Last weekend, Target finally disclosed at least one cause of the massive data breach that exposed personal and financial information on more than 110 million customers: Malicious software that infected point-of-sale systems at Target checkout counters. Today’s post includes new information about the malware apparently used in the attack, according to two sources with knowledge of the matter.
In an interview with CNBC on Jan. 12, Target CEO Gregg Steinhafel confirmed that the attackers stole card data by installing malicious software on point-of-sale (POS) devices in the checkout lines at Target stores. A report published by Reuters that same day stated that the Target breach involved memory-scraping malware.
This type of malicious software uses a technique that parses data stored briefly in the memory banks of specific POS devices; in doing so, the malware captures the data stored on the card’s magnetic stripe in the instant after it has been swiped at the terminal and is still in the system’s memory. Armed with this information, thieves can create cloned copies of the cards and use them to shop in stores for high-priced merchandise. Earlier this month, U.S. Cert issued a detailed analysis of several common memory scraping malware variants.
Target hasn’t officially released details about the POS malware involved, nor has it said exactly how the bad guys broke into their network. Since the breach, however, at least two sources with knowledge of the ongoing investigation have independently shared information about the point-of-sale malware and some of the methods allegedly used in the attack.
‘BLACK POS’
On Dec. 18, three days after Target became aware of the breach and the same day this blog broke the story, someone uploaded a copy of the point-of-sale malware used in the Target breach to ThreatExpert.com, a malware scanning service owned by security firm Symantec. The report generated by that scan was very recently removed, but it remains available via Google cache (Update, Jan. 16, 9:29 a.m.: Sometime after this story ran, Google removed the cached ThreatExpert report; I’ve uploaded a PDF version of it here).
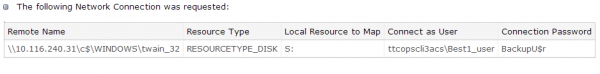
According to sources, “ttcopscli3acs” is the name of the Windows computer name/domain used by the POS malware planted at Target stores; the username that the malware used to upload stolen data data was “Best1_user”; the password was “BackupU$r”
According to a source close to the investigation, that threatexpert.com report is related to the malware analyzed at this Symantec writeup (also published Dec. 18) for a point-of-sale malware strain that Symantec calls “Reedum” (note the Windows service name of the malicious process is the same as the ThreatExpert analysis –“POSWDS”). Interestingly, a search in Virustotal.com — a Google-owned malware scanning service — for the term “reedum” suggests that this malware has been used in previous intrusions dating back to at least June 2013; in the screen shot below left, we can see a notation added to that virustotal submission, “30503 POS malware from FBI”.
The source close to the Target investigation said that at the time this POS malware was installed in Target’s environment (sometime prior to Nov. 27, 2013), none of the 40-plus commercial antivirus tools used to scan malware at virustotal.com flagged the POS malware (or any related hacking tools that were used in the intrusion) as malicious. “They were customized to avoid detection and for use in specific environments,” the source said.
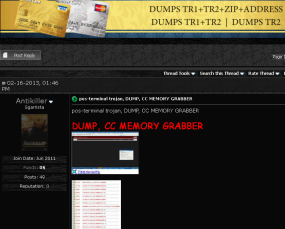
 That source and one other involved in the investigation who also asked not to be named said the POS malware appears to be nearly identical to a piece of code sold on cybercrime forums called BlackPOS, a relatively crude but effective crimeware product. BlackPOS is a specialized piece of malware designed to be installed on POS devices and record all data from credit and debit cards swiped through the infected system.
That source and one other involved in the investigation who also asked not to be named said the POS malware appears to be nearly identical to a piece of code sold on cybercrime forums called BlackPOS, a relatively crude but effective crimeware product. BlackPOS is a specialized piece of malware designed to be installed on POS devices and record all data from credit and debit cards swiped through the infected system.
According the author of BlackPOS — an individual who uses a variety of nicknames, including “Antikiller” — the POS malware is roughly 207 kilobytes in size and is designed to bypass firewall software. The barebones “budget version” of the crimeware costs $1,800, while a more feature-rich “full version” — including options for encrypting stolen data, for example — runs $2,300.
THE ATTACK
Target has yet to honor a single request for comment from this publication, and the company has said nothing publicly about how this breach occurred. But according to sources, the attackers broke in to Target after compromising a company Web server. Somehow, the attackers were able to upload the malicious POS software to store point-of-sale machines, and then set up a control server within Target’s internal network that served as a central repository for data hoovered by all of the infected point-of-sale devices.
“The bad guys were logging in remotely to that [control server], and apparently had persistent access to it,” a source close to the investigation told KrebsOnSecurity. “They basically had to keep going in and manually collecting the dumps.”
It’s not clear what type of software powers the point-of-sale devices running at registers in Target’s U.S. stores, but multiple sources say U.S. stores have traditionally used a home-grown software called Domain Center of Excellence, which is housed on Windows XP Embedded and Windows Embedded for Point of Service (WEPOS). Target’s Canadian stores run POS devices from Retalix, a company recently purchased by payment hardware giant NCR. According to sources, the Retalix POS systems will be rolled out to U.S. Target locations gradually at some point in the future.
WHO IS ANTIKILLER?
A more full-featured Breadcrumbs-level analysis of this malware author will have to wait for another day, but for now there are some clues already dug up and assembled by Russian security firm Group-IB.
Not long after Antikiller began offering his BlackPOS crimeware for sale, Group-IB published an analysis of it, stating that “customers of major US banks, such as such as Chase (Newark, Delaware), Capital One (Virginia, Richmond), Citibank (South Dakota), Union Bank of California (California, San Diego), Nordstrom FSB Debit (Scottsdale, Arizona), were compromised by this malware.”
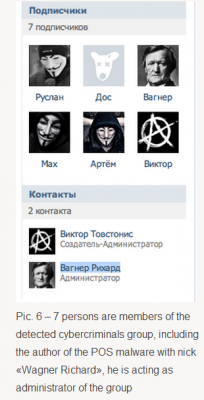
In his sales thread on at least one crime forum, Antikiller has posted a video of his product in action. As noted by Group-IB, there is a split second in the video where one can see a URL underneath the window being recorded by the author’s screen capture software which reveals a profile at the Russian social networking site Vkontakte.ru. Group-IB goes on to link that account to a set of young Russian and Ukranian men who appear to be actively engaged in a variety of cybercrime activities, including distributed denial-of-service (DDoS) attacks and protests associated with the hackivist collective known as Anonymous.
One final note: Dozens of readers have asked whether I have more information on other retailers that were allegedly victimized along with Target in this scheme. According to Reuters, “smaller breaches on at least three other well-known U.S. retailers took place and were conducted using similar techniques as the one on Target.” Rest assured that when and if I have information about related breaches I feel confident enough about to publish, you will read about it here first.




Part of the problem is that administrators are often loathe to secure machines properly because in the long run the current security scheme sucks.
For example, one particular log management SEIM REQUIRES administrator access. Kind of stupid I know.
There are reports in the media that the stolen data contains phone numbers and/or email addresses…. neither of which is on the mag stripe or accessible to a POS reader.
Personally I think the POS reader story – and the president of Target promoting the smart chip solution in interviews – is just a way of them deflecting attention away from a data centre breach.
+1
Don’t blame the admins, blame the developers and managers who don’t enforce ALREADY KNOWN best practices because they are lazy.
Does anyone know what POS Target is using? This is the type of breach that I’m concerned about. It’s that gap between when the card is swiped and when it is encrypted.
Not sure what they were using. There are many vendors of encrypting terminals. Some even have technology that hardware encrypts the data in the reader head itself. Tough to crack that.
It doesn’t matter really what the POS system is using, unless the software at the terminal is sending the encrypted data directly to the processor. Most of the POS breaches happen at the server, where the encrypted card data is sent to the server, then has to be unencrypted, then re-encrypted to the processors format for approval. During that time, the card number is in memory unencrypted. When the process memory is dumped (without affecting the process) it is then scanned for expression matches that gets the card numbers. A good protection is using a qualified POS installer that has years of experience keeping bad guys out. A bad protection is hiring an IT company who uses lazy remote access softwares and does not understand the POS environment.
Would segmentation of the POS systems (firewalls/VLANs) helped for the malware to not infect the POS systems themselves?
VLAN / network management would have helped insulate this attack from succeeding. There’s no way that a compromised webserver that was accessible from the outside should have granted them access to their POS systems. That is lunacy.
Agree 100%…. Doubtful any Target Web server is hosted on the corp. Network.
And yet, looney things like this happen all the time. Take the Bit9 breach, for example. And that was a security company!
http://krebsonsecurity.com/2013/02/bit9-breach-began-in-july-2012/
We’ve failed to provide adequate computer and network security. I think it is important to discuss the possibility that the decisions to fail so have been tactical. And the blame for such tactical decisions is spread across all significant institutions responsible. Personally, I am a short step from concluding that the significant institutions who are responsible for consumer and citizen digital security simply don’t want it.
Heartland’s payment network was segmented off from their corporate network and still got breached due to a hijacked VPN connection between the two.
Heartland’s payment network was segmented off from their corporate network and still got breached due to a hijacked VPN connection between the two.
Indeed. But Heartland had so many other problems that at that point if it were not a hijacked VPN it would have been something else.
I’ve been frustrated at the fact that people keep wanting to say there are massive similarities between the Target hack and the Heartland (etc) hacks. Aside from both being very large, the similarities are rather minor, from the methodologies to the off-the-shelf software/malware used to the actual skills and skill levels of the people involved.
The one similarity I would (ironically) mention is that whoever did do the Target hack probably tried to use the Heartland/TJX/etc breaches as ‘lessons’. Which amuses the hell out of me since random everyday people are pushing for ‘details’, especially technical details, about these sorts of hacks — and most of them do not know their asses from their elbows about what any of it means. In other words, public exposes about the methodologies used in TJX, Heartland, etc, contribute to the ‘problem’ and most likely went a long way towards making the Target hack possible in the first place. As do ‘whitehat’ talks on hacking banks/POS systems/demonstrations of RAM scraping malware such as the ones Trustwave have given numerous times. I’ve been enjoying some of the security company attempts at “redaction”, of course, of ‘internal server names’ but seriously, what the hell is the point if you’ve already published it? And what the hell is the point if you’re just creating blueprints for the next people to copycat the malware involved?
If people want these sorts of hacks to be rarer, people need to quit making it so damned easy to copy what other people have done, use other peoples’ exploits, or provide vivid examples of how to commit the crimes in question. And no, you cannot put the ‘genie’ back in the bottle at this point (unless suddenly everybody up and said ‘oh well, let me totally change my multimillion-dollar infrastructure). So where does this leave things?
I suspect I am ‘preaching to the choir’ here, though. 🙂
So who is to blame? Of course the data thieves who pulled off this heist but what liability or fault is elsewhere? The bank robber is too blame for robbing a bank but shat if the bank used a very poor lock at its front door. Is the Bank then liable for the robber breaking in or is it perhaps the lock company that sells easy to break into locks and gives no option for banks to use other kinds of locks. In short what liability does Visa and MasterCard have in using old technology that is easy to steal from rather than bringing into use technology that offers a far better security.
EMV chip card technology has been used around the world for years with its adoption seeing substantially reduced rates of credit card fraud. Yet Visa and MasterCard failed to bring this technology in a timely manner to the United States making now the US the target for international credit card thieves. It’s kind of like selling superior locks for years to major banks around the world for their front doors and leaving all the banks in the US with a simple lock that anyone can open. So who really is at fault for the Target data breach? The store that was sold a poor and insecure lock or the lock seller for continuing to sell an inferior and vulnerable product?
The reason the banks haven’t gone over to a chip and pin card system is simple: it actually costs them less to keep the existing mag stripe system in place than they lose through card fraud. The amount the banks lose each year is only about 5% of their total transaction value; this is less than they calculate it would cost to change over to the new system. So, until such time as either 1) the banks sustain really huge losses, or 2) the government mandates that they change over completely, we’ll be stuck with the mag stripe into the indefinite future.
Your take on Chip card or what is known as EMV, A. Schmidt was true up until about four years ago. Since then the United States has seen an explosion in CC fraud. 3 years ago it was estimated that USA CC fraud ran at $4billion per annum. Estimated United States CC fraud for 2012 was over $6billion. This is a frightening an frankly an unserstainable figure. What has happened is since the rest of the advanced world has adopted EMV the USA has become the weak link in the chain. The USA being the least secure for card technology has become the most favoured nation for CC thieves. Apart from the economic impact on the players in the CC food chain you have the incredible cost to the consumer of identity theft. With every major CC breach you have a sunami of identity theft. For which the CC industry is the cause of because of using defunct highly insecure methodology BUT who do not carry the economic consequences of resultant identity theft for which they should be held liable. Yes the thieves are at fault but so too is the figurative bank manager that leaves his front door open for the thieves to come in.
EMV now is being deployed in the United States but way too late and at a far too slow a pace then what is needed to protect the consumer, merchants and financial institution alike. Those that control the payment system and decided for whatever reason to keep delaying the introduction of a safer payments technology should be held accountable by legislators and the class action lawyers. In my not so humble opinion. In the meantime the payments networks are slowly introducing EMV int the US and by 2016-2017 everyone’s debit and CC will have an EMV chip. But given now the magnitude of consumer exposure to ID theft and the gigantic increase in actual dollar losses ($6billion in 2012) it is high time for fast tracking EMV deployment in the United States. Not doing so is an act of gross negligence on the part of the payments industry.
“Those that control the payment system and decided for whatever reason to keep delaying the introduction of a safer payments technology should be held accountable by legislators and the class action lawyers.”
I keep hearing rumblings that the rollout of EMV will be accompanied by a push (by the banks and card-issuers) to change the liability rules. The suggestion is that a transaction-with-PIN will be presumed to be authorized and that proof of fraud will have to be made by the customer. As opposed to today’s scenario where the bank has to prove that the transaction is genuine.
It is more than rumour LDMalone. It is the plan. Visa and MasterCard have already put in train a liability shift to the machine operators for machines that don’t accept EMV in the USA. This is now forcing all to implement EMV now ahead of the customer roll out of EMV cards. The shift for fraud liability to the customer is not far behind as they have been successful in doing this on other countries. Problem is that while EMV or chip & pin is far safer than mag stripe it is not 100% full proof. EMV stores a person’s PIN on the EMV chip and this has been hacked. Also the system can be tricked into believing a valid card is being used when in fact it isn’t. And that is not to mention that the cards will be dual card’s with a mag stripe still used as a fall back. The UK saw a 50% reduction in cc fraud after the introduction of EMV. But that left a remaining 50% fraud rate of previous rates.
@ Chaya – Your facts are incorrect here.
Problem is that while EMV or chip & pin is far safer than mag stripe it is not 100% full proof. EMV stores a person’s PIN on the EMV chip and this has been hacked. (Not true – no chip has been hacked or compromised that a PIN has been stolen – and all chips are not created equal so some have more counter-measures than others)
Also the system can be tricked into believing a valid card is being used when in fact it isn’t. (Not true if it truely is a chip-based transaction)
And that is not to mention that the cards will be dual card’s with a mag stripe still used as a fall back. The UK saw a 50% reduction in cc fraud after the introduction of EMV. (UK saw a 70% reduction in fraud and during the same period US fraud rates went up by 70% and 42% of world fraud occurs in the US)
I get your points, but the finger still points to the thieves. Target is already suffering from bad publicity and loss of sales.
My issue with people wanting the government to punish them is that same government is never punished for it’s actions yet it’s quick to want to punish a private company. The politicians who are speaking publicly to punish Target are only doing it for political points, because they know it’s popular to bash a big company.
In closing to me blaming Target is lie blaming a woman who was sexually assaulted by saying she shouldn’t have dressed a certain way and shouldn’t have been at a place by herself during certain hours..sure you could blame her for her decisions, but a crime was still committed and she has to suffer what happened to her..so there is no point in blaming her or Target because they were the victims..it’s the criminals we need to go after
Great article… THANK YOU.
It is amazing that the consumer always stays always unprotected
Target and the banks tell you that you are protected and they will give you another card but what email addresses and physical addresses, who will pay to protect those pieces of information.
I’m sorry to let you know, but you home address, phone number, and name is public information that any one can see.
Personal Identifying Information (aka P.I.I.) is not public.
http://en.wikipedia.org/wiki/Personally_identifiable_information
You want to show me that all 110 million people in that breach owned property under their name? Had listed phone numbers?
If the P.I.I came off of the driver’s license from scanning, that is federal law that was broken, DPPA.
If the P.I.I came from financials via the debit card, that is also federal law that was also broken, FCRA.
will Target pay you or me for having a change of address and protecting us from email and mail scams???
When will the government step in and mandate the consumer protection at the adequate level?
why still allowing the use of the old card technology? why not chip technology like the rest of the world? The banks, mastercard and Visa have developed the technology and deployed it in Europe and Australia but they do not want to deploy it to protect the payment information due to their greed
I forget what company provides Target’s POS software, but it’s easy to figure out because there’s copyright notices by the company while the register is booting up.
Target does use VLAN’s to segment various parts of their network. Maybe the routing rules are too lax? Maybe the intruders modified the software deployment server that all registers periodically and automatically receive updates from? This server can also PXE boot up registers and perform complete reinstallation’s of the OS and POS software.
Target registers are mainly NCR hardware and they run an embedded version of Windows.
Most if not all Target stores have a local Microsoft Hyper V server that runs the various store systems as virtual machines; it sounds as if the hackers also had access to this system in order to install their server as a virtual machine for collecting all of the information in a central point that they could then transfer from across the Internet.
They are either very sophisticated hackers that go beyond installing some malware or they bought their way in through of one of the many developers or admins that Target relies on to run their systems.
LT, I will opine the possibility of some assistance provided here via an inside 3rd party to make this happen all to easily.
I think Fair look Cream is so resonable cream. I was looking for some item who can perform on acne on my greasy epidermis with out any negative complication on the epidermis.
I made the decision to use fair look cream as I discovered it finish ayurvedic remedy with no known negative reactions. I must acknowledge, originally, I was a bit frightened but when I used it for a number of several weeks, I get my acne eliminated and a noticeable shine on my experience. I would like to recommend
it for anyone looking to get rid of acne and in common as well. examine this weblink http://www.fairlookcream.com/ to know more about this product
As always a good article. As a security consultant I here the same old BS from developers and application admin all the time” I can’t update or upgrade the OS because it will break my application(s)”
as an auditor NOT MY problem.
My recommendation to these clients is to move towards out of the box solutions with little or no modifications being made, with paid support that is not affected by patching and upgrades. Now this will typically make every developer in the company hate me since there is no job security when companies move away from in house development. Just my two cents…..
You are right. It is amazing the number of big organizations that will not spend $20k for a piece of hardware or software until they get hit with a multi-million dollar breach. The State of SC got burned for saving money that way. I work for a Fortune 20 company that still lives on Win-XP because they are to cheap to upgrade their apps to run on anything newer. In many cases you can not use the Firefox browser for their external online pages.
Last. I am not sure the US is the leading technology country anymore. Too many of our technology companies have become so large they are hide bound by their size when it comes to upgrading computer/communications networks.
I have advocated for some time that organization and businesses be required to carry insurance for IT risks, or that it be excluded from their regular business coverage.
The charge for insurance coverage will vary widely based upon the security practices, as it does for fire suppression etc. Once there is an identifiable charge, based upon risk, then bean-counters can understand spending money to reduce that cost.
Until then, we are just preaching. And financial-oriented managers seldom respond to that.
Oh dear, Brian. Looks like you had an intruder at 06:48 unless you’re branching out into face creams.
This article does not mention that the Target Canada stores running Retalix POS software were not affected at all. Beside the fact that that Canada uses Chip and PIN….the payment terminals are hardware encrypted Point to Point (P2P)….Using this method in the U.S. would have prevented any type of “Memory Scraping.” As soon as Target switches to this method in the U.S. even the magnetic stripe cards will be hardware encrypted as well and will prevent this. Retalix will be in Target U.S. soon.
Lack of quick response shows clearly that the culprit is known and no harm intended (you guessed it) and now they need to spin up stories to blame it on others 🙂
I just received a call from Antigua/Barbuda; let the Target leak scams begin!
http://800notes.com/Phone.aspx/1-268-762-0155
Google McAfee BlackPOS. You will find a brief discussion of dated July 24, 2013. It dismisses this as rather low level not very powerful software. It references several earlier write-ups. PCI Guru quotes the relevant PCI standards that would have protected against this. This is dated May 28th, 2013. The article implies that they already have an AV signature for it. (but of course the bad guys can change signatures every millisecond).
XYLIBOX has a complete dump of what BlackPos does in a posting dated May 28, 2013.
Looks like this was well known and already existing best practices, would have stopped this. But then PCI compliance is just for the auditors, not something we do to actually stop bad guys.
PCWorld has a story dated March 24, 2013. McAfee Warns of Point of Sale Malware. They called it vSkimmer. It reports that it was first seen by McAfee on Feb 13, 2013.
The article points out the Whitelist protection would prevent it from going anything. AV on a POS devices will eventually always loose. But good Whitelist system, properly managed in accordance with PCI standards will protect against this kind of thing. POS systems are simple, closed, well defined systems that are perfect match for Whitelist software.
If indeed the Target hack concerns Windows XP embedded, I’m super interested in knowing more. Microsoft has an April 8th end-of-support deadline for Windows XP and this plays right into the doomsday scenario we’re concerned about. I know that Home Depot is running Windows XP at it’s POS…
Please keep us posted and drill down into the XP comment you have in one of your paragraphs in the story. Many thanks!
Target’s registers do not specifically mention Windows XP when booting up or when hitting Control Alt Delete. The OS look and UI makes it seem to be a product based off of Windows XP, but it’s simply referred to as Windows Embedded. My guess is that support for this version will continue past the date Microsoft will support Windows XP.
However, Target’s other client computers in the company are still on XP. Photo lab, Pharmacy, Wedding/registry kiosks, Hiring kiosks, All office computers, digital signage, etc.
Target is almost entirely a Windows shop. From their registers, most of their servers, to their newer models of price checkers throughout the store, even the PDA’s the team members use.
Another angle to consider in the lack of better POS hardware, etc. is who is providing the current ones in the US and what’s their lobbying spend to keep their products at the register?
A trusted source close to the situation has told me the attack did *not* come through target.com…
Why do we not talk about how lax security is on the store level for retailers such as Target? My company has been contracted numerous times by Target, Walmart, and others to do POS re-imaging server replacements. The contracts have us do the work without requiring a check of qualifications or background checks. One big box chain even contracted us to replace the servers at their local locations. Per contract we took the old servers out of the store to ship at the local UPS store with no requirements to sign them out of the store, to do a memory wipe, or any other form of security. This surprised me because these were the machines handling all credit card transactions. At a Target location we were even given the key to the server room in 2013 and were able to do work without even one employee escorting us. In addition to this, no store employee even asked for identification or a work order. When we told them we were there to do work, the manager handed us the key and pointed the way. I have had the same experience at Old Navy, Walmart, Sallie Beauty, and many more so why do we not see more breaches with such a lax security structure?
I find your comments hard to believe. Im not calling you out, but if true, this is just incredible what you have just stated here. Again, if true, they clearly do not have policies in place to protect HCI data. The thought of a bunch of service providers running around a server room with no escort sitting there overseeing their work and then pulling out machines to ship via UPS! Again, if true, Target has way more issues on it hands that this breach.
In addition, you are dealing with people that sell plastic items from China, these are not Info Sec people. Obviously there has been no security awareness training at the local store level with the store managers/supervisors on the importance of all those flickering LED’s in that closet down the hall.
Again, if all true, this breach is possibly the tip of the iceberg forTarget’s ill’s when it comes to Info Sec right down to the store personnel.
I can confirm that this is indeed how target operates. Although server replacements don’t happen during business hours and store ARE notified prior to a server upgrade/replacement. To add to Marc’s comment, some stores even use the server room for storing shelving, gift cards, and other check out merchandising because they don’t want to have to walk across the store to get those items from the back room. Sometimes access to the room is given to lowest level team members and sometimes the door is left open and the room unsupervised.
Good account of the incident however, the paragraph concerning the “somehow” begs further consideration. The authors of this code must be very clever or very well resourced to pull off a breach of this scale. My guess is the later.
“Somehow, the attackers were able to upload the malicious POS software to store point-of-sale machines, and then set up a control server within Target’s internal network that served as a central repository for data hoovered by all of the infected point-of-sale devices.”
Your point regarding the “somehow” is truly spot-on. There seems to be little investigation into HOW the malware was dsitributed across a substantial portion of the point of sale devices in Target’s network. Further, I’ve seen multiple articles today that indicate that the “sniffed” data was stored on what sounds like a “zombie” server in Target’s protected network. According to these reports, the hackers came back inside to “pull” the stolen data.
My questions……
1. How did the malware get distributed to a large percentage of the Target POS devices? Was the malware “planted” like an easter egg in the base POS code base and then inadvertantly distributed by Target through normal channels?
2. How did Target’s Risk Management/Information Security team miss the exfiltration of this data? The volume of the movements had to be enough to trigger alarms if the teams were monitoring for anomalous NetFlow information.
As a former CTO for a national retailer, I am struggling to understand why these questions are not being pursued. I’ve seen these kinds of attacks, and they are both maddening and chilling when you learn the details.
Thanks Brian for the investigations. But I think you need to go much deeper.
I’m constantly amazed at how many people come here to paste or repeat information that was first printed here. I think I’ve dug about 100 miles deeper than anyone else, thanks.
Agreed… Brian, just stay focus and continue your efforts. Super job!
We need to not only up our security, but we need to have people supervise the ones who are “protecting” our nation. We shouldn’t always be relying on the software that automatically helps us against these viruses and melware in systems. Especially if they had said it was located early last year.
Two Mexican nationals have been arrested in McAllen, Texas in possession of 96 counterfeit credit/debit cards that had been used fraudulently in local retail stores. The police claim that the data used to make the cards came from the Target breach, but federal authorities dispute this, saying there is currently no link between the arrests and the Target investigation. See:
http://www.mysanantonio.com/news/local/article/Couple-arrested-at-border-in-connection-with-5159770.php
Video of the McAllen Police Dept. news conference is on Youtube at:
http://www.youtube.com/watch?v=0DAZSCELBdY
It is reported that 40K POS machine’s in the Target heist had been infected. This obviously was not done by multible insertions at the POS terminal with the malware being then installed one by one on each terminal. The malware must have been either inserted at one POS terminal and then wormed its way into server network or the intrusion was via a single store server connected to the network or an inside job at HQ data processing center. Given previous cc heists at retailers over the years going back to the TJ Max debacle, simply entering into the central HQ server was all that was needed to scoop up everything.
Frankly, it is not quite as simple as claimed.
To have a piece of malware “worming” its way through the protected network requires quite a bit of time and creates an inordinate number of opportunities for the malware to be inadvertently discovered. This inadvertent detection is something most hackers seem to work very hard to avoid.
Further, given the large number of HOSTS found on a corporate network such as Target’s, simply finding a way in is only the start. Most retail IT shops don’t use inviting hostnames like POS_Workstation_1234 to name servers or workstations. In these situations, I have seen quite a bit of surreptitious surveillance undertaken by the hackers simply to FIND a ripe target to attack.
Simply finding one device to compromise and gain entry into the protected network is not enough.
Actually, one device is all that is necessary if the thief has credentials with enough permissions, and knowledge of the infrastructure and host configurations. Liek so many of the other comments, this one is ripe with ignorant assumptions and close-mindid ‘insight’, typacal of it security professionals.
With all due respect, most hackers do not know much about how to avoid inadvertent detection. Most of the time they get lucky, or the administrators (or systems themselves) are just not very security-conscious in the first place.
Statements like “Simply finding one device to compromise and gain entry into the protected network is not enough.” however show even less familiarity with how security in the real world operates (and is yet one in a long line of reasons why tokenised authentication and VPNs are so important for remote access, although far from perfect).
Most ‘harder’ networks are only hardened from the outside, but soft, chewy, and easy to traverse through in the middle because ‘business’ is a lot easier when this is the case (or more specifically, it is a lot harder when this is NOT the case).
The truth is that by allowing internet into and out of a company you are probably going to be compromised eventually, and probably already are and have been for a long time. Businesses would fare better if their security followed more of a ‘sinking ship’ model: close off breached areas to limit the damage; this is part of the idea behind the (imperfect) concept of a DMZ.
What kind of security tools does target and NM use? Did these not find the threat?
If they had been monitoring their traffic they would have noticed stuff going out, from the infected server out to where it wasn’t supposed to go to. Sure it goes undetected in anti virus software. However they could have been able to monitor the data, and noticed that stuff that came from the POS, to the server, was going to places that they weren’t supposed to go to. It doesn’t matter if the hacker is using malware or encrypted data, that you can’t crack. If you are managing that Network, you can still see the data that is going on the wires, and monitor it.
forgot to add that the malware is what goes undetected in anti-virus, that’s what i was referring to in that one sentence or however many it was.
what happened to those carbon paper credit card slider things?