Software giant Citrix Systems recently forced a password reset for many users of its Sharefile content collaboration service, warning it would be doing this on a regular basis in response to password-guessing attacks that target people who re-use passwords across multiple Web sites. Many Sharefile users interpreted this as a breach at Citrix and/or Sharefile, but the company maintains that’s not the case. Here’s a closer look at what happened, and some ideas about how to avoid a repeat of this scenario going forward.
The notice sent to ShareFile users looked like this:
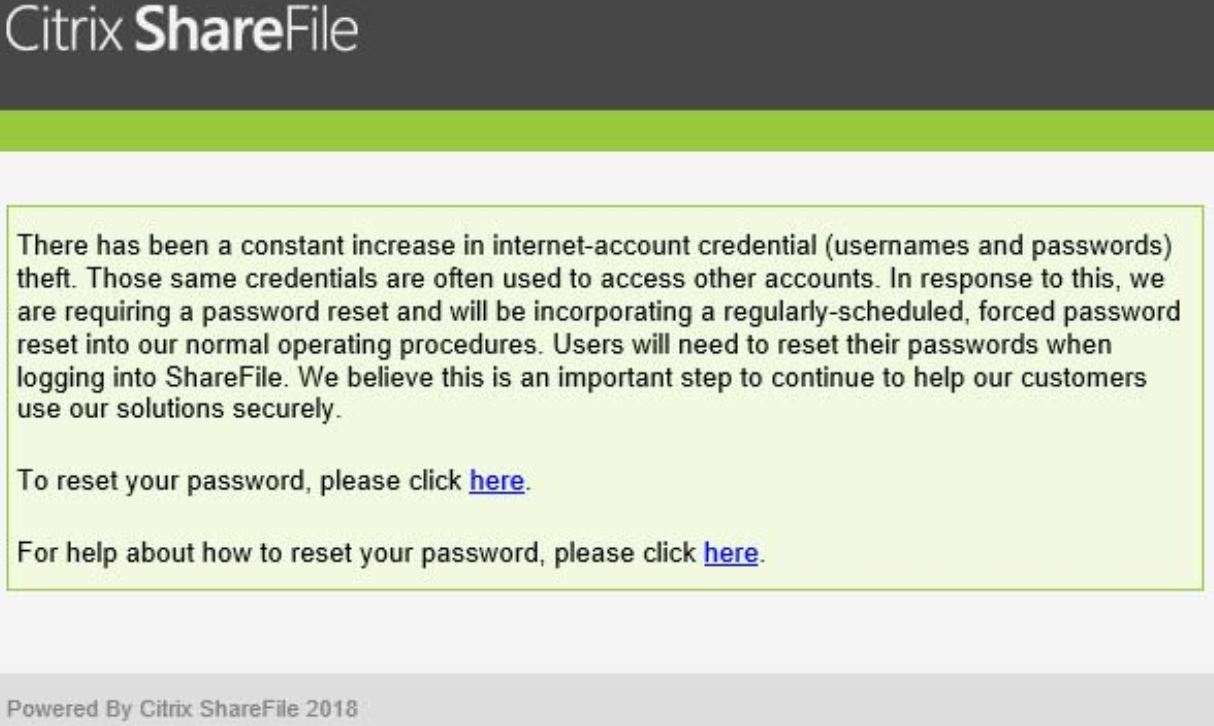
Dozens of readers forwarded the above message to KrebsOnSecurity, saying they didn’t understand the reasoning for the mass password reset and that they suspected a breach at ShareFile.
I reached out to ShareFile and asked them point blank whether this reset effort was in response to any sort of intrusion at Citrix or ShareFile; they said no. I asked if this notice had been sent to everyone, and inquired whether ShareFile offers any form(s) of multi-factor authentication options that customers could use to supplement the security of passwords.
A Citrix spokesperson referred me to this page, which says ShareFile users have a number of options when it comes to locking down their accounts with multi-factor authentication, including a one-time code sent via SMS/text message, as well as one-time passwords generated by support authenticator mobile apps from Google and Microsoft (app-based multi-factor is the more secure option, as discussed here).
More importantly, the Citrix spokesperson said the company did not enforce a password reset on accounts that were using its most robust form of multi-factor authentication (single sign-on solutions, or SSOs). To wit:
“This is not in response to a breach of Citrix products or services,” wrote spokesperson Jamie Buranich. “Citrix forced password resets with the knowledge that attacks of this nature historically come in waves. Attacker’s additional efforts adapt to the results, often tuning the volume and approach of their methods. Our objective was to minimize the risk to our customers. We did not enforce a password reset on accounts that are using more stringent authentication controls. Citrix also directly integrates with common SSO solutions, which significantly reduces risk.”
The company did not respond to questions about why it decided to adopt regular password resets as a policy when doing so flies in the face of password and authentication best practices recommended by the National Institute of Standards and Technology (NIST), which warns:
“Verifiers SHOULD NOT require memorized secrets to be changed arbitrarily (e.g., periodically). However, verifiers SHALL force a change if there is evidence of compromise of the authenticator.”
NIST explains its rationale for steering organizations away from regular forced password resets thusly:
“Users tend to choose weaker memorized secrets when they know that they will have to change them in the near future. When those changes do occur, they often select a secret that is similar to their old memorized secret by applying a set of common transformations such as increasing a number in the password. This practice provides a false sense of security if any of the previous secrets has been compromised since attackers can apply these same common transformations.”
“But if there is evidence that the memorized secret has been compromised, such as by a breach of the verifier’s hashed password database or observed fraudulent activity, subscribers should be required to change their memorized secrets. However, this event-based change should occur rarely, so that they are less motivated to choose a weak secret with the knowledge that it will only be used for a limited period of time.”
In short, NIST says it makes sense to force an across-the-board password reset following a breach — either of a specific user’s account or the entire password database. But doing so at regular intervals absent such evidence of compromise is likely to result in less complex and secure passwords.
Ideally, ShareFile users who received a password reset notice may be able to avoid the next round of password resets by adopting one of the two-step authentication options mentioned above. And I hope it goes without saying, but please don’t re-use a password you used anywhere else.
However, if you are the type of person who likes to re-use passwords, then you definitely need to be using a password manager, which helps you pick and remember strong passwords/passphrases and essentially lets you use the same strong master password/passphrase across all Web sites.
Incidentally, there are several companies — such as auth0 and Okta — that make it easy to integrate with breached password databases like Troy Hunt’s HaveIBeenPwned.com to help proactively prevent users from picking passwords they have used at other sites (or at least at other sites that have been breached publicly).
Whether online merchants are willing to adopt such preemptive approaches is another matter, said Julie Conroy, research director with the Aite Group, a market analyst firm.
“With the reality that such a vast swath of username/password combinations have been compromised, this creates the potential for a ton of inline friction, something that is an anathema to merchants, and which banks work hard to stay away from as well,” Conroy said.
Update: 4:53 p.m. ET: Citrix just published its own blog post about this here.




So, not a security breach, just a breach of best practices.
Sounds like Citrix to me!
I can confirm they forced a reset for people with multifactor in place, I was one of them.
I can also confirm that accounts with multifactor were reset. All our accounts got reset and we have 2FA enabled.
Bizarre that they did this over a weekend with no warning to sys admins. Monday was a fun day.
I received warning the day before (on Sunday,) or more correctly, I found out on Monday when going through my Junk Folder that they had sent a warning on Sunday.
Regarding the NIST recommendations about not expiring passwords, I am curious about whether this is any research to support the contention that users choose weaker passwords when they know they will have to change them.
I, too, can confirm that MFA accounts were forced to reset. Worse, there’s no way to turn off SMS codes, even when signed up for time-based tokens. I contacted support, saying that I have Authy (Google Authenticator) enabled but I’m still getting SMS codes every time I log in. They said there’s no way to turn those off. Seems useless to use the authentication app if they’re still sending the texts. For a service built to be secure and private, seems they’re pretty sloppy on their implementation.
Websites now and days, need to enforce 100 percent across the board use of two-step authentication on all users , otherwise no access should occur.
It’s nice in theory, but that would kill a lot of corporate batch processing at the very least.
Might also consult with MS to see what happens when MFA outages occur.
A forced 2fA/mfa policy would be quite costly, as you’d have a PR and legal nightmare with disability and civil rights advocates.
Throwing up any barrier to use is a clear violation of the ADA, given the lack of authentication products designed for use by the disabled.
Also, the authentication products currently marketed have a cost that’s beyond the means of poor people.
That depends on who the customers are.
The clients’ employees most likely are not disabled such that they cannot use the current software.
That’s a foolish statement if I’ve ever read one. These laws are in place in spite of the majority not being disabled.
And just what form of 2FA would you require? RSA token key fobs? After the SercurID fiasco why anyone would trust RSA Security products again is a mystery.
Yubikeys? Not libre/free software. There’s no way to independently confirm their veracity. They also aren’t free so will cost money either to the user or the service provider. Don’t bet the bottom line on anyone being willing to shell out for any hardware key regardless of who made it.
Cell phone based 2FA? Don’t make me laugh. This is worse than the compromised RSA tokens.
Google Authenticator? Requires Google services and not everyone trusts them. Rightfully so as the service is not open source (can’t be independently reviewed) and is a single source of failure not under user control. People rightfully believe Google is becoming too powerful and pervasive as it is. After changing phones once and having to deal with Authenticator fallout I’ll never use it again.
Email notification of unfamiliar login locations? What if the email account is compromised due to password reuse? This is one of the most common account compromise vectors.
Our vendor just switched to Sharefile about 2 weeks ago and we were also included in this mass reset. It doesn’t seem length of time the password has been set has anything to do with it, as we already had a brand new password… Good job, Citrix.
It makes no difference how old the account is nor how recent the last password change was. Those who tend to reuse passwords across accounts will likely do so with new accounts that they open, too. Mitigating a credential stuffing attack requires this assumption.
Well, this is actually a good time to find a new file sharing hosting service. Talk about customer hostile. Either require MFA or don’t. Require longer passphrase or don’t. But don’t just annoy your customers in the name of security.
Wow, and I filed my email from Citrix this morning in my work block sender folder, assuming it was my employer testing me for security compliance as it regularly does. Let’s see….not expecting to get an email from Citrix, and email contains hotlinks to click on. Is it only me that thinks there could be fundamental issues with approach here?
In other news, Quora, a comment platform similar to Disqus, sent me an email yesterday 3 December telling me their system was breached and that I needed to reset my password. The beat goes on.
NIST Special Publication 800-63B Digital Identity Guidelines Authentication and Lifecycle Management
Direct NIST reference to reference from main document:
https://pages.nist.gov/800-63-3/sp800-63b.html#memsecretver
DOI permalink:
https://doi.org/10.6028/NIST.SP.800-63b
For the reasons stated, I wish Israeli banks and credit-card companies would follow the NIST guidelines, and not force us to change our passwords every 90 days.
Many users of our system (usually third party business contacts) have thought this was a phishing attempt and have reported the email as phishing. The good news is that phishing awareness actually works, even with third party companies. The bad news is that reputable companies start training our users to click on unsollicited password reset requests, which actually creates a new social engineering threat.
^ yep
PayPal sent me a phish message recently. Of all companies, you would think that they would know better. I could take that email exactly as written, change the links, and go phishing myself.
100s of my staff received the message. However we don’t ‘intentionally’ use ShareFile. It obviously is being used by third parties. So every single user marked the message as phishing… CITRIX – a waste of effort
A little heads up would have been nice. Our helpdesk lit up from everyone thinking this was a phishing attack. We use SSO/SAML so our users cannot even change their passwords so that was yet another level of confusion.
Horrible support relating to these issues. I waited 3 hours on Monday just to be told someone will get back with me. Its Wednesday and still haven’t heard a peep. My entire SF system is down
What happened:
I tried to log in to Sharefile and discovered that my password wasn’t working. I used the forgot password link to change it. I only got the email about changing it this morning.
What should have happened:
The account login should’ve succeeded and then informed me that I needed to reset my password and that I would be receiving a password reset link in the mail.
The way in which this was handled has cost countless hours of busy work for IT and security departments that use Citrix services. Worse, it reinforces bad behaviors by asking users to click on a link in an email that they didn’t ask for and were not expecting.
+1
I can confirm that they did NOT force a password reset for SSO, at least for our organization. I did have to reset passwords for each of the four other tenants where I don’t use SSO, though.
I can no longer use ShareFile Sync on any of my systems since Citrix forced this mess on us. Every system that I try to connect from reports “500 Server Error” and “Invalid URL access. Please Contact Administrator. “. As usual Citrix support is useless. I wonder if they are aware of what the A stands for in the CIA triad?
My users received the emails Monday morning, at which point I checked their website and saw a notice to the same effect. Regarding their ShareFile tools, the website has been warning to update client software for many months. They seem to be removing the work ShareFile from their products. Ex: ShareFile Outlook Plugin is now Citrix Files for Outlook.
It’s being sent to email addresses that are not attached to users with Citrix accounts. That’s a good way to prompt an IT department (me) to block your entire email domain.
Members of the security group I participate in have reported that there are multiple versions of the “Citrix” message being received. They provided screen shots. They also report that MalwareBytes, ESET, and Virus Total have been flagging some of the IPs from which these messages are coming from (which is many).
This has created a great deal of confusion for them. Fortunately, our organization has only received about 20 such messages. Unfortunately, we should not have any users subscribing to this service since we must comply with HIPAA and we do not have a formal relationship with Citrix. The site is blocked but I am checking to see if there might still be a hole in our filtering products.
The problem of people who re-use passwords across multiple Web sites has nothing to do with password-guessing attacks. If they hack website A and use that hacked password on website Z, they didn’t have to guess anything.
I wish that Sharefile would have simply directed their users to their website to reset their passwords rather than include a link to do it. How soon before the “bad guys” spoof this email with bad links and are sending out phishing emails?? Already happening would be my guess!
We have been diligently training our users to be wary of unsolicited emails and suspicious links. Along comes Citrix, and sends out a suspicious looking email. Naturally users are junking it or reporting it to Admins.
They did give a heads up, although a very short and ambiguous one. As the admin for Sharefile sites for a few companies, I received an email Sunday at 4:27 PM directing me on what was going to happen.
I sent emails to all my Sharefile users advising them on what to do, but I was getting calls and emails from people before anyone even took time to read the email I had sent.
Well Citrix just opened the door for a nightmare. Cybercriminals now have an easy spoof to guarantee they will get people’s Sharefile login credentials. IT is now telling their users this was a legitimate email and to expect more since Citrix wants more frequent password changes.
This email campaign went against every best practice that all Security Teams are attempting to train end-users on. Our users flagged it as phishing and our email security gateway eventually started flagging them as phishing.
I wish they would have just put up a support notice on their website rather than send these crappy emails that look like phishing attempts…..our Help Desk was also swamped with emails and calls.
At least our users had the awareness not to click on links, but our productivity suffers when we have to jump up to respond to all these false positive “cry-wolfs”…..
Thanks Citrix…..
I just got an email this afternoon from an auditing firm we use about the issue. They indicated that Citrix told them it was in response to a credential stuffing attack they detected.
Does anyone think the correct response to a credential stuffing attack that effects a small portion of the user base – is to punish the entire user base and spam them with phishing emails?
Anyone? Anyone? Bueller?
Citrix should have locked accounts that were targeted. This would have been a more appropriate targeted response.
I received that very Citrix ShareFile “you must change your password” via email over the weekend. In the absence of any other context, I initially figured that it, the email, was a phishing expedition, so I quarantined it.
Now, finding out that the email was as legit as such a thing could be (what about “We will never contact you by email about your account or sensitive/personal information”?), I’m still not inclined to do a pwd-reset, as the account was “required of me” (as a private citizen) just to receive and execute some recent documents, unlikely to be used again.
From a user/citizen’s point of view, this Citrix ShareFile thing is just another example of persistent corporate imposition, setting the user up for a long-term liability. Don’t need it, don’t want it, yet have to “manage and secure” it? Hey, Citrix: Just delete my account!
Just my 2¢-worth.
I wish Citrix had explained why they also expired OAUTH2 tokens – our nightly batch jobs that send out reports failed. Our operators are NOT going to connect the Citrix password reset announcement to a failed batch run w/o explicit notice.