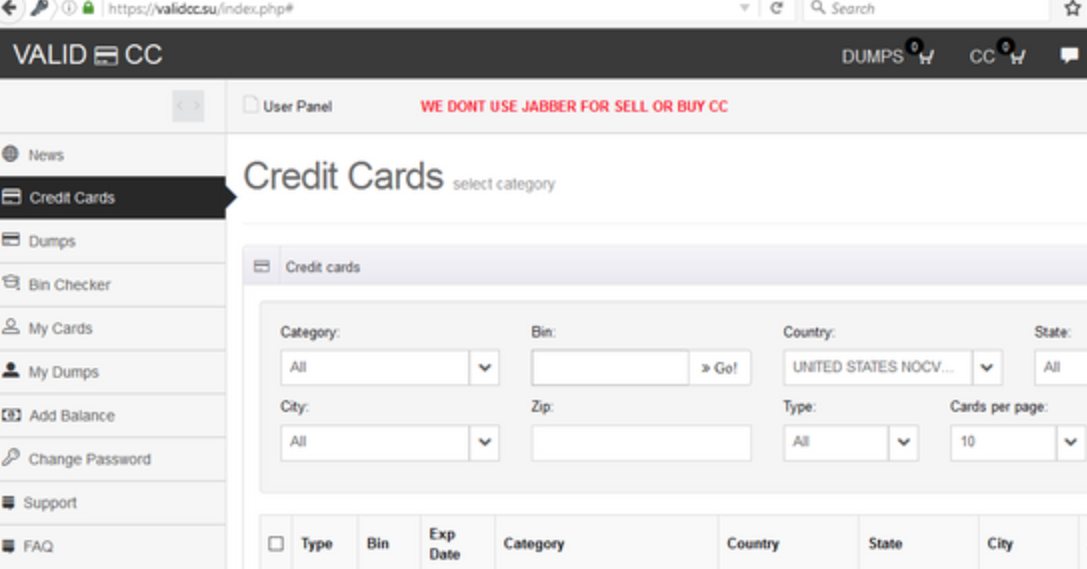
Russian Govt. Continues Carding Shop Crackdown
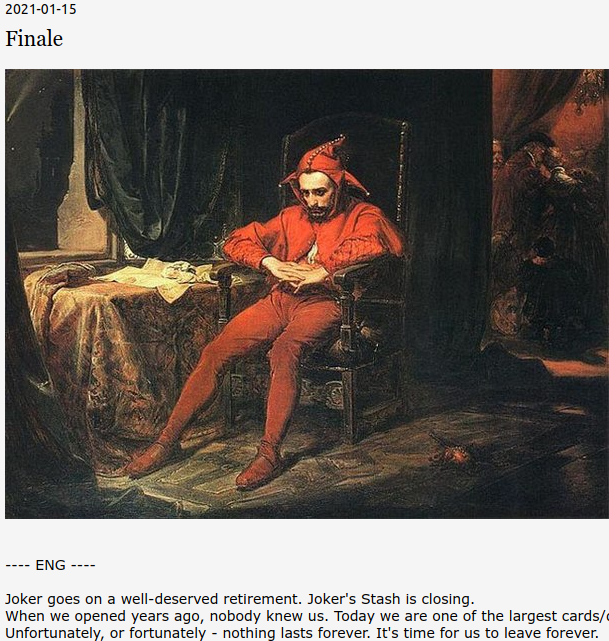
Russian authorities have arrested six men accused of operating some of the most active online bazaars for selling stolen payment card data. The crackdown — the second closure of major card fraud shops by Russian authorities in as many weeks — comes closely behind Russia’s arrest of 14 alleged affiliates of the REvil ransomware gang, and has many in the cybercrime underground asking who might be next.