Nearly a week after this blog first reported signs that Home Depot was battling a major security incident, the company has acknowledged that it suffered a credit and debit card breach involving its U.S. and Canadian stores dating back to April 2014. Home Depot was quick to assure customers and banks that no debit card PIN data was compromised in the break-in. Nevertheless, multiple financial institutions contacted by this publication are reporting a steep increase over the past few days in fraudulent ATM withdrawals on customer accounts.
The card data for sale in the underground that was stolen from Home Depot shoppers allows thieves to create counterfeit copies of debit and credit cards that can be used to purchase merchandise in big box stores. But if the crooks who buy stolen debit cards also are able to change the PIN on those accounts, the fabricated debit cards can then be used to withdraw cash from ATMs.
Experts say the thieves who are perpetrating the debit card fraud are capitalizing on a glut of card information stolen from Home Depot customers and being sold in cybercrime shops online. Those same crooks also are taking advantage of weak authentication methods in the automated phone systems that many banks use to allow customers to reset the PINs on their cards.
Here’s the critical part: The card data stolen from Home Depot customers and now for sale on the crime shop Rescator[dot]cc includes both the information needed to fabricate counterfeit cards as well as the legitimate cardholder’s full name and the city, state and ZIP of the Home Depot store from which the card was stolen (presumably by malware installed on some part of the retailer’s network, and probably on each point-of-sale device).
This is especially helpful for fraudsters since most Home Depot transactions are likely to occur in the same or nearby ZIP code as the cardholder. The ZIP code data of the store is important because it allows the bad guys to quickly and more accurately locate the Social Security number and date of birth of cardholders using criminal services in the underground that sell this information.
Why do the thieves need Social Security and date of birth information? Countless banks in the United States let customers change their PINs with a simple telephone call, using an automated call-in system known as a Voice Response Unit (VRU). A large number of these VRU systems allow the caller to change their PIN provided they pass three out of five security checks. One is that the system checks to see if the call is coming from a phone number on file for that customer. It also requests the following four pieces of information:
-the 3-digit code (known as a card verification value or CVV/CV2) printed on the back of the debit card;
-the card’s expiration date;
-the customer’s date of birth;
-the last four digits of the customer’s Social Security number.
On Thursday, I spoke with a fraud fighter at a bank in New England that experienced more than $25,000 in PIN debit fraud at ATMs in Canada. The bank employee said thieves were able to change the PINs on the cards using the bank’s automated VRU system. In this attack, the fraudsters were calling from disposable, prepaid Magic Jack telephone numbers, and they did not have the Cv2 for each card. But they were able to supply the other three data points.
KrebsOnSecurity also heard from an employee at a much larger bank on the West Coast that lost more than $300,000 in two hours today to PIN fraud on multiple debit cards that had all been used recently at Home Depot. The manager said the bad guys called the customer service folks at the bank and provided the last four of each cardholder’s Social Security number, date of birth, and the expiration date on the card. And, as with the bank in New England, that was enough information for the bank to reset the customer’s PIN.
The fraud manager said the scammers in this case also told the customer service people they were traveling in Italy, which made two things possible: It raised the withdrawal limits on the debit cards and allowed thieves to withdraw $300,000 in cash from Italian ATMs in the span of less than 120 minutes.
One way that banks can decrease the incidence of PIN reset fraud is to require that callers supply all of the requested information accurately, and indeed the bank employee I heard from in New England said a nearby financial institution she’d contacted that used the same VRU system saw its PIN fraud drop to zero when it began requiring that all questions be correctly answered. The bank on the West Coast that I interviewed also said it had already begun requiring all five elements before processing PIN changes on any cards that have been used at Home Depot since April.
Still, some of the world’s largest banks have begun moving away from so-called knowledge-based authentication for their VRU systems toward more robust technologies, such as voice biometrics and phone printing, said Avivah Litan, a fraud analyst with Gartner Inc.
“We saw this same activity in the wake of the breach at Target, where the thieves would call in and use the VRUs to check balances, remove blocks on cards, get the payment history and of course change PINs,” Litan said.
Voice biometric technologies create an index of voice fingerprints both for customers and various fraudsters who conduct VRU fraud, but Litan said fraudsters often will use voice synthesizers to defeat this layer of detection.
Phone printing profiles good and bad callers alike, building fingerprints based on dozens of call characteristics, including packet loss, dropped frames, noise, call clarity, phone type and a host of other far more geeky concepts (e.g., “quantization,” and “taggers“).
ANALYSIS
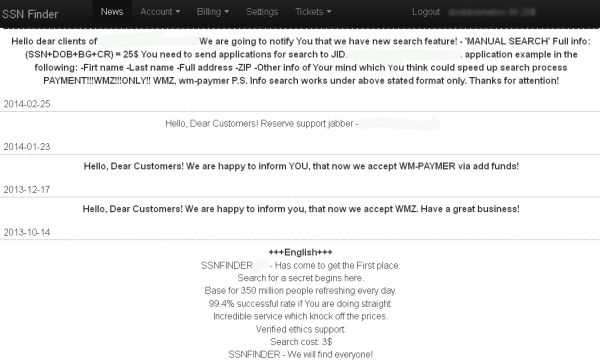
The fact that it is still possible to use customer service or an automated system to change someone else’s PIN with just the cardholder’s Social Security number, birthday and the expiration date of their stolen card is remarkable, and suggests that most banks remain clueless or willfully blind to the sophistication of identity theft services offered in the cybercrime underground. I know of at least two very popular and long-running cybercrime stores that sell this information for a few dollars apiece. One of them even advertises the sale of this information on more than 300 million Americans.
Banks are long overdue to move away from knowledge-based authentication. Forget about the fact that most major providers of these services have been shown to be compromised in the past year by the very crooks selling Social Security numbers and other data to identity thieves: The sad truth is that today’s cybercriminals are more likely to know the correct answers to these questions than you are.
I bring this up mainly because Home Depot is, predictably, offering credit monitoring services to affected customers (which, given the length of this breach is likely to impact a significant chunk of the American population). Credit and debit card fraud is annoying and inconvenient and can be at least temporarily expensive for victims, but as long as you are keeping a close eye on your monthly statements and reporting any unauthorized charges immediately, you will not be on the hook for those charges.
Please note that credit monitoring services will not help with this task, as they are not designed to look for fraud on existing accounts tied to your name and personal information. As I’ve noted in several stories, credit monitoring services are of dubious value because although they may alert you when thieves open new lines of credit in your name, those services do not prevent that activity. The one thing these services are good for is in helping identity theft victims clean up the mess and repair their good name.
However, given the fact that your Social Security number, date of birth and every possible answer to all of these knowledge-based authentication questions can be had for $25 in order to establish new lines of credit in your name, it makes good sense for people to avail themselves of free credit monitoring services. But there is little reason to pay for these services. If you don’t already have a credit monitoring service for free then maybe you haven’t been paying close enough attention to the dozens of companies over the past year that have likely lost your data in a breach and are already offering these services for free.
For more information about the benefits and limits of credit monitoring services — as well as other helpful tips to proactively safeguard your credit file — see this story.
More information, including an FAQ about the breach, released by Home Depot is available at this link.





Using TDBank I just called in to change my Pin and all I needed was my checking account number and the old Pin. !!!!!! Poof.
I’m naming the bank because I think it’s shocking that there was no additional hoops to jump through. Two-step authentication on the on-line banking site but nothing via telephone.
So MelbaM, all you had to do was call the number on the back of the access card, enter your access card number (which may be already compromised), enter your 3 or 4 digit telephone pin and provide your checking account number?
How would the fraudsters get your telephone pin, which is diff than your access card pin, and your checking account number?
Just curious?
Did you use your home phone? it’s possible they verified you were calling from your home number as a factor in their process. While this won’t stop family members from being a source of fraud, it may be a good deterrent to the average criminal.
I doubt calling from your home phone will stop the crooks. I’ve so much number spoofing recently it’s ridiculous.
Actually, it may. The phone number identification mechanism used for 800–number calls is not the same as Caller ID and has to be accurate. That’s because the recipient pays for the call, so the identification needs to be accurate and auditable.
I have no idea why the Caller ID system doesn’t use this data source, but it doesn’t. There are some companies offering call-screening systems that loop through an 800 number specifically so the real calling number can be determined.
I agree that 800 number calls are handled differently. But I don’t think that matters to the average person who is bombarded with spoofed calls.
But it could. If the FCC would get off its butt and REQUIRE that CallerID info be taken from this existing data stream, we could shut down telemarketers rather quickly.
The telcos don’t want that, of course, since they make a nice pile of cash from it.
For what it’s worth, that 800# handling is called “ANI” (Automatic Number Identification). It’s not that hard to spoof ANI anymore since the explosion of VOIP and VSP’s.
It is only a bit harder than spoofing caller ID. If Caller ID was suddenly eliminated and ANI was used for everything, then criminals, telemarketers, collectors, etc. would spoof ANI instead and hardly skip a beat.
The PSTN is complicated. There are so many organizations and interconnections that it is unlikely to ever be able to provide a “spoof-proof” identification system.
I bet the bank had your home phone number on caller ID, and it matched the home phone number on your checking account information.
So where do we stand now. Its been about 10 days since HD acknowledged this problem. Their web site provides a response:
https://corporate.homedepot.com/MediaCenter/Pages/Statement1.aspx
and offers a solution:
https://homedepot.allclearid.com/
(1) Looks like if you shopped at HD after April you qualify for help. Unfortunately there is no ending date. Does this mean that there is an ongoing problem?
(2) If you shopped at HD during this period without a problem, so far, should you sign up?
(3) I bet a lot of people qualify so how do they control cost?
My bank initially just recommended keeping an eye on my cc.
Is there a chance that this will amount to a big deal about nothing?
I called my cc on 9/17 and a recorded message apologized for the long wait because of HD but said that it was not necessary to get a new cc unless you had a problem. Is this just a better way to deal with a problem?
If the three digit code was compromised then Home depot should be held accountable for all the losses. All operating rules say you can’t keep 3 digit cvv code on the system
Really? – http://mobile.businessweek.com/articles/2014-09-12/home-depot-didnt-encrypt-credit-card-data-former-workers-say
If you have a Wall Street Journal subscription for online access, this is probably worth reading (but don’t ask me why the URL is so weird):
Home Depot Upped Defenses, But Hacker Moved Faster
Retailer Culture of Preparation and Testing No Match for Stealthy Data Thieves
http://online.wsj.com/articles/home-depot-upped-defenses-but-hacker-moved-faster-1410564218?mod=LS1
I have shopped at HD during the period in question but there has been no problem with my card – so far.
I was there again yesterday for a few things and decided to try the “chip” mechanism that is present in the reader. No luck – it’s not enabled. If you put a card in you get a message asking you to swipe (or tap – the NFC stuff IS enabled).
I shopped at Home Depot back in June 25th of this year and just yesterday my debit card was charged a total of around $1,200.
I’m quite cautious with my card, never sticking it out there, only one who uses it, only use it around town in same places, don’t use it online, don’t use atm’s etc.
Just one little bucket of paint and someone goes on a shopping spree on my expense.
Can’t say I want to shop at Home Depot for a while.
People, please stop using your debit cards at stores…..please.
Chase is starting to replace cards stemming from Home Depot Breach
http://www.reuters.com/article/2014/09/17/jpmorgan-cards-idUSL1N0RI1RT20140917
Do we know is this is the tip of the iceberg?
My local credit union did the same thing a couple weeks ago. I was trying to find out for the life of me why out of the blue I would have my card cancelled and re-issued. My guess is that it is cheaper for these institutions to just send out new cards en masse than waiting to hear from customers regarding fraud reports.
US Bank did the same thing to me over the Target breach late last year.
We too were recently hit by Home Depot. Was told by Santander was only people who used the self check out lines. My husbands card was snagged here in MA we used the Leominster store, fools used the card info in Danvers MA at Home Depot and Lowes. Police notified, Feds notified and cameras being pulled and going after them. I was told a lot of this is from the Bronx NY that they recently arrested a bunch of men from there with stolen credit cards, they also had same issue at Walmart up here as well. So bank makes you wait for your money, wait 10 days for new card, open all new accounts and they suggested a separate account for debit card use only. I feel violated for the first time in my life and will somehow track this scumbag down. There will always be more, but hey its the principle behind it. I am not a happy camper. Looks like cash is still KING! Be safe everyone!
Not all credit card companies are equally customer friendly. I know merchants dislike American Express because they are more costly, but as an AmEx cardholder, I am a very happy camper. On 14-Aug-2014, I ordered some gifts online from Harry & David using my AmEx card which I normally use at just CostCo. Thursday, 28-Aug, between midnight and 2AM, PDT, someone made 3 online purchases using my AmEx card. At 7:30am I got a call from AmEx card fraud. I told them I hadn’t used my card and they immediately canceled the purchases and my card and asked if I wanted the new card sent by regular mail or next day delivery. With the holiday coming up, I opted for next day and had my new card on Aug-29. And I live in the boonies.
Take-aways:
1 American Express has efficient programs in place to detect cc fraud.
2 They act fast to alert their customers to possible fraud.
3 They get you your new card in less than 36 hours
4 Watch this space for the next “big” retailer” to be breached, ie, Harry & David.
BTW, I called H&D that morning and was told they’d get back to me for details. I’m still waiting.
Guess where I won’t be shopping again…
What i will like to know is how did home depot know about the theft?
BEQSkz You made some clear points there. I looked on the internet for the issue and found most people will go along with with your site.
OK my credit card was just hacked yesterday, I do shop alot at Home Depot. I use my Visa card for all my bills, vehicle ins. and the list is hugh. Ok they will not charge me for these misc charges which are all from mexico. Now I won’t get a new card for another ten days? how will I survive? I can’t even buy gas or pay auto ins. for two vehicles which both are due this week? I am a disabled vet on a fixed income. Do you really know what it all this really entails. I have to contact all my utility companies, insurance etc. hugh list, and give them the new card number when I get it in ten days??????? The last time I received a new card number I spent two days on the phone trying to caontact everyone involved to pay my bills. AM I MAD AT HOME DEPOT!!!!!!!!!! They owe me big time, sorry ain’t going to handle it.