In May 2019, KrebsOnSecurity broke the news that the website of mortgage title insurance giant First American Financial Corp. had exposed approximately 885 million records related to mortgage deals going back to 2003. On Wednesday, regulators in New York announced that First American was the target of their first ever cybersecurity enforcement action in connection with the incident, charges that could bring steep financial penalties.

First American Financial Corp.
Santa Ana, Calif.-based First American [NYSE:FAF] is a leading provider of title insurance and settlement services to the real estate and mortgage industries. It employs some 18,000 people and brought in $6.2 billion in 2019.
As first reported here last year, First American’s website exposed 16 years worth of digitized mortgage title insurance records — including bank account numbers and statements, mortgage and tax records, Social Security numbers, wire transaction receipts, and drivers license images.
The documents were available without authentication to anyone with a Web browser.
According to a filing (PDF) by the New York State Department of Financial Services (DFS), the weakness that exposed the documents was first introduced during an application software update in May 2014 and went undetected for years.
Worse still, the DFS found, the vulnerability was discovered in a penetration test First American conducted on its own in December 2018.
“Remarkably, Respondent instead allowed unfettered access to the personal and financial data of millions of its customers for six more months until the breach and its serious ramifications were widely publicized by a nationally recognized cybersecurity industry journalist,” the DFS explained in a statement on the charges.
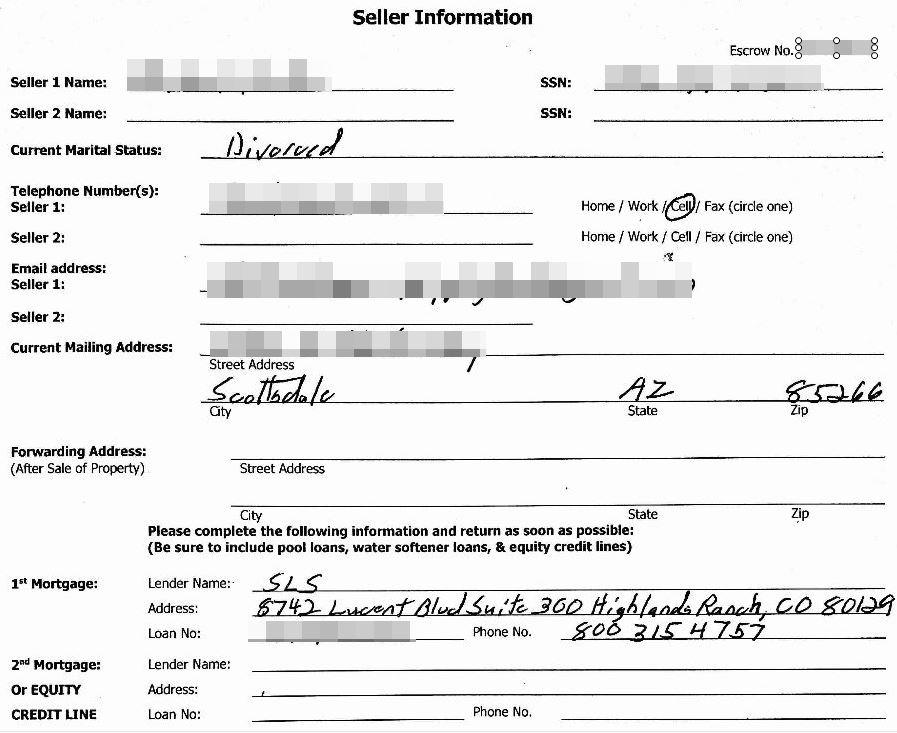
A redacted screenshot of one of many millions of sensitive records exposed by First American’s Web site.
Reuters reports that the penalties could be significant for First American: The DFS considers each instance of exposed personal information a separate violation, and the company faces penalties of up to $1,000 per violation.
In a written statement, First American said it strongly disagrees with the DFS’s findings, and that its own investigation determined only a “very limited number” of consumers — and none from New York — had personal data accessed without permission.
In August 2019, the company said a third-party investigation into the exposure identified just 32 consumers whose non-public personal information likely was accessed without authorization.
When KrebsOnSecurity asked last year how long it maintained access logs or how far back in time that review went, First American declined to be more specific, saying only that its logs covered a period that was typical for a company of its size and nature.
But in Wednesday’s filing, the DFS said First American was unable to determine whether records were accessed prior to Jun 2018.
“Respondent’s forensic investigation relied on a review of web logs retained from June 2018 onward,” the DFS found. “Respondent’s own analysis demonstrated that during this 11-month period, more than 350,000 documents were accessed without authorization by automated ‘bots’ or ‘scraper’ programs designed to collect information on the Internet.
The records exposed by First American would have been a virtual gold mine for phishers and scammers involved in so-called Business Email Compromise (BEC) scams, which often impersonate real estate agents, closing agencies, title and escrow firms in a bid to trick property buyers into wiring funds to fraudsters. According to the FBI, BEC scams are the most costly form of cybercrime today.
First American’s stock price fell more than 6 percent the day after news of their data leak was published here. In the days that followed, the DFS and U.S. Securities and Exchange Commission each announced they were investigating the company.
First American released its first quarter 2020 earnings today. A hearing on the charges alleged by the DFS is slated for Oct. 26.




What is the view of their cybersecurity insurance firm?
#Cancelled.
If they have cyber insurance – it seems likely payout isn’t going to occur. Standard language is that known weaknesses must be addressed – and a pen test showing the vuln absolutely classifies it as known.
But ultimately the outcome is going to be a rounding error for First American. A top flight cyber security setup costs 8 digits per year or more; unless the fine is high 9 digits or more, being insecure has paid off, particularly since First American’s business is basically a monopoly/monopsony and there is very low likelihood of actual business fallout.
885 Million consumer records exposed. $1000 fine per record accessed. Each record can be accessed multiple times, each time incurring a new fine.
885 million times 1000 means an 885 billion fine. Not counting multiple accesses to the same records.
They had revenue (not profit) of 6.2 billion in 2019. Is a fine of more than 100 times their yearly revenue enough?
I think you can see why their initial response isn’t so much as to dispute the facts but instead claim that the venue is inappropriate (“none from New York”). Of course it’s worthless – they’re on the NYSE which is what makes the venue appropriate.
Looks like some CxOs are about to get a costly lesson in why they shouldn’t have slashed IT budgets to the bone.
The fines are levied on records were provably accessed improperly; not on the amount of potential records exposed.
If we look at what the scraper bots may have been vacuuming up, its about 350,000 files as per FAF’s own records. The fine is not fixed at $1000 per record, rather that is the maximum penalty; regulators decide what the fine value will be for each file improperly accessed.
Conceivably, a max fine would be $350M based on these numbers alone.
Yes, your assessment of max fine is more realistic.
And realistically, the actual fine is going to be a lot less.
My bet is under $100M for sure, under $20M very possible.
Big enough that the law can be said to be successful “Look, yuuuge fine” but small enough that no one gets really peeved.
If the civil cost is in the billions of $s they may file for bankruptcy protection.
…generally there has to damages from loss – so if it gets to litigation the DFS and consumers have to show actual loss…
…there aren’t 885 million consumers or homes in the US so there’s a lot of overlap there…
This data goes back to 2003. Also, one record doesn’t equal one mortgage or title insurance record. Many records corresponded to the same individual.
SCOTUS ruled in the Zappos (Amazon) case last year that breaches don’t have to be accompanied by provable loss. SCOTUS rejecting the case means it goes to trial in Federal court. https://www.scotusblog.com/case-files/cases/zappos-com-inc-v-stevens/
Why wasn’t Equifax charged under this law?
It was drafted in response to that incident.
NYS Dept of Financial Services regulates First American. Whereas Equifax is not regulated by this agency. It is licensed as a CRA under Federal law and if regulated by the FTC. Look at the FTC cases online and you will find that they do not go after big business ever. Why? Good question.
Wonder when a “have I been pwned” type search tool will exist for people to see if their stuff was in the compromise….
>>> the company said a third-party investigation into the exposure identified just 32 consumers [impacted]
From my own regular experience being called to conduct cyber forensic investigations such as this, here’s what the above phrase actually means:
“We have no idea how our internal security systems work, so we paid a 3rd party to come in and try to figure them out. They told us our monitoring systems suck / we had no logging at the time of the breach, and so we/they had no evidence to confirm if more than 32 single records were accessed.
We’re going to therefor claim that “the evidence only shows 32 records were accessed” and we’re going to conveniently minimize the fact that we simply weren’t paying attention at the time the breach occurred, and so we aren’t able to positively know if any others were accessed.”
Sadly another “win” for Krebs digging up security flaw truth and another loss for customers of an organization where management likely vetoed security recommendations until caught by embarrassing public disclosure. Management including the Board of Directors should be held to pay the fines personally for fiduciary irresponsibility.
I agree with you on individuals who are responsible should be held accountable. But just like whistle blowers from Enron the the NSA, a sacrificial goat will be put on the chopping block, and the guilty will jump with a golden parachutes.
I’m mostly stunned it wasn’t fixed immediately after the pen test, that is just pure stupidity. If I was on their IT team and they didn’t let us fix it, I would have left. If the captian decides to let the ship burn, there is no reason to stay on board.
Shareholders benefit from lax security (it saves money, which companies pay out in dividends). It’s not an offense against the company.
I agree but am highly doubtful anyone but the poor souls holding the bag – i.e. the security folks – will have their asses handed to them.
Cybersec folks who are on the ball have already identified the threats, created a risk register and have projects to counter the areas that require remediation. The final hurdle is more difficult than any that precede it… getting the commitment of the board/C-Level… and impossible if there’s little to no visibility of cyber.
My guess is security was underfunded (i.e. not in that sweet spot of 6%-11% of total IT Spend for digital companies) and the execs did not sign off on the “risk acceptance”…
Does anyone know if this breach included First American Home Warranty clients?
Richard – yes First American Home Warranty is a subsidiary of First American Financial
So an absolutely worthless first american home warranty was Excreted, Discharged, and otherwise Passed into and as part of a real estate purchase I made in 2018. I wonder how much of my “bank account numbers and statements, mortgage and tax records, Social Security numbers, wire transaction receipts, and drivers license images” were exposed due to my being the gift recipient of this otherwise totally useless Elimination?
This is why the United States needs federal data protection and or privacy laws on the books to hold big corporation liable for damages against consumers when it comes to data breaches.
I see the name “Brian Krebs” in the NYDFS complaint on page 13 at this pdf link:
https://www.dfs.ny[.]gov/system/files/documents/2020/07/ea20200721_first_american_notice_charges.pdf
(link broken for safety)
Good work Mr. Krebs.
This is the first step in the right direction. Until and unless financial institutions are held liable for their industry-standard security of consumers’ private financial information, no changes will occur.
This is great news. Hold businesses accountable and in the interest of their bottom-line, they’ll have a be forced into a different viewpoint. Up to now it’s been: oh, yeah. About that. So sorry.
When there is a consequence and accountability we’ll see things change.
Thanks BK for always getting the info to us regular people. Best regards.
I do not remember the name of the credit monitoring service you use could you please repeat it
hello
great post
What is that strange font on the form? Like something from those old Lutheran books of souls. Americans are so weird, lol.
It’s ‘weird’ to judge ‘Americans’ generally because of 1 company’s font choice too… actually the word is ‘dumb’ for that. YMMV.
I think the “strange font” you ask about is the handwriting of the person who filled out the form. I assume the form was scanned and the digital image was stored in FAF’s system. At about the same time the digital image was taken, I imagine someone keyed some or all of the values from the form into an application that stored a representation of the data into a database, to make the data searchable and able to be processed by programs.
I imagine there are legal requirements that the original form must be kept, and that a digital image of the original is an acceptable substitute for the original paper.
I am guessing about most of this, since I have never worked in that line of business.
The real solution to this problem isn’t fines, it’s removing their immunity from product liability lawsuits so that 350,000 or more people can file a class-action suit. If we are going to leave security up to careless amateurs then Congress needs to regulate it properly. Expecting commercial entities to know how to secure their data is sheer lunacy! It’s the same as Detroit selling cars without airbags and expecting the buyer to know they must install them and how (except airbags would be easier to install than cybersecurity!).
It doesn’t seem like you understand that the big money behind seat belt laws was the auto insurance companies.
Seat belts reduce deaths; deaths are the single most expensive loss in accidents.
Now let’s take the understanding of this dynamic into cyber: is the cyber insurance industry large enough to generate a similar level of pressure? No.
Are there standard cyber security tools and/or practices which are proven to reduce losses? No.
Does even spending $100M mean you won’t get breached? No.
So why again should companies be liable for poor security – given that “good” security seems far more art than science or engineering?
Note I’m not saying security isn’t important.
I’m saying that systemically, both the practice and economics of cybersecurity simply aren’t scalable.
I have a mortage with them. How can i join the lawsuit?