On Feb. 21, 2019, KrebsOnSecurity contacted Italian restaurant chain Buca di Beppo after discovering strong evidence that two million credit and debit card numbers belonging to the company’s customers were being sold in the cybercrime underground. Today, Buca’s parent firm announced it had remediated a 10-month breach of its payment systems at dozens of restaurants, including some locations of its other brands such as Earl of Sandwich and Planet Hollywood.
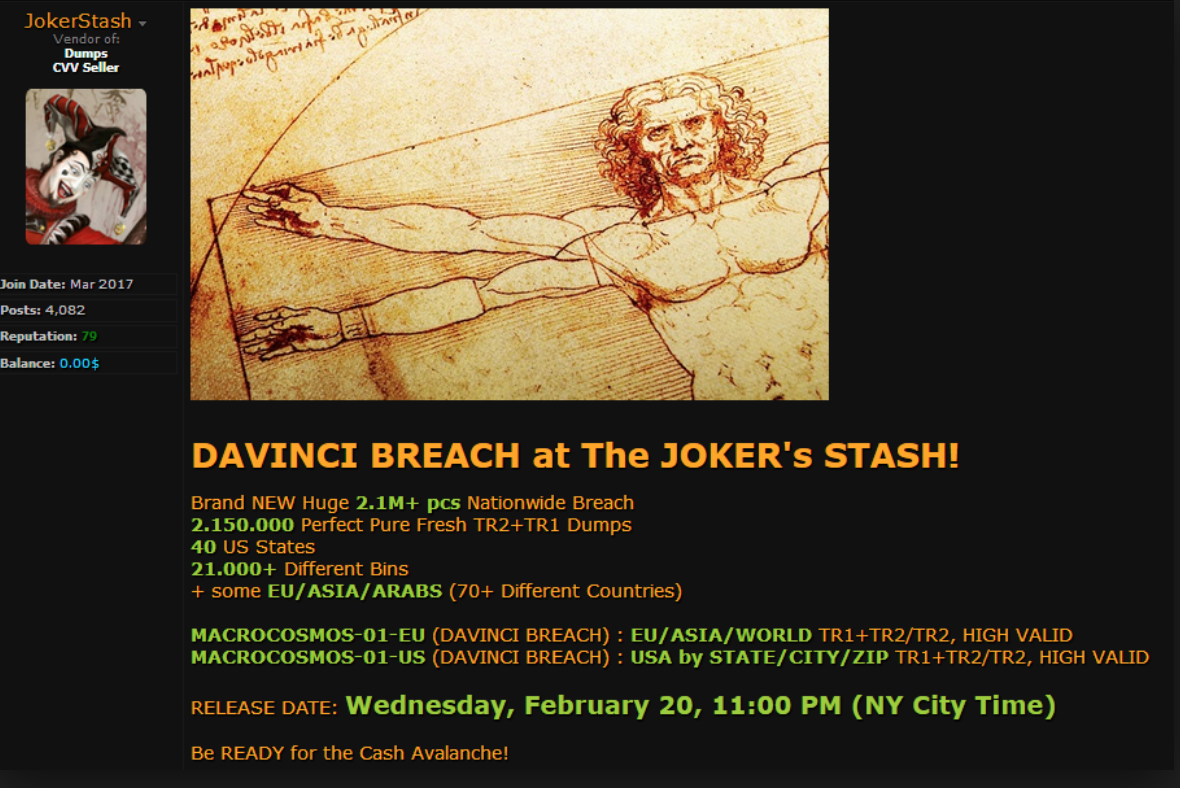
Some 2.1 million+ credit and debit card accounts stolen from dozens of Earl Enterprises restaurant locations went up for sale on a popular carding forum on Feb. 20, 2019.
In a statement posted to its Web site today, Orlando, Fla. based hospitality firm Earl Enterprises said a data breach involving malware installed on its point-of-sale systems allowed cyber thieves to steal card details from customers between May 23, 2018 and March 18, 2019.
Earl Enterprises did not respond to requests for specifics about how many customers total may have been impacted by the 10-month breach. The company’s statement directs concerned customers to an online tool that allows one to look up breached locations by city and state.
According to an analysis of that page, it appears the breach impacts virtually all 67 Buca di Beppo locations in the United States; a handful out of the total 31 Earl of Sandwich locations; and Planet Hollywood locations in Las Vegas, New York City and Orlando. Also impacted were Tequila Taqueria in Las Vegas; Chicken Guy! in Disney Springs, Fla.; and Mixology in Los Angeles.
KrebsOnsecurity contacted the executive team at Buca di Beppo in late February after determining most of this restaurant’s locations were likely involved a data breach that first surfaced on Joker’s Stash, an underground shop that sells huge new batches of freshly-stolen credit and debit cards on a regular basis.
Joker’s Stash typically organizes different batches of stolen cards around a codename tied to a specific merchant breach. This naming convention allows criminals who purchased cards from a specific batch and found success using those cards fraudulently to buy from the same batch again when future cards stolen from the same breached merchant are posted for sale.
While a given batch’s nickname usually has little relation to the breached merchant, Joker’s Stash does offer a number of search options for customers that can sometimes be used to trace a large batch of stolen cards back to a specific merchant.
This is especially true if the victim merchant has a number of store locations in multiple smaller U.S. towns. That’s because while Joker’s Stash makes its stolen cards searchable via a variety of qualities — the card-issuing bank or expiration date, for example — perhaps the most useful in this case is the city or ZIP code tied to each card.
As with a number of other carding sites, Joker’s Stash indexes cards by the city and/or ZIP code of the store from which the card was stolen (not the ZIP code of the affected cardholders).
On Feb. 20, Joker’s Stash moved a new batch of some 2.15 million stolen cards that it dubbed the “Davinci Breach.” An analysis of the cities and towns listed among the Davinci cards for sale included a number of hacked store locations that were not in major cities, such as Burnsville, Minn., Livonia, Mich., Midvale, Utah, Norwood, Ohio, and Wheeling, Ill.
Earl Enterprises said in its statement the malicious software installed at affected stores captured payment card data, which could have included credit and debit card numbers, expiration dates and, in some cases, cardholder names. The company says online orders were not affected.
Malicious hackers typically steal card data from organizations by hacking into point-of-sale systems remotely and seeding those systems with malicious software that can copy account data stored on a card’s magnetic stripe. Thieves can use that data to clone the cards and then use the counterfeits to buy high-priced merchandise from electronics stores and big box retailers.
Cardholders are not responsible for fraudulent charges, but your bank isn’t always going to detect card fraud. That’s why it’s important to regularly review your monthly statements and quickly report any unauthorized charges.




Are these restaurant chains moving to tokenized processing of bankcards? We’ve been doing that for over a year now, no unencrypted card numbers are ever on our system or exposed.
But the restaurant industry is slow to adopt new security measures, so they are likely still using swipe readers at the hacked locations.
There are some that have upgraded to support the chip. (AFAIK, Buca di Beppo has not.) However, pay at the table in the US is still extremely rare outside of the largest chains and likely will continue to be for some time to come.
Anyway, I’m feeling that the EMV liability shift wasn’t nearly as strong of a motivator as the card networks thought it’d be. Perhaps this is a case where regulation at the government level would have been helpful.
The level of regulation in the US is commensurate to the affordability of the system to merchants. It is actually amazing Chip-N-Pin is reaching the adoption levels it has in America.
Another great article , the credit card breach news always starts here first !
They refuse to update their card readers, they also need to have card processors on each table that only accept chip transactions. I really hate when the waitstaff disappears with my card for 20 minutes as well. Isn’t it time they got ahead of the game. As for Buco, their food isn’t very good and their restaurants have poor acoustics>
I also hate when a restaurant does that(I’ve never been to any of the places listed here)!!
I need to make a better effort at bringing cash to a place I know does that.
BTW, can anyone tell me why some places swipe my card & then insert to use the chip? Doesn’t seem secure to me.
Chip and signature + tip adjust continuing to be allowed makes pay at the table hard to justify for restaurants. Not to mention that there are apparently a significant number of customers who are not fans of pay at the table, so implementing it when few other places are will likely alienate them. (In my experience, outside of the large major chains like Chili’s and Applebee’s, pay at the table in the US is extremely rare.)
Of course, this assumes a restaurant upgraded to support the chip at all. A fair number are still swiping.
“apparently a significant number of customers who are not fans of pay at the table”
What reason would people not be fans of keeping possession of their credit card instead of having it walked around a restaurant?
Likely in large part due to tipping. Right now it’s done with the server away from the table, so they don’t see the amount until after the guests have left. With a portable payment terminal, the server is standing there while the guests enter the amount. I can see how that’d be awkward if it’s not something done at every restaurant.
fwiw, restaurants whose staff leave payment machines w/ customers and then walk away are just asking to be hacked in various ways. I haven’t looked into it in detail, but I expect that someone will have a way to tamper with the machines… The machines can generally trigger credits/refunds in addition to making charges (I’m not sure if they require extra codes for approval, but a key-pad-logger can be installed, if the staff is away…).
I can understand the hesitancy wrt revealing the tip amount, but it’s a pretty silly thing–the wait staff will know the amount and will probably remember you long enough to be able to associate the amount with you.
This article clearly stated that the point of sale computer system was hacked, remotely.
This article has nothing to do with waitstaff skimming cards or card readers.
Did you even read it?
Are you sure?
“Malicious hackers typically steal card data from organizations by hacking into point-of-sale systems remotely and seeding those systems with malicious software that can copy account data stored on a card’s magnetic stripe.”
The above describes how the hack usually works. As former IT for a restaurant chain I can assure you there are often many opportunities to surreptitiously connect a USB to a point-of-sale terminal to install malicious software.
Yes, quite sure. It’s a systemic matter, not the fault of the staff in a restaurant location.
Hey, where’s the obligatory “we take our customers security very seriously” BS? Also how about offering a (useless) free credit monitoring service? I guess they don’t do it in Italy, hah?
From the Buca di Beppo Web site:
“We remain committed to safeguarding the security of our guests’ information and deeply regret that this incident occurred.”
So there’s the BS you were looking for, Dennis.
BS indeed!
The only actions they suggest on their website are things that YOU, the customer, should do. Nothing at all on their part. And certainly not even the hint of offering any credit monitoring protection (however useless that may be).
They “deeply regret” this incident — no doubt because of the inconvenience to them, not us.
A shabby response. Definitely not the kind of company I’ll patronize.
Can anyone explain why restaurant establishments (and possibly other similar random-transactional-businesses) would have any need to store mag stripe info for more than, say, 24 hours? I expect that the back end payment processors issue a transaction number for every payment made by the front side vendor for tracking purposes. It seems that if B.d.B. and others would simply not retain the sensitive data unnecessarily it would reduce risk in large amounts.
This breach, like many others before it, was caused by malware on the point-of-sale devices that captures the card data as the customer’s card is being physically swiped at the register — not when the data is somehow stored in the retailer’s systems.
That makes much more sense. There shouldn’t be any reason for a merchant of that kind to store cc data like that. Great article!
Time for customers to vote with their feet and refuse to patronize these establishments who allow such breaches to occur for an extended period of time, and then refuse to talk to the press about its occurrence. It’s not like there is a shortage of Italian restaurants or sandwich shops. As for Planet Hollywood, well….
By that logic, you should skip any restaurant that hasn’t been breached because it may be breached in the future. Or, better yet, maybe you should just stop using credit cards.
I, for one, essentially HAVE stopped using my credit cards, except in the few mega retailers who, if they get breached, then virtually EVERYONE in America will be having a bad hair day right along with me. Only those mega companies seem to actually take any of this “security” stuff seriously. I haven’t used any of my cards at any *restaurant* in literally years, and I won’t, because of stuff like this. The card companies have gone to great lengths to get everyone addicted to using plastic, but doing so is unambiguously dangerous. Cash is your friend. Flip that middle finger at the card companies. They deserve it because they don’t do s**t except collect fees… which they do, even on fraudulent transactions.
I actually take the opposite approach, I use my credit cards frequently, make sure to reconcile the accounts on a monthly basis (which should alert me to fraudulent transactions), and otherwise don’t worry about it. It’s not MY money that’s at risk. Having to update accounts set to charge against a particular card would be annoying if a given card was compromised and had to be re-issued, but I consider it a reasonable trade-off for the convenience of using a credit card.
I do make sure to use a real credit card, and not one of the those annoying hybrid Debit/ATM cards that suck money directly out of your bank account.
Always been corruption dealing with Esau if no the bible I’m not against it because it’s every company you go in spend money on ,comma since ,add up the dollars because the cents don’t make sense so you have a company or franchises dubbling up der money . The Italian way .
What really sicks is when Bucca sends you emails for special offers they only accept your credit or debit card not cash to redeem offer. So what’s that all about””” something’s fishy
WAIT! WAIT! WAIT! Wait just an effing minute here! Brian, your time line is NOT making things clear. Please elaborate. You write that you contacted the company and informed them of the issue on Feb. 21, 2019, and yet the company CONTINUED to have card numbers stolen from it right up to and through March 18, 2019?? Am I reading that right?
Brian, please do clarify. And it is really totally OK to blow your own horn here, under the circumstances. Are you, to the best of your knowledge, both the first and also the ONLY party to have informed this company about the breach? And why did it take them nearly a full month to take this matter seriously and to actually lock things down?? This is just NUTS and shows an abject and callous disregard for the safety of the company’s customers. This is really inexcusable. May the lawsuits begin!
Ron, watch the potty mouth and calm down.
So you contacted them on 02/21 but you are reporting it on 03/29.
Did you agree to wait for a good reason?
Burnsville is a Minneapolis suburb; for all practical purposes it is Minneapolis.
In the same vein, Norwood is a suburb of Cincinnati, Ohio.
Nothing will change until merchants who leak our credit card data are penalized significantly.
The tech to avoid these problems is available. The only reason merchants are not using it is that the money they save by not upgrading is literally worth more than the risk they take in not upgrading (because there really isn’t any risk right now). Risk = Severity($) x Probability of occurring x Exposure to the risk. To put it another way: convert risk to dollars, then follow the money. If that points to not investing in proper security, there will be no meaningful security.
Regrets and yet another credit monitoring subscription do not help. Only when merchants are obligated to observe good security practices via threat of major financial pain will they do so. Flip the equation so it is NOT worth the risk of operating with vulnerable payment processing systems and practices. Only then will we see improvement.
They should be made to eat their own food!
For some reason the Coffee Bean and Tea Leaf joints in our locality have cards inserted in the chip card slot that say “Swipe” with an arrow pointing towards the card swipe slot. The manager said they had problems with the Verifone terminals so they were just using the mag stripe. Sigh.
Not unusual.
I was in a chain sandwich shop Saturday. Their chip readers were all broken.
The owner was working that night.
She said corporate forced them to buy that particular system… and corporate doesn’t want to hear about they’re broken.
Franchisees are responsible for paying to have them fixed.
What forum was this on?
ROB: Discussing the most well arranged podcast, though I think we perform good job of masking that.
The Romans only had VHF and three black and white channels
— all in Latina. The records I’ve heard so far are unimaginable. http://myy.me/skyalpinequeenstowncasino515726
Krebs why you making free marketing for this guys??? Shud take them down with police not making free marketing and revenue for them!!!
Unlogical
Great site you have here but I was curious about if you knew of any discussion boards that
cover the same topics discussed in this article?
I’d really like to be a part of group where I can get suggestions from other knowledgeable individuals that
share the same interest. If you have any recommendations, please let me know.
Appreciate it!
Explains why their affiliate program on Rakuten abruptly shut down earlier this year.
Has there been any reporting on what POS stack Earl of sandwich uses, or specifically at those locations?
The PCI council and congress need to get their act together and start making examples out of these offenders. With fines and incentives. At the very least more public shaming is needed.