Godaddy.com, the world’s largest domain name registrar, recently addressed an authentication weakness that cybercriminals were using to blast out spam through legitimate, dormant domains. But several more recent malware spam campaigns suggest GoDaddy’s fix hasn’t gone far enough, and that scammers likely still have a sizable arsenal of hijacked GoDaddy domains at their disposal.

On January 22, KrebsOnSecurity published research showing that crooks behind a series of massive sextortion and bomb threat spam campaigns throughout 2018 — an adversary that’s been dubbed “Spammy Bear” — achieved an unusual amount of inbox delivery by exploiting a weakness at GoDaddy which allowed anyone to add a domain to their GoDaddy account without validating that they actually owned the domain.
Spammy Bear targeted dormant but otherwise legitimate domains that had one thing in common: They all at one time used GoDaddy’s hosted Domain Name System (DNS) service. Researcher Ron Guilmette discovered that Spammy Bear was able to hijack thousands of these dormant domains for spam simply by registering free accounts at GoDaddy and telling the company’s automated DNS service to allow the sending of email with those domains from an Internet address controlled by the spammers.
Very soon after that story ran, GoDaddy said it had put in place a fix for the problem, and had scrubbed more than 4,000 domain names used in the spam campaigns that were identified in my Jan. 22 story. But on or around February 1, a new spam campaign that leveraged similarly hijacked domains at GoDaddy began distributing Gand Crab, a potent strain of ransomware.
As noted in a post last week at the blog MyOnlineSecurity, the Gand Crab campaign used a variety of lures, including fake DHL shipping notices and phony AT&T e-fax alerts. The domains documented by MyOnlineSecurity all had their DNS records altered between Jan. 31 and Feb. 1 to allow the sending of email from Internet addresses tied to two ISPs identified in my original Jan. 22 report on the GoDaddy weakness.
“What makes these malware laden emails much more likely to be delivered is the fact that the sending domains all have a good reputation,” MyOnlineSecurity observed. “There are dozens, if not hundreds of domains involved in this particular campaign. Almost all the domains have been registered for many years, some for more than 10 years.”
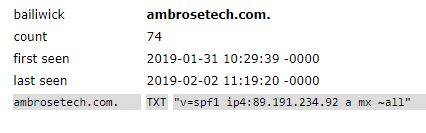
A “passive DNS” lookup shows the DNS changes made by the spammers on Jan. 31 for one of the domains used in the Gand Crab spam campaign documented by MyOnlineSecurity. Image: Farsight Security.
In a statement provided to KrebsOnSecurity, GoDaddy said the company was confident the steps it took to address the problem were working as intended, and that GoDaddy had simply overlooked the domains abused in the recent GandCrab spam campaign.
“The domains used in the Gand Crab campaign were modified before then, but we missed them in our initial sweep,” GoDaddy spokesperson Dan Race said. “While we are otherwise confident of the mitigation steps we took to prevent the dangling DNS issue, we are working to identify any other domains that need to be fixed.”
“We do not believe it is possible for a person to hijack the DNS of one or more domains using the same tactics as used in the Spammy Bear and Gand Crab campaigns,” Race continued. “However, we are assessing if there are other methods that may be used to achieve the same results, and we continue our normal monitoring for account takeover. We have also set up a reporting alias at dns-spam-concerns@godaddy.com to make it easier to report any suspicious activity or any details that might help our efforts to stop this kind of abuse.”
That email address is likely to receive quite a few tips in the short run. Virus Bulletin editor Martijn Grooten this week published his analysis on a January 29 malware email campaign that came disguised as a shipping notice from UPS. Grooten said the spam intercepted from that campaign included links to an Internet address that was previously used to distribute GandCrab, and that virtually all of the domains seen sending the fake UPS notices used one of two pairs of DNS servers managed by GoDaddy.
“The majority of domains, which we think had probably had their DNS compromised, still point to the same IP address though,” Grooten wrote. That IP address is currently home to a Web site that sells stolen credit card data.
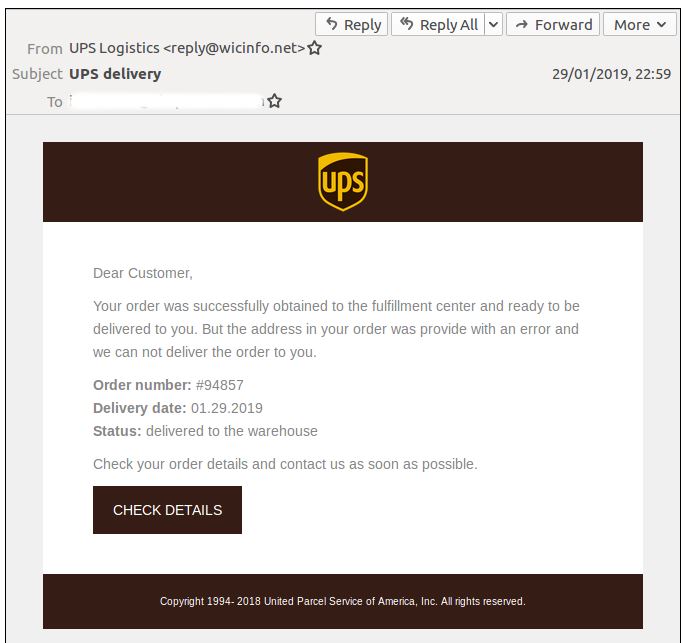
The fake UPS message used in a Jan. 29 Gand Crab malware spam campaign. Source: Virus Bulletin.
Grooten told KrebsOnSecurity he suspects criminals may have succeeded at actually compromising several of GoDaddy’s hosted DNS servers. For one thing, he said, the same pair (sometimes two pairs) of name servers keep appearing in the same campaign.
“In quite a few campaigns we saw domains used that were alphabetically close, [and] there are other domains used that had moved away from GoDaddy before these campaigns, yet were still used,” Grooten said. “It’s also interesting to note that hundreds — and perhaps thousands — of domains had their DNS changed within a short period of time. Such a thing is hard to do if you have to log into individual accounts.”
GoDaddy said there has been no such breach.
“Our DNS servers have not been compromised,” Race said. “The examples provided were dangled domains that had zone files created by the threat actor prior to when we implemented our mitigation on January 23. These domain names were parked until the threat actors activated them. They had the ability to do that because they owned the zone files already. We’re continuing to review customer accounts for other potential zone entries.”
First emerging in early 2018, Gand Crab has been dubbed “the most popular multi-million dollar ransomware of the year.” Last week, KrebsOnSecurity was contacted by a company hit with Gand Crab in late January after an employee was taken in by what appears to be the same campaign detailed by Virus Bulletin.
Charlene Price is co-owner of A.S. Price Mechanical, a small metal fabrication business in Gilbert, South Carolina. Price said an employee was tricked into infecting one of their hard drives with Gand Crab, which encrypted the drive and demanded $2,000 in bitcoin for a key needed to unlock the files.
While Price and her husband consulted with tech experts and debated what to do next, the extortionists doubled the ransom demand to $4,000.
Sites like nomoreransom.org distribute free tools and tutorials that can help some ransomware victims recover their files without paying a ransom demand, but those tools often only work with specific versions of a particular ransomware strain. Price said the tool nomoreransom.org made available for Gand Crab infections was unable to decrypt the files on her scrambled hard drive.
“It’s not fair or right and this is unjust,” Price said. “We have accepted the fact, for now, that we are just locked out our company’s information. We know nothing about this type of issue other than we have to pay it or just start again.”
Update: 2:55 p.m. ET: Added statement from GoDaddy.




Very interesting write-up, thank you for your time spent on the article and researching this! As for the last statement from Price: “we know nothing about this type of issue” is such a haunting statement of our current InfoSec society. Most of these ransomware attacks are entirely preventable, but it’s interesting to see how attackers are starting to become more innovative in their delivery. It’s making it harder to spot and avoid in some cases.
“Most of these ransomware attacks are entirely preventable”
^This
“^This”
^This
And no hard drive backup to employ…. lesson learned the hard way…
This ^^
You have no idea how many complaints that I’ve sent to abuse(at)godaddy(dot)com in the last ten years alone, regarding spam and phishing abuse.
Well, I’m done with GoDaddy since 2003. They said one of my domains was under attack so they decided to delete it instead of removing it from the DNS. Then they wanted to charge me over $100 to recover it for a mistake they made. I complained to several entities (BBB, ICANN, etc.) but GoDaddy refused my case and deleted my account. I ended up losing my domain.
Once upon a time, GoDaddy was an excellent operation to deal with. But I’ve observed a marked decline since it was sold to a group of hedge funds (as in “profits come first, everything else is secondary”) in 2011. A shame.
That seems to be the way it goes today. I agree, this really is a shame as they used to be much more reputable than they are today.
That’s a good point. Have you noticed a dramatic increase in the amounts of times you report spam and phishing over each year? I ask because at work it seems as though over the past 3 years alone, we report — more often than in past years — spam and phishing attempts daily. Obviously it’s typically worse during the holiday season, but in general the amount of spam we receive has climbed significantly.
Can’t speak for the OP, but I’ve definitely seen a major recent increase in spam volume – in the past 3-4 months, or so. It used to be notable if the filters on my servers caught more than 100 messages in a single day – but lately, it’s often in the 300-400 range. Most of it’s pretty inept and easy to filter, E.g. those “your account has been hacked” bitcoin extortion spams, especially the ones that spoof the recipient’s EMail (to bolster the spammer’s claims that they have compromised the recipient’s accounts) – which, of course, fail SPF tests.
Spam from Indian SEO/web dev morons has been on the rise too, though they seem to cycle between different freemail providers – lately most of them seem to come from @aol.com addressess. Though for a while, I was seeing a surprising amount coming from what appeared to be paid G-Suite accounts (non-Google domains using Google’s servers as their MX, which so far as I know is not possible with free GMail accounts, but only paid G-Suite accounts).
The other thing I’ve noticed is a massive increase in the number of spamvertised URLs served by CloudFlare – along with weaselly “we’re not a hosting provider” excuses that CloudFlare hides behind as justification for knowingly providing service to spammers.
Google domains let you set forwarding rules to a gmail inbox and will probably look very similar to gsuite (I get the option to use either with my domain) so I would guess they are doing that, it’s a heck of a lot cheaper than going gsuite.
“The other thing I’ve noticed is a massive increase in the number of spamvertised URLs served by CloudFlare – along with weaselly “we’re not a hosting provider” excuses that CloudFlare hides behind as justification for knowingly providing service to spammers.”
These Content Distribution Networks like CloudFlare and Akamai are one day going to be held accountable. They could offer a simple API to the public which would allow us to see behind the veil that protects these criminal organizations but do they? No.
I promise you – their culpability will see justice one day.
Since the early days, Go Daddy has been more concerned with maximizing revenue than with security. I remember it used to do business with some pretty dodgy customers.
Regards,
I saw Long ago Photo on internet forum how russia Had Sexual intercourse with USA Russia was dominant side.
crooks penetrating Everything
crooks penetrate godaddy hole!
but life is about sex Everything is sex
Looks like we’re going to have to increase your Depo-Provera dosage. Again.
I run a free information hobby site that is pretty well known. I use one of the E-mail services offered by GoDaddy, my ISP for my website. I use the same E-address for most of my business. THAT has been a mistake. About once or twice a year, for some years of GoDaddy service, and this is simplified….someone on the same server (so I have been told) will start spamming and then the server is blocked by one or more of the many SPAM blocking servicers. I never know when some important E-mail from me is being blocked. It is annoying to try to find out, and, send another of the same E-mails, using a different account. Yes, the GoDaddy fix happens within a day or two. I never get a SMTP code back on these lost E-mails. I am on the verge of leaving GoDaddy forever, due to this one problem. Since I own the domain, this should be relatively easy…..and I may move everything from GoDaddy…I have two active domains with them.
its is called a blacklist and it doesnt just happen to GoDaddy domains…
I know that, but godaddy uses a server setup that causes all else to that server to go happily crazy, if there is a spammer on it, because the server is blocked, that means my domain too. OK, so this is simplified.
Robert, any shared hosting situation will give you the same results. If you want something different, you’ll have to pay significantly more.
Your issue is not a GoDaddy-specific problem; it’s a shared hosting problem.
Domain registrars will keep being a source of problems, as long as they automate much of what they do.
No one’s verifying customers or forms of payment, or checking for stolen information.
There’s no waiting periods, either, before implementing transactions for “customers.”
That’s why Namecheap and godaddy are synonymous with spam and ransom/malware.
And godaddy seems to be the registrar of every fake restaurant site I see.
Excellent report.
I work at a domain registrar (thankfully not GoDaddy), and while it is possible to register a domain name online with fraudulent info, we have a robust Fraud department in place that works 24/7 to track down and delete fraudulent registrations. Those guys don’t call into support for help so we can’t suss them out over the phone. As for domain transfers (ie, transferring registration to another registrant), we have another team that works hand-in-hand with our Legal department to make sure they are done legitimately (requires government issued photo ID for both parties).
Thank you for the information. It’s nice to read there exists a company doing things right.
From GoDaddy: “These domain names were parked until the threat actors activated them.”
This is an EXCEPTIONALLY revealing quote from Godaddy. All you have to do is to read between the lines.
It basically says two things:
First, that the NEW crop of domains that Spammy Bear is abusing now are NOT actually “new hijacks”. They are instead domains that Spammy Bear had already successfully hijacked some time ago, and that Spammy Bear is just bringing out of mothballs (and into production use) now.
Second, it says that GoDaddy hasn’t even actually yet managed to chase Spammy Bear completely out of its systems or off of its network. GoDaddy may or may not have actually fixed the underlying problem that allowed Spammy Bear to get in in the first place, but even that isn’t altogether clear.
Anyone who failed to read such a poorly-written form ostensibly from UPS and then actually clicked on the bait should have their login credentials revoked permanently, as the fractured syntax and misspelled wording is a clear giveaway that it was written by someone whose first language is NOT English. The first line of defense has to be the user brain of every recipient who gets such a piece of malware.
Ah, ye olde “if you were dumb enough to fall for this, you deserve it” chestnut.
You’re not helping.
And I’ve seen plenty of ostensibly intelligent people fall for this under the right circumstances, so aside from not helping, your premise is also deeply flawed.
A the end of the day, the defenses should lie at the recipients end because spammers will find a way… Even if domains are legit, they could still be a source of phishing emails or spam.
As for GoDaddy, they have been on the scammer end themselves. Stopped registering domains with them when I found out that they were selling domain name availability queries to squatters who would temporarily register the name to blackmail you if you did not register it right after you checked availability….
Brian, you should also take a look at Blue Host, i have been seeing this exact same thing with a lot of their domains being hijacked and then sub-domains being created all pointing to ASN(OVH) in France, this has been happening for months now and they all point to outdated cpanels/php.
I made a thread about it here mate.
https://www.bleepingcomputer.com/forums/t/686678/bluehost-has-been-hacked/
I contacted their support but got the same scripted excuses, they simply denied it was their fault.
From my standpoint, still seeing the vast majority of this activity (Sextortion, specifically) coming from domains outside the US. Central American domains (Argentina, Chile, Colombia, etc.) seem to be the favorites.
Other “hot” regions for this are Southeast Asia, and Eastern Europe.
A bit out of Russia and the Middle East as well.
Not saying this isn’t happening, but given how much I’ve seen of this kind of activity, I’m shocked I haven’t seem at least a few examples like the ones being described in this article.
I have seen Several FAKE Fed EX notifications alomost exactly like the UPS e-mail just hit today. Key NOTE: Several issues make with Caps and grammer make this one easy to spot. I think Go Daddy better check again.
Go daddy is allowing hackers to steal or hijack accounts and demand funds to get it back. I go from business to business as a software engineer and hear a about this alot. They say go to ICANN but they have all the facts right in front of them and do nothing. I’m working yet again at a company that had its site hijacked Godaddy turn against its customers so does ICANN. What a horrible company.