Last month, KrebsOnSecurity identified U.K. citizen Daniel Kaye as the likely real-life identity behind a hacker responsible for clumsily wielding a powerful botnet built on Mirai, a malware strain that enslaves poorly secured Internet of Things (IoT) devices for use in large-scale online attacks. Today, a German court issued a suspended sentence for Kaye, who now faces cybercrime charges in the United Kingdom.
Daniel Kaye’s Facebook profile page.
In February 2017, authorities in the United Kingdom arrested a 29-year-old U.K. man on suspicion of knocking more than 900,000 Germans offline in a Mirai attack in November 2016. Shortly after that 2016 attack, a hacker using the nickname “Bestbuy” told reporters he was responsible for the outage, apologizing for the incident.
Prosecutors in Europe had withheld Kaye’s name from the media throughout the trial. But a court in Germany today confirmed Kaye’s identity as it handed down a suspended sentence on charges stemming from several failed attacks from his Mirai botnet — which nevertheless caused extensive internet outages for ISPs in the U.K., Germany and Liberia last year.
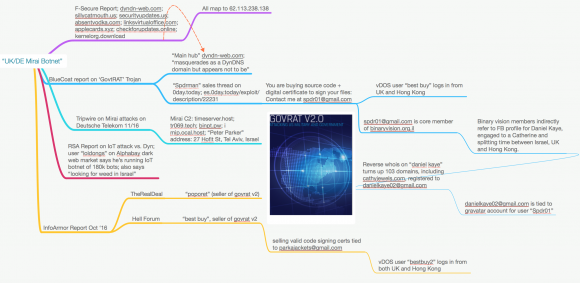
On July 5, KrebsOnSecurity published Who is the GovRAT Author and Mirai Botmaster BestBuy. The story followed clues from reports produced by a half-dozen security firms that traced common clues between this BestBuy nickname and an alter-ego, “Spiderman.”
Both identities were connected to the sale of an espionage tool called GovRAT, which is documented to have been used in numerous cyber espionage campaigns against governments, financial institutions, defense contractors and more than 100 corporations.
That July 5 story traced a trail of digital clues left over 10 years back to Daniel Kaye, a 29-year-old man who had dual U.K. and Israeli citizenship and who was engaged to be married to a U.K. woman.
Last week, a 29-year-old identified by media only as “Daniel K” pleaded guilty in a German court for launching the attacks that knocked 900,000 Deutsche Telekom customers offline. Prosecutors said Daniel K sold access to his Mirai botnet as an attack-for-hire service.
The defendant reportedly told the court that the incident was the biggest mistake of his life, and that he took money in exchange for launching attacks in order to help start a new life with his fiancee.
Today, the regional court in the western city of Cologne said it would suspend the sentence of one year and eight months against Kaye, according to a report from Agence France Presse.
While it may seem that Kaye was given a pass by the German court, he is still facing criminal charges in Britain, where authorities have already requested his extradition.
As loyal readers here no doubt know, KrebsOnSecurity last year was massively attacked by the first-ever Mirai botnet — an attack which knocked this site offline for almost four days before it came back online under the protection of Google’s Project Shield service.
In January 2017, this blog published the results of a four-month investigation into who was likely responsible for not only for writing Mirai, but for leaking the source code for the malware — spawning dozens of competing Mirai botnets like the one that Kaye built. To my knowledge, no charges have yet been filed against any of the individuals named in that story.




I think Germany is setting a bad example in handling punishment for these miscreants. Even though he will be going to Britain, there is no way the German government can guaranty that England will punish him at all if convicted or even if he will be convicted. He should be sentenced to time in both cases and then serve them concurrently.
I concur, Nite!
He should remain in the cooler until
all DDS have ended.
One loss of freedom deserves another.
If this guy was sentenced in the United States ,he would have received a life sentence , like Ross Ulbricht.
No…
This guy wasn’t selling drugs and weapons or trying to hire a hit man… A LOT diff…
The government cares less about physical harm than they do on monetary harm. This guy who doesn’t physically harm a soul will be tried harder than an actual person committing voluntary murder
Ross ulbritch never sold any weapons nor hired Hitman, he was convicted of hosting a site where he would make revenue of people selling drugs on his site, only reason he got life time sentence is the government is trying to make an example of him. Mean while some murderer rapist is doing less time than him. Stupid
@ciueh
https://www.wired.com/2015/02/read-transcript-silk-roads-boss-ordering-5-assassinations/
I think the point t being made is that he was never charged with the hitman stuff because it was essentially entrapment and undertaken by DEA staff who were subsequently charged with illegal acts related to silk road
Oh well, maybe the UK will do better..?
Will prison time really be worth the use of tax payers money? He’s not a dangerous or violent criminal and putting him in with some won’t really benefit anyone. A few hundred hours teaching the elderly to use iPads would be a better use of everyone’s time.
Prison time is not just to punish the past crime(s) of an individual, but also to serve as a deterrent to others.
The punishment should fit the crime. What was the lost productivity/revenue and costs associated with mitigating the attacks? It could easily be calculated to be over $1 million dollars or more likely 10x more.
It would seem teaching the elderly how to use iPads isn’t a symmetrical punishment.
Brian might have some thoughts on what punishment would be fitting from his perspective.
There is very little evidence that “deterrence” works. Just look at the USA’s ineffective and brutal death penalty.
If you’re concerned about the amount he’s cost the taxpayer, why do you want to increase the tax burden by imprisoning him?
Far better to see what we can learn from him and then make him useful.
I love all the comments from anonymous people saying guys like this should be lauded and studied instead of imprisoned. Jail time as a consequence is indeed a deterrent. Not to all, for sure, but to some. Just because one’s actions only amount to a reshuffling of ones and zeros doesn’t mean those actions don’t have real-world negative consequences for countless people. Those who choose to profit or gain despite the destruction they cause by their actions deserve to pay for their crimes when they’re caught.
Other fallacies like comparing criminal hacking to murder are not even worth discussing. Then again it’s important to remember that a significant portion of this site’s readership plays for the cybercriminal team, so what other response would you expect?
Surely you, as an supposedly intelligent man, can’t believe bigger sentences are good in the long term? The main reason USA has so many problems with its prisons are the long-ass sentences that make absolutely no sense if you want people to become functioning members to society after their sentence.
I’m very happy that the German court didn’t see the need for other than a suspended sentence and so should be you. No need to have this guy in a prison for years, I think he pretty much learned his lesson. The argument that bigger sentences prevent people from commiting a crime is thrash and has pretty much been scientifically proven to have no impact.
I don’t think that the german court decided this way because they looked at the whole story. The sentence was probably caused because the german court looked strictly on the crime regarding the german telekom (I also think they are bound to do that according to german law), the attitude of Mr Kaye and his criminal record in terms of prior sentences. If Mr Kaye had been sentenced before the sentence would, most likely, not have been suspended.
Prison in the US is about punishment and the recidivism rates show how effective that is. Elsewhere prison is about rehabilitation and in general the recidivism rates are lower as a result. In the US prisons are just another way to milk the tax payer of cash whilst providing few benefits except for politicians to show they are tough on crime.
He needs to be punished to deter both him from doing it again, and deter others from pursuing illegal projects in the future.
While it may be unfortunate that a nonviolent offender gets jailed with violent offenders, nobody made him break the law. He made his decision all on his own, now he has to live with the consequences.
Don’t do the crime if you can’t handle the cornholing.
Since when did the Germans become bleeding heart push-overs?
You must be kidding, right?
http://www.ironcurtainproject.eu/en/stories/apologies-from-a-minister-president/why-former-stasi-is-treated-with-kid-gloves/
http://www.businessinsider.com/former-nazi-officials-in-germany-post-world-war-ii-government-2016-10
Problem-reaction-solution.=same who bring problems will find the solution:)
Germany is no dummy! Pass Kaye off to the UK courts and let THEM bear the cost of incarceration 😉
Even in scams frauds etc never easy money!! U got to work for profit learn and improve urself. this Atm utopian are just nonsense!!
@Bolt Clifford, I’m sure that Krebs’ readers are likely purchasers of your card skimming services. Using your skillful command of the English language, both in this post and your linked website, I feel confident that sales will skyrocket.
Once again they are sending the WRONG MESSAGE by giving this guy a ‘passola’. Until the punishments start fitting their crimes these hack crews won’t stop.
They all need to get real jobs in the real world and stop being leeches on society.
They need to have mandatory sentences put in place. This would hopefully detour the others.
They need to make examples of these people once they are caught. Otherwise they will go right back to doing this while on parole.
Get real. its whote collar crime.thts why punishment low.
Who remembers the original Star Trek episode “Trouble with Tribbles”? The punishment Cyrano Jones received? I think that would be an appropriate punishment for botnet creators. You make a problem, you clean it up. 17.9 years indeed.
Even if he completely cleaned up the mess (removed Marai from every infected IoT devices that he infected), all those devices would immediately be re-infected from the many other botmaster hopefuls.
I agree with “you make a mess – you clean it up”. But why did the manufacturers make it so easy to mess these devices? These devices are an attractive nuisance…
“The attractive nuisance doctrine applies to the law of torts, in the United States. It states that a landowner may be held liable for injuries to children trespassing on the land if the injury is caused by an object on the land that is likely to attract children.”
…that means IoT devices should be secured against people with the intelligence of children .
Unfortunately, the concept of deterrence does not work well on cybercrime because the perps all believe they are smart enough to get away with the crime.
You can catch many, throw them in jail, and the next still believes he/she won’t get caught. 🙁
If you’re a suspected Botnet controller with multiple nation states competing to send you to prison, you get a Friend Request. If you send Brian a request, he’s going to ignore it. If we’re gonna be friends, I need to hack harder? I’m getting mixed signals.
Nothing personal just business. He do crime he do time. After he use money and live happy.thts it.
Not sure why he wasn’t sentenced to hard time in Germany. These attacks are enormously destructive and disruptive, and there must be consequences when we catch these hackers.
The lengthy and impressive sequence of events (nice digging Krebs) required to identify this cybercriminal give a hint as to how hard it would be to prosecute them for their crimes. Future cybercrime prosecutors may want to steal an idea from organized crime prosecutors, which is to nail these dirt bags for tax evasion. We may not be able to prove how they stole the money, but it’s fairly certain that they didn’t then declare their earnings and pay taxes on it!
funfact, this is the same uk dnm vendor whom went by the handle BestBuy on alphabay and a slew of the other dnm’s
Meanwhile, back in Las Vegas: http://www.theregister.co.uk/2017/08/03/wannacrykiller_cuffed_over_kronos_banking_trojan/ .
German courts have dropped the ball. Unless the west starts to vigoursly defend its commerce structures, it will send a message that it continues to be willing to bear the loss and damage caused by rogue states and their actors.
Back in the day, the robbery of a bank caused a problem to a town or a company. Now, a kid with a cheap computer can write code to bring down hundreds of banks at once, and other parts of the internet to a standstill. Businesses that depend on the internet experience outages. If it were a power company that was so incompitent that they were responsible for browning out businesses, governments might seek compensation. Or, the companies might sue through the court system. Now, it’s individual actors, or gangs, or states, with frequently malicious intent.
Where are the international diplomacy channels on this issue? Where is the UN? Where is the WTO? Are there sactions for transgressions? No. Again, it is individual states, chasing across state lines. Despite it being a sigificiant hub of commerce, there is NOTHING governing the wild west of the internet.
If you said to a person, “would you like to start a business in the wild west”, unless they were particuarly nostalgic, they would probably say no. But the internet? People forget that the internet is one botnet away from being out of service for periods of time. They forget the inordinate amounts of spam spouted by poorly managed devices.
So my point? Germany’s punishment has no bearing on the consiquences of the actions of this individual. It’s beyond a joke. He has crippled parts of the critical infastructure of the world, and Germany says his behavior is no worse than minor possession of an illicit substance.
I hope Theresa does better.
In this latest article, “spoofit.org” provides more details about Daniel Kaye and how he has been running his operations for several years.
Read more about Daniel, aka “I just needed to make some extra money to marry” here.
http://www.spoofit.org/spiderman-a-spot-in-the-net/
This is actually good point to all not to share such kind of information through internets. Nowadays it is not hard to find anything about anybody because of such actions like “sharing of confidential information in social networks” or for example not utilizing correctly your documents.