Peter Yuryevich Levashov, a 37-year-old Russian computer programmer thought to be one of the world’s most notorious spam kingpins, has been extradited to the United States to face federal hacking and spamming charges.

Levashov, in an undated photo.
Levashov, who allegedly went by the hacker names “Peter Severa,” and “Peter of the North,” hails from St. Petersburg in northern Russia, but he was arrested last year while in Barcelona, Spain with his family.
Authorities have long suspected he is the cybercriminal behind the once powerful spam botnet known as Waledac (a.k.a. “Kelihos”), a now-defunct malware strain responsible for sending more than 1.5 billion spam, phishing and malware attacks each day.
According to a statement released by the U.S. Justice Department, Levashov was arraigned last Friday in a federal court in New Haven, Ct. Levashov’s New York attorney Igor Litvak said he is eager to review the evidence against Mr. Levashov, and that while the indictment against his client is available, the complaint in the case remains sealed.
“We haven’t received any discovery, we have no idea what the government is relying on to bring these allegations,” Litvak said. “Mr. Levashov maintains his innocence and is looking forward to resolving this case, clearing his name, and returning home to his wife and 5-year-old son in Spain.”
In 2010, Microsoft — in tandem with a number of security researchers — launched a combined technical and legal sneak attack on the Waledac botnet, successfully dismantling it. The company would later do the same to the Kelihos botnet, a global spam machine which shared a great deal of computer code with Waledac.
Severa routinely rented out segments of his Waledac botnet to anyone seeking a vehicle for sending spam. For $200, vetted users could hire his botnet to blast one million pieces of spam. Junk email campaigns touting employment or “money mule” scams cost $300 per million, and phishing emails could be blasted out through Severa’s botnet for the bargain price of $500 per million.
Waledac first surfaced in April 2008, but many experts believe the spam-spewing machine was merely an update to the Storm worm, the engine behind another massive spam botnet that first surfaced in 2007. Both Waledac and Storm were major distributors of pharmaceutical and malware spam.
According to Microsoft, in one month alone approximately 651 million spam emails attributable to Waledac/Kelihos were directed to Hotmail accounts, including offers and scams related to online pharmacies, imitation goods, jobs, penny stocks, and more. The Storm worm botnet also sent billions of messages daily and infected an estimated one million computers worldwide.
Both Waledac/Kelihos and Storm were hugely innovative because they each included self-defense mechanisms designed specifically to stymie security researchers who might try to dismantle the crime machines.
Waledac and Storm sent updates and other instructions via a peer-to-peer communications system not unlike popular music and file-sharing services. Thus, even if security researchers or law-enforcement officials manage to seize the botnet’s back-end control servers and clean up huge numbers of infected PCs, the botnets could respawn themselves by relaying software updates from one infected PC to another.
FAKE NEWS
According to a lengthy April 2017 story in Wired.com about Levashov’s arrest and the takedown of Waledac, Levashov got caught because he violated a basic security no-no: He used the same log-in credentials to both run his criminal enterprise and log into sites like iTunes.
After Levashov’s arrest, numerous media outlets quoted his wife saying he was being rounded up as part of a dragnet targeting Russian hackers thought to be involved in alleged interference in the 2016 U.S. election. Russian news media outlets made much hay over this claim. In contesting his extradition to the United States, Levashov even reportedly told the RIA Russian news agency that he worked for Russian President Vladimir Putin‘s United Russia party, and that he would die within a year of being extradited to the United States.
“If I go to the U.S., I will die in a year,” Levashov is quoted as saying. “They want to get information of a military nature and about the United Russia party. I will be tortured, within a year I will be killed, or I will kill myself.”
But there is so far zero evidence that anyone has accused Levashov of being involved in election meddling. However, the Waledac/Kelihos botnet does have a historic association with election meddling: It was used during the Russian election in 2012 to send political messages to email accounts on computers with Russian Internet addresses. Those emails linked to fake news stories saying that Mikhail D. Prokhorov, a businessman who was running for president against Putin, had come out as gay.
SEVERA’S PARTNERS
If Levashov was to plead guilty in the case being prosecuted by U.S. authorities, it could shed light on the real-life identities of other top spammers.
Severa worked very closely with two major purveyors of spam. One was Alan Ralsky, an American spammer who was convicted in 2009 of paying him and other spammers to promote the pump-and-dump stock scams.
The other was a spammer who went by the nickname “Cosma,” the cybercriminal thought to be responsible for managing the Rustock botnet (so named because it was a Russian botnet frequently used to send pump-and-dump stock spam). In 2011, Microsoft offered a still-unclaimed $250,000 reward for information leading to the arrest and conviction of the Rustock author.
Microsoft believes Cosma’s real name may be Dmitri A. Sergeev, Artem Sergeev, or Sergey Vladomirovich Sergeev. In June 2011, KrebsOnSecurity published a brief profile of Cosma that included Sergeev’s resume and photo, both of which indicated he is a Belorussian programmer who once sought a job at Google. For more on Cosma, see “Flashy Car Got Spam Kingpin Mugged.”
Severa and Cosma had met one another several times in their years together in the stock spamming business, and they appear to have known each other intimately enough to be on a first-name basis. Both of these titans of junk email are featured prominently in “Meet the Spammers,” the 7th chapter of my book, Spam Nation: The Inside Story of Organized Cybercrime.
Much like his close associate — Cosma, the Rustock botmaster — Severa may also have a $250,000 bounty on his head, albeit indirectly. The Conficker worm, a global contagion launched in 2009 that quickly spread to an estimated 9 to 15 million computers worldwide, prompted an unprecedented international response from security experts. This group of experts, dubbed the “Conficker Cabal,” sought in vain to corral the spread of the worm.
But despite infecting huge numbers of Microsoft Windows systems, Conficker was never once used to send spam. In fact, the only thing that Conficker-infected systems ever did was download and spread a new version of the the malware that powered the Waledac botnet. Later that year, Microsoft announced it was offering a $250,000 reward for information leading to the arrest and conviction of the Conficker author(s). Some security experts believe this proves a link between Severa and Conficker.
Both Cosma and Severa were quite active on Spamit[dot]com, a once closely-guarded forum for Russian spammers. In 2010, Spamit was hacked, and a copy of its database was shared with this author. In that database were all private messages between Spamit members, including many between Cosma and Severa. For more on those conversations, see “A Closer Look at Two Big Time Botmasters.”
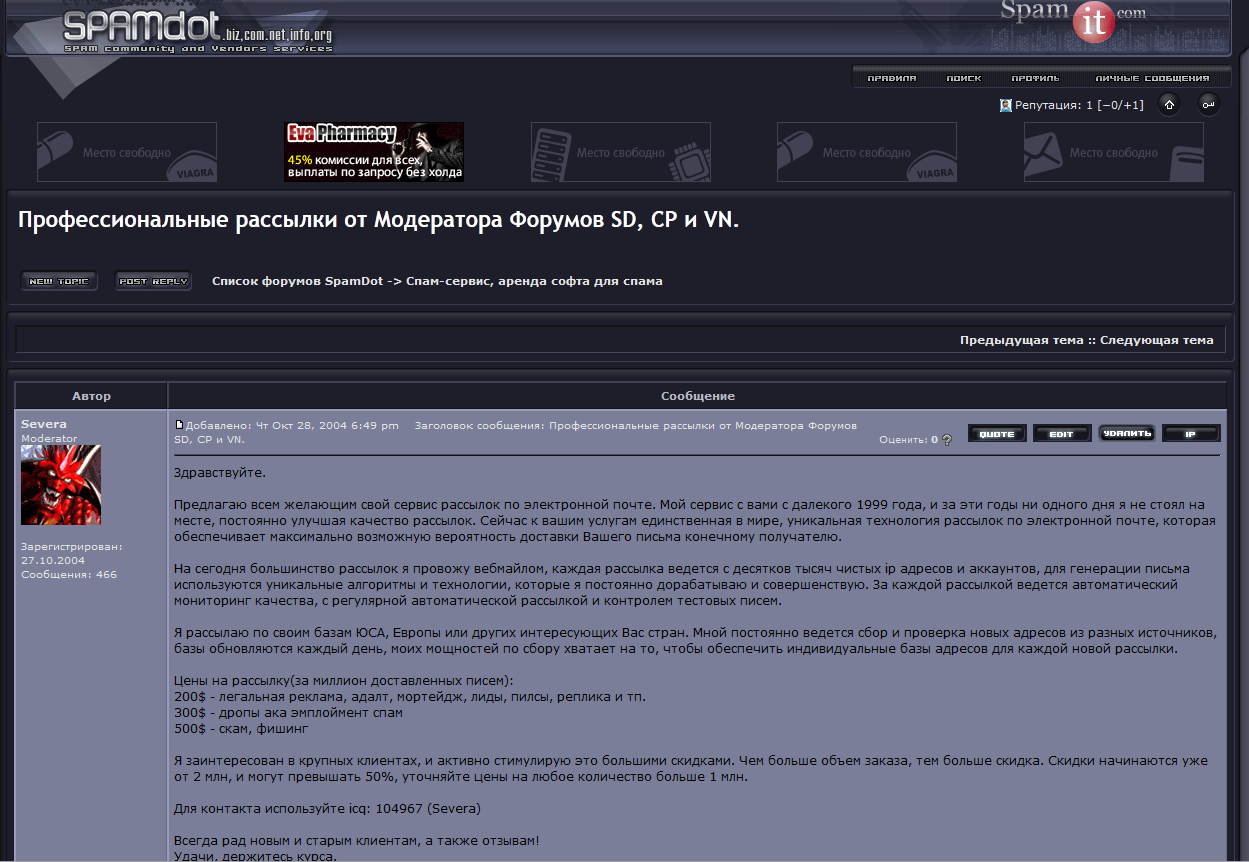
In addition to renting out his spam botnet, Severa also managed multiple affiliate programs in which he paid other cybercriminals to distribute so-called fake antivirus products. Also known as “scareware,” fake antivirus was at one time a major scourge, using false and misleading pop-up alerts to trick and mousetrap unsuspecting computer users into purchasing worthless (and in many cases outright harmful) software disguised as antivirus software.

A screenshot of the eponymous scareware affiliate program run by “Severa,” allegedly the cybercriminal alias of Peter Levashov.
In 2011, KrebsOnSecurity published Spam & Fake AV: Like Ham & Eggs, which sought to illustrate the many ways in which the spam industry and fake antivirus overlapped. That analysis included data from Brett Stone-Gross, a cybercrime expert who later would assist Microsoft and other researchers in their successful efforts to dismantle the Waledac/Kelihos botnet.
Levashov faces federal criminal charges on eight counts, including aggravated identity theft, wire fraud, conspiracy, and intentional damage to protected computers. The indictment in his case is available here (PDF).
Further reading: Mr Waledac — The Peter North of Spamming




Sergey Vladimirovich Sergeev, not Sergey Vladomirovich Sergeev
The DOJ better hope he pleads guilty, because I can’t see how a jury would convict based on the evidence presented here and in linked articles.
At worst, it seems that this guy allegedly took money from criminals to deliver their junk mail, by allegedly taking advantage of huge security holes.
It’s technical and convoluted. There’s no violence or weaponry. How could the DOJ convince a jury of reasonable people to stay awake and convict a guy of a crime where there is no permanent harm done?
Just look at the war on drugs how many non violent criminals are locked up years for far less than what this person is suspected of!
Your logic is a FAIL
This guy broke the law, and deserves to be punished.
People like you claiming he didn’t do anything bad and doesnt deserve to be charge is disgusting.
break the law, get in trouble. All of those people serving time for drugs are there because they broke the law, a law that is CLEAR as day.
Yeah, send him straight to gaol! No need to try him! If he was innocent we wouldn’t be reading about him in the first place!
WOW
If you think there isn’t enough evidence to convict this guy, you’re really uninformed aren’t you
Perhaps you should have look at some of the laws pertaining to cyber crime, internet fraud, etc
A. The ad hominem approach won’t work, dummy. 🙂
B. I’ve read about the relevant criminal laws and find them absurd. I remain unconvinced that this individual’s alleged conduct merits the use of government force and imprisonment.
This stuff belongs in tort claims, not criminal courts.
Sorry, but if half of what the government claims is true, Severa/Levashov is responsible for a crazy amount of spam over the past 10-15 years. And by the way, we’re not just talking about Viagra spam. His services were hired to pimp an unreal amount of phishing and malware campaigns.
In addition, Severa was known to have managed multiple pay-per-install campaigns. These affiliate programs basically hired malware purveyors to seed their pools of infected computers with whatever malware programs his clients were paying him to install.
Assuming these associations are true, it seems appropriate that the USG is using their considerable resources to bring the accused to face charges.
I read your reply and appreciate every word.
My problem here is philosophical, not legal or factual. You make an excellent case for Severa’s alleged unlawful conduct. Yet I find myself feeling that the affected laws are an overreach by government into areas that should be between individuals.
That said, if I were a member of his jury, I’d keep an open mind about it. He certainly sounds like a creep who doesn’t deserve pity.
Your philosophical problem is a problem. You’re getting that from libertarianism but in fact it’s a perversion of libertarian doctrine.
Libertarians hold that “crimes of force or fraud” are legitimate ground for prosecution by government, rather than by civil lawsuits. Spam is fraud, pump & dump scams are fraud, and malware is a type of “force” against your computer and others. QED all prosecutable by gov as crimes.
By your logic, assault & battery ought to be “between individuals” as well. Fail.
You do understand fencing stolen goods is illegal, right? But it seems like he is probably guilty of far more than that. Many people are convicted on the basis of less circumstantial evidence than there is here.
> convict a guy of a crime where there is no permanent harm done?
A thief steals a car which was unlocked. How could he be convicted of a crime where there is no permanent harm done?
I wouldn’t vote to convict a jerk for unlawfully moving an unlocked car.
I would agree to hold him responsible for any loss that occurred, though.
So, if your car was unlocked, you would be okay if I jumped in, took it for a joy ride, and put it back when I was done?
Moving an unlocked vehicle in the US is pretty much allowed in most all jurisdictions, as long as your intent was not theft, vandalism, or other nefarious activity.
One particular case was recently on a TV show about entrapping car thieves: A “bait” car was left either running, or off with the keys in the ignition, and unlocked on a street in a known high crime area of a large metropolitan area. The police staked out the car and waited.
In one case, a nearby person, after conversing with a bouncer outside a nearby bar, was seen to enter the “bait” car, drive it off the street into a nearby parking lot, close it up and lock the doors. As a police car came by, he hailed it and handed the keys over to the cops, and told them what he had done explaining the car had been left parked next to a fire hydrant, which turned out to be true. The police stakeout lead explained that moving an unlocked car off the street from an illegal parking place was completely legal and no charges could be filed, since the intent of the person was not malicious.
“But despite infecting huge numbers of Microsoft Windows systems, Conficker was never once used to send spam.”
My personal experience is I once had a spam sample with a sending IP that CBL-abuseat suspected as confiker linked to a “My Canadian Pharmacy” template to my knowledge–one of perhaps hundreds of spam samples I’ve gone through.
np,he will sit in the jail few years,and after he will be good business man, he will take and use his money and thats it !!
simple !
Wow, what a good use of police resources! Arrest someone that sends Email!!! Good job guys! Keeping the streets safe! That’s who I’m really worried about is people sending email, now I Can walk the streets at night 😀
If we’re to arrest people who are behind annoying and fraudulent mail, let’s lock up postal carriers and marketing professionals.
Apparently you don’t know how to read.
This guy was responsible for infecting (some cases destroying) systems, and spreading malware that STEALs information such as usernames, passwords, social security, and even bank information.
Just because it happened on the internet, doesn’t mean it never happened.
Just because you weren’t affected, doesn’t mean others weren’t.
PETER BROKE THE LAW
Break the law, get charge with the crime
Easy logic, if you can’t understand something so simple, you have no brain.
Keep repeating yourself. Include squats so you’ll burn calories, too.
Yes I would love to spend hundreds of thousands prosecuting a guy that sends email hahahahha! Learn some priorities. Ask any avg person they would be pissed about this. Also we are going to have to house and feed him… maybe i should send some emails too
@Totally “Yes I would love to spend hundreds of thousands prosecuting a guy that sends email.”
Yes, I agree with you. Minimizing this guys crime by saying he “sends email” is like saying a bank robber shouldn’t be charged because “He took a few pieces of paper”.
Maybe you’re new to the infosec space, I don’t know, but if you ask anyone who spent time trying to protect their systems against the deluge of spam/phishing/botnet/viruses etc., you will pretty much get 100% agreement that these people should absolutely be prosecuted for the good of society.
“Sent some email”…pfft.
very solid looking guy, this guy dont look like criminal.
criminals looking have different looking,
criminals are poor and ugly dirty bastards.
this guy cant be criminal. solid guys dont fit in jail…with low life un educated loosers:)
So now we know stay away from
Apple. Google .Yahoo .Sendspace .Foursquare and most of the others US company’s as they will collude with FBI in no time.
Long live Severa – he truly was a mastermind. Even though you may have defeated Severa, you will fail to defeat Anubis. Botnet is nothing compared to the malware I have invented. Very soon, hundreds of millions of emails shall be flooded. I will cause havoc and destruction upon all existing e-mail providers in the world. This will serve as the ultimate revenge for imprisoning my brothers, who are great in spirit and brilliant in mind. Dear cyber security, if you think you are in control of this world, I shall kindly remind you, that you’re not. I will soon unleash the software that will cause complete chaos and disruption in the global email network. Make sure to have lots of coffee around, because you’re going to need it to identify me.
Brace yourselves, mortals. The Bionet is coming.
~ Anubis.
don’t waste your time trying to identify who posted this comment. I used Tor browser and the email is anonymous.
I am not impressed by your threat. I doubt you are better than any of the others who have gotten caught. Sooner or later you will make a mistake that will cause you ruin.
cyber criminals work togehter with illuminati.
thats for sure !!
they want to invent communism world-wide.
and start use rfied chips.
This can’t be all about spamming, Levashov must have been targeted for other more important reasons. In the Spamhaus list of the Top 10 Worst Spammers, he’s only number 7. Of those above him in the list, five are based in the US. In other words, if law enforcement were seriously concerned about reducing spam then they would before now have moved against some of those US-based spammers – one of them has a spam history going back 20 years. Levashov is the only Russian in the Top 10, although there are two Ukrainian outfits in there. When are we going to see the American spammers featuring in one of Brian’s excellent investigative pieces?
I sure hope that Levashov/Severa and his family saw every smidgen of Antonio Gaudi’s public architecture, and took in an FC Barcelona game or two (while Neymar was still with the team)–because that sure was an expensive vacation! If not, they didn’t get their money’s worth!
I wonder how many of the comments for this article that protest Levashev’s prosecution are plants by his confederates and by other spammers and malefactors to defend their own predation. Just sayin’.
Probably a lot of them. Two that I can see have obvious Russian-to-English grammar and usage, and I wasn’t even looking hard.
The more these creeps drop in here to defend themselves, the better.
They may be using TOR, but they will live to regret it, as TOR was originally developed by the US Intelligence Community, who are quite a bit smarter than the criminal losers who think it’s protecting them.
If a “kingpin” used the same passwords for social media as for his cybercrime sites, his cybersec IQ is below room temperature, and the lesser-known crooks can’t be any smarter.
Middle Eastern terrorist groups make similar mistakes and their members get droned. These Russian cybercriminals can at least be glad they’ll be allowed to live, and that US federal prisons are clean and humane, unlike Russian prisons. The goal is to confine them where they can’t harm anyone, and even a “luxury cell” will accomplish that. They might even be allowed to have typewriters.
https://www.thedailybeast.com/tony-soprano-of-cybercrime-snitches-on-russian-hacker
Brian, I believe you’ve covered Shalon’s situation in a previous article.