John Gilmore, an American entrepreneur and civil libertarian, once famously quipped that “the Internet interprets censorship as damage and routes around it.” This notion undoubtedly rings true for those who see national governments as the principal threats to free speech.
However, events of the past week have convinced me that one of the fastest-growing censorship threats on the Internet today comes not from nation-states, but from super-empowered individuals who have been quietly building extremely potent cyber weapons with transnational reach.
More than 20 years after Gilmore first coined that turn of phrase, his most notable quotable has effectively been inverted — “Censorship can in fact route around the Internet.” The Internet can’t route around censorship when the censorship is all-pervasive and armed with, for all practical purposes, near-infinite reach and capacity. I call this rather unwelcome and hostile development the “The Democratization of Censorship.”
Allow me to explain how I arrived at this unsettling conclusion. As many of you know, my site was taken offline for the better part of this week. The outage came in the wake of a historically large distributed denial-of-service (DDoS) attack which hurled so much junk traffic at Krebsonsecurity.com that my DDoS protection provider Akamai chose to unmoor my site from its protective harbor.
Let me be clear: I do not fault Akamai for their decision. I was a pro bono customer from the start, and Akamai and its sister company Prolexic have stood by me through countless attacks over the past four years. It just so happened that this last siege was nearly twice the size of the next-largest attack they had ever seen before. Once it became evident that the assault was beginning to cause problems for the company’s paying customers, they explained that the choice to let my site go was a business decision, pure and simple.
Nevertheless, Akamai rather abruptly informed me I had until 6 p.m. that very same day — roughly two hours later — to make arrangements for migrating off their network. My main concern at the time was making sure my hosting provider wasn’t going to bear the brunt of the attack when the shields fell. To ensure that absolutely would not happen, I asked Akamai to redirect my site to 127.0.0.1 — effectively relegating all traffic destined for KrebsOnSecurity.com into a giant black hole.
Today, I am happy to report that the site is back up — this time under Project Shield, a free program run by Google to help protect journalists from online censorship. And make no mistake, DDoS attacks — particularly those the size of the assault that hit my site this week — are uniquely effective weapons for stomping on free speech, for reasons I’ll explore in this post.
Google’s Project Shield is now protecting KrebsOnSecurity.com
Why do I speak of DDoS attacks as a form of censorship? Quite simply because the economics of mitigating large-scale DDoS attacks do not bode well for protecting the individual user, to say nothing of independent journalists.
In an interview with The Boston Globe, Akamai executives said the attack — if sustained — likely would have cost the company millions of dollars. In the hours and days following my site going offline, I spoke with multiple DDoS mitigation firms. One offered to host KrebsOnSecurity for two weeks at no charge, but after that they said the same kind of protection I had under Akamai would cost between $150,000 and $200,000 per year.
Ask yourself how many independent journalists could possibly afford that kind of protection money? A number of other providers offered to help, but it was clear that they did not have the muscle to be able to withstand such massive attacks.
I’ve been toying with the idea of forming a 501(c)3 non-profit organization — ‘The Center for the Defense of Internet Journalism’, if you will — to assist Internet journalists with obtaining the kind of protection they may need when they become the targets of attacks like the one that hit my site. Maybe a Kickstarter campaign, along with donations from well-known charitable organizations, could get the ball rolling. It’s food for thought.
CALIBRATING THE CANNONS
Earlier this month, noted cryptologist and security blogger Bruce Schneier penned an unusually alarmist column titled, “Someone Is Learning How to Take Down the Internet.” Citing unnamed sources, Schneier warned that there was strong evidence indicating that nation-state actors were actively and aggressively probing the Internet for weak spots that could allow them to bring the entire Web to a virtual standstill.
“Someone is extensively testing the core defensive capabilities of the companies that provide critical Internet services,” Schneier wrote. “Who would do this? It doesn’t seem like something an activist, criminal, or researcher would do. Profiling core infrastructure is common practice in espionage and intelligence gathering. It’s not normal for companies to do that.”
Schneier continued:
“Furthermore, the size and scale of these probes — and especially their persistence — points to state actors. It feels like a nation’s military cyber command trying to calibrate its weaponry in the case of cyberwar. It reminds me of the US’s Cold War program of flying high-altitude planes over the Soviet Union to force their air-defense systems to turn on, to map their capabilities.”
Whether Schneier’s sources were accurate in their assessment of the actors referenced in his blog post is unknown. But as my friend and mentor Roland Dobbins at Arbor Networks eloquently put it, “When it comes to DDoS attacks, nation-states are just another player.”
“Today’s reality is that DDoS attacks have become the Great Equalizer between private actors & nation-states,” Dobbins quipped.
UM…YOUR RERUNS OF ‘SEINFELD’ JUST ATTACKED ME
What exactly was it that generated the record-smashing DDoS of 620 Gbps against my site this week? Was it a space-based weapon of mass disruption built and tested by a rogue nation-state, or an arch villain like SPECTRE from the James Bond series of novels and films? If only the enemy here was that black-and-white.
No, as I reported in the last blog post before my site was unplugged, the enemy in this case was far less sexy. There is every indication that this attack was launched with the help of a botnet that has enslaved a large number of hacked so-called “Internet of Things,” (IoT) devices — mainly routers, IP cameras and digital video recorders (DVRs) that are exposed to the Internet and protected with weak or hard-coded passwords. Most of these devices are available for sale on retail store shelves for less than $100, or — in the case of routers — are shipped by ISPs to their customers.
Some readers on Twitter have asked why the attackers would have “burned” so many compromised systems with such an overwhelming force against my little site. After all, they reasoned, the attackers showed their hand in this assault, exposing the Internet addresses of a huge number of compromised devices that might otherwise be used for actual money-making cybercriminal activities, such as hosting malware or relaying spam. Surely, network providers would take that list of hacked devices and begin blocking them from launching attacks going forward, the thinking goes.
As KrebsOnSecurity reader Rob Wright commented on Twitter, “the DDoS attack on @briankrebs feels like testing the Death Star on the Millennium Falcon instead of Alderaan.” I replied that this maybe wasn’t the most apt analogy. The reality is that there are currently millions — if not tens of millions — of insecure or poorly secured IoT devices that are ripe for being enlisted in these attacks at any given time. And we’re adding millions more each year.
I suggested to Mr. Wright perhaps a better comparison was that ne’er-do-wells now have a virtually limitless supply of Stormtrooper clones that can be conscripted into an attack at a moment’s notice.
A scene from the 1977 movie Star Wars, in which the Death Star tests its firepower by blowing up a planet.
SHAMING THE SPOOFERS
The problem of DDoS conscripts goes well beyond the millions of IoT devices that are shipped insecure by default: Countless hosting providers and ISPs do nothing to prevent devices on their networks from being used by miscreants to “spoof” the source of DDoS attacks.
As I noted in a November 2015 story, The Lingering Mess from Default Insecurity, one basic step that many ISPs can but are not taking to blunt these attacks involves a network security standard that was developed and released more than a dozen years ago. Known as BCP38, its use prevents insecure resources on an ISPs network (hacked servers, computers, routers, DVRs, etc.) from being leveraged in such powerful denial-of-service attacks.
Using a technique called traffic amplification and reflection, the attacker can reflect his traffic from one or more third-party machines toward the intended target. In this type of assault, the attacker sends a message to a third party, while spoofing the Internet address of the victim. When the third party replies to the message, the reply is sent to the victim — and the reply is much larger than the original message, thereby amplifying the size of the attack.
BCP38 is designed to filter such spoofed traffic, so that it never even traverses the network of an ISP that’s adopted the anti-spoofing measures. However, there are non-trivial economic reasons that many ISPs fail to adopt this best practice. This blog post from the Internet Society does a good job of explaining why many ISPs ultimately decide not to implement BCP38.
Fortunately, there are efforts afoot to gather information about which networks and ISPs have neglected to filter out spoofed traffic leaving their networks. The idea is that by “naming and shaming” the providers who aren’t doing said filtering, the Internet community might pressure some of these actors into doing the right thing (or perhaps even offer preferential treatment to those providers who do conduct this basic network hygiene).
A research experiment by the Center for Applied Internet Data Analysis (CAIDA) called the “Spoofer Project” is slowly collecting this data, but it relies on users voluntarily running CAIDA’s software client to gather that intel. Unfortunately, a huge percentage of the networks that allow spoofing are hosting providers that offer extremely low-cost, virtual private servers (VPS). And these companies will never voluntarily run CAIDA’s spoof-testing tools.
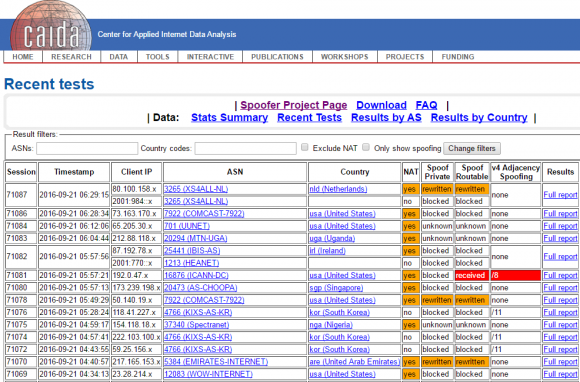
CAIDA’s Spoofer Project page.
As a result, the biggest offenders will continue to fly under the radar of public attention unless and until more pressure is applied by hardware and software makers, as well as ISPs that are doing the right thing.
How might we gain a more complete picture of which network providers aren’t blocking spoofed traffic — without relying solely on voluntary reporting? That would likely require a concerted effort by a coalition of major hardware makers, operating system manufacturers and cloud providers, including Amazon, Apple, Google, Microsoft and entities which maintain the major Web server products (Apache, Nginx, e.g.), as well as the major Linux and Unix operating systems.
The coalition could decide that they will unilaterally build such instrumentation into their products. At that point, it would become difficult for hosting providers or their myriad resellers to hide the fact that they’re allowing systems on their networks to be leveraged in large-scale DDoS attacks.
To address the threat from the mass-proliferation of hardware devices such as Internet routers, DVRs and IP cameras that ship with default-insecure settings, we probably need an industry security association, with published standards that all members adhere to and are audited against periodically.
The wholesalers and retailers of these devices might then be encouraged to shift their focus toward buying and promoting connected devices which have this industry security association seal of approval. Consumers also would need to be educated to look for that seal of approval. Something like Underwriters Laboratories (UL), but for the Internet, perhaps.
THE BLEAK VS. THE BRIGHT FUTURE
As much as I believe such efforts could help dramatically limit the firepower available to today’s attackers, I’m not holding my breath that such a coalition will materialize anytime soon. But it’s probably worth mentioning that there are several precedents for this type of cross-industry collaboration to fight global cyber threats.
In 2008, the United States Computer Emergency Readiness Team (CERT) announced that researcher Dan Kaminsky had discovered a fundamental flaw in DNS that could allow anyone to intercept and manipulate most Internet-based communications, including email and e-commerce applications. A diverse community of software and hardware makers came together to fix the vulnerability and to coordinate the disclosure and patching of the design flaw.
 In 2009, Microsoft heralded the formation of an industry group to collaboratively counter Conficker, a malware threat that infected tens of millions of Windows PCs and held the threat of allowing cybercriminals to amass a stupendous army of botted systems virtually overnight. A group of software and security firms, dubbed the Conficker Cabal, hashed out and executed a plan for corralling infected systems and halting the spread of Conficker.
In 2009, Microsoft heralded the formation of an industry group to collaboratively counter Conficker, a malware threat that infected tens of millions of Windows PCs and held the threat of allowing cybercriminals to amass a stupendous army of botted systems virtually overnight. A group of software and security firms, dubbed the Conficker Cabal, hashed out and executed a plan for corralling infected systems and halting the spread of Conficker.
In 2011, a diverse group of industry players and law enforcement organizations came together to eradicate the threat from the DNS Changer Trojan, a malware strain that infected millions of Microsoft Windows systems and enslaved them in a botnet that was used for large-scale cyber fraud schemes.
These examples provide useful templates for a solution to the DDoS problem going forward. What appears to be missing is any sense of urgency to address the DDoS threat on a coordinated, global scale.
That’s probably because at least for now, the criminals at the helm of these huge DDoS crime machines are content to use them to launch petty yet costly attacks against targets that suit their interests or whims.
For example, the massive 620 Gbps attack that hit my site this week was an apparent retaliation for a story I wrote exposing two Israeli men who were arrested shortly after that story ran for allegedly operating vDOS — until recently the most popular DDoS-for-hire network. The traffic hurled at my site in that massive attack included the text string “freeapplej4ck,” a reference to the hacker nickname used by one of vDOS’s alleged co-founders.
Most of the time, ne’er-do-wells like Applej4ck and others are content to use their huge DDoS armies to attack gaming sites and services. But the crooks maintaining these large crime machines haven’t just been targeting gaming sites. OVH, a major Web hosting provider based in France, said in a post on Twitter this week that it was recently the victim of an even more massive attack than hit my site. According to a Tweet from OVH founder Octave Klaba, that attack was launched by a botnet consisting of more than 145,000 compromised IP cameras and DVRs.
I don’t know what it will take to wake the larger Internet community out of its slumber to address this growing threat to free speech and ecommerce. My guess is it will take an attack that endangers human lives, shuts down critical national infrastructure systems, or disrupts national elections.
But what we’re allowing by our inaction is for individual actors to build the instrumentality of tyranny. And to be clear, these weapons can be wielded by anyone — with any motivation — who’s willing to expend a modicum of time and effort to learn the most basic principles of its operation.
The sad truth these days is that it’s a lot easier to censor the digital media on the Internet than it is to censor printed books and newspapers in the physical world. On the Internet, anyone with an axe to grind and the willingness to learn a bit about the technology can become an instant, self-appointed global censor.
I sincerely hope we can address this problem before it’s too late. And I’m deeply grateful for the overwhelming outpouring of support and solidarity that I’ve seen and heard from so many readers over the past few days. Thank you.




Glad to see your website is back!
I’m convinced it’s about time that the manufacturers of these devices are forced into producing systems that comply to a minimum security standard at least, and – since these devices are aimed at the average citizen – can also be operated in a somewhat safe mode by John Doe.
How could this be achieved? We need strong product liability laws, making manufactures financially liable for the damage that results from poorly implemented security – so that it hurts. This includes the obligation for delivering security updates over a period of – let’s say – five years. If manufacturers fail to comply, they will have to recall their products.
Resellers – especially the big ones like Amazon and Co. – should realize what cheap crap is sold through their platform; sometime this crap will be turned against them.
ISPs and Telco companies should cooperate in banning / not allowing insecure devices.
And we as consumers should be clear about the result of having more and more interconnected devices (do we need them at all??), and buying the latest smartphone / computer / TV / … each and every year.
Yes, I’m fully aware that this will be a Sisyphus work, and there will be loads of manufactures crying out loud, and 99% of the consumers will ignore this. But we need to start before it’s too late.
And yes, I’m still dreaming of a better world … 😉
Laws will not fix this – every law created is countered by creative attorneys and is its own never-ending arms race of law versus loophole. It’s clearly had little to no impact in many other regulatory areas where those actively responsible have some means of blaming it on someone way below them and getting away with it.
I agree that more laws are not particularly helpful in this case. However, how about a class action lawsuit? Seems like this is a known flaw in the design of IoT devices and if the manufacturers continue churning out devices without regard to the damage caused by bad design, they might be found to be legally negligent. In any case, this seems to be a modern version of an externality. https://en.wikipedia.org/wiki/Externality
sadly, something serious will have to happen before normal common sense will result in legislation worldwide to force any vendor to sell reasonably secure product.
with “serious” I mean personal harm / property damage . like flooding a valley behind a dam or something like that.
it is like cars. any country will severely punish you if the car doesn’t have proper breaks and steering. but a lot of accidents had to happen before that was fixed.
My guess for a likely legislative catalyst is a DDoS of a 911 PSAP. Specifically at a time when actual emergencies necessitating fire/rescue result in calls to 911 which aren’t answered, resulting in loss of life.
To quote the immortal words of President Gerald R. Ford “Our long national nightmare is over!”
🙂
Welcome back Brian.
(Vaguely inappropriate innuendos about you “keeping it up” from now on removed for the sake of the children in the audience. 🙂
How about getting reviewers of connected devices to rate the security. That way consumers can make better choices and it may force manufactures to improve. Resistance to hacking should be just as important as frame rates or bits per second.
Do you honestly think the average device reviewer is even marginally qualified to perform a security assessment? I don’t.
Oh, good idea.
There have been French TV Companies that have been targeted last year, including a news channel, and this is clearly censorship, whatever the target we should fight against it.
The great thing about the Internet is it democratizes power, where anyone can make themselves heard no matter big or small they are. The terrible thing about the Internet is it democratizes power, where anyone can make themselves heard no matter big or small they are.
Thank you Google. Really proud of you. Guess we should all buy Google stocks.
Brian, I really missed your posts. Much longer and I would probably have had to deal with withdrawal symptoms 🙂
WELCOME BACK! Glad to see your blog back online! Good article btw.
Welcome back Brian. Excellent article, I am pessimistic as well (since anything that might increase costs or loose “customers” is always fought), but perhaps with the visibility of your site it’ll get some traction.
I wonder, if there was a particular brand or handful of brands of IoT devices involved in this attack, would it be practical to sue the manufacturers for their negligently-insecure firmware? If cheap router or camera makers had some kind of legal liability to the damage that their products cause to third parties, that might provide some incentive for better security…
It’s all of them. Just look back at the other posts regarding the government sponsored hacking company that got hacked. 🙂 If that guy can do that in a couple of weeks time, imagine the scope of IoT and people with nothing but time on their hands to do this research.
In my humble opinion this is one of your most outstanding posts ever. Though I am not a security professional it certainly seems to me that everything you’ve previously written about fits under the broad umbrella of the things you’ve discussed in this post.
“I don’t know what it will take to wake the larger Internet community out of its slumber to address this growing threat to free speech and ecommerce. My guess is it will take an attack that endangers human lives, shuts down critical national infrastructure systems, or disrupts national elections.”
Wow!
The United States of America DID endure a horrific attack on 9/11 that DID cost human lives. Did that event cause everyone to wake up? I keep asking myself that question all these years later. I think, unfortunately Brian, that you’ve only just scratched the tip of the iceberg. You’re gonna be chipping away at this for quite a while. Suggest you advise your family that you might be home late for dinner. Keep up the good work. We look forward to your insight into a very real issue.
Welcome back! Thank you to Google for taking on the protection of such a dangerous journalist. Sadly, you are right. For 99% of journalists or bloggers in a similar situation, they would just be offline, which in some cases means “out of work” until they agree not to say things that offend the DDOSers.
the Internet Society presented their internet hygiene program at the ISC2 Congress in Orlando earlier this month. they named in MANNRS. It was well detailed.
How do you compel companies to fix their stuff, with ever-faster product cycles?
Example: I have an older Kguard camera DVR from late 2010. The latest firmware was from late 2011. It still works fine, and like most “appliances” I expect it to have a lifetime of 10-20 years. I contacted the company in 2013, concerned with the security issues in the DVR. They said “Our RD is working hard checking it. We will let you know when we have firmware update available. ” They never posted updates. This year I asked again, and they replied “Sorry, this DVR have be phase out more then 5 years and we don’t have plant to upgrade the DVR firmware.” i.e. We don’t care.
If IOT devices / “appliances” are to have a lifetime of typical “appliances”, we have to somehow put pressure on the manufacturers to support them accordingly. I’m not sure if legal or media/ “shaming” pressure is the best approach, but something needs to be done.
Have you considered just pulling the power cord?
It sounds to me like the better way to go would be to not use it. The only reason Apple grew to be what it is, is the fact that people en mass are buying their products. The only reason MySpace is all but gone is the fact that people en mass no longer use it (same with AOL). It all seems quite clear to me.
Oh hey! I’m actually working on a dvr from that era, working on a new firmware. got kernel 4.8-rc4 to boot on it, more to follow. Please contact me!
I don’t think it’s possible.
I think the best that can be arranged is behavioral quarantines.
Linux has seccomp-bpf [1] and AppArmor [2] which allow Linux systems to define rules that constrain what applications are expected/allowed to do.
A similar thing could be developed for devices. In order to make it work reasonably well, I think it would have to be a pluggable in-line hardware module (basically 2 rj45 ethernet ports with Power-over-Ethernet, some ram, a microSD reader and a CPU). The device could be addressed initially to define rules (downloading/uploading a profile based on the device it’s quarantining), and then could switch to a read-only mode where it is purely passthrough. Future updates could require inserting the microSD card into a computer. — The advantage of a read-only mode for the appliance is that it shouldn’t be hackable.
A theoretical policy for a device:
allow dhcp for 1 device
allow dns queries for *.google.com
allow dns queries for appliance.example.com
allow connect to {*.google.com,appliance.example.com} on port https
disallow everything else.
I think this would be pretty easy to design and enforce.
It would probably even be possible to design timeout chains so that a DNS query for X which yields IP Y would allow for a TCP connection to Y for time limit Z — possibly based on the timeout for the DNS record for X.
[1] https://en.wikipedia.org/wiki/Seccomp
[2] https://en.wikipedia.org/wiki/AppArmor
You’ve just described a firewall.
The real trick here is making the consumers responsible for their devices. If a device is used in an attack, the ISP should cut them off until the subscriber has remediated the problem. Nothing gets someone’s attention faster than being kicked off the internet.
In the case of compromised ISP equipment, I guess we’re going to have to sue. Krebs may be the first person to have a truly solid case that they’re being negligent. Luckily nobody died, but if the USG thought Snowden was a cyber-pearl-harbor or cyber-9/11 they have a really disturbing wake-up call pending.
Personally, my ISP’s gear was pitched out and replaced with items I own and control. No unsolicited traffic in, and only known systems and ports out. As it should be.
Yes, I’ve described a firewall.
But. Most routers have the same software update problems as IoT devices.
And, many devices connect via WiFi or at least allow local traffic as a default policy. I’m suggesting a model where each device gets its own inline firewall. And devices aren’t allowed to have active cellular / WiFi. If a device has an enabled WiFi radio, then it could look for other networks and eventually crack a nearby network and escape the designated firewall. It could also listen for other MAC addresses and impersonate a device, hoping to escape the firewall rules.
Cellular is even more dangerous than WiFi, as it allows for devices to participate in telephony DDoS or attacks on cellular infrastructure, or possibly impersonation of a cellular basestation.
Glad to see your website is back. Good idea to have a common baseline security standard for networking devices. Operating in safe mode is also viable, since majority use cases can be met with the device working in safe mode.
And yes, thanks to Google, great show.
The weaponozation of this and other attcks concerns me as well. DDoS, Ransomware, Spear phishing are in my opinion ACTIVE campaigns agaisnt someone or some thing.
What can be done? Lets leverage the ISP’s and the CDN’s to follow some guidelines to eliminate this stuff, as you mentioned there exists a methodology right now to limit (DDoS) type of attacks.
Running my own blog I was forced off the internet in a much lower scale way in 2011. I fought as best I could but yes it is VERY easy to silence the individual.
The ease at which people say “its a business decision” to justify something that is WRONG (in my opinion) taints both the business and the writyer but NOT the attacker.
Glad your back, and hang in there.
~zackis
We’ll never be able to guarantee every device attached to the Internet is secure. Pursuing that is futile.
IP’s addresses generating DDOS traffic should be locked by their ISP. Customers would then complain and could be told to either fix/update their equipment or stay offline.
Google/Amazon/etc should band together to name & shame, pressure and ultimately block from their services ISPs that choose not do anything about the ISP’s network generating massive DDos traffic.
I would be inclined to say that ISPs that can’t police their customers should themselves be cut from the net.
I am actually kind of horrified that DNS can use UDP. I suppose at the time it seemed like a good idea, but now it seems like a pretty crummy one.
One thing that will help is serious jail time for those caught. These two Israeli cyber-punks should be extradited to the US for prosecution. If I was the judge, they would get a minimum of ten years.
LOL, like Israel would ever extradite. AIPAC would lobby it six feet underground.
Good to see you back. Thank You for what you continue to do.
Welcome to the HTTPS club finally. We’ve had a ticket reserved for you awaiting pick up at the “will call” window for quite a while. Glad you finally arrived.
Lots of good insight and links here. Allowing spoofed IP addresses is one of the most annoying problems yet to be rectified.
The Good Guys Lose?
I understand the reasons why Akami let you go but it I have asked myself if I would ever buy services from a company that surrendered from a fight. Paid Customer or not, they choose to keep in their network, this is what they do. Given the scale of the attack it should have been seen a test of their capabilities. A challenge worthy of song. Instead they backed out when the going got tough because of short term loss (well maybe a few million a day may not be short term for most).
As a CEO I would have preferred the news story to say, “Akami defeats the greatest DOS attack in history”. Instead this feels like the story actually was, “The Good Guys Lose”.
Not Cool Akami. Prudent, but not cool.
El Jorge
Google Rocks for taking this on…and Brian you rule! IoT’s = crap. Young woman in Austin reported her baby monitor hacked for months as someone watched her and the baby. A little bit of convenience ain’t worth the privacy we give up. Time for class action lawsuits against the manufacturers (ask VW, Toyota, and Honda how much the bad PR alone cost them, let alone the multi-million dolar settlements). http://www.kvue.com/news/local/austin-mothers-warning-after-baby-monitor-hacked/324959027
http://krebsonsecurity.com/2014/01/bug-exposes-ip-cameras-baby-monitors/
I came across a gentleman once that unplugged the power cord to the cam he put in is little boy’s bedroom. He told me that when he realized one morning that he could easily see the video feed from his neighbor’s apartment (from their cam), he then knew his neighbor could just as easily be watching his child.
Not so much a hack really. Just an insecure flaw made into the design of the device.
Given that these things usually run on 2.4Ghz, I would never recommend using them simply because of the radio interference they can create disrupting WiFi. But then 2.4Ghz cordless phones often do the same thing.
There are multiple technical reasons to not use them. Even if your not a tin-foil-hat wearer.
Good to see you are back Brian.
Hopefully this type of attack will challenge the industry to develop solutions to stop this.
Let’s build a better DDOS trap.
It might be helpful to think about the attack from an economic perspective, because robust financials could reduce the need for sophisticated technical solutions.
A DOS of this website can’t prevent the publication of the content through some other channel. And there exist channels (such as Google+) that are essentially DOS-proof.
What a DOS can attack is the monetization of the content on this website, thus making it harder for Brian to produce future content.
Therefore, it would make sense to build an additional income stream that is independent from page views on this site (e.g. a subscription or donation model). Given this robust second income stream, it would be affordable to temporarily mirror recent content on a DOS-proof platform while an attack is tacking place. This would render the DOS ineffective and ultimately reduce the likelihood of future attacks.
I’ve always thought the IETF should endorse the Usenet Death Penalty model. Usenet had problems with spam. At one point Earthlink was their largest single source of this. So, after months of working with the ISP, and failing to get them even to try to fix the problem. They declared a “UDP”, and all participating server operators simply stopped carrying the traffic from Earthlink. As a result, the Earthlink _customers_ demanded it be fixed.
Something similar could be worked out for ISPs that won’t do egress filtering. The IETF should publish a standard which explains the “DDoS Death Penalty”; any ISP who fails to filter the traffic they originate will simply be isolated.
I realize there are some legal hurdles to this, but I still think it’s the right idea. The Internet at large scale is a community of engineers. And bad citizens should be shunned by that community.
I’m agree. There’s already precedent for blacklisting based on behaviors. That’s what RBLs are for email, after all. Why not do the same here? If a provider doesn’t implement BCP38, they don’t get the benefit of connectivity.
If they don’t do this already, I’d especially like to see the Tier 1 providers do this aggressively. If a Tier 2 or below cannot get access, you’d see a hell of a lot of pressure put on them to fix their ways. And if there’s such a thing as a Tier 1 who doesn’t do that sort of ingress filtering, well… I question their competence to be a Tier 1, but aside from that, I can’t see them surviving without being able to peer with others. Anything below a Tier 2 who doesn’t do it would ideally be looked upon as an undesirable customer by the higher level providers, and a bad service by end use customers. Anyway, in that ideal world, the pressure would come from the top tier providers *and* the customers. But that’s a dream at this time, I admit.
Brian, your site is intermittently unreachable as of this time, returning the message “503 Service Temporarily Unavailable” from “shield”.
However, accessing it through Tor works reliably.
Probably some anycast server problems. 😛
I wonder if/when the other shoe will drop. All these IoT devices creating traffic. How much per device? Per customer? What is their traffic profile? What did it cost to carry this garbage? What was the impact on their ISPs? Their neighbors? And when will they get a large bill from their ISP?
Now there’s a class action suit. Negligent design. Damages. Broad base of victims.
And I forgot to mention that Bruce Schneier has been writing about why software liability would be a good things for the last 11 or 12 years.
So, you ask for and advice measures which will help censorship from governments. This will help free speech … especially in/from a country where “free speech” is such a hollow phrase like the US.
As a computer security journalist for over 20 years I can tell you that the fear of DDoS attacks absolutely tempers what I write at times. I don’t want something I write to end up bringing down my employer’s site. Even the hacker groups that claim to be all about honesty and transparency, have no problem bringing down my site if they disagree with what I write. It’s another huge reason why we need to lessen their threat.
how is criminal activity censorship?
That’s a bit of a nitpick. Sure, the strict denotation of “censorship” is the exercise of power by an official body (i.e. government) to legitimately suppress the publication of information. But that’s a bit narrow a viewpoint nowadays.
For some decades now, censorship has been used in casual speech to denote situations where any body or group with any sort of power uses their abilities unfairly to silence opposing voices, normally smaller ones who lack the same levels of power. The word gets misused a lot, but it’s not inaccurate to say that the general perception of the concept is not limited to official bodies use – or misuse – of legal powers. The loose definition actually better captures the sense the general population has on the concept than the strict definition does. Brian is a small voice (no offense! He’s an independent blogger using a resource provided for free, and doesn’t have a news organization’s infrastructure backing him). The DDOS agent(s) is(are) the body with “power” in the form of a botnet likely built from mundane IoT devices. That agent (or those agents) is using that “power” to suppress Brian’s “speech”. Yes, they’re hardly an official body, and yes, it’s completely illegitimate activity, but again: The modern idea is that censorship refers to power structures used unfairly to silence others. So you point out a technically correct criticism, but it’s at odds with general understanding.
Brian, if you want to have a sensorship-proof site, then you’re using the wrong technology
take a look at freenet http://freenetproject.org . in this case trying to DoS you site by requesting it multiple times would make it more popular and accessible, because it would be cached on more nodes.
unfortunately everyone is also using the wrong technology too (web browsers), and it would be tough to get them to install the freenet software
btw you could make an experiment to upload a static version of your site to freenet. i’m sure some of your readers would like it
@a: It appears you do not understand the problem at all.
Freenet is a nice technology — but if you direct 620gbps of attack traffic at it, it will crumble and become completely unusable for anything. The “caching” on more nodes is the same thing Akamai does. The problem isn’t the distribution. The problem is the amount of crap traffic directed at the edge nodes. Freenet is currently around 7k nodes. An attack of the size Brian’s site got would have been around 90mbit/s of continuous traffic per node. Freenet nodes don’t have that much bandwith on average.
Freenet is cool, but please don’t make promises it cannot possibly keep.