Thousands of people graduate from colleges and universities each year with cybersecurity or computer science degrees only to find employers are less than thrilled about their hands-on, foundational skills. Here’s a look at a recent survey that identified some of the bigger skills gaps, and some thoughts about how those seeking a career in these fields can better stand out from the crowd.

Virtually every week KrebsOnSecurity receives at least one email from someone seeking advice on how to break into cybersecurity as a career. In most cases, the aspirants ask which certifications they should seek, or what specialization in computer security might hold the brightest future.
Rarely am I asked which practical skills they should seek to make themselves more appealing candidates for a future job. And while I always preface any response with the caveat that I don’t hold any computer-related certifications or degrees myself, I do speak with C-level executives in cybersecurity and recruiters on a regular basis and frequently ask them for their impressions of today’s cybersecurity job candidates.
A common theme in these C-level executive responses is that a great many candidates simply lack hands-on experience with the more practical concerns of operating, maintaining and defending the information systems which drive their businesses.
Granted, most people who have just graduated with a degree lack practical experience. But happily, a somewhat unique aspect of cybersecurity is that one can gain a fair degree of mastery of hands-on skills and foundational knowledge through self-directed study and old fashioned trial-and-error.
One key piece of advice I nearly always include in my response to readers involves learning the core components of how computers and other devices communicate with one another. I say this because a mastery of networking is a fundamental skill that so many other areas of learning build upon. Trying to get a job in security without a deep understanding of how data packets work is a bit like trying to become a chemical engineer without first mastering the periodic table of elements.
But please don’t take my word for it. The SANS Institute, a Bethesda, Md. based security research and training firm, recently conducted a survey of more than 500 cybersecurity practitioners at 284 different companies in an effort to suss out which skills they find most useful in job candidates, and which are most frequently lacking.
The survey asked respondents to rank various skills from “critical” to “not needed.” Fully 85 percent ranked networking as a critical or “very important” skill, followed by a mastery of the Linux operating system (77 percent), Windows (73 percent), common exploitation techniques (73 percent), computer architectures and virtualization (67 percent) and data and cryptography (58 percent). Perhaps surprisingly, only 39 percent ranked programming as a critical or very important skill (I’ll come back to this in a moment).
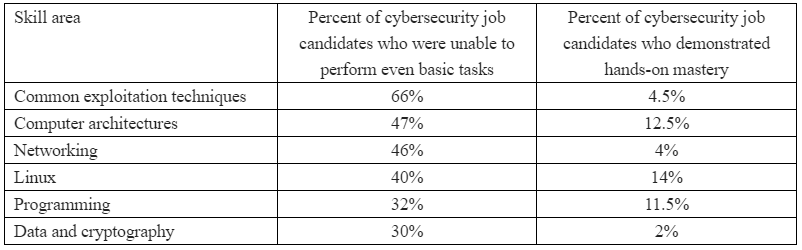
How did the cybersecurity practitioners surveyed grade their pool of potential job candidates on these critical and very important skills? The results may be eye-opening:
“Employers report that student cybersecurity preparation is largely inadequate and are frustrated that they have to spend months searching before they find qualified entry-level employees if any can be found,” said Alan Paller, director of research at the SANS Institute. “We hypothesized that the beginning of a pathway toward resolving those challenges and helping close the cybersecurity skills gap would be to isolate the capabilities that employers expected but did not find in cybersecurity graduates.”
The truth is, some of the smartest, most insightful and talented computer security professionals I know today don’t have any computer-related certifications under their belts. In fact, many of them never even went to college or completed a university-level degree program.
Rather, they got into security because they were passionately and intensely curious about the subject, and that curiosity led them to learn as much as they could — mainly by reading, doing, and making mistakes (lots of them).
I mention this not to dissuade readers from pursuing degrees or certifications in the field (which may be a basic requirement for many corporate HR departments) but to emphasize that these should not be viewed as some kind of golden ticket to a rewarding, stable and relatively high-paying career.
More to the point, without a mastery of one or more of the above-mentioned skills, you simply will not be a terribly appealing or outstanding job candidate when the time comes.
BUT..HOW?
So what should you focus on, and what’s the best way to get started? First, understand that while there are a near infinite number of ways to acquire knowledge and virtually no limit to the depths you can explore, getting your hands dirty is the fastest way to learning.
No, I’m not talking about breaking into someone’s network, or hacking some poor website. Please don’t do that without permission. If you must target third-party services and sites, stick to those that offer recognition and/or incentives for doing so through bug bounty programs, and then make sure you respect the boundaries of those programs.
Besides, almost anything you want to learn by doing can be replicated locally. Hoping to master common vulnerability and exploitation techniques? There are innumerable free resources available; purpose-built exploitation toolkits like Metasploit, WebGoat, and custom Linux distributions like Kali Linux that are well supported by tutorials and videos online. Then there are a number of free reconnaissance and vulnerability discovery tools like Nmap, Nessus, OpenVAS and Nikto. This is by no means a complete list.
Set up your own hacking labs. You can do this with a spare computer or server, or with older hardware that is plentiful and cheap on places like eBay or Craigslist. Free virtualization tools like VirtualBox can make it simple to get friendly with different operating systems without the need of additional hardware.
Or look into paying someone else to set up a virtual server that you can poke at. Amazon’s EC2 services are a good low-cost option here. If it’s web application testing you wish to learn, you can install any number of web services on computers within your own local network, such as older versions of WordPress, Joomla or shopping cart systems like Magento.
Want to learn networking? Start by getting a decent book on TCP/IP and really learning the network stack and how each layer interacts with the other.
And while you’re absorbing this information, learn to use some tools that can help put your newfound knowledge into practical application. For example, familiarize yourself with Wireshark and Tcpdump, handy tools relied upon by network administrators to troubleshoot network and security problems and to understand how network applications work (or don’t). Begin by inspecting your own network traffic, web browsing and everyday computer usage. Try to understand what applications on your computer are doing by looking at what data they are sending and receiving, how, and where.
ON PROGRAMMING
While being able to program in languages like Go, Java, Perl, Python, C or Ruby may or may not be at the top of the list of skills demanded by employers, having one or more languages in your skillset is not only going to make you a more attractive hire, it will also make it easier to grow your knowledge and venture into deeper levels of mastery.
It is also likely that depending on which specialization of security you end up pursuing, at some point you will find your ability to expand that knowledge is somewhat limited without understanding how to code.
For those intimidated by the idea of learning a programming language, start by getting familiar with basic command line tools on Linux. Just learning to write basic scripts that automate specific manual tasks can be a wonderful stepping stone. What’s more, a mastery of creating shell scripts will pay handsome dividends for the duration of your career in almost any technical role involving computers (regardless of whether you learn a specific coding language).
GET HELP
Make no mistake: Much like learning a musical instrument or a new language, gaining cybersecurity skills takes most people a good deal of time and effort. But don’t get discouraged if a given topic of study seems overwhelming at first; just take your time and keep going.
That’s why it helps to have support groups. Seriously. In the cybersecurity industry, the human side of networking takes the form of conferences and local meetups. I cannot stress enough how important it is for both your sanity and career to get involved with like-minded people on a semi-regular basis.
Many of these gatherings are free, including Security BSides events, DEFCON groups, and OWASP chapters. And because the tech industry continues to be disproportionately populated by men, there are also a number cybersecurity meetups and membership groups geared toward women, such as the Women’s Society of Cyberjutsu and others listed here.
Unless you live in the middle of nowhere, chances are there’s a number of security conferences and security meetups in your general area. But even if you do reside in the boonies, the good news is many of these meetups are going virtual to avoid the ongoing pestilence that is the COVID-19 epidemic.
In summary, don’t count on a degree or certification to prepare you for the kinds of skills employers are going to understandably expect you to possess. That may not be fair or as it should be, but it’s likely on you to develop and nurture the skills that will serve your future employer(s) and employability in this field.
I’m certain that readers here have their own ideas about how newbies, students and those contemplating a career shift into cybersecurity can best focus their time and efforts. Please feel free to sound off in the comments. I may even update this post to include some of the better recommendations.




Brian,
I’ve had a very successful 20-year career in cyber security, and I completely agree with your advice. I’m now retired from NASA.
One of my favorite interview questions was: “What is a subnet mask, and what does it do?” I was amazed (and appalled) by how many candidates – some with degrees and a long list of certifications – couldn’t answer that question. It seems that academia is focusing entirely on Layer Seven (the application layer) while neglecting the underlying network.
I often had to say: “You can program. That’s nice. You should interview for a developer position.” And as for degrees, my ideal candidate had the character of Michael Faraday, whose formal education ended at age 12. What made him such a great scientist was his curiosity. Somehow, the academic path today seems to diminish the innate curiosity that will carry a person through their entire cybersecurity career.
For the curious, a subnet mask represents both host and network on which the host(s) belong. 255.255.255.0 (/24) means a network can allocate 254 IP addresses to hosts on a network. The final IP address a host could use would be something like 10.10.10.254, with the final address .255 being used as the broadcast IP. Change the netmask to 255.255.255.240 (/20) increases the number of hosts that can be on a single network from 254 up to 4094. I hope I am recalling this correctly…
…actually a .240 net mask is less IP’s…
…255.255.240.0 is more…
https://dnsmadeeasy.com/support/subnet/
…and normally you’d use either the netmask or the / notation after the IP address, not both as you have…
…the / is usually called the “slash” notation, so if your IP address is 192.168.1.15/24…
…so how many IP addresses are there in this scenario?…
Using the [192.168.0.0/24] example somewhere above:
Class C network address: 192.168.0.1
Network: 192.168.0.0/24 (the “/24”, is shorthand for subnet mask 255.255.255.0, which has 24 leading 1-bits)
Subnet Mask: 255.255.255.0
Broadcast: 192.168.0.255
254 Hosts per subnet
Host address range: 192.168.0.1 – 192.168.0.254
The IP addressing system is built upon a hierarchy, with every IP address containing two parts: one that identifies the network portion and one that identifies the host portion.
Subnetting designates bits from the host portion and groups them with the network portion, and uses bitwise AND calculations. As well as dividing an address into host and network portions, it can be further divided into a subnet number. A subnet mask uses a 32-bit number and dotted decimal like an IP address.
Dividing these addresses and classes into usable networks, usually referred to as subnetting or subnetworking, is a complex, in-depth topic.
Networking professionals sometimes use the format N.H.H.H, where N is the Network and H is the Host (local network devices, computers, and so on).
The process of subnetting helps to address the limitation of global IP addresses and the prospect of them running out. It splits a “network portion” of an IP address into smaller subnetworks on the same network.
I wrote a chapter in a published book (2011) on the topic of: TCP/IP. Even though I’ve never even been employed in computing – so I’m extremely rusty with terminology. I would not use the above as an explanation, but it covers a few random points. There isn’t really room here – without going too far off topic – to explain the basics of Subnetting or things like; octets, most significant bit or CIDR, etc.
For a layperson, just think about how the telephone system uses “division” to conserve limited telephone numbers (area code, etc.) when it routes your telephone calls. So you can simply dial a single phone number, connect and communicate “speaking” to the other person you are trying to reach, using the specific number you dialled.
…the only thing i’d add to your great explanation is that many isp’s are cutting the number of ip addresses you get at home by giving you a brain dead number like (example only) 192.168.25.25/30…
Patrick, “a long list of certifications” (and even a degree), is not enough information to determine a good candidate. And it isn’t even enough information to have any expectation during an interview.
If you listed the certifications, it’ll probably be apparent whether or not someone should be expected to answer a simple question about subnets.
Sometimes, the problem lies with the people looking at the resume, and not the candidate.
Did you give HR a list of required keywords and certification names? Did you make sure all certs have a listed expiration date?
In your job posting, were you specific on what you were looking for? (e.g. at least 2 network, 1 systems, 1 cloud, etc.)
Certification is great, precisely because they expire. Unlike degrees, an employer should expect someone with a current Network+ cert to understand a subnet.
Qualified candidates are out there… but many times, the job listings are poorly done, and the result is a flood of wrong candidates.
Also, I disagree with your idea that formal education isn’t ideal. Nobody should expect a prodigy. In cyber, yes they are out there. But don’t expect to find them, they are very rare.
I don’t usually comment, but in this case I will. Brian is absolutely 100% right. You can be as “book smart” as you want. if you don’t have any practical knowledge or skill you are missing most of your marketable skills. I have been into computers since the early 80’s where I spent a lot of time on BBSes learning what there was to learn in those days ;). I took a vocational class in high school to unix sysadmin skills and to learn structured programming (Basic, Pascal, Fortran, and COBOL). I was working as a sysadmin full time starting in college in the early 90’s and graduated with a degree in MIS. The only class I found useful in college related to my career was a class called fundamentals of data communication where we learned the VERY basics of computer networking. My degree was a nice piece of paper with no real practical value for the time of effort I put into obtaining it. While working as a sysadmin, I taught myself Novell, Lantastic, and Banyan Vines. I also volunteered to help out the PC team work on PC’s as I was fairly proficient with PC hardware. I wanted to learn more so I moved into a network team and learned about Cisco routers and switching. I also enjoyed the infrastructure side so I learned about structured cabling and began to manage all onsite cabling work and managed cabling and data center infrastructure projects on the side. While I was a network guy I spent a LOT of time learning how to debug packet captures on Network General Sniffers. Some of it was in classes to learn the fundamentals, but most of it was in the real world solving real problems. After a long career in networking my employer moved into an Enterprise Architect Role where I spent several years using all the skills I had acquired over the years. After several years in Enterprise Architecture I moved into a Security Architecture role. After a long career at that company I decided it was time to move on and became a Sr. Security Architect at a company that is 100% focused on Cyber Security. Along with consulting with clients I interview potential candidates for various roles. Practical experience trumps being “book smart” and loaded up with degrees and certifications 100% of the time. I have worked with numerous people who had certs and no experience and in every case I have personally been a party too they have no value till they actually know something. This even includes encounters with a couple of guys who had their CCIEs, but really didn’t understand networking. A cert means you interested in a subject, you might know some fundamentals, and is a good place to get started. I tell people if they want to get hand on experience, go volunteer. Find a homeless shelter, a church, or some non-profit and help them for free or for some small amount of money. What you will gain in experience where you actually learn something and can honestly put on your resume will benefit you far more than what they can or can’t pay you hourly. Do it as early as you can (like high school or in college). When I graduated from college I had 4 years of sysadmin experience. If you can’t find volunteer work, then find a job with a company that does IT work and be willing to take an entry level position for the opportunity to learn as much as you can. Thats my advice FWIW….
…i’d agree that volunteering is important, not only do get experience but you’re likely to see things you would not otherwise see…
…btw i built me first s-100 computer in 1984, had to choose cpm or msdos…
JC. thanks for your advice. I’m constantly trying to get my son motivated. He loves tinkering and repairing Macs and PC. I know the a bigger career is in the work you do. What do you do and where do you work?
Thanks
Tim
Hi,
I think another issue with this is people are not asking the right question and the questions they ask they don’t get straigh answers. At this stage asking the right question is the key.
I don’t have a 4 year degree and want to get into cyber security. I want to get the comptia certifications up to security plus for starters but don’t know where to start learning. I’m trying the monthly sub websites like cousera, edx, etc but do not feel ready to take the test with these only. Can anyone help?
…get network+…
…then security+…
…then cissp…
…spend a year on the help desk…
…then you can specialize after that…
…then in maybe 5 years you know enough to be useful in cyber…
CISSP requires 5 years of security related experience across a ceratin number of the 8 domains. Telling someone to get the CISSP before spending a year on help desk seems like bad advice.
My advice –
A+
Net+
–Start applying for entry level jobs in IT
Security+
Linux+
–Setup Github account and start doing some python / java coding and put your projects out there. Look for problems that you need to slove at work and see if you can solve them programatically
–Start building skills by home labbing / job shadowing where possible. Get involved in local infosec groups
–Begin looking for more advanced roles in IT or lower level roles in security
SSCP or SSCP associate
GSEC if you can swing it
CASP
CySA
CCNA Cyber OPs
–Make the full time switch to security
CISSP or CISSP associate
…when i got my cissp you did not need 5 years experience, a resume review, and a recommendation from another cissp, now you do…
…my point was you need five years experience to be useful, the other certs give you that although you can get that experience in other ways, you don’t need all those certs…
I agree you don’t need the certs, I was using them as more of a reference as a study path. On the other hand having the certs helps you get past the HR filter
…yep…
…and the hr filter is often an AI fueled pos…
…or worse yet, a human with zer0.nada knowledge…
@john lee read the blog post above
Go to a Community College. We have a great IT program at TCC (Tidewater Community College). I have taught here for 19 years. Our IT program is hands on bottom up basics first program.
…i agree – in alaska we have ctc and they have a pretty good teacher and a good AA in cyber…and it’s online…
Very helpful.
I’m currently going through penetration testing career path. I have a fair knowledge of networking but I don’t know real world hand-on experience though I try to play around with some virtual environment. I agree that volunteering will be a good way to get some real world experience but I don’t know how or where to get this. any suggestions on where I can volunteer ? I will really appreciate any suggestions.
Most Cyber Security Experts are career techs who have spent their life working through the IT systems they protect it is not something you can book learn in a couple years. Look for a Community College with a good program.
Our program at TCC Tidewater Community College has broad base of knowledge with a lot of hands on.
The Cyber Security Program is designated as a National Center of Academic Excellence in Cyber Defense (CAE2Y) for Two-Year schools (NSA-CAE2Y) by the National Security Agency and the U.S. Department of Homeland Security.
Does depend on what you count as mastery take networks do you mean some one like me who has say CCNA level for tcp/ip worked in OSI I had root on the UK’s ADMD
Or do you mean someone who decide he ought to get one of these CCIE certs – did the exam got 98% and wrote a personal letter to John Chambers explain why he was right.
This guy was one of the three inventors of ethernet.
…you need the equivalent knowledge of a ccna, not the cert necessarily, but it don’t hurt…
…if you want to make big bucks you get a ccne…
…the rest of your post is noise…
Phoenix cyber security hiring managers have recently stated that “character and enthusiasm” win the day over certifications (within reason, obviously). They noted that having integrity, treating people well, and an insatiable curiosity sit front seat. They noted the preference for “good people” that show a commitment to the field (e.g. using available home or online labs), which supports what Brian said.
There will always be those positions that simply require a given set of skills but perhaps the reason we have 1M+ unfilled positions is because hiring managers are putting the wrong priorities first. We have all been on a team where there was that one toxic person, right?
For entry level positions, yes, a baseline set of knowledge is valuable. We offer an intro to cybersecurity course, ISACA has the CSX Fundamentals, and CompTIA has the Security+. If you can find someone with these and are “good people” then hire, hire, hire and then help them specialize to meet your own unique needs.
How do people get a foot in the door? I’d recommend focusing on level 1 analyst roles in a security operations center (SOC) or managed/monitored security services provider (MSSP) and/or in governance, risk, and compliance (GRC).
Jeffrey
It’s funny reading all these comments from people that got into this business 20+ years ago and landed a job with no experience tell people that they should volunteer and work for free on top of the degree and certs that are already required of us now.
There might be a skills gap, but that gap starts with the employers themselves who don’t want to lift a finger to train anybody, but also expect a unicorn employee with 10+ years of very specific experience and perfect resume that get’s them through the HR robot firewall to fall into their lap and fill an “entry-level” position at entry-level pay.
…the question was how to “break in” – the answer is to get experience…
..the rest, as they say, rests on that…
…waiting for training from an employer is a formula to get old, with no experience…
…a “progressive” solution…
Another funny thing is that a lot of those people with +20 years of experience in the field as so called “security experts” has some of the most insecure systems I’ve ever seen while on pentesting engagements.
A lot of their so called skill sets are obsolete these days and yet they insist they know how to do their jobs.
…if they only had 20 years experience then it’s wrong at best…
…or they did not really have experience they just worked as a cog in a place where they did not really learn…
…from someone with 40+ years experience…
As retired and still passionate IT (Security) Consultant I fully agree with your story and findings.
I hope new employees can understand it and will follow your advise.
Thanks for the nice story,
Kind regards,
John
With so many certification types, who do you recommend getting these kinds of certs at what point in their career?
CISSP
CompTIA Security+
CEH
CISM
CISA
Thanks
Tim
Here’s a quick swag:
CISSP – generally viewed as the leading certification for mid-career professionals cover general security. Requires 5+ years of security experience. Because of its scope, someone with a CISSP can *generally* be viewed as versed in multiple aspects of computer security.
CompTIA Security+ – from the web site: “validates the baseline skills you need to perform core security functions and pursue an IT security career”. Good first-level cert.
CEH – if you want to do penetration testing and similar roles, this is the cert for you. It’s tough but companies who are serious about security will seek out CEHs.
CISM – another good, general cert. I have heard a few people say it’s not as rigorous as a CISSP but I wouldn’t pass up a resume with a CISM.
CISA – if you want to do information security auditing, this is almost required. It is geared more towards auditing procedures and governance but does cover general info sec.
Personal aside – early in my career I was anti certification (I just didn’t want to deal with more tests). However, after I was laid off and forced into a quick job search my opinion changed. Certs improve the probability of having your resume be noticed. I currently have a CISSP and a PMP. I started a new job last November and my boss right out told me one reason I got the interview was because of my certs.
Is there/Could we get an article for developers and computer science grads that wish to explore changing careers or getting started in this field? Most of the things in the table of desirable skills overlap with what developers need to know too, but many devs lack knowledge of networking and security beyond the application layer as well as hands-on experience.
I have a CS degree, mainly specialized in security topics in college, studied for the CCNA, and have years of experience with Linux (so nothing special from a dev perspective). But, I know I lack experience with penetration testing and system administration, as well as knowledge of security professional methodologies and practices. Something tailored to identifying where the knowledge gaps are and how to address them would be greatly appreciated.
I made the switch from development to security after 10+ years of development. For me, I took on non-development projects at work that lead me toward security (I worked at a bank so security was pretty ingrained). For example, I became the expert on application security audits. I learned what auditors looked for and how to have that evidence ready. Having the evidence ready meant I got involved with the vulnerability scanning, pen testing, authentication, authorization, user roles, secure data transmission & storage, and more.
Development is a great way to get into security – particularly if you are a developer in a high-regulated industry such as financial services or healthcare. In my experience, we need more people from the development & application side in security. If you work at a company with an information security group, contact them about being a “secure code champion” or something similar. At the bank I worked at, when I engaged the corporate info sec team about that, I became their best friend.
Finally, security is much more than pen testing and firewall rules – take a look at the domains in the CISM or CISSP.