More than 250 customers of a popular and powerful online attack-for-hire service that was dismantled by authorities in 2018 are expected to face legal action for the damage they caused, according to Europol, the European Union’s law enforcement agency.
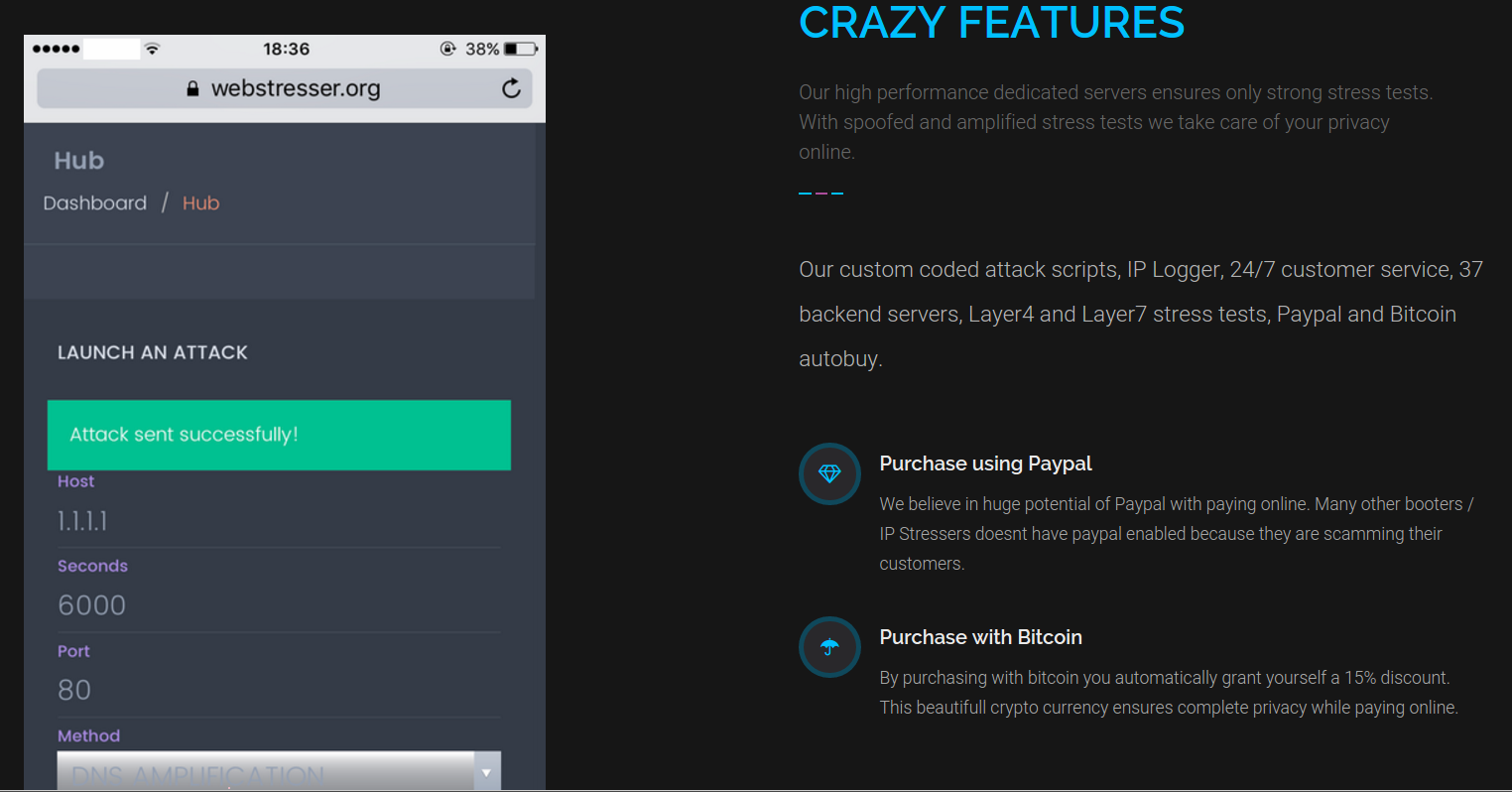
In April 2018, investigators in the U.S., U.K. and the Netherlands took down attack-for-hire service WebStresser[.]org and arrested its alleged administrators. Prior to the takedown, the service had more than 151,000 registered users and was responsible for launching some four million attacks over three years. Now, those same authorities are targeting people who paid the service to conduct attacks.
In the United Kingdom, police have seized more than 60 personal electronic devices from a number of Webstresser users, and some 250 customers of the service will soon face legal action, Europol said in a statement released this week.
“Size does not matter – all levels of users are under the radar of law enforcement, be it a gamer booting out the competition out of a game, or a high-level hacker carrying out DDoS attacks against commercial targets for financial gain,” Europol officials warned.
The focus on Webstresser’s customers is the latest phase of “Operation Power Off,” which targeted one of the most active services for launching point-and-click distributed denial-of-service (DDoS) attacks. WebStresser was one of many so-called “booter” or “stresser” services — virtual hired muscle that even completely unskilled users can rent to knock nearly any website or Internet user offline.
Operation Power Off is part of a broader law enforcement effort to disrupt the burgeoning booter service industry and to weaken demand for such services. In December, authorities in the United States filed criminal charges against three men accused of running booter services, and orchestrated a coordinated takedown of 15 different booter sites.
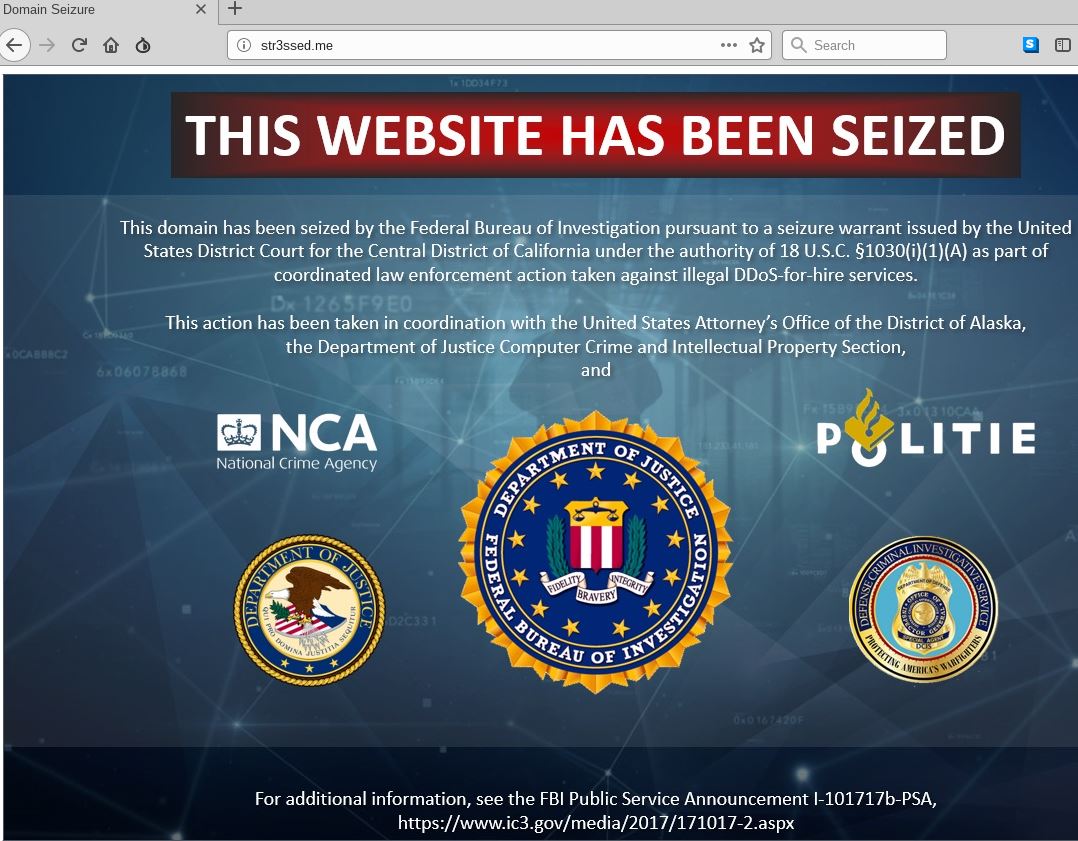
This seizure notice appeared on the homepage of more than a dozen popular “booter” or “stresser” DDoS-for-hire Web sites in December 2018.
The takedowns come as courts in the United States and Europe are beginning to hand down serious punishment for booter service operators, their customers, and for those convicted of launching large-scale DDoS attacks. Last month, a 34-year-old Connecticut man received a 10-year prison sentence for carrying out DDoS attacks a number of hospitals in 2014. Also last month, a 30-year-old in the United Kingdom was sentenced to 32 months in jail for using an army of hacked devices to crash large portions of Liberia’s Internet access in 2016.
In December 2018, the ringleader of an online crime group that launched DDoS attacks against Web sites — including several against KrebsOnSecurity — was sentenced to three years in a U.K. prison. And in 2017, a 20-year-old from Britain was sentenced to two years in jail for renting out Titanium Stresser, a booter service that earned him $300,000 over several years it was in operation.
Many in the hacker community have criticized authorities for targeting booter service administrators and users and for not pursuing what they perceive as more serious cybercriminals, noting that the vast majority of both groups are young men under the age of 21 and are using booter services to settle petty disputes over online games.
But not all countries involved in Operation Power Off are taking such a punitive approach. In the Netherlands, the police and the prosecutor’s office have deployed new legal intervention called “Hack_Right,” a diversion program intended for first-time cyber offenders. Europol says at least one user of Webstresser has already received this alternative sanction.
“Skills in coding, gaming, computer programming, cyber security or anything IT-related are in high demand and there are many careers and opportunities available to use these wisely,” Europol said.
According to U.S. federal prosecutors, the use of booter and stresser services to conduct attacks is punishable under both wire fraud laws and the Computer Fraud and Abuse Act (18 U.S.C. § 1030), and may result in arrest and prosecution, the seizure of computers or other electronics, as well as prison sentences and a penalty or fine.




“vast majority of both groups are young men under the age of 21 and are using booter services to settle petty disputes over online games.”
That pretty much sums it up on this article
That pretty much sums up those who SWAT as well. As we know, that can have deadly consequences.
I bet there is overlap between the two groups.
Agree , they all hang out on Discord
Yeah, and they probably all like good french fries as well. So what?
There’s a logical fallacy concept you should look into, called “hasty generalization.”
Whatever dude, you’re the only one here with an illogical phallus.
Everyone uses Discord….
Discord tends to be popular in certain groups but outside of them its not particularly popular.
Its like saying IRC is extremely popular because I go onto IRC and a some of the people I know are also on IRC. Does that mean that IRC is super popular with everyone? Of course not.
Small sample sizes, particularly of the “well it’s true for me and my friends” variety, generally doesn’t bode well for genuinely accurate statements.
Makes sense. Discord is only used by gamers and pedophiles after all.
The idea of a diversion program makes way more common sense than sending some kid to Federal prison for 10+ years for hiring a service to boot a gaming competitor off the internet. Conversely, the person who hired the same service to boot hospitals offline deserves a 10 year prison service.
That is exactly what Hack_Right does. It only applies to first time offenders who caused limited harm. More serious crimes or multiple offenders are not eligible.
https://nltimes.nl/2018/12/18/dutch-police-send-young-hackers-intern-companies
There is always a chance that giving them more training and tools might make them even more dangerous too. Let’s hope the perpetrator has a change of heart and mind, if said person sees the advantages of going straight.
Cough Dendroid cough
There’s also the thought that if they’re using a stresser/booter that they’re not very skilled to begin with, is there a lot of need for script kiddies?
Exactly – I should have said a very low chance! LOL!
I agree, there needs to be harsher punishment to fit the crime. In the case of the hospital DDoS, like you said, I do agree they should get the full punishment as that affects more than 1 person and it affects people’s lives/well-being. However, on the other side, some young, punk, gamer booting off 1 person because he wants to win a match should not get the same amount of time — in my opinion.
As the list of customers becomes public, I am curious to know if any (even one) of them used Webstresser in the way its operators claimed it was meant for (e.g. to test your own network’s security). And if there are any such people, will they also be prosecuted?
I’m waiting for how those cases, if they exist, will unravel too. Prosecuting somebody for him/her making use of a potentially harmful tool to test the scenarios that type of tools could create seems kinda nonsensical.
Easy enough to prove. I suspect there’s probably like only 1 legit customer in 10,000 though. If you were legit, you’d have a contract with a customer who asked you to test such things. Or you’d have paystubs from your employer and an order from a boss.
If you were legit cybersecurity pro for hire, you’d know that these were super shady things from all the news about them in recent years and have made a paper trail on purpose if you ever had a legit need to use one to CYA.
What you wouldn’t have is an xbox account full of taunts that you’d run someone off the internet, followed 5 minutes later by payment to the service.
I suspect that webstresser kept enough logs to track down those customers. And if so, it likely contains information about which sites a customer asked to be “stressed”. If that’s the case, then someone could easily demonstrate that it was their own site they directed the attack against.
I believe in some types of crimes there doesn’t have to be a complaint for there to be a actionable offense (I’m thinking UK’s “Afray” laws), but I suspect this isn’t one of them. I.e., it would be like hiring a known criminal organization to file your tax returns “totally legitimately”. Is that criminal? (Maybe in terms of “aiding and abbetting” by simply paying for perfectly legal services??)
I have been charged with ddos attacks against my own network. So yes they will be prosecuted.
“to test your own network’s security” is just a canard used to try to absolve themselves of legal liability. If you really want to test your own network security you install Kali Linux on a good laptop, get a bit of training, then actually test your network security with the tools implemented in that distribution. Otherwise the claim is meadow muffins, IMHO.
Bitcoin, no surprise. Paypal? What? Why is it doing business with such sites?
I never payed for webstressers services.
I was thinking but I Don’t Know how I Can use webstresser to make money?
I was doing carding Years ago but it seems to me its no working anymore.
its getting harder to Get in good online business.
I Even invested in bitcoin then it suddenly dropped.
I hope crypto bull run Will start I invest and earn money.
While the ““vast majority” might be petty gamers, there are certainly a fair number of extortionist and internet terrorists hiding among those gamer users. Malicious users deserve to be brought to justice.
The days of DDoS need to be over. Can’t come soon enough.
If you’re interested in how cybersecurity-related cases (like this one) are generally being prosecuted in the US and don’t want to go to law school, there’s actually a fairly new part-time / one-year Master’s program for execs at NYU. It’s a joint program between NYU Law and NYU Tandon (engineering school): https://cybersecurity-strategy-masters.nyu.edu/
since you always get the best education from a university.. err i mean diploma mill…
that have put multiple generations in massive debt and taken advantage of… okay ill stop but yeah higher ed is beyond broken, go away
Please, Netherlands, and other liberal countries, do NOT treat these criminals as some talented computer hackers. It doesn’t take too much brain power to DDoS someone. Those are not computer geniuses.
People who commit those “crimes” are like 12-21 years old, they didn’t even grow up yet, they don’t even realise the consequences of their cyber behavior.
And if they got great ambition for IT why not?
I think “Hack_Right” is a great innovation, for the youth and the government, it will teach them to develop skills in a legal way and also some law.
In my opinion some country’s can take this as an example, instead of putting them in jail to scare them of.
Agreed!
“attacks against commercial targets for financial gain” – Europe police prattle
This is the biggest baloney.
No one hires these junk services to make money. They do it for revenge, to annoy, to impress their friends. Not for financial gain.
Web-stress services are only for unpleasant kids and large ani.
a little off topic but was this at all related to thr xdedic seizure?
Why are the law enforcement officials who “seized” the str3ssed.me web site still hiding it behind Crimeflare?
What is the ACTUAL IP address where this website is ACTUALLY hosted, and why is Interpol hiding that info from us?
Some of us, at least, are curious, and would like to know exactly what kinds of OTHER and ADDITIONAL nefarious crap may still be being hosted on the exact same network.
Also, this European GDPR-inspired crap which apparently allows the identities of the GUILTY to be protected is just that, utter crap. Now it apparently even extends to guilty networks!
None of this makes any sense on the face of it. Why did Interpol “seize” the web site at all? Could they really not even convince the Montenegrins to simply terminate the domain registration for the str3ssed.ME domain name? If not why not? It’s their TLD after all!
This is a swell way for Montenegro to enter into the European Union! They should certainly start out by selling .ME domain names to cybercriminals and then refusing to de-register those, even when asked by law enforcement.
Swell. Just swell.
Three swells and two craps!
Try some of that European decaf coffee.
Very good. Interesting read. But, why have the police not taken over the server? Or taken it down? There may be legit business’s on that server. Remember not everything on a server is bad, that server helps someone else communicate, do business, or download porn. It may have been an unsecured portion of someone’s else’s server. Or a honey pot left in the sun, to see what else shows up. Oh, and , yeah, stress testing a web site is legal, if done for the right reasons and by the right people. It should have been covered in part of security training. And the comment about script kiddies, poor analogy, what is a program?
G0d I am so glad I have nothing to do with company’s like these anymore. Keeping myself out of trouble and all legal.
Good read Brain. Every time I visit your site I find another reason to stay out of that scene.. screw hackforums and all that stupid inmature stuff.
You already have the right attitude. Having someone fix the tying/grammar errors on your website will help you get even more clients.
Contact me via email:
justin@techfriendz.co