A chief criticism I heard from readers of my book, Spam Nation: The Inside Story of Organized Cybercrime, was that it dealt primarily with petty crooks involved in petty crimes, while ignoring more substantive security issues like government surveillance and cyber war. But now it appears that the chief antagonist of Spam Nation is at the dead center of an international scandal involving the hacking of U.S. state electoral boards in Arizona and Illinois, the sacking of Russia’s top cybercrime investigators, and the slow but steady leak of unflattering data on some of Russia’s most powerful politicians.

Sergey Mikhaylov
In a major shakeup that could have lasting implications for transnational cybercrime investigations, it’s emerged that Russian authorities last month arrested Sergey Mikhaylov — the deputy chief of the country’s top anti-cybercrime unit — as well as Ruslan Stoyanov, a senior employee at Russian security firm Kaspersky Lab.
In a statement released to media, Kaspersky said the charges against Stoyanov predate his employment at the company beginning in 2012. Prior to Kaspersky, Stoyanov served as deputy director at a cybercrime investigation firm called Indrik, and before that as a major in the Russian Ministry of Interior’s Moscow Cyber Crime Unit.
In a move straight out of a Russian spy novel, Mikhaylov reportedly was arrested while in the middle of a meeting, escorted out of the room with a bag thrown over his head. Both men are being tried for treason. As a result, the government’s case against them is classified, and it’s unclear exactly what they are alleged to have done.
However, many Russian media outlets now report that the men are suspected of leaking information to Western investigators about investigations, and of funneling personal and often embarrassing data on Russia’s political elite to a popular blog called Humpty Dumpty (Шалтай-Болтай).
According to information obtained by KrebsOnSecurity, the arrests may very well be tied to a long-running grudge held by Pavel Vrublevsky, a Russian businessman who for years paid most of the world’s top spammers and virus writers to pump malware and hundreds of billions of junk emails into U.S. inboxes.
In September 2016, Arlington, Va.-based security firm ThreatConnect published a report that included Internet addresses that were used as staging grounds in the U.S. state election board hacks [full disclosure: ThreatConnect has been an advertiser on this blog]. That report was based in part on an August 2016 alert from the FBI (PDF), and noted that most of the Internet addresses were assigned to a Russian hosting firm called King-Servers[dot]com.
King-Servers is owned by a 26-year-old Russian named Vladimir Fomenko. As I observed in this month’s The Download on the DNC Hack, Fomenko issued a statement in response to being implicated in the ThreatConnect and FBI reports. Fomenko’s statement — written in Russian — said he did not know the identity of the hackers who used his network to attack U.S. election-related targets, but that those same hackers still owed his company USD $290 in unpaid server bills.
A English-language translation of that statement was simultaneously published on ChronoPay.com, Vrublevsky’s payment processing company.
“The analysis of the internal data allows King Servers to confidently refute any conclusions about the involvement of the Russian special services in this attack,” Fomenko said in his statement, which credits ChronoPay for the translation. “The company also reported that the attackers still owe the company $US290 for rental services and King Servers send an invoice for the payment to Donald Trump & Vladimir Putin, as well as the company reserves the right to send it to any other person who will be accused by mass media of this attack.”

ChronoPay founder and owner Pavel Vrublevsky.
I mentioned Vrublevsky in that story because I knew Fomenko (a.k.a. “Die$el“) and he were longtime associates; both were prominent members of Crutop[dot]nu, a cybercrime forum that Vrublevsky (a.k.a. “Redeye“) owned and operated for years. In addition, I recognized Vrublevsky’s voice and dark humor in the statement, and thought it was interesting that Vrublevsky was inserting himself into all the alleged election-hacking drama.
That story also noted how common it was for Russian intelligence services to recruit Russian hackers who were already in prison — by commuting their sentences in exchange for helping the government hack foreign adversaries. In 2013, Vrublevsky was convicted of hiring his most-trusted spammer and malware writer to attack one of ChronoPay’s chief competitors, but he was inexplicably released a year earlier than his two-and-a-half year sentence required.
Meanwhile, the malware author that Vrublevsky hired to launch the attack which later landed them both in jail told The New York Times last month that he’d also been approached while in prison by someone offering to commute his sentence if he agreed to hack for the Russian government, but that he’d refused and was forced to serve out his entire sentence.
My book Spam Nation identified most of the world’s top spammers and virus writers by name, and I couldn’t have done that had someone in Russian law enforcement not leaked to me and to the FBI tens of thousands of email messages and documents stolen from ChronoPay’s offices.
To this day I don’t know the source of those stolen documents and emails. They included spreadsheets chock full of bank account details tied to some of the world’s most active cybercriminals, and to a vast network of shell corporations created by Vrublevsky and ChronoPay to help launder the proceeds from his pharmacy, spam and fake antivirus operations.
Fast-forward to this past week: Multiple Russian media outlets covering the treason case mention that King-Servers and its owner Fomenko rented the servers from a Dutch company controlled by Vrublevsky.
Both Fomenko and Vrublevsky deny this, but the accusations got me looking more deeply through my huge cache of leaked ChronoPay emails for any mention of Mikhaylov or Stoyanov — the cybercrime investigators arrested in Russia last week and charged with treason. I also looked because in phone interviews in 2011 Vrublevsky told me he suspected both men were responsible for leaking his company’s emails to me, to the FBI, and to Kimberly Zenz, a senior threat analyst who works for the security firm iDefense (now owned by Verisign).
In that conversation, Vrublevsky said he was convinced that Mikhaylov was taking information gathered by Russian government cybercrime investigators and feeding it to U.S. law enforcement and intelligence agencies and to Zenz. Vrublevsky told me then that if ever he could prove for certain Mikhaylov was involved in leaking incriminating data on ChronoPay, he would have someone “tear him a new asshole.”
As it happens, an email that Vrublevsky wrote to a ChronoPay employee in 2010 eerily presages the arrests of Mikhaylov and Stoyanov, voicing Vrublevsky’s suspicion that the two men were closely involved in leaking ChronoPay emails and documents that were seized by Mikhaylov’s own division — the Information Security Center (CDC) of the Russian Federal Security Service (FSB). A copy of that email is shown in Russian in the screen shot below. A translated version of the message text is available here (PDF).
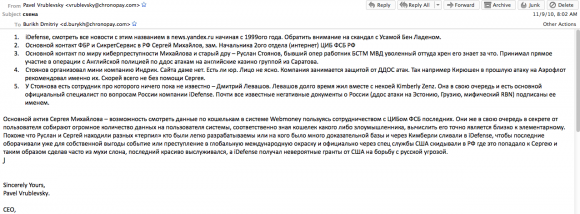
A copy of an email Vrublevsky sent to a ChronoPay co-worker about his suspicions that Mikhaylov and Stoyanov were leaking government secrets.
In it, Vrublevsky claims Zenz was dating a Russian man who worked with Stoyanov at Indrik — the company that both men worked at before joining Kaspersky — and that Stoyanov was feeding her privileged information about important Russian hackers.
“Looks like Sergey and Ruslan were looking for various ‘scapegoats’ who were easy to track down and who had a lot of criminal evidence collected against them, and then reported them to iDefense through Kimberly,” Vrublevsky wrote to a ChronoPay subordinate in an email dated Sept. 11, 2010. “This was done so that iDefense could get some publicity for themselves by turning this into a global news story. Then the matter was reported by US intelligence to Russia, and then got on Sergey’s desk who made a big deal out of it and then solved the case brilliantly, gaining favors with his bosses. iDefense at the same time was getting huge grants to fight Russian cyberthreats.”
Based on how long Vrublevsky has been trying to sell this narrative, it seems he may have finally found a buyer.
Verisign’s Zenz said she did date a Russian man who worked with Stoyanov, but otherwise called Vrublevsky’s accusations a fabrication. Zenz said she’s uncertain if Vrublevsky has enough political clout to somehow influence the filing of a treason case against the two men, but that she suspects the case has more to do with ongoing and very public recent infighting within the Russian FSB.
“It is hard for me imagine how Vrublevsky would be so powerful as to go after the people that investigated him on his own,” Zenz told KrebsOnSecurity. “Perhaps the infighting going on right now among the security forces already weakened Mikhaylov enough that Vrublevsky was able to go after him. Leaking communications or information to the US is a very extreme thing to have done. However, if it really did happen, then Mikhaylov would be very weak, which could explain how Vrublevsky would be able to go after him.”
Nevertheless, Zenz said, the Russian government’s treason case against Mikhaylov and Stoyanov is likely to have a chilling effect on the sharing of cyber threat information among researchers and security companies, and will almost certainly create problems for Kaspersky’s image abroad.
“This really weakens the relationship between Kaspersky and the FSB,” Zenz said. “It pushes Kaspersky to formalize relations and avoid the informal cooperation upon which cybercrime investigations often rely, in Russia and globally. It is also likely to have a chilling effect on such cooperation in Russia. This makes people ask, “If I share information on an attack or malware, can I be charged with treason?’”
Vrublevsky declined to comment for this story. King Servers’ Fomenko could not be immediately reached for comment.





Real good article
Brian–I’m not sure I grasp all the details here, but it sounds like you’re on the verge of publishing another John LeCarre novel. Riveting stuff.
This is better than reading crime novels on sundays. Kudos for that awesome update. Whether or not Kimberly Zenz is actually truthful would be another interesting thing to know.
Imagine! The Russian government stooping to using convicted hackers to fight cybercriminals! Did they steal the idea from us? Or we from them? With all the multifarious businesses, this is a real world of scuzz.
Brain – Spam Nation is a must read and with these recent developments I hope you would consider a 2nd book ?
My review of Spam Nation: https://youtu.be/eQiP_a6VXwQ
keep up the great reporting !
Scott
http://www.HackedAgain.com
You have a really big nose
Get ’em, Krabz!
I wonder if Ramzan Kadyrov got himself into anything recently as he did a few years ago.
That’s not cyber-related much, but Russia’s politics is a strange dogfight to watch.
Very impressive…
Brian, not sure what I am reading here:
“The company also reported that the attackers still owe the company $US290 for rental services and King Servers send an invoice for the payment to Donald Trump & Vladimir Putin, as well as the company reserves the right to send it to any other person who will be accused by mass media of this attack.”
Is Fomenko/King Servers alleging that DJT & VP were directly involved in these attacks?
No, they are trying to be funny, nothing more.
One of the first quotes is so contradictory: We don’t know who it is, but it’s definitely not the Russian Secret Services.
Nothing personal just business.
So pointless to read nothing really here.
This artice is full of complicated words i dont undestood nothing at alll and why would i ?? Becouse to read about someone got arrested…what do i get from this information?? Nothing no information at all police and goverment wasting his time and resourses to arrest some low life criminals. But circus still on…
So im asking again what information i get from here if i read this article ??? How does it change my life ??? No matter someone can steal 5miljon 100miljon our lifes will not change everything will be same still in our everyday daily activities. So pointless
I guess, liquid, that is just a difference between Russian and United States thinking. Here, we still hold onto a hope that, with information, we can make decisions as to how we will proceed with various aspects of action and thought. While it’s true that there are people here who will tell us it’s all a charade; all sides are the same, I have to believe that’s not so.
It becomes harder to know what to believe given the sheer amount of sources of “information” and accompaning noise. There are sources that you can say are generally trustworthy( ( I consider this site one of them). Then there’s the issue of what is actionable, which I think is more to what liquid is saying. We can access reams of information, but what good is it if all it does is affect our mood( usually not for the better)? I try to focus on personally actionable information, and pay less(or no) attention to that which isn’t.
I guess this cyber crooks are highly educated
Then im asking why they do what they do ?
Person who can steal million or can do big frauds.
He have good contacts. Good knowledge and good skills and brain. With his knowledge and skills there is alot more things to do then he can get alot profit. And its all legal but they do what??
They choose illegal way to use all their knowledge to just steal??
Its same thing when kim kardiashan been robbed in france.
First of all the person who is capable to oraginse and execute this kind of things must have so good knowledge and contacts that this contacts and skills will give him 10x times better ways to earn money. And most likely his not even bother with this .
And other thing is all this cybercrooks prey on usa most likely it is usa 8-5 honest tax payer who will pay all this circus.
But then im asking why usa dont do anything about it ?
Why they leave doors open ? And guys who go in to this backdoors and steal then how they know that doors are open??
I undestood if someone with good education can get access but we see alot low life criminals without any education at all even with lack of knowledge of english. And they can still access to alot money also where they learn ?? Until this answer not explained then really no information at all here.
I think it is true, people do not think when they let information out. When they are comfortable, the information comes out, they talk of work at a bar, others listen, gain information. If people not happy, they talk about the bad things. I am sure some people talk for money, others talk for fame or just want to kill the business. There are many documents out there and people can make a guess on what might be the truth. The press will print what makes money and MIGHT be true.
What you read on Kreb’s website is more stable than other places. He will find out information and point fingers. Other news will not do this.
Other news want readers and web site hits. It is a stupid news day when many bad articles say same thing with nothing in it.
I personally think Russia is on life support system. They need hackers to take money from other countries to keep going. So if the Russian hackers get millions, or billions of dollars, then Russia is happy. If the hackers do not play good with each other, they will go to jail and the government will make them look guilty. Then other hackers will do what they are told, or also go to jail.
I think same thing happens in China, but not as much.
Yes it is a circus, but until all learn to shut the mouth and lock the doors, the ability to steal will always be there. Greed will show its true colors one day. let us hope it is soon.
Liquid,
It appears you do not know / understand the biblical teaching on sin. The nature of man. Get it “my way” as Frank would sing it. It is not logical, it is just the “nature of man”. That is what repentance is all about. Turning from “my way” to God’s way. I’ve seen it first hand in myself. Not criminal stuff per se, just “my way”.
And you’ll notice “my way” tends to head down hill over time. Small crimes become bigger crimes. It’s never enough.
Hey Liquid,
Structure. This article lays out structure and relationships of power, or of corruption, depending on how you define it.
You smartly highlight skills and intelligence against the decision of how to employ them. The line between good and bad is drawn differently for different folks, but this article, with your appended moral framework, becomes even more valuable.
Lying, cheating, and stealing are bad from whichever side of the moral line one stands, be that on the cybercriminal or on the cyber-government side. Personally, I think you and I would agree we trust neither…
Now the Church of Prosperity, that’s a different matter… haha…sarc-OFF.
Happy Trails,
Alex
Fantastic and thorough. I have read the 2 New York Times articles.
Great Job!
Who will take bk’s place after he begins his new career writing novels and screen plays for six figure advances? Anyone? Hello? Oh well….
It’s no secret that antivirus companies employ former cybercriminals, so I wouldn’t trust Kaspersky saying they didn’t know about this guy’s history, for example, please make a background check of employees from Polish branch of the company ESET in Cracow from the R&D team, you might find very interesting personas.
You may as well post their names and histories if you’re going to be that specific.
I guess Kaspersky AV subscriptions ought to be rethought very very carefully before you ever renew them.
Good point. Guess I will be using Windows Defender. 🙁
Humpty Dumpty had a great fall. Incredible flight of fancy…
An international cooperation may lead to the state treason sometimes.
I repeat you once again, Brian. You should start to control your mind to understand that Vrublevsky is nothing but a petty crook who has no power and no balls to take part in this case.
By the way, is this photo of Mikhailov?
Too much information we dont know anymore what is false and what is truth.
Russia has money too much but look this way rusdian oligars are the ones who invest money in to usa uk real estate markets and they rise up property prices around world.
So we see money is from western countries then it goes to russia
There it will be cleaned and returned back to countries where money been stolen. So we see russians crimimals run the world not usa washington or queen of england .
The amount of money you are talking about is significant but at the same time is a drop in the bucket compared to the power the US, UK, EU, etc have. Sorry Russian (cyber) criminals, you may think you have power, but its much smaller than you want other to believe…
oh and you still live in Russia which is punishment in itself…
> …UK…
LOL. Yet another funny Britt detected. You’d better go and wax you sash windows.
Based on this information, would you trust Kaspersky antivirus products more or less?
This article does not change my opinion about Kaspersky Corp. It was founded by Eugene Kaspersky, post-KGB training. The fact that he was in KGB tech training school when he and another student came up with the kernel that would eventually become Kaspersky AV. Regardless of Eugene’s integrity, Russian government would not allow such a great Russian asset go without providing some access or backdoor for covert sleuthing. Additionally, Kaspersky has revealed several important cybersecurity operations of national importance to America’s NSA. Their actions make them appear to be an arm of Russian government. These feelings ahve not change
I should have stated that his studies were ‘sponsored by the KGB’ and he was a youth member of communist party. After graduating he then served in Russian military software dev corp.
Also interesting how well capitalism has served him, wonder if he’s still carrying communist card
Great article, if anybody knows about security – its those who are able to get round it!
Takes a thief to catch a thief I guess!
I cancelled my Kaspersky subscription. I just won’t risk it anymore. Not worth it.
Let me try again. Nearly all the news we have so far on the Russian hackers case is based on only one FSB source cited in one article from Tsargard, a conservative TV and news site run by Malofeyev, the same businessman who funded the Russian separatists in Ukraine, and Alexander Dugin, the “Eurasianist” who is part of the ultranationalist movements that find Putin too soft on Ukraine. That is, it’s not a trustworthy source.
Novaya Gazeta is quoting Tsargrad, and cites *on some points* its own FSB/law-enforcement source who may or may not be the same person leaking to Tsargrad. So what we have — as we so often have with Russian stories — are only intelligence leaks targeted to certain media which may or may not be disinformation.
Moscow Times, Rachel Maddow, Politico are quoting Novaya Gazeta quoting Tsargrad.
We don’t have an indictment, lawyers, human rights activists, relatives, neighbours, co-workers — anything — on this case, as we have had with some of the most high-profile cases in Russia.
Novaya Gazeta’s extensive past work on Vrublyovsky is very helpful as background, as is your publication of what Vrublyovsky is saying in emails here. But he’s an ex-con with a complicated relationship with the characters in this story, and most importantly, an associate of Sergei Ivanov, Putin’s former chief of staff, still in the Security Council, who is claimed by the Trump dossier to have been fired over arguments about the handling of the US hack (and we have no idea if that is true; I lean toward thinking it is unlikely given that he is still in the Security Council). So Vrublyovsky is likely involved in Kremlin clan wars and that’s the larger story.
But we need an indictment and lawyers and all the rest. We do not have information about what this case is about, formally or informally, we only have speculation.
It might be related to the DNC hack or the Arizona hack or the Trump dossier. It might be narrowly related to Vladislav Surkov’s email hack. But it may also be related to a run by German Gref, CEO of Sberbank, at the Russian presidency in the 2018 elections that Putin wants to stop. It might also be about mafia turf wars over who gets the lucrative cash stream from online purchases of Aeroflot tickets. The hackers are the lieutenants in these various battles and some have been taken in the skirmish, but we don’t know if they are the ones who are really the protagonists of the story or not.
Hi Catherine,
This smacks so heavily of “fake news” and has a very good chance of being greatly embellished (not by Brian but the sources). The Russians are very proficient at misinformation and false flag operations; it is a keystone of their whole intelligence operation. Think about when they used to fly the same planes over and around during May-day parades to make our intelligence community believe they had more than they really had. A very obvious technique but when your target WANTS to believe the lie, it works. I think the New York Times, DNC, Hillary supporters, and anyone who opposes President Trump want to believe that anything but bad policy and a terribly flawed candidate resulted in the current situation. So they will continue to fan the flames of the Russian boogieman. Your discussion of actual facts will not dissuade people who want to believe a certain narrative. Good job though!!!
Sounds pretty spot-on, Catherine. I’d forgotten about Pavel’s ties to Ivanov, although now that I look I did link to an article about that in my story:
https://krebsonsecurity.com/2011/08/pharma-wars-purchasing-protection/
https://krebsonsecurity.com/wp-content/uploads/2011/08/ivanov-vrub-300×235.png
Never mind the facts – just the narrative tells us something interesting:
– Mr V. is a jailed crook who is released early and goes to work hacking for the FSB
– Mr M is a policeman who investigates hackers
– Mr M seizes documents from Mr V relating to Mr V’s criminal activities
– Those documents are leaked
– Mr M is arrested for treason
We are talking about Russia here – things aren’t going to be too complicated….
Vrublebsky started to work for Mikhailov many years ago. This cooperation was caused by some discreditable stuff relating to early criminal activity of Chronopay which Mikhailov had. It’s necessary to remember that Chronopay was founded as the payment processor for adult websites including absolutely illegal in any jurisdiction.
Your points are well made, Catherine. We will never know the details of this story, nor the full background to it : treason charges mean that the trial(s) wil be held in secret. All we have is leaks, rumour, speculation and deduction – for now, at least.
Bloomberg have a piece by Leonid Bershidsky which adds a litttle to what we know : https://www.bloomberg.com/view/articles/2017-01-30/how-russian-hackers-became-a-kremlin-headache
Would love to have a little more insight into this FSB infighting you alluded to. Also, by not dropping Levashov’s name (though you do link the email contents that name him), do you think some might draw the conclusion that you’re trying to avoid drawing attention to him?
So considering the timing of these arrests, what is the likelyhood that Mikhaylov may or may not have leaked files to the US, and was outed by the trump administration? To conspiracy minded?
I think this post was about cybercrime. But people here are paying more attention to liquid comment. As they dragged bible, sin in the comments. Common people whats the point here to introduce bible and sin?
Brian, hello.
Will be better to let us know about your coop with K. Zenz. It would be more interesting.
Or i can let everyone know about your DEAL in that case (written in article).
Thank you.
p.s. I hope u will let us know about your role in that deal. Bcs i know that.
I think they should have sent the bill for $290 from the unpaid server services to Hillary….the real Slim Shaddy
I wonder if we should stop using Kaspersky antivirus since it’s a Russian software. Any comments Brian?
I dug up an old article from NPR with a comment from Brian stating he still uses Kaspersky from 2015. How do you feel about it now Brian?
http://www.npr.org/sections/alltechconsidered/2015/08/10/431247980/kaspersky-lab-a-cybersecurity-leader-with-ties-to-russian-govt
And I was about to renew my Kasperky (AV only) license with a free after rebate deal I found. Over the past year that I’ve had it, I would definitely rank it as the most aggressive product I’ve used before, stopping unnecessary connections by websites for other traffic they are trying to send, most likely for ads and data collection. So I like the product but is it worth the risk?
Kgb fsb run the world. There is no question about this.
Every crime group are under kgb fsb control.
Together they run all the dark markets and carding forums.
Together they train new motivated money hungry criminals.
No questions about that. But who cares? Nobody dont care.
And what anyone can do it ?? Nothing
Snake oil vendors like Kaspersky never had my trust. Same goes for the Romanian bit defender. Full of blackhats who turned white?
I seriously doubt that Pavel can make the Russian government go after his “enemy” but I have zero doubt that the government tried to turn him around. I also chatted with him when he was running chronopay and he always gave me the impression of a lunatic on drugs.
Very interesting article but unfortunately no juridical proof.
You SO ROCK, Brian!!!
I’m LOVING Spam Nation and am so glad to see they’re finally going to PAY!!!!!
Have a great night!!
Sue
🙂