system and others it’s not. If not, we went out and got firewalls, Multiscanning AV’s from OPSWAT, and sandboxes from Fire eye. For a company that did $4 billion in Rev. last year there is no excuse.
this probably will be a silly question to most here but… we received a letter from Adobe informing us of the security breach… and the family member the letter was addressed to has absolutely NO IDEA or CLUE why or how their personal information would even be connected to ADOBE.
Will one of you please offer illumination on how personal information ends up with this company?
🙂
The less cynical side of me would say your family member probably purchased or registered with them along time ago…
But Unfortunately, it could be because other sites sell information to other companies! So there’s a strong likelihood that that’s how the information came into possession of Adobe.
🙂
Or it could simply be a case where his information came to Adobe through a legitimate acquisition of some smaller company with whom he had previously done business and provided them with that information prior to Adobe gobbling them up. There are many different possibilities, but if he’s really curious and/or concerned he might ask one of his friends who is an attorney to send a formal request to Adobe (just a letter, not an actual lawsuit) for an explanation and clarification. That might not come back to him very quickly, but then again Adobe’s legal department couldn’t simply ignore it completely at the risk of some later elevation to a real lawsuit.
This whole issue seems to have been handled badly and even though Adobe are trying to explain the issues, they keep getting the message wrong!
Personally, I stay on top of ID theft and fraud information so I wasn’t too surprised when I received a letter notifying me of the Adobe hack.
I’ve opted to get my monitoring done by a company I trust.. and it’s not one that’s mentioned here!
The password file has password hints and all passwords that are the same hash to the same string. You can easily work out any common password from the set of hints you get. There are password hints like “the usual one” so a lot of reuse is there. A lot of people will be hacked.
38 mln. is some serious number. Abose should be really hiding now.
It’s far more than 38 million. Take a look here, you can see if your data is in the list: http://adobe.breach.il.ly