I received a number of media requests and emails from readers over the weekend to comment on a front-page New York Times story about an organized gang of cybercriminals pulling off “one of the largest bank heists ever.” Turns out, I reported on this gang’s activities in December 2014, although my story ran minus many of the superlatives in the Times piece.
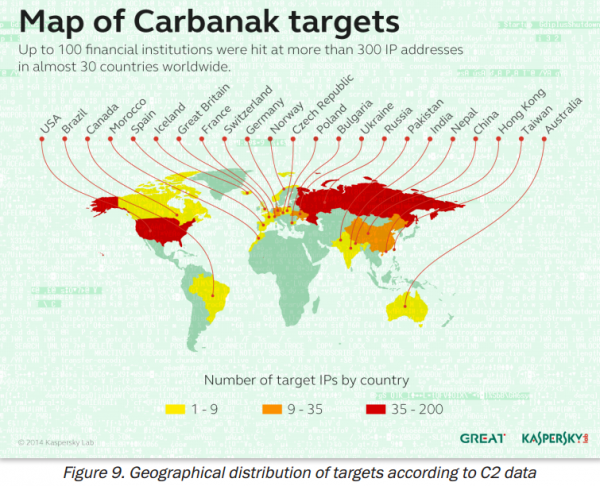
The Times’ story, “Bank Hackers Steal Millions Via Malware,” looks at the activities of an Eastern European cybercrime group that Russian security firm Kaspersky Lab calls the “Carbanak” gang. According to Kaspersky, this group deployed malware via phishing scams to get inside of computers at more than 100 banks and steal upwards of USD $300 million — possibly as high as USD $1 billion.
Such jaw-dropping numbers were missing from a story I wrote in December 2014 about this same outfit, Gang Hacked ATMs From Inside Banks. That piece was based on similar research published (PDF) jointly by Dutch security firm Fox-IT and by Group-IB, a Russian computer forensics company. Fox-IT and Group-IB called the crime group “Anunak,” and described how the crooks sent malware laced Microsoft Office attachments in spear phishing attacks to compromise specific users inside targeted banks.
“Most cybercrime targets consumers and businesses, stealing account information such as passwords and other data that lets thieves cash out hijacked bank accounts, as well as credit and debit cards,” my December 2014 story observed. “But this gang specializes in hacking into banks directly, and then working out ingenious ways to funnel cash directly from the financial institution itself.”
I also noted that a source told me this group of hackers is thought to be the same criminal gang responsible for several credit and debit card breaches at major retailers across the United States, including women’s clothier Bebe Stores Inc., western wear store Sheplers, and office supply store Staples Inc.
Andy Chandler, Fox-IT’s general manager and senior vice president, said the group profiled in its December report and in the Kaspersky study are the same.
“Anunak or Carbanak are the same,” Chandler said. “We continue to track this organization but there are no major revelations since December. So far in 2015, the financial industry have been kept busy by other more creative criminal groups,” such as those responsible for spreading the Dyre and Dridex banking malware, he said.
ANALYSIS
Certainly, learning that this group stole possibly close to USD $1 billion advances the story, even if the Kaspersky report is a couple of months late, or generous to the attackers by a few hundred million bucks. The Kaspersky report also references (but doesn’t name) victim banks in the United States, although the New York Times story notes that the majority of the targeted financial institutions were in Russia. The Group-IB/Fox-IT report did not mention US banks as victims.
Two readers at different financial institutions asked whether The Times was accurate in stating that employees at victim banks had their computers infected merely after opening booby-trapped emails. “The cybercriminals sent their victims infected emails — a news clip or message that appeared to come from a colleague — as bait,” The Times’ story reads. “When the bank employees clicked on the email, they inadvertently downloaded malicious code.”
As the Kaspersky report (and my earlier reporting) notes, the attackers leveraged vulnerabilities in Microsoft Office products for which Microsoft had already produced patches many months prior — targeting organizations that had fallen behind on patching. Victims had to open booby trapped attachments within spear phishing emails.
“Despite increased awareness of cybercrime within the financial services sector, it appears that spear phishing attacks and old exploits (for which patches have been disseminated) remain effective against larger companies,” Kaspersky’s report concludes. “Attackers always use this minimal effort approach in order to bypass a victim’s defenses.”
Minimal effort. That’s an interesting choice of words to describe the activities of crime groups like this one. The Kaspersky report is titled “The Great Bank Robbery,” but the work of this gang could probably be more accurately described as “Death by 1,000 cuts.”
Why should crime groups like this one expend more than minimal effort? After all, there are thousands of financial institutions here in the United States alone, and it’s a fair bet that on any given day a decent number of those banks are months behind on installing security updates. They’re mostly running IT infrastructure entirely based on Microsoft Windows, and probably letting employees browse the Web with older versions of Internet Explorer from the same computers used to initiate wire transfers (I witnessed this firsthand just last week at the local branch of a major U.S. bank). It’s worth noting that most of the crime gang’s infrastructure appears to be Linux-based.
This isn’t intended as a dig at Microsoft, but to illustrate a point: Most organizations — even many financial institutions — aren’t set up to defeat skilled attackers; their network security is built around ease-of-use, compliance, and/or defeating auditors and regulators. Organizations architected around security (particularly banks) are expecting these sorts of attacks, assuming that attackers are going to get in, and focusing their non-compliance efforts on breach response. This “security maturity” graphic nicely illustrates the gap between these two types of organizations.
As I wrote in my December story, the attacks from the Anunak/Carbanak gang showcase once again how important it is for organizations to refocus more resources away from preventing intrusions toward detecting intrusions as quickly as possible and stopping the bleeding. According to the Fox-IT/Group-IB report, the average time from the moment this group breaks into bank internal networks and the successful theft of cash is a whopping 42 days.
Kaspersky’s report notes a similar time range: “There is evidence indicating that in most cases the network was compromised for between two to four months, and that many hundreds of computers within a single victim organization may have been infected.” Both the Kaspersky and Group-IB/Fox-IT reports contain pages and pages of threat indicators, including digital signatures and network infrastructure used by this group.
So those are some takeaways for financial institutions, but what about banking customers? Sadly, these developments should serve as yet another wake-up call for small to mid-sized businesses based in the U.S. and banking online. While consumers in the United States are shielded by law against unauthorized online banking transactions, businesses have no such protection.
Russian hacking gangs like this one have stolen hundreds of millions of dollars from small- to mid-sized businesses in the U.S. and Europe over the past five years (for dozens of examples, see my series, Target: Small Businesses). In the vast majority of those cyberheists, the malware that thieves used to empty business accounts was on the victim organization’s computers — not the bank’s.
Now, add to that risk the threat of the business’s bank getting compromised from within and the inability of the institution to detect the breach for months on end.
“Advanced control and fraud detection systems have been used for years by the financial services industry,” the Kaspersky report observed. “However, these focus on fraudulent transactions within customer accounts. The Carbanak attackers bypassed these protections, by for example, using the industry-wide funds transfer (the SWIFT network), updating balances of account holders and using disbursement mechanisms (the ATM network). In neither of these cases did the attackers exploit a vulnerability within the service. Instead, they studied the victim´s internal procedures and pinpointed who they should impersonate locally in order to process fraudulent transactions through the aforementioned services. It is clear that the attackers were very familiar with financial services software and networks.”
Do you run your own business and bank online but are unwilling to place all of your trust in your bank’s security? Consider adopting some of the advice I laid out in Online Banking Best Practices for Businesses and Banking on a Live CD.
Update, 3:45 p.m. ET: A copy of the Kaspersky report on the Carbanak gang is here (PDF). Also, Fox-IT has released a Q&A on the differences and commonalities between their December report and Kaspersky’s this week.




Thank you for this post. There’s some really awesome information here.
I read in some places that the hackers were able to remotely cause ATMs to spit out cash, Is this possible? Is this what they did?
I remember the last big bank hack (where Arab Banks were hit for $45 million), People were sent out with debit cards to drain ATMS.
In short, “sort of”
Brian has a couple of articles that talk about it:
http://krebsonsecurity.com/2014/10/spike-in-malware-attacks-on-aging-atms/
Roughly, an ATM is like a Cash Register. It has drawers for bills, and it has wires that control them. Because the ATM needs to be able to check your balance, it’s “networked” to something. (A cash register doesn’t need to be networked.)
Past that, it’s a matter of “is the computer sufficiently secure”. And the answer on average seems to be “probably not”.
Kapersky did a demo of a infected ATM spitting out cash https://www.youtube.com/watch?v=QZvdPM_h2o8&feature=youtu.be
Is there any possibility that these gangs could/would recruit insiders to walk the malware into their employers’ networks, or intentionally download something? I know stupidity gets the job done for free, but hey….
Linux and Open Source Software beckons……….
well, if it’s good enough for Bank thieves, the Navy, and the NSA, then by golly it’s good enough for Banks!!
Congrats Krebs, excellent report. I think the big issue in all those attacks seems be that the tools we use to defend our organizations tend to fail, no matter how many tools or which vendor products use; in many cases couldn’t block a simple spear phishing attack and trojan download.
Recently I detect a spear phishing attack with a word doc file attached, that use macros to download an exe file from Internet. I cheked the word doc an the site with different tools and no ones detect the infection. If I were unable to investigate this issue, an alert the vendors to generate asap a solution could harm my organization and all would be a mess.
Keep in mind just a good trained, commitment and shaped group ready to act when is need it.