You may have heard that today’s phone fraudsters like to use caller ID spoofing services to make their scam calls seem more believable. But you probably didn’t know that these fraudsters also can use caller ID spoofing to trick your bank into giving up information about recent transactions on your account — data that can then be abused to make their phone scams more believable and expose you to additional forms of identity theft.
Last week, KrebsOnSecurity told the harrowing tale of a reader (a security expert, no less) who tried to turn the tables on his telephonic tormentors and failed spectacularly. In that episode, the people impersonating his bank not only spoofed the bank’s real phone number, but they were also pretending to be him on a separate call at the same time with his bank.
This foiled his efforts to make sure it was really his bank that called him, because he called his bank with another phone and the bank confirmed they currently were in a separate call with him discussing fraud on his account (however, the other call was the fraudster pretending to be him).
Shortly after that story ran, I heard from another reader — we’ll call him “Jim” since he didn’t want his real name used for this story — whose wife was the target of a similar scam, albeit with an important twist: The scammers were armed with information about a number of her recent financial transactions, which he claims they got from the bank’s own automated phone system just by spoofing her phone number.
“When they originally called my wife, there were no fraudulent transactions on her account, but they were able to specify the last three transactions she had made, which combined with the caller-ID had mistakenly earned her trust,” Jim explained. “After we figured out what was going on, we were left asking ourselves how the crooks had obtained her last three transactions without breaking into her account online. As it turned out, calling the phone number on the back of the credit card from the phone number linked with the card provided the most recent transactions without providing any form of authentication.”
Jim said he was so aghast at this realization that he called the same number from his phone and tried accessing his account, which is also at Citi but wholly separate from his spouse’s. Sure enough, he said, as long as he was calling from the number on file for his account, the automated system let him review recent transactions without any further authentication.
“I confirmed on my separate Citi card that they often (but not quite always) were providing the transaction details,” Jim said. “I was appalled that Citi would do that. So, it seemed the crooks would spoof caller ID when calling Citibank, as well as when calling the target/victim.”
The incident Jim described happened in late January 2020, and Citi may have changed its procedures since then. But in a phone interview with KrebsOnSecurity earlier this week, Jim made a call to Citi’s automated system from his mobile phone on file with the bank, and I could hear Citi’s systems asking him to enter the last four digits of his credit card number before he could review recent transactions.
The request for the last four of the customer’s credit card number was consistent with my own testing, which relied on a caller ID spoofing service advertised in the cybercrime underground and aimed at a Citi account controlled by this author.
In one test, the spoofed call let KrebsOnSecurity hear recent transaction data — where and when the transaction was made, and how much was spent — after providing the automated system the last four digits of the account’s credit card number. In another test, the automated system asked for the account holder’s full Social Security number.
Citi declined to discuss specific actions it takes to detect and prevent fraud. But in a written statement provided to this author it said the company continuously monitors and analyzes threats and looks for opportunities to strengthen its controls.
“We see regular attempts by fraudsters to gain access to information and we are constantly monitoring for emerging threats and taking preventive action for our clients’ protection,” the statement reads. “For inbound calls to call centers, we continue to adapt and implement detection capabilities to identify suspicious or spoofed phone numbers. We also encourage clients to install and use our mobile app and sign up for push notifications and alerts in the mobile app.”
PREGNANT PAUSES AND BULGING EMAIL BOMBS
Jim said the fraudster who called his wife clearly already knew her mailing and email addresses, her mobile number and the fact that her card was an American Airlines-branded Citi card. The caller said there had been a series of suspicious transactions, and proceeded to read back details of several recent transactions to verify if those were purchases she’d authorized.
A list of services offered by one of several underground stores that sell caller ID spoofing and email bombing services.
Jim’s wife quickly logged on to her Citi account and saw that the amounts, dates and places of the transactions referenced by the caller indeed corresponded to recent legitimate transactions. But she didn’t see any signs of unauthorized charges.
After verifying the recent legitimate transactions with the caller, the person on the phone asked for her security word. When she provided it, there was a long hold before the caller came back and said she’d provided the wrong answer.
When she corrected herself and provided a different security word, there was another long pause before the caller said the second answer she provided was correct. At that point, the caller said Citi would be sending her a new card and that it had prevented several phony charges from even posting to her account.
She didn’t understand until later that the pauses were points at which the fraudsters had to put her on hold to relay her answers in their own call posing as her to Citi’s customer service department.
Not long after Jim’s spouse hung up with the caller, her inbox quickly began filling up with hundreds of automated messages from various websites trying to confirm an email newsletter subscription she’d supposedly requested.
As the recipient of several of these “email bombing” attacks, I can verify that crooks often will use services offered in the cybercrime underground to flood a target’s inbox with these junk newsletter subscriptions shortly after committing fraud in the target’s name when they wish to bury an email notification from a target’s bank.
‘OVERPAYMENT REIMBURSEMENT’
In the case of Jim’s wife, the inbox flood backfired, and only made her more suspicious about the true nature of the recent phone call. So she called the number on the back of her Citi card and was told that she had indeed just called Citi and requested what’s known as an “overpayment reimbursement.” The couple have long had their credit cards on auto-payment, and the most recent payment was especially high — nearly $4,000 — thanks to a flurry of Christmas present purchases for friends and family.
In an overpayment reimbursement, a customer can request that the bank refund any amount paid toward a previous bill that exceeds the minimum required monthly payment. Doing so causes any back-due interest on that unpaid amount to accrue to the account as well.
In this case, the caller posing as Jim’s wife requested an overpayment reimbursement to the tune of just under $4,000. It’s not clear how or where the fraudsters intended this payment to be sent, but for whatever reason Citi ended up saying they would cut a physical check and mail it to the address on file. Probably not what the fraudsters wanted, although since then Jim and his wife say they have been on alert for anyone suspicious lurking near their mailbox.
“The person we spoke with at Citi’s fraud department kept insisting that yes, it was my wife that called because the call came from her mobile number,” Jim said. “The Citi employee was alarmed because she didn’t understand the whole notion of caller ID spoofing. And we both found it kind of disturbing that someone in fraud at such a major bank didn’t even understand that such a thing was possible.”
SHOPPING FOR ‘CVVs’
Fraud experts say the scammers behind the types of calls that targeted Jim’s family are most likely fueled by the rampant sale of credit card records stolen from hacked online merchants. This data, known as “CVVs” in the cybercrime underground, is sold in packages for about $15 to $20 per record, and very often includes the customer’s name, address, phone number, email address and full credit or debit card number, expiration date, and card verification value (CVV) printed on the back of the card.
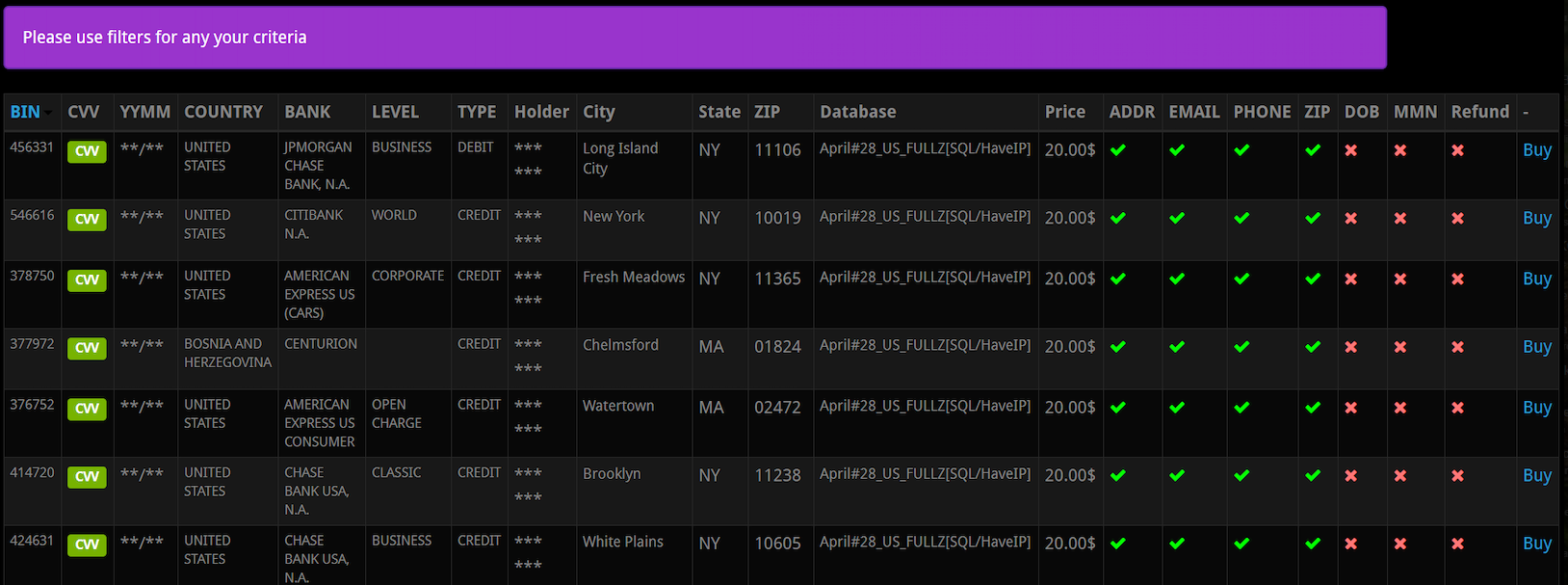
A screen shot from an underground store selling CVV records. Note that all of these records come with the cardholder’s address, email, phone number and zip code. Click to enlarge. Image: Gemini Advisory.
Dozens of cybercrime shops traffic in this stolen data, which is more traditionally used to defraud online merchants. But such records are ideally suited for criminals engaged in the type of phone scams that are the subject of this article.
That’s according to Andrei Barysevich, CEO and co-founder of Gemini Advisory, a New York-based company that monitors dozens of underground shops selling stolen card data.
“If the fraudsters already have the target’s cell phone number, in many cases they already have the target’s credit card information as well,” Barysevich said.
Gemini estimates there are currently some 13 million CVV records for sale across the dark web, and that more than 40 percent of these records put up for sale over the past year included the cardholder’s phone number.
Data from recent financial transactions can not only help fraudsters better impersonate your bank, it can also be useful in linking a customer’s account to another account the fraudsters control. That’s because PayPal and a number of other pure-play online financial institutions allow customers to link accounts by verifying the value of microdeposits.
For example, if you wish to be able to transfer funds between PayPal and a bank account, the company will first send a couple of tiny deposits — a few cents, usually — to the account you wish to link. Only after verifying those exact amounts will the account-linking request be granted.
JUST HANG UP
Both this and last week’s story illustrate why the only sane response to a call purporting to be from your bank is to hang up, look up your bank’s customer service number from their Web site or from the back of your card, and call them back yourself.
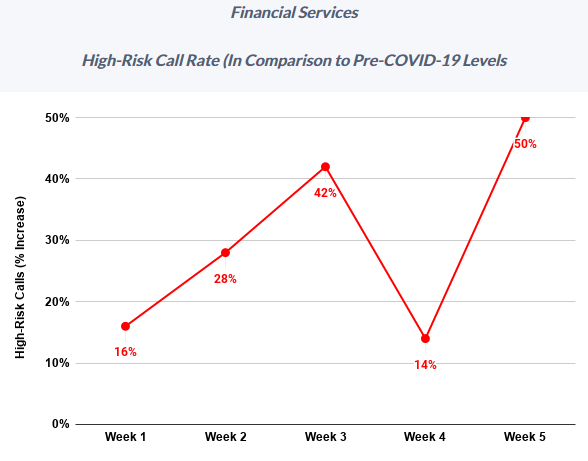
Meanwhile, fraudsters who hack peoples’ finances with nothing more than a telephone have been significantly upping the volume of attacks in recent months, new research suggests. Fraud prevention company Next Caller said this week it has tracked “massive increases in call volumes and high-risk calls across Fortune 500 companies as a result of COVID-19.”
“After a brief reprieve in Week 4 (April 6-12), Week 5 (April 13-19) saw call volume across Next Caller’s clients in the telecom and financial services sectors spike 40% above previous highs,” the company found. “Particularly worrisome is the activity taking place in the financial services sector, where call traffic topped previous highs by 800%.”
Next Caller said it’s likely some of that increase was due to numerous online and mobile app outages for many major financial institutions at a time when more than 80 million Americans were simultaneously trying to track the status of their stimulus deposits. But it said that surge also brought with it an influx of fraudsters looking to capitalize on all the chaos.
“High-risk calls to financial services surged to 50% above pre-COVID levels, with one Fortune 100 bank suffering a high-risk increase of 60% during Week 5,” the company wrote in a recent report.




I have my main number on a Contacts List. If a caller ID is on the list, my phone rings. If not, the call goes straight to voicemail and does not ring. Its the best way to deal with scammers and robo callers.
Same here. It’s taken a while, but my scam call volume has dropped dramatically.
Recently a fraudster attempted to scam me by spoofing my CCs customer service number (the one on the back of my card). Since I have that number in my contact list, it showed up on my caller ID and got through my “Do Not Disturb” setting.
The fraudster claimed to be from my CC fraud department and began putting me through the paces. It nearly worked to fool me into giving them access to my card, but several things in the conversation didn’t feel quite right, so I hung up and called my CC company directly.
Have recently received an email from my CC company with several suggestions as to how to avoid being defrauded. One of them was “Never Believe Caller ID”.
I agree with the writer: Hang up and initiate the call to your CC company yourself.
I can call you from whatever number I want (it’s called spoofing the caller ID). Let me know the number to call and the number you want the call to be from and I’ll do it.
Red Hot, I am sorry for having to ask such a doofus question, but I have no idea what you are trying to convey: When you say, “My main number (you mean your bank or credit card company number?) is on a Contact list (you mean these numbers of cc company and bank are on contact List on your cell phone?
Sorry, I have not been keeping up with techie/scam/phishing stuff at all.
What he means the number he use to have people call him. The phone he uses has a screening process that you must input certain people you know on the contact list. It goes one of three ways:
1. When the caller on the contact list calls you, they can get through and the phone will ring.
2. When the phone number that is not on the list calls, caller will not go through and the phone won’t ring.- This is for the robocaller.
3. Sometimes you have certain calls you are expecting, the phone will force the caller to input a special key to get through.
I have switched my parent’s phone with this phone and the calls from such spoofing has stopped the ringing down to occasionally made things much tolerable. I just have to delete the calls that were made.
For the record, a bank will never call you to ask for information.
How do you put names on a “Contact List”? Is this a feaure of the phone?
It’s kind of hard to believe that there is no technology available to shut down these spoofers. And if there is, why hasn’t it been implemented to PREVENT a call from being completed if the caller ID is not correct?
The problem is that it’s always been a cat and mouse game,and it will always be. You block one loophole,they find another.
Make a better mousetrap, and they make a better mouse. Make something foolproof, and they make a better fool….
The calls are made via computer and they have the ability to channel their own number with others who may have no idea it is being used. Don’t be surprise if you have a person calling you to stop calling them when you did not call them in the first place.
This has to do with the design of the POTS switching system from many decades ago which never even conceived of of VOIP based services.
There is an emerging technology by which telcos will be able to digitally sign and attest caller ID info (it’s called SHKEN/STIR). However, it’s pretty new and still being implemented with a lot of delays and pushback mainly from smaller landline telcos for whom it is expensive and difficult to implement this technology in their existing systems.
It’s obvious that the security model of traditional phone calls is broken, just like that of email.
But what makes this worse is the fact that much fewer people are aware of this type of spoofing compared to email spoofing. As we can see from the article:
“The person we spoke with at Citi’s fraud department kept insisting that yes, it was my wife that called because the call came from her mobile number,” Jim said. “The Citi employee was alarmed because she didn’t understand the whole notion of caller ID spoofing. And we both found it kind of disturbing that someone in fraud at such a major bank didn’t even understand that such a thing was possible.”
Finding accurate information about this issue is difficult, and I also wonder why phone companies don’t do anything about it. It seems to me that it’s not possible to completely eliminate caller ID spoofing.
Why is a bank relying on in-band Caller ID signalling? That’s like relying on the “From:” address in an email
They should be using out-of-band Automatic Number Identification if they want to rely on phone numbers; it’s more expensive since it’s not part of normal service, but it’s way more difficult to spoof.
You answered your own question : “… it’s more expensive …”. Only when the cost of dealing with spoofed phone numbers is more expensive than making use of out-of-band Automatic Number Identification will they start using the latter. It literally is less expensive to allow the problem to persist, and businesses make decisions on one criterion alone : profit.
They don’t actually care about what is right for the customer. They only care about maximizing profit, therefore allowing a calculated amount of fraud to occur, weighed against the cost (in training, implementation, loss of business, etc.) of combatting it.
While the technology employed is new-ish, the scam isn’t.
This type of scam started in the mid 1990s, and was more successful then at fraud than it is now, and much easier to avoid today.
For whatever reason, scammers would get hold of relevant info, such as phone numbers and addresses (the phone book – an ancient device – too complicated to explain here). They’d cold-call people, usually in upper middle class neighborhoods (maps and phone books…) and trick unsuspecting victims into revealing their bank name.
That’s all they needed.
The rest is the same; calling the bank while speaking to the victim and snowballing the scam into an illegitimate payday for the fraudsters.
Back then you could simply tell the bank your telephone number (no need for caller ID spoofing) AND where to mail the check, and your bank would comply.
ALWAYS CALL YOUR BANK BACK! And if you didn’t “just call” them, insist that they understand that!
And another good one, just for old time sake – NEVER click on links in emails!
One of the red flags here for me was “Citi.”
I deal with several credit card companies, and Citi has been hands-down the worst in regards to security practices. Disclosing recent activity based on a phone number is a really good example.
That, the fact that they have had multiple documented breaches, and a stunning lack of competence by their phone reps have led me to the conclusion that it’s not safe to do business with them.
There are plenty of other, more competent banks out there.
Some of us cannot have the main number on a contact list. I have a teenage granddaughter who regularly loses and breaks her phone. She then calls for rescue from whatever phone is handy. I have received 75 spam calls and 35 texts since the end of February. Even the one call I answered was obviously not right because they thought my name was Ray. I do not respond, but report and block and they still keep coming. Maybe I’d be in trouble if my name really was Roy. Instead, it’s just really annoying. Take nothing at face value. Check everything and use some logic. Always ask for a before number so you can call them back and verify first before giving out any info.
My bank never calls me directly, nor should anyone else’s. If someone calls you and says they’re from the bank, just start praising Jay-zus and the power and the glory until they go away (or convert!)
You can make it more fun than that by just repeating every question they ask (but obviously never answering a single one). If you have kids, you’ll remember this infuriating game they love to play. Scammers don’t like it much either…
I wonder how much spoofing material is collected for the “Leave a Comment” tools just like this one
The FTC is the Federal agency tasked with fighting Internet and telephone fraud. Why the ‘L isn’t it more active in that activity? If it needs more funding, let’s demand our Senators and Reps provide significantly more funding.
I have two agencies calling me all the time. 1) AUTO Warranty company that wants to extend my warranty of my 5 year old car. 2) Home warranty company who want to sell me warrantee on my newly built home.
I wish there was a way to shake them off or there was a way to identify and report these two sick companies.
It’s a lot more than two entities calling…..
For the auto warranty, if I have time to play, I ask “which one?” or sometimes I say it is a Hupmobile.
Finding the last 4 digits on a credit/debit card is easy. Thats what merchants print on the transaction receipt.
Yep. It’s also exposed by countless e-commerce Web sites, where you change one number in an order record and boom you’re looking at someone else’s order info, including their name, address, phone number (usually mobile) and last four of their credit card number. I could do one post a week about major companies that are exposing this information in this exact way and still not run out of material for a year or more.
But I bet you didn’t know this: Ten years ago a crack commando unit was sent to prison by a military court for a crime they didn’t commit. These men promptly escaped from a maximum-security stockade to the Los Angeles underground. Today, still wanted by the government, they survive as soldiers of fortune. If you have a problem… if no one else can help… and if you can find them… maybe you can hire… The A-Team.
In Florida (and probably other states) in order to vote, the Division of Elections makes the following information public: “Once filed, with few exceptions, all voter registration information is public record including your name, address, date of birth, party affiliation, phone number and email address.”
Then there are companies that publish that information so it is easily accessible with Google or other search engines.
Beware of the PG&E Utility phone scam. You get a call from a phone number which appears to be PG&E. A recording informs you your power is about to cut off in 4 hours because of non payment on your bill. Voice tells you to call back this xxx-xxx-xxxx number to pay your bill to keep your power from being turned off.
Don’t fall for the scam. I contacted PG&E after getting one of these calls. PG&E is aware of the phone scam…but that’s about it…they can’t do much about scammers spoofing their phone number. You’d think PG&E would send out notices warning their customers.
Not to give away too much, in case the scammers aren’t aware, but some professional licensing agencies require contact information, including phone numbers and address be made public.
I second the complaints about Citi – we have had numerous hacks of their cards over the years, and in the last 2 years, it has increased. As a result I check their online site at least once a day for fraudulent charges and no longer store the card info at any online e-commerce sites.
Many years ago (when Krebs was still at the WaPo) a scammer with my info called my bank and all my cc companies seeking emergency cash because I was supposedly on vacation in Mexico. He did this on a Sunday evening, and on Monday morning I noticed a $1000 withdrawal from my checking acct! None of my account companies called me, until American Express got hit – they had him on the line while they were talking to me! Krebs reported the hack because they also got Justice Breyer of the Supreme Court, omg!
My credit monitoring service had not noticed anything or alerted me, btw. It was a big hassle – getting a police report was the biggest hurdle because the local police were so overwhelmed with cases. Had to call my local politician to get the police to even call me back. The credit bureaus were also a royal pain in the you know where. They acted as if it was THEIR information, not mine! I got so fed up, when I finally got them to do something, I put a freeze on them. I was really po’d at my bank, and changed to a different one.
The hacker had used my info to apply for a mortgage which they did by hacking Country Wide, then they ran a credit report which listed all my account info, and proceeded to call each on with the sob story.
They also tried to get an IRS refund and I had to go through a lot of rigamarole to straighten that out. This was the early days of scamming the IRS and the IRS was playing catch-up.
We all have to assume all our information is out there for sale, DOB, SSN, Addr, etc., and pay close attention to our accts. I do not even pick up the phone to numbers I do not recognize. And my voice mail message does not identify anything about us. Also, got an unlisted number, well worth the extra 50 cents a month, imho. Good luck folks!