The apparent credit and debit card breach uncovered last week at Home Depot was aided in part by a new variant of the malicious software program that stole card account data from cash registers at Target last December, according to sources close to the investigation.
On Tuesday, KrebsOnSecurity broke the news that Home Depot was working with law enforcement to investigate “unusual activity” after multiple banks said they’d traced a pattern of card fraud back to debit and credit cards that had all been used at Home Depot locations since May of this year.
A source close to the investigation told this author that an analysis revealed at least some of Home Depot’s store registers had been infected with a new variant of “BlackPOS” (a.k.a. “Kaptoxa”), a malware strain designed to siphon data from cards when they are swiped at infected point-of-sale systems running Microsoft Windows.
The information on the malware adds another indicator that those responsible for the as-yet unconfirmed breach at Home Depot also were involved in the December 2013 attack on Target that exposed 40 million customer debit and credit card accounts. BlackPOS also was found on point-of-sale systems at Target last year. What’s more, cards apparently stolen from Home Depot shoppers first turned up for sale on Rescator[dot]cc, the same underground cybercrime shop that sold millions of cards stolen in the Target attack.
Clues buried within this newer version of BlackPOS support the theory put forth by multiple banks that the Home Depot breach may involve compromised store transactions going back at least several months. In addition, the cybercrime shop Rescator over the past few days pushed out nine more large batches of stolen cards onto his shop, all under the same “American Sanctions” label assigned to the first two batches of cards that originally tipped off banks to a pattern of card fraud that traced back to Home Depot. Likewise, the cards lifted from Target were sold in several dozen batches released over a period of three months on Rescator’s shop.
![The cybercrime shop Rescator[dot]cc pushed out nine new batches of cards from the same "American Sanctions" base of cards that banks traced back to Home Depot.](https://krebsonsecurity.com/wp-content/uploads/2014/09/AS6-12-600x558.png)
The cybercrime shop Rescator[dot]cc pushed out nine new batches of cards from the same “American Sanctions” base of cards that banks traced back to Home Depot.
The tip from a source about BlackPOS infections found at Home Depot comes amid reports from several security firms about the discovery of a new version of BlackPOS. On Aug. 29, Trend Micro published a blog post stating that it had identified a brand new variant of BlackPOS in the wild that was targeting retail accounts. Trend said the updated version, which it first spotted on Aug. 22, sports a few notable new features, including an enhanced capability to capture card data from the physical memory of infected point-of-sale devices. Trend said the new version also has a feature that disguises the malware as a component of the antivirus product running on the system.
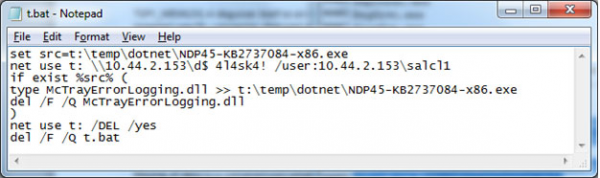
Contents of the new BlackPOS component responsible for exfiltrating stolen cards from the network. Source: Trend Micro.
Trend notes that the new BlackPOS variant uses a similar method to offload stolen card data as the version used in the attack on Target.
“In one the biggest data breach[es] we’ve seen in 2013, the cybercriminals behind it offloaded the gathered data to a compromised server first while a different malware running on the compromised server uploaded it to the FTP,” wrote Trend’s Rhena Inocencio. “We surmise that this new BlackPOS malware uses the same exfiltration tactic.”
An Internet search on the unique malware “hash” signature noted in Trend’s malware writeup indicates that the new BlackPOS verison was created on June 22, 2014, and that as late as Aug. 15, 2014 only one of more than two-dozen anti-malware tools (McAfee) detected it as malicious.
ANTI-AMERICAN MALWARE
Other clues in the new BlackPOS malware variant further suggest a link between the cybercrooks behind the apparent breach at Home Depot and the hackers who hit Target. The new BlackPOS variant includes several interesting text strings. Among those are five links to Web sites featuring content about America’s role in foreign conflicts, particularly in Libya and Ukraine.
Three of the links point to news, editorial articles and cartoons that accuse the United States of fomenting war and unrest in the name of Democracy in Ukraine, Syria, Egypt and Libya. One of the images shows four Molotov cocktails with the flags of those four nations on the bottles, next to a box of matches festooned with the American flag and match ready to strike. Another link leads to an image of the current armed conflict in Ukraine between Ukrainian forces and pro-Russian separatists.
This is interesting given what we know about Rescator, the individual principally responsible for running the store that is selling all of these stolen credit and debit cards. In the wake of the Target breach, I traced a long list of clues from Rescator’s various online identities back to a young programmer in Odessa, Ukraine. In his many personas, Rescator identified himself as a member of the Lampeduza cybercrime forum, and indeed this site is where he alerts customers about new batches of stolen cards.
As I discovered in my profile of Rescator, he and his crew seemed somewhat taken with the late despotic Libyan leader Muammar Gaddafi, although they prefer the phonetic spelling of his name. The Web site kaddafi[dot]hk was among four main carding shops run by Rescator’s crew (it has since been retired and merged with Rescator[dot]cc). The domain kaddafi[dot]me was set up to serve as an instant message Jabber server for cybercrooks, advertising its lack of logging and record keeping as a reason crooks should trust kaddafi[dot]me to handle their private online communications.
When I reached out to Rescator last December to obtain comment about my findings on his apparent role in the Target break-in, I received an instant message reply from the Jabber address “kaddafi@kaddafi[dot]me” (in that conversation, the person chatting with me from that address offered to pay me $10,000 if I did not run that story; I declined). But I also discovered that the kaddafi[dot]me domain was a blog of sorts that hosted some harsh and frankly chilling anti-American propaganda.
The entire three-part manifesto posted on the kaddafi[dot]me home page is no longer available, but a professionally translated snippet of this tirade reads:
“The movement of our Republic, the ideology of Lampeduza – is the opposition to Western countries, primarily targeting the restoration of the balance of forces in the world. After the collapse of the USSR, we have lost this fragile equilibrium face of the planet. We – the Senate and the top people of the Republic are not just fighting for survival and our place under the sun, we are driven by the idea! The idea, which is living in all of us – to return all that was stolen and taken from our friendly countries grain by grain! We are fighting for a good cause! Hot blood is flowing in us, in citizens, who want to change situation in the world. We do not bend to other people’s opinions and desires, and give an adequate response to the Western globalism. It is essential to be a fighter for justice!
Perhaps we would be living completely differently now, if there had not been the plan of Allen Dulles, and if America had not invested billions in the collapse of the USSR. We were deprived of a common homeland, but not deprived of unity, have found our borders, and are even closer to each other. We saw the obvious principles of capitalism, where man to a man is a wolf [[see here for more context on this metaphor]]. Together, we can do a lot to bring back all the things that we have been deprived of because of America! We will be heard!
Citizens of Lampeduza – “free painters” ready to create and live the idea for the good of the Motherland — let’s first bend them over, and then insert deeper!!!





![Google-translated version of Kaddafi[dot]me homepage.](https://krebsonsecurity.com/wp-content/uploads/2014/09/kaddafi-me-600x389.png)

It’s rather interesting that the site Rescator cc uses Cloudflare and they allow a forum to be hidden that supports cyber-crime related to recent retail breaches.
Cloudflare…indeed!
How is Cloudflare’s service not considered aiding a crime? Have they ever commented?
I had a correspondence with Cloudflare the last time the Target cards showed up. They said they weren’t protecting criminals, but after I showed them what they were doing they stopped the protection.
really now, then why are they still using cloudflare
Last year, Brian said something similar about Cloudflare in a Defcon presentation about paid DDoS services which Cloudflare protects. Matthew Prince, the CEO of Cloudflare responded during the Q&A period by coming up to the podium, taking the microphone, and explaining that Cloudflare will not make moral judgements or censor anyone. However, they will always respond to any request that is backed by a court order. Prince is an ex-lawyer, and believes that the legality of web sites should be decided by the court system, and not by any individual or corporation.
For me, that was one of the best moments of Defcon 2013. Sorry Brian, but I think Matthew won that debate.
So if I own a parking lot, does that same logic entitle me to allow car bombs to be placed there without performing “due care” for fear that I might be censoring car bombers? I don’t understand the reasoning here.
Matthew made it into an ad hominem attack on me, which is what people who are on the losing and indefensible end of an argument (and lawyers) typically do. I chose not to stoop to his level.
In my opinion there should be a vetting process applied to site Cloudflare joins as a customer. Protecting a website, who’s main goal is to make money illegally, is absolutely wrong. This isn’t a site that has content which is objectionable to certain people (E.G Crude humor, religion, pornography, etc.), this is a site that’s dealing with the selling of stolen property, which is always illegal.
If you look at it this way, Cloudflare is profiting off the breached cards at Home Depot and Target, by taking money from a site that paid for protection by the sale of stolen credit cards. It’s wrong.
Also, to quote Cloudflare’s own Terms of Use:
“If the investigation reveals any information, act, or omission, which in CloudFlare’s sole opinion, constitutes a violation of any local, state, federal, or foreign law or regulation, this Agreement, or is otherwise deemed harm the Service, CloudFlare may immediately shut down your access to the Service.”
I’d certainly state that running a carder store, or a DDoS service, is a violation of the law and/or harms Cloudflare’s reputation.
They can kick off these scum if they wanted to. They don’t.
By saying you won’t stoop to his level, aren’t you making an attack on his character, thus putting you at his level?
Home Depot confirmed the breach with a new statement:
“Home Depot today finally confirmed that its payment systems have been breached, but a number of crucial questions remain unanswered by the giant home improvement retailer.
In a statement released late this afternoon, Home Depot said customers using payment cards at its U.S. and Canada locations, more than 2,200 in the U.S. alone, could be impacted. Online shoppers have been spared, Home Depot said in its statement.
“While the company continues to determine the full scope, scale and impact of the breach, there is no evidence that debit PIN numbers were compromised,” the statement said.”
Thanks to the Target breach, when I replaced my debit card before any fraud was detected on my account, I have a credit card with a low limit that I use for purchases particularly at big box stores, which seem to be particularly hard hit by breaches. Thanks to Home Depit, I now had to replace this card.
I think I shall write my bank a letter advising them to take Matthew Prince’s advice to heart – and sue the pants off his company for costs related to replacing cards in breach after breach, replacing lost monies, and punitive damages for Cloudflare’s utter disregard for public safety in the financial and personal data arenas.
This would fall under Prince’s doctrine of ‘letting the courts decide,’ I believe.
There is a legal concept known as “willful blindness.” In this case, where a website is actively and openly flouting the law and posting stolen credit cards, CloudFlare would appear to be willfully blind about its customer.
If Cloudflare shut down that illegal credit card forum, then Krebs wouldn’t have nothing to do during the day, therefore, no insightful articles . LOL
Brian would still have plenty to do – there are always ATM skimmers..
I suppose if all of the underground markets went away, there would be no place to go and buy those things either.
I believe it is legal for them to offer their services to CC shops since they do not host any content; they merely provide a proxy service. The CEO, Prince is a lawyer so he’s familiar with the relevant laws.
This isn’t the first and probably not the last website of dubious legality that they offer their services too. In the past they offered their services to lulzsec. Also they protect a couple hamas websites.
I don’t know the legal ramification, except it’s gone on awhile, and the traffic connection must (presently) go through CloudFlare (here let me hold the gun while you pull the trigger).
Any chance you’ll update the list of Zip Codes with these latest cards going up for sale? That really helped as mine wasn’t on the first list. Also, if BlackPOS was created in June, does that mean I’m safe if I used my card at Home Depot on May 24? Thanks for all of your work.
Be sure to search for your store’s ZIP code rather than your home ZIP code (if they aren’t the same, that is).
There is a query limit on the web site containing the cards for sale. There are about 43,000 zipcodes in the US, but only 1,932 of them have Home Depot. Anyway you slice it getting a completely accurate picture of the compromise from the selling web site isn’t likely.
re 43,000
http://www.carrierroutes.com/ZIPCodes.html
re 1,932
http://krebsonsecurity.com/wp-content/uploads/2014/09/hd_zips.txt
Is there a similar list for Canadian postal codes?
http://www.aggdata.com/free/canada-postal-codes
Record Count: 1,620
Last Updated: 03/01/2012
Is there any reason I should doubt that Rescator is a state-sponsored actor?
Yes, the absurdity of his rhetoric… 🙂
A more likely guess, given that Brian tracked him down to Odessa, Ukraine, is that he’s a pro-Russian Ukrainian not happy with the economic life of his country since the collapse of the USSR and not happy with the current neo-Nazi regime (heavily supported by the US.)
I’ve been following the rebellion by the eastern Ukraine against the Western neo-Nazi junta in the last few months and clearly the reference to “American Sanctions” is directed at the sanctions unilaterally (and illegally under international law) imposed by the US on Russia in response to the situation.
This is one (or several) guys attempt to retaliate – and make some money for himself. 🙂 It’s very unlikely that he needs or has received direct assistance from a state actor.
From my seat, absolutely not.
That said, the reason from ascertaining that is guarded by an extremely serious NDA.
I’ll suffice it to say that the Estonia campaign suggested the relationship. The South Ossetia campaign *really* tipped the hand.
So, the “freedom fighter” nonsense is nothing more than bovine excrement served up on rye and called a Reuben. It’s still, erm, fertilizer, not meat.
We’ll suffice it to say, I’m no fan of US or old USSR foreign policies, I was at the spear end of some US side events.
There are no saints here, only plenty of sinners. One of whom is trying to arise from the ashes of being outspent and hence, defeated.
Meanwhile, the two children messed up their “room”, which happens to be our planet, resulting in the foreign policy nightmare we have today.
So, we’re left with a massive mess, planet wide, with various and sundry nations in disarray and one attempting to climb back to lost glory, another rising from long ago European depredations and the US trying to blunder our way forward.
Honestly, I’m trying to figure out how we won’ t eventually end up with radioactive rain, caused by one loose cannon satellite state going rouge with thermonuclear weapons (or worse, network based “WMD” usage being considered equal (which isn’t far from the truth today)).
Got a realistic answer to the problems? Go for it, nations tried and failed in epic manner.
The reality is, it isn’t *only* the US holding the match, it’s a handful of nations equally flipping a strike anywhere match. Their mutual prodding making the gravity greater to try to strike the match, but also the fuel closer to plutonium in the higher gravity whirlpool, awaiting eventual supercritical mass.
Why FBI or NSA not doing anything against such dump sellers. Cyber world have to be more secure now. If Target and Home Dept can’t be trusted than whom should we trust about online payments. Security agencies should have to take strict measures against Them
That is also true that USA is paying price of its War activities in some countries under the Banner of NATO.
FBI and NSA can’t do much in other countries without cooperation of the local government. For some reason Russia is not particularly cooperative. Perhaps they are pre-occupied with their military invasion of a neighboring sovereign country?
I have been using my PayPal account at Home Depot for a couple of years now. It doesn’t require you to swipe, only to time your credentials on the terminal, I wonder if this would have been picked up by the malware. If so they could potentially use this at home depot, but luckily I use an entirely different set of credentials for PayPal in general + 2 factor authentication.
I think we should focus more on the Modus Opreandi and TTPs (Tactics, Techniques and Procedures) of the attackers and less on the malware itself. That’s what we in Aorato tried to do in our report: http://www.aorato.com/blog/untold-story-target-attack-step-step/
An interesting point that confirms the generality of our conclusions is that in attacks against retailers aimed at credit cards, attackers assume that they will be caught. This is a result of a noisy, monetization path that triggers the credit card companies fraud alerts. Therefore, in this attacks. attackers invest less in long lived infrastructure, stealthiness, etc. Specifically in this case, the attackers had gone one step further and planted some propaganda (or a red herring) within their bound-to-get-caught malware.
I thought I recall hearing that Home Depot used Linux, much like their rival, Lowe’s.
Did they have a CIO change to windows POS terminals at some point?
That would be a big error.
http://www.zdnet.com/blog/btl/home-depots-ceo-switch-could-alter-it-strategy/4213
It was in March that I noticed the register at a local store using XP Embedded. It caught my attention at the time, since I knew XP support was ending in April.
XP support has ended…. However, XP embeded is good for a few more years.
http://support.microsoft.com/lifecycle/search/default.aspx?sort=PN&alpha=Windows+XP+Embedded&Filter=FilterNO
XPE and POS Ready 2009 do not lose support or patches until 2016 and 2019 respectively.
As far as I know Home Depot has always used XP for their POS at least as far back as 2005
I wish Home Depot would hurry up shredding all their corporate documents and deleting all their emails tying them to this breach so we can hear their spin about how everything is fine and nothing to worry about. Perhaps they will try to divert blame and say something like: “those unauthorized Home Depot charges you are now seeing on your credit card statement really is not Home Depot’s fault since you undoubtedly shopped at Target or one of the other many retailers suffering, so it will be best to contact those stores for resolution. Thank you for shopping at Home Depot…….”
HD certainly didn’t learn the basics of crisis management – get the news out fast and on your own terms (and hopefully on a Friday).
What do Sally Beauty, Adobe, PF Chang, UPS, Neiman Marcus and now Home Depot all have in common? The company didn’t announce the breaches so they lost the initiative and were responding.
See #2, #6 and #7 from the below and maybe forward them to Home Depot
http://agnesday.com/10-new-rules-crisis-communications-infographic/
On releasing bad news on Friday
http://politicaldictionary.com/words/friday-news-dump/
http://www.slate.com/articles/business/moneybox/2004/09/friday_night_blights.html
Remember too – EMV wouldn’t have helped Target because the malware grabbed the information from RAM in the POS while it was plain text. Would it have helped protect HD? Don’t think so. So why is EMV being “forced”?
EMV would have helped to a degree. While the card number is static, there is other data in the transaction that is dynamic coming from the card. Thus, you couldn’t use that data in a replay attack from another terminal.
In particular, the CVC number that is encoded on the magnetic stripe will not be present in the memory of the POS terminal because with an EMV transaction, the magnetic stripe of the card is not read.
With an EMV transaction, there is in effect a dynamic CVV that is used to demonstrate that the card is actually present, but the number is different for every transaction. Thus if you captured the number from one transaction, it would not be reusable in a different transaction.
So again, still wondering about Canadian HD. But we are mostly EMV chip and pin here. So if they breached the POS here, they would not be reading the mag stripe data hence no CVV. And since most places in Canada are chip and pin that makes fraudulent use of a stolen CC by itself (card replication) not as useful and physical merchandise purchase potential is therefore limited.
That leaves online internet fraud, which as Brian has explained is not as convenient to try and ultimately cash out on.
Just to amplify what Jason is saying … magstripe depends on the POS and the rest of the chain being secure. That turned out to be a bad design! Basically providing Brian with years of material to write about.
EMV corrects that design: the key bits stay on the chard-chip are not sent up to the POS or anything. EMV sends some info to the POS, but not enough to make a duplicate card. So the POS could be 100% corrupt, but the info provided by the chip is not very useful.
I wonder why the US government hasn’t asked any help from the Ukrainian government with arresting this (alleged) criminal. As Ukraine has now turned away from the USSR… sorry, Russia towards the west, I really think that they should help stopping cybercriminals living (or staying) in Ukraine.
And, if rescator[dot]cc is evidently criminal, why haven’t the .cc-domain adminstartors seized this domain?
IIRC the reported location is Odessa. That’s in the area forcibly annexed by Russia so the Ukrainian government will first have to kick the Russians out before they can apprehend Rescator. Might be a long wait.
Wrong.
Odessa WAS a Russian city, but after USSR collapse Ukraine snatched it (South-East part of Ukraine was assigned to Ukrainian part of USSR by Lenin only in 1922; it’s build by Russians and Russians inhabit this territory)
Today it’s controlled by CIA-installed junta from Kiev. It was some protests, but they was brutally suppressed. In Odessa protests mostly ended when pro-kiev nazi burned alive 40+ protesters (google for “Odessa 2 May Trade Unions House”)
I wonder where you get your information? Odessa is in the western part of Ukraine, safe from USSR… sorry, Russia.
I believe it was Ossetia that was intended.
As in the 2008 Russian invasion of Ossetia, in Georgia.
Noteworthy was multiple “criminal hacker” groups initiating a network attack against the Georgian government as military operations began.
The timing was close enough to be apparent as part of the military operation, rather tipping the Russians hand on cyber operations.
Not to start a political argument, but there is NO area ” forcibly annexed by Russia” in the Ukraine. That includes Crimea.
Richard, perhaps the operative word for the Ukraine is, “yet”.
There *are* Russian forces in the Ukraine. The Russians said that the soldiers were “on vacation and went voluntarily”.
I must say, after serving for nearly 28 years in the US Army, I find the Russian Army very, very generous to their soldiers. After all, they let them go on vacation with their tanks, artillery and crew served weapons.
Boy, I sure could’ve used a tank during rush hour when I was home on leave!
You wouldn’t think that “Richard Steven Hack” was a Russian name, but judging by your comments on this article so far, I think it’s pretty clear whose team you play for.
Maybe Richard the hack is rescator
#keep your hand of Donbas
So, what do we hear from HD? Are they still “investigating?” Have they cleaned their POSs? Have they taken any remedial action?
As for “rescator,” he’ll eventually do something stupid and get swept away, only to be replaced by someone else.
I’m wondering the same thing… has there been any official press release about the breach (recently)?
For now, everything they have to say about this is here:
https://corporate.homedepot.com/MediaCenter/Pages/Statement1.aspx
It’s been a long wait for me to hear from HD. My bank account was hacked on October 10 at their Seguin, Texas store and October 11 at their Katy, Texas store. Both times they were for two gift cards at each store for a total of over $1600.00. My bank credited my account, however, I could not get an answer from HD corporate. Three letters remain unanswered.
How about file integrity monitoring? It is still one of the 12 PCI requirements? Are they not performing file integrity monitoring on their POS systems? If they were performing file integrity monitoring properly, their IT staff would have been alerted almost immediately of any changes to the point-of-sale computers. I would like to know what PCI consulting firm signed off on Home Depot’s compliance certification.
Not really. It is easy to fool FIM these days.
FireEye detects the malware just fine and will block it with ease. Home Depot is NOT a FireEye customer though.
I am pretty confident they use Cisco’s Sourcefire, which in my view, is not as good as Fireeye in detecting such breach.
The irony thing is that Fireeye detected the initial breach at Target and issued an alert but Target security team, which is new to Fireeye’s system, failed to respond. The more irony thing is that after Target breach, Home Depot didn’t learn anything and continued to run comfortably with its insufficient IT security practice, and suffered breach from the same malware and the same hackers.
Target was a FireEye customer, and that didn’t help them because the alert came in with 10,000 other alerts that were not important. You need something that will not only identify malicious downloads but also prioritize the ones that are real threats.
Then pay more attention to Fireeye’s alerts next time. 🙂
FireEye has a 0% false positive rate, legally they say 0.01%. The failure was they decided to not put the FireEye appliance into blocking mode thus relying on human intervention. It was Target’s failure 100%, not FireEye’s at all. It did not come in with 10,000 other alerts, these were very very specific. I am very familiar with the innerworkings of what happened there, it was Minneapolis who dropped the ball. India even created the ticket for the event. FireEye alerts are very specific, they would have immediately see where the ex-filtration was happening to.
Fireeye does not have a “zero” false positive rate.
We’ve been evaluating their product for 6 weeks. In that period, it’s generated hundreds of false postive alerts, and not a single true positive.
Would you care to post a redacted pastebin of an alert? I have installed over 100 of their devices and have never seen a single false positive. If you are receiving hundreds then you likely have another issue. Are you evaluating an NX or another appliance?
This is nothing new. My bank account was debited over $1600.00 last year for four gift cards at Home Depot stores in Seguin, Texas and Katy,Texas. My bank credited my account, but Home Depot could not have cared less. One of the managers at the Katy, TX store was even upset that a Home Depot Resolution Expeditor gave me his name to contact. They didn’t care when it happened to me on October 10 and 11 last year! Their “Resolution Expeditor” could get no response for nearly one month. I still have his emails. I sent three letters to their corporate office and received NO reply.
Just because a purchase was made through your account there doesn’t mean that’s the source – it would be foolish for a criminal to “cash out” in the exact same place the fraud was committed in the first place! It’s very likely that they obtained your information in some other way, such as card skimming, and decided on The Home Depot as the method to “cash out.”
Basically, they go in, get the gift cards, and either use them themselves or sell them off to complete the cycle. Buying a bunch of big Home Depot cards isn’t as likely to raise many eyebrows. Why? Because they carry things such as nice power tools, everyone knows those aren’t cheap! All that he has to say is he’s a mechanic/carpenter/some other position, and is treating some of his coworkers or buds who like to frequent HD to some gift cards for Christmas as he has some extra cash and they love them some DeWalt and Milwaukee tools.
Brian:
Thanks again for your great reporting. Based on the number of thefts and the misinformation out there it would be great if you could create a “scorecard” showing the date, entity, size of the breach, status, etc. – and a link to your related article.
I think it’s time to go back to the barter system.
Why? As a consumer I have no responsibility and they pay me to use their credit cards with 1% cash back. Why should I even care as long as they keep paying me with no liability?
For one, the hassle factor. When I am issued a new card, I have to notify my gym, cell carrier, etc, to update their billing. Then I have to update my records in Quicken.
Besides, who do you really think pays in the long run? The consumer!
I wouldn’t deny that it’s inconvenient to have a card cancelled because I’ve lived through it… while out-of-town at a wedding in another state. So yes, it’s a damn pain-in-the-backside that aggravates me to no end.
That said, I’d still say I was well shielded. I didn’t have to pay the hundreds of dollars that was spent in my name by the card thief, and I even got some of those Visa “gift” cards to use in the interim while the case was being handled. So I wasn’t stranded without money. And that, right there, is all the reason I need to advocate for payment card use, even in the face of all these thefts. As bad as the aggravation was for me, it was still light-years away from being out to the dollar amount that was stolen. Having to redo all my automatic payments is a pittance next to being out so much money with nothing to show for it.
You should switch to cash, then if you lose it you can only blame yourself and won’t get reimbursed. For me I have no liability and credit card companies pay me to use their cards. You can’t beat that and you can’t complain. I don’t want Chip and PIN because its a false security and the retailers will pass the cost on down to the customer in a major way, way more than the fraud that is just cancelled by the credit card agencies. They detect it early and cancel all the cards, its really a minuscule loss to them. Chip and PIN for every retailer is a major cost. Plus, explain to me how Chip and PIN protects Amazon purchases or anything you buy online?
Fer sure! +1
Good thing I got new debit cards as soon as I heard the news on your site Krebs. I guess, at least until chip and pin (even if that’s a saving grace), I’ll be using best practice of multiple accounts. One for regular purchases with a low limit and the other for direct payments, etc.
Even easier don’t use debit cards for purchases, don’t use anything tied directly to your bank account. Regular credit cards cause you no pain if they are used for fraud, all you have to do is monitor charges and report the ones you didn’t make, no loss to you at all. Well until the expense of the overall fraud trickles down to us the consumer.
One thing that is not clear to me is when paying with a Debit transaction, does the credit information during the swipe still get read and stored, and thus able to be sold by the bad guys? I have been to Home Depot a few times over this time period, but always used my debit card with a PIN, never using it in credit mode. I want to know if I’m still vulnerable and if I should consider asking my bank to just reissue me a new one and hope that this one comes with Chip-and-PIN.
Related, I’ve recently noticed (over the past 3 or 4 months) rapid upgrading by many local stores to the new card reader which can now do Chip-and-PIN, from the big box stores to the small locally owned shops.
Yes, you will still be at risk. The scrape captured the CC# and can be used as a simple CC for fraud, they don’t need your pin. But you are actually at greater risk as fraud will empty your bank account, avoid using ATM/Debit style cards for anything other than ATM cash.
The breach plus recent F score from Qualys SSL Labs on Home Depot’s online checkout server reveals failed internal IT security team/process, incompetent outside security consultant and inferior IDS/IPS system.
The hiring of Fishnet by Home Depot, the rumored incumbent security consultant, to help the investigation of current breach, indicates a serious conflict of interest and management failure.
It will be very interesting to see how the Home Depot stock reacts to this breach. In my personal view, it will behave like what Target stock did: goes down, goes up, goes down again and finally when the company gives in to the pressure and confesses, it dives.
Who is the supplier of the POS system? I would think like most of these systems there is a company that specializes in these and is contracted for the servicing/updating. I know ultimately the responsibility lies with HD, but I’m curious to see if there are links on the POS side as well.
HD listed in my zip code is using Ingelico POS terminals.
The POS is XPE
infected point-of-sale systems running Microsoft Windows
What a surprise. Why businesses take on the risk of using ANYTHING Microsoft if they’re unwilling to invest in strong anti-virus, malware & hacking measures is seriously concerning. Wonder how long before their insurance companies refuse to provide liability &/or fraud coverage -smh
And what are the other options? Run Mac on 20,000 POS terminals and a mega retailer? Does Mac even make a dedicated POS system, since everything has to run on Mac hardware.
Wait, lets make it all Linux? Do you really think that will make a difference? The OS does not matter. There is a lot of money to be made in carding and POS hacking. Once the profit is gone, there will be new attacks against other lucrative targets.
No, I got it. We’ll all be paying with bitcoins. Nope, there’s already bitcoin wallet attacks out there in the wild.
If it’s OK to kill an American and his 16 year old son without due process using a hellfire missile launched from a drone & we know who’s doing this I don’t understand why our government doesn’t just handle this situation?? I could make a pretty good argument that what this gentleman doing could be considered terrorism and it would be in our best interests to treat it so. Honestly there aren’t many problems in this world that can’t be solved by the appropriate application of high explosives =) Just my 2 cents
Eric, do learn the difference between theft and terrorism.
A small hint, a terrorist will blow up a market full of men, women and children.
A thief only steals.
You advocate drone missile attacks in cities in the Ukraine, Saint Petersburg and the Jinan Military Region of China.
Nations we are not at war with, who also possess drone weapons and also possess thermonuclear weapons.
Nations that *would* be at war with us, for launching a missile against a civilian most certainly is an act of war.
We didn’t even do that during the hottest part of the cold war!
Please learn the difference between murder from terrorism, theft and war.
And someone needs to learn sarcasm – both the nuclear and conventional type.
I’m gonna destroy them.
I never go to Home Depot – because of proximity – but went to one in July. If that one had its data breached I should just go ahead and get new cards?
IMHO. I would much rather know where to locate card dumps like this vs. have card dumps go completely underground.
It’s pure speculation that just because a hosting company allows it to continue on as is. That it is not actively working with government agencies while doing so. Sadly. Even so, card dumps show up after the fact.
At least this way security agencies SHOULD be able to spend less time collecting “Meta Data” for cell phones and more time on breadcrumb trails from major breaches like this. From websites like this.
That said. It would appear based on current and present facts that some of these agencies can’t tie their shoes to get ready to start looking for these breadcrumb trails. Which maybe why these card shops have spent little effort in going completely to the “Dark Web”.
The major card issuers and banks also are very much to blame because there have been additional methods available for at least two decades that could have been used vs. sticking with “TRACK” data as their only protection methods. To at least help limit what we are still seeing today.
Rumors have it that 50 percent of U.S. adults since 2013 have had some sort of identity theft take place. Brian can verify the accuracy of these stats.
Maybe it’s time to “Wake UP!” Get the card issuers, banks, and merchants to put both short term and long term game plans together, as in NOW! Which should have taken place many years ago.
Don
Nothing really surprising here, but it is still good to know. I am also sure we will see more of the same in the near future – I am convinced there are dozens if not more breaches out there under way, or not discovered yet. The retail industry is slower than molasses in reacting to this.
I hope Brian covers any news about industry actually reacting to this, and maybe an attempt to over haul the PCI standards. I need to check his list – maybe he already has!
FYI – Home Depot just issued a press release confirming the breach event of both their US and Canadian store locations. No evidence of PIN compromise or online store.
And in the “closing the barn door after the horse is gone” department, they say:
“Responding to the increasing threat of cyber-attacks on the retail industry, The Home Depot previously confirmed it will roll out EMV “Chip and PIN” to all U.S. stores by the end of this year, well in advance of the October 2015 deadline established by the payments industry.”
Canada has had EMV since 2007 and the shift for most card companies occurred in 2012, so what precisely was breached in Canada? Should be interesting once we learn how transparent they are.
If you read carefully about Chip and PIN, the rolling one-time security code that gets changed after each transaction is an OPTIONAL feature. A bud of mine is security manager for a very large producer of those cards and he said many retailers do not implement it because it slows down the transaction. That could require the retailer to open more register lines than usual .
Chip and PIN is NOTHING but a liability shifting mechanism for card-present transactions.
In the US, a card-present transaction fraud loss is automatically borne by the bank because the merchant is presumed to have validated the signature 100% of the time. Seriously.
After the deadline kicks in, whether it’s the actual date or the 80% mark, card-present transactions that are fraudulent will have the loss absorbed by the merchant, not the bank, if the merchant is not using Chip and PIN.
Next story: Major banks are silent investors in payment card terminal manufacturers and card manufacturers.
Pretty much, and Cowchip-N-Pen can be compromised as well. I object to being made to pay for what really is an old system that costs too much, is too big to fail, and then I get left holding the bag – just like millions of other customers.
There are cheaper faster better systems, that are new technology, but let’s face it – any system that is poorly implemented through out the entire infrastructure will fail anyway.
Brian:
Perhaps I am not fully awake or the diesel exhaust that I breathed during my 20 mile bicycle ride into work this morning did fry my brains, but I am having problems trying to reconcile the photograph of the building taken during a late afternoon on a partially cloudy day that I see at the beginning of this article with the contents of the article.
Can someone please help me? It is a symbolic relation of the weather and the situation with cloudfire; ie; an approaching storm?
Thank you
Mark Allyn
Portland, Oregon
I think you are being serious – as a fellow bike commuter I can appreciate the diesel fumes and their effect.
The picture is of a boarded up/closed Home Depot location.
Surprisingly, I just threw up in my mouth a little bit after reading this. Maybe I’ve been out of the antivirus industry too long . . .
Anyhow, it is sickening. Not sure what else can be said.
NEW POS MALWARE FAMILY – BACKOFF
In 2014 Trustwave SpiderLabs discovered a new family of point of sale (POS) malware active from October 2013 through at least May 2014. We witnessed the use of this malware family, which we’ve named Backoff, in at least three separate forensic investigations. The malware scrapes memory from running processes on the victim machine and searches that memory for track data. In addition, the malware includes a command-and-control (C&C) component that facilitates the uploading of discovered data, updating the malware, downloading/executing additional malware and uninstalling the malware. New variants of Backoff also include keylogging functionality. Overview here: https://gsr.trustwave.com/topics/backoff-pos-malware/backoff-malware-overview/
BackOff Technical Analysis here: http://blog.spiderlabs.com/2014/07/backoff-technical-analysis.html
US-CERT Alert here: https://www.us-cert.gov/sites/default/files/publications/BackoffPointOfSaleMalware.pdf
Brian needs to start charging for his services.
http://www.businessweek.com/news/2014-09-08/home-depot-confirms-computer-data-system-breach
“The retailer said last week that it only learned of a possible breach after independent journalist Brian Krebs reported on Sept. 2 that hackers may have stolen customer data and made counterfeit credit- and debit-cards. It’s been investigating the matter since.”
https://corporate.homedepot.com/MediaCenter/Pages/Statement1.aspx
“Last Tuesday, September 2, we disclosed that we were investigating a possible breach of our payment data systems. We want you to know that we have now confirmed that those systems have in fact been breached, which could potentially impact any customer that has used their payment card at our U.S. and Canadian stores, from April forward.”
So like 5+ months? OMG. They could easily surpass Heartland.
I thought they said they knew about it for two months? Maybe the SSL Labs finding was more prophetic than we knew.
SSL Labs scan is more revealing of the weakness in Home Depot’s IT security practice – 2 days after a major breach, the “secured” checkout server of Home Depot website failed a very basic, ancient PCI compliance test – SSL V2 and weak ciphers.
The irony thing is that The Home Depot people had no idea about this scan. Almost a day after someone posted the SSL Labs link on this website, the company requested SSL Labs not show the scan result – which was a big bold ugly F.
I saved a copy of the scan result in case it’s requested in a future court case.