Skimming devices that crooks install inside fuel station gas pumps frequently rely on an embedded Bluetooth component allowing thieves to collect stolen credit card data from the pumps wirelessly with any mobile device. The downside of this approach is that Bluetooth-based skimmers can be detected by anyone else with a mobile device. Now, investigators in the New York say they are starting to see pump skimmers that use cannibalized cell phone components to send stolen card data via text message.
Skimmers that transmit stolen card data wirelessly via GSM text messages and other mobile-based communications methods are not new; they have been present — if not prevalent — in ATM skimming devices for ages.
But this is the first instance KrebsOnSecurity is aware of in which such SMS skimmers have been found inside gas pumps, and that matches the experience of several states hardest hit by pump skimming activity.
The beauty of the GSM-based skimmer is that it can transmit stolen card data wirelessly via text message, meaning thieves can receive real-time transmissions of the card data anywhere in the world — never needing to return to the scene of the crime. That data can then be turned into counterfeit physical copies of the cards.
Here’s a look at a new skimmer pulled from compromised gas pumps at three different filling stations in New York this month. Like other pump skimmers, this device was hooked up to the pump’s internal power, allowing it to operate indefinitely without relying on batteries.
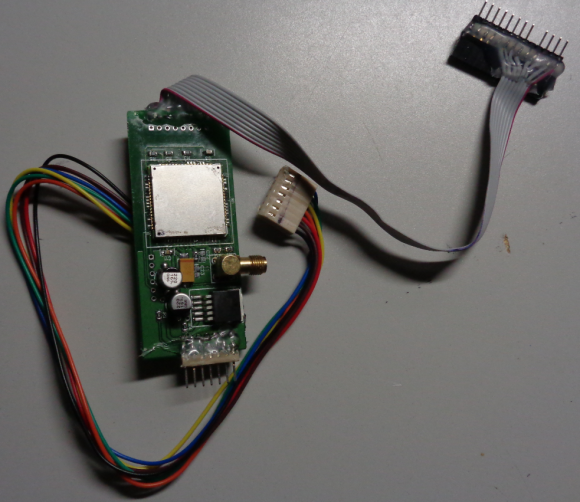
A GSM-based card skimmer found embedded in a gas pump in the northeastern United States.
It may be difficult to see from the picture above, but the skimmer includes a GSM-based device with a SIM card produced by cellular operator T-Mobile. The image below shows the other side of the pump skimmer, with the SIM card visible in the upper right corner of the circuitboard:
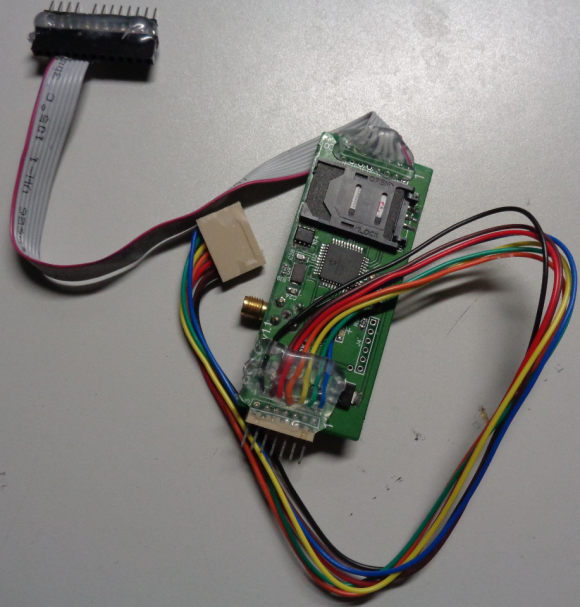
The reverse side of this GSM-based pump skimmer shows a SIM card from T-Mobile.
It’s not clear what type of mobile device was used in this skimmer, and the police officer who shared these images with KrebsOnSecurity said the forensic analysis of the device was ongoing.
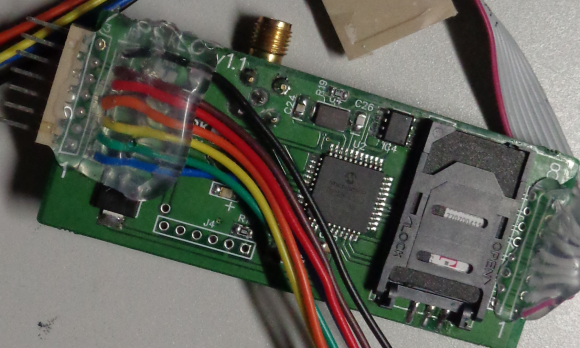
Here’s a close-up of the area around the SIM card:
The officer, who shared these photos on condition of anonymity, said this was thought to be the first time fraud investigators in New York had ever encountered a GSM-based pump skimmer.
Skimmers used at all three New York filling stations impacted by the scheme included T-Mobile SIM cards, but the investigator said analysis so far showed the cards held no other data other than the SIM’s card’s unique serial number (ICCID).
KrebsOnSecurity reached out to weights and measures officials in several states most heavily hit by pump skimming activity, including Arizona, California and Florida.
Officials in all three states said they’ve yet to find a GSM-based skimmer attached to any of their pumps.
Skimmers at the pump are most often the work of organized crime rings that traffic in everything from stolen credit and debit cards to the wholesale theft and commercial resale of fuel — in some cases from (and back to) the very fuel stations that have been compromised with the gang’s skimming devices.
Investigators say skimming gangs typically gain access to station pumps by using a handful of master keys that still open a great many pumps in use today. In a common scenario, one person will distract the station attendant as fuel thieves pull up alongside the pump in a van with doors that obscure the machine on both sides. For an in-depth look at the work on one fuel-theft gang working out of San Diego, check out this piece.
There are generally no outward signs when a pump has been compromised by a skimmer, but a study KrebsOnSecurity published last year about a surge in pump skimming activity in Arizona suggests that skimmer gangs can spot the signs of a good mark.
Fraud patterns show fuel theft gangs tend to target stations that are close to major highway arteries; those with older pumps; and those without security cameras, and/or a regular schedule for inspecting security tape placed on the pumps.
Many filling stations are upgrading their pumps to include more physical security — such as custom locks and security cameras. In addition, newer pumps can accommodate more secure chip-based payment cards that are already in use by all other G20 nations.
But these upgrades are disruptive and expensive, and some stations are taking advantage of recent moves by Visa to delay adding much-needed security improvements, such as chip-capable readers.
Until late 2016, fuel station owners in the United States had until October 1, 2017 to install chip-capable readers at their pumps. Under previous Visa rules, station owners that didn’t have chip-ready readers in place by then would have been on the hook to absorb 100 percent of the costs of fraud associated with transactions in which the customer presented a chip-based card yet was not asked or able to dip the chip (currently, card-issuing banks and consumers eat most of the fraud costs from fuel skimming).
But in December 2016, Visa delayed the requirements, saying fuel station owners would now have until October 1, 2020 to meet the liability shift deadline.
The best advice one can give to avoid pump skimmers is to frequent stations that appear to place an emphasis on physical security. More importantly, some pump skimming devices are capable of stealing debit card PINs as well, so it’s good idea to avoid paying with a debit card at the pump.
Armed with your PIN and debit card data, thieves can clone the card and pull money out of your account at an ATM. Having your checking account emptied of cash while your bank sorts out the situation can be a huge hassle and create secondary problems (bounced checks, for instance).




One thing I find missing in the above comments, or possibly missed it, is that for a cannibalized phone to transmit text, doesn’t it have to be activated and on the phone carrier network? And if that is true, wouldn’t that make somebody traceable to law enforcement? Most of us have had burner-type phones in the past, before smartphones. Even if from a payphone, they had to be activated to get phone calls or text capability.
You buy 2x pre-paid SIMs and burner phones with cash (shades on) then activate and register the SIMs online (public WiFi, VPN, proxy and MAC spoofer kthanx) with someone else’s ID/credentials – a ‘scan pack’ of someone’s current driver’s license/passport/ID is what, $5 USD in bitcoin on SilkRoad – then buy prepaid credit via voucher in cash (shades again) to load the ‘skimmer cell’ (don’t need credit to receive texts, just activated SIM/prepaid no.). Can’t trace the purchase of the SIMs, phones or credit cos cash (and dem shades!) and the SIM IMEI no’s and cell phone numbers are traced back to the poor guy whose wallet was stolen 2 weeks ago (ref stolen IDs for carrier registration).
For the receive-side you don’t need another cell phone – it’s even easier than that. You just text the data to a VoIP SMS number that can literally be anywhere in the world. If this is run by an organized group that can apparently layout high volume PCBs, they can probably manage to post-process the data to feed into an automated system to market the stolen data faster that you can detect fraud… The following is speculation: with such low latency, I’d imagine that somewhere out on the net now is a website that provides on-demand stolen card data, that is “fresh” (stolen seconds before the user wants to spend the electronic funds) then immediately discarded and replaced by the next fresh data. If the cell modem is sending its location data (most 2G+ modems use GPS for time alignment), that site could even localize data stolen so that cards are used in their home territory first. Gotta check those readers before you stick you card in them… I’m also thinking Chip Cards aren’t going to last very long once mag stripes are truly obsolete.
Prepaid would make it tougher to trace but at some point money changes hands and that means either a physical payment or a possibly more-traceable digital one. Even to receive the texts would most likely require some type of paid service.
The fact that these things are hooked into the pump’s power would suggest to me that someone involved with this has pretty intricate knowledge of the internals of those pumps, and for them to also have the master keys makes it seem almost as if someone who works or worked for a pump manufacturing or servicing company is or was involved. I wonder how the data breaks down as far as whether specific makes or models of pump are hit by this type of thing more than others.
Not if the phone is a “burner”. These are prepaid phones that are basically disposable and do not require a contract. For criminal activity they are often purchased through intermediaries to avoid chain of custody.
You could always use cash when you suspect there may be a dubious type of card machine at the gas station.
You can always use your phone inside the store as it is more secure.
How does this interface to the gas pump to perform the skimming? is there something installed on the outside? Inside?
It is rather simple.
1) The crook gains access to the interior of the pump. This is usually through using a key they copied/purchased although it may be possible they simply picked the lock. The locks on pumps are not complex.
2) Once inside, the crook disconnects the wire harness that connects to the card reader that is mounted on the outside of the pump case.
3) The crook then connects his custom made device to the card reader on the pump.
4) The crook then connects the pump wire harness to his custom device. This put the custom device inline with the card reader and the pump computer system. Thus, each transaction on the pump continues to function, but the custom device copies all the communications (data) between the card reader and the pump computer.
That’s about it. The custom devices these crooks use can be purchased through vendors on the dark web or in some situations are created by hand by the crook themselves.
Thanks for the info, my question, how do they install the devices onto the pump?
Pull up and disassemble the housing while no is supposedly looking?
The crooks usually attack pumps that are not well observed or attended. They only need a few minutes to install the skimmer. Sometimes only seconds if they know the pump design and don’t have any issues with the placement.
They also target pumps based upon design since more common designs will likely be targeted to allow for broader market in the dark web for the skimmer devices. Of course, some crooks are technically savvy enough to create their own custom devices for this activity.
Lastly, if the pump design uses the well known lock that uses the same key for all the pumps, they only need the one key to access the pumps that fit the design. Some states are working on or have passed legislation mandating that gas stations use pumps that have unique lock/key configurations for each pump. This legislation is slow going due to gas station interests lobbying that to replace the locks would be costly.
To be honest, even if they do use unique locks for each pump, many of the lock designs they use are not complex and generally easy to pick given time.
My thought: Gas pumps should integrate technical design that would disable the card reader, and provide external visual indication of possible compromise, if the card reader is disconnected from the pump computer for any reason. This is an engineering thing more than anything else. It would make the card reader technology a bit more complex and likely add cost, but the benefits of such a design would be long term.
You’d need to do better than that, since if it was triggered on disconnection they’d simply have to switch to inductive coupling for the skimmer.
Despite new locking mechanisms, crooks also make brute force entry into the pump. The dispensers are actually pretty flexible and the crind door can be popped open. Crooks have also replaced the locks with ones completely stripped of any security features. The station doesn’t know because their keys still work but a paperclip or screwdriver now works just as well.
https://www.wsls.com/news/virginia/roanoke/victims-couldnt-see-card-skimming-device-at-area-gas-station
Cant the pumps themselves be rigged as faraday cages to inhibit signals (BT, 4G, Wifi)? Likewise many gas stations have a metal roof over the pumps-couldnt these be designed to similar effect? basically, at pump you are in a location similar to an aircraft – no smoking, devices in airplane mode…
In theory yes, but I don’t think they need to go that far – the whole pump doesn’t need to be a Farady cage, just the reader and whatever basic control board is in there. The whole reader assembly can be in a welded/potted enclosure and cast into the retail face of the pump – all it needs is 10MBps ST-fiber for data (with a VPN from the pump to the station master computer) and then just low-energy DC power to function (filtered internally). If they used printers and display modules that had an industrial PMMA fiber for serial data – you basically get your hardware firewall right there (output only!!). Have a number pad? Send the data over another PMMA fiber in with a paired scramble key on constrained bytes. There would be nothing to plug into, and EMI compliance would be easier… Biggest reason to get into a gas pump right now is to change the paper roll. If they made printers that didn’t provide access to the internals for the pump face to replace paper, that would also help.
Has anyone successfully created a skimmer than can track/capture/bypass chip verification?
The readers still need to be configured correctly – they must require a chip transaction. There are article describing that the fraud in Europe didn’t stop with the introduction of chip cards, it merely shifted to the next weak point. Card and cash trapping is still technically possible – imagine if you stick a card into a reader, then punch in your pin, but the card doesn’t come out at the end of the transaction. The scammer can still use the PIN and gets your physical card. It’s a bit more obvious yes, but the effect is still the same.
I remember this past October (2016) my brother was with me at a Haunted House. They had a public ATM outside and when he stuck his card in the ATM crashed and kept his card. When the staff called the ATM company, they said they’d send out a service rep next business day and he should just leave his card in the machine. YEAH RIGHT, it was Friday evening!! This was a portable ATM, and since I’ve done Desktop IT and know the ATM was probably running Windows XP – I found the power cable and gave it a cold reboot (“Did you turn it off and on again?”). Credit card spat out as it went though it’s power-on tests…
Whew. It was that or I was going back to my truck to get an axe.
Just for good measure my brother called his CC company and had a new card sent out. You never know – the service phone number might have been a rouse, and the Haunted House staff might have been in on it. You sadly can’t take any of that for granted these days.
Only in the US where cards have a magnetic strip along with chip. The mag strip is coded to tell the POS that it has a chip therefore must use the chip. For a bad guy, all he has to do is recode the mag to make it a non chip transaction. I’ve not heard anyone so far actually clone it successfully but it is possible.
This is the reason why I supported the idea of full chip rollover instead the current half baked process which allows skimmers to migrate to the gas stations because of the required upgrade coming in 2020.
Has there been instances where the gas station owner is involved?
I have only heard of a few isolated instances of cellular GSM skimmers – bluetooth skimmers are far more common
cyber thieves need to upgrade their technology as cellular GSM (2G) is shut down by all carriers except T-Mobile which is in the process of sunsetting the technology. 3G will follow in 2019.
great discussion/comments – thx
Scott
http://www.ScottSchober.com