In May 2019, KrebsOnSecurity broke the news that the website of mortgage settlement giant First American Financial Corp. [NYSE:FAF] was leaking more than 800 million documents — many containing sensitive financial data — related to real estate transactions dating back 16 years. This week, the U.S. Securities and Exchange Commission settled its investigation into the matter after the Fortune 500 company agreed to pay a paltry penalty of less than $500,000.

First American Financial Corp.
If you bought or sold a property in the last two decades or so, chances are decent that you also gave loads of personal and financial documents to First American. According to data from the American Land Title Association, First American is the second largest mortgage title and settlement company in the United States, handling nearly a quarter of all closings each year.
The SEC says First American derives nearly 92 percent of its revenue from its title insurance segment, earning $7.1 billion last year.
Title insurance protects homebuyers from the prospect of someone contesting their legitimacy as the new homeowner. According to SimpleShowing.com, there are actually two title insurance policies in each transaction — one for the buyer and one for the lender (the latter also needs protection as they’re providing the mortgage to purchase the home).
Title insurance is not mandated by law, but most lenders require it as part of any mortgage transaction. In other words, if you wish to take out a mortgage on a home you will not be able to do so without giving companies like First American gobs of documents about your income, assets and liabilities — including quite a bit of sensitive financial data.
Aside from its core business competency — checking to make sure the property at issue in any real estate transaction is unencumbered by any liens or other legal claims against it — First American basically has one job: Protect the privacy and security of all these documents.
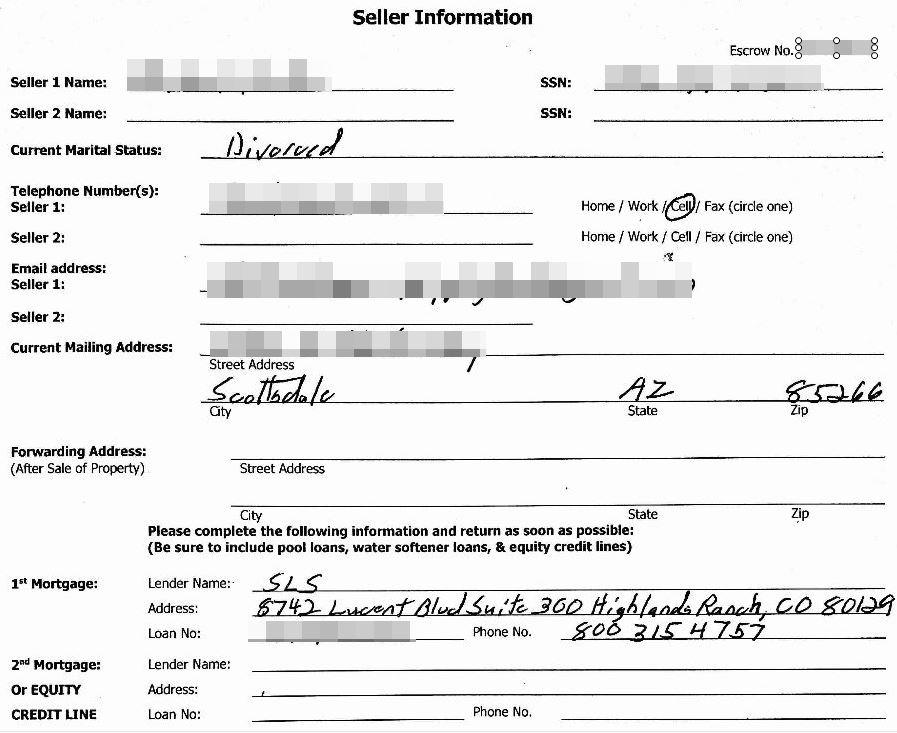
A redacted screenshot of one of many millions of sensitive records exposed by First American’s Web site.
It’s easy to see why companies like First American might not view protecting this data as sacrosanct, as the entire industry’s incentive for safeguarding all those sensitive documents is somewhat misaligned.
That is to say, in the title insurance industry the parties to a real estate transaction aren’t customers, but rather they are are the product. The actual customers of the title insurance companies are principally the banks which back these mortgage transactions.
We see a similar dynamic with social media platforms, where the “user” is not the customer at all but the product whose data is being bought and sold by these platforms.
Roughly five months before KrebsOnSecurity notified First American that anyone with a web browser could view sensitive document in its “Eagle Pro” database online just by changing some characters at the end of a link, an internal security audit at First American flagged the exact same vulnerability.
But the company never acted to fix it until the news media came calling.
The SEC’s administrative proceeding (PDF) explains how things slipped through the cracks. Under First American’s documented vulnerability remediation policies, the data leak was classified as a security weakness with a “level 3” severity, which placed it in the “medium risk” category and required remediation within 45 days.
But rather than recording the vulnerability as a level 3 severity, due to a clerical error the vulnerability was erroneously entered as a level 2 or “low risk” severity in First American’s automated tracking system. Level 2 issues required remediation within 90 days. Even so, First American missed that mark.
The SEC said that under First American’s remediation policies, if the person responsible for fixing the problem is unable to do so based on the timeframes listed above, that employee must have their management contact the company’s information security department to discuss their remediation plan and proposed time estimate.
“If it is not technically possible to remediate the vulnerability, or if remediation is cost prohibitive, the [employee] and their management must contact Information Security to obtain a waiver or risk acceptance approval from the CISO,” the SEC explained. “The [employee] did not request a waiver or risk acceptance from the CISO.”
So, someone within First American accepted the risk, but that person neglected to ensure the higher-ups within the company also were comfortable with that risk. It’s difficult not to hum a tune whenever the phrase “accepted the risk” comes up if you’ve ever seen this excellent infosec industry parody.
The SEC took aim at First American because a few days after our May 24, 2019 story ran, the company issued an 8-K filing with the agency stating First American had no prior indication of any vulnerability.
“That statement demonstrated that First American’s senior management was not properly informed of the prior report of a vulnerability and a failure to remediate the problem,” wrote Michael Volkov, a 30-year federal prosecutor who now runs The Volkov Law Group in Washington, D.C.
Reporting for Reuters Regulatory Intelligence, Richard Satran says the SEC charged First American with violating Rule 13a-15(a) of the Exchange Act.
“The rule broadly requires firms involved in securities issuance to have a compliance process in place to assure material information follows securities laws,” Satran wrote. “The SEC avoided getting into the specific details of the breach and instead focused on the way its disclosure was handled.”
Mark Rasch, also former federal prosecutor in Washington, said the SEC is signaling with this action that it intends to take on more cases in which companies flub security governance in some big way.
“It’s a win for the SEC, and for First America, but it’s hardly justice,” Rasch said. “It’s a paltry fine, and it involves no admission of guilt by First American.”
Rasch said First American’s first problem was labeling the weakness as a medium risk.
“This is lots of sensitive data you’re exposing to anyone with a web browser,” Rasch said. “That’s a high-risk vulnerability. It also means you probably don’t know whether or not anyone has accessed that data. There’s no way to tell unless you can go back through all your logs all those years.”
The SEC said the 800 million+ records had been publicly available on First American’s website since 2013. In August 2019, the company said a third-party investigation into the exposure identified just 32 consumers whose non-public personal information likely was accessed without authorization.
When KrebsOnSecurity asked how long it maintained access logs or how far back in time that review went, First American declined to be more specific, saying only that its logs covered a period that was typical for a company of its size and nature.
However, documents from New York financial regulators show First American was unable to determine whether records were accessed prior to Jun 2018 (one year prior to fixing the weakness).
The records exposed by First American would have been a virtual gold mine for phishers and scammers involved in Business Email Compromise (BEC) scams, which often impersonate real estate agents, closing agencies, title and escrow firms in a bid to trick property buyers into wiring funds to fraudsters. According to the FBI, BEC scams are the most costly form of cybercrime today.
First American is not out of the regulatory woods yet from this enormous data leak. In July 2020, the New York State Department of Financial Services announced the company was the target of their first ever cybersecurity enforcement action in connection with the incident, charges that could bring steep financial penalties. That inquiry is ongoing.
The DFS considers each instance of exposed personal information a separate violation, and the company faces penalties of up to $1,000 per violation. According to the SEC, First American’s EaglePro database contained tens of millions of document images that included non-public personal information.




As usual the “good ole boy” club protects each other. It would seem to me to be more appropriate to add three zeros to the fine just for force management to respond to investors about the reason for their incompetence in protecting sensitive personal information.
While applying to speedway, someone in Indianapolis Indiana, had used selv apis, and shadows to exploit them through cheap prepaid phone I’m using, this on wotc assessment recording it to the actual submittal form and also blocking me from submitting application for review by company, as completed. They probably did this to spread malware prior to my onboarding
Dear customers of First American Financial,
$500,000 fine / 800,000,000 documents compromised = $0.000625 penalty for FSF’s total and complete failure to protect your highly sensitive financial information. Don’t spend it all in one place. (Oh, wait. You don’t actually get any of even that pittance.)
You’re welcome.
– Securities & Exchange Commission
Their needs to be mandatory fines and penalties against companies that don’t keep their secure. In the past 10 yrs we consistently see these bad actor events occur and the companies get a slap on the wrist if any penalty at all. Until the consequences are increased to inflict financial harm will these companies take network and personal data security seriously. This is the new crime spree we are seeing escalate with these hackers/bad actors and it’s increased 300%. Everyone needs to wake-up because this will continue to get worse cause the consequences don’t equal the amount of money and data that are being stolen/harvested.
“But the company never acted to fix it until the news media came calling.”
“and it involves no admission of guilt.”
-Official slogans of Corporate America
What are the chances that NY DFS are going to extract a meaningful eye-opening for this “medium” total fail in their first-ever enforcement action that won’t then be appealed for 10 years itself.
$500k…
500k of their vital organs? Because if they only paid $500k in cash then we can look forward to this being ignored
Video so, so good…looking forward to more on the Kreb’s MTV channel…
Right? So perfectly dumb-great, we loved it. There’s a whole slew of ’em. It fills the void for a moment.
Looks like SEC is reminding the industry that just accepting the risk is the proper choice; if exposing all the customers’ data costs just $500k then it would be stupid to invest in actual security, which would be much more expensive than that.
…it’s pretty typical of the SEC that if someone else (in this case the “…New York State Department of Financial Services…” is investigating the SEC bows out…
…nothing to see here…
Wonder if Afroman gets any residuals? (Pro Tip: Tall Cans is a better song)
https://www.youtube.com/watch?v=WeYsTmIzjkw&ab_channel=AfromanVEVO
https://www.youtube.com/watch?v=2Eyna84qI9o&ab_channel=kyoukilis20
Please note that this was only the SEC’s fine against First American Title for specifically First American Title’s conduct on May 24, 2019 in responding to Brian’s original report, and on May 28, 2019 with their Form 8-K. This fine does NOT go after the underlying security breach and disclosures by the First American Title’s EaglePro or FAST Repository systems.
As reported in this article and many others, the New York State Department of Financial Services conducted its own investigation into the matter, and found far more than what was originally reported here. It helps to be able to go into a hostile company’s turf and issue investigative subpoenas, I expect. Please check out the NYS DFS Complaint from their website at https://www.dfs.ny.gov/system/files/documents/2021/06/ea20200721_first_american_noh.pdf as that makes incredible reading in and of itself.
NYS DFS has the potential to levy billions of dollars in fines under this enforcement action.
Similarly, the Federal Trade Commission has clear jurisdiction for yet another set of claims against First American Title as well, since representations were made by First American Title about how secure their FAST Repository was. The FTC has been silent thus far, to the best of my knowledge, but I expect that the FTC is awaiting NYS DFS actions to determine whether additional enforcement action would be appropriate.
Yes, a $487,616 civil penalty would be considered paltry in the face of the over 850 million documents (ranging in dates from 2003 to 2019) that were exposed between 2013 and 2019. Instead, consider this is only the SEC fine for filing one highly-misleading Form 8-K, and one egregiously wrong public statement, and that First American Title faces regulatory action from more agencies that will focus on the underlying cybersecurity breach circumstances and First American Title’s cyber liability for failing to meet its responsibilities to protect that information.
…correct, the SEC only cares about Securities Act of 1934 as updated, violations (like an incorrect 8k and such). The current law only requires public companies to disclose cyber issues in the 8k. They let others enforce cyber violations…
Or a written lie to the SEC, for a prescient example? That’s worth something too – $500,000 ante.
Let’s see if they double down.
SEC enforces Sarbanes Oxley. SOX has Cyber requirements, but Treasury doesn’t have (enough or any?) Cyber Examiners on staff. NIST 800-115 is the Federal Government’s Technical Guide to Information Security Testing and Assessment. On Page 22 charts show the skills/certifications required to perform a technical security assessment. But in the 2020 GAO-20-631 Financial Services Cybersecurity report on page 35 Treasury admits that it can only perform 10 cyber examinations at a time, despite 88,000 employees. Treasury needs to be restructured. If their focus solely remains accounting and small-time securities fraud, they need to rebalance/retrain their staff to handle cyber forensics investigations. Treasury needs to refocus on the fraud that puts the USA most at risk, and this fraud always has an element of technological discovery.
Sending First American data offshore is a violation of many Federal laws. Title insurance is only applicable to N America. So why does First American have 3,000 IT workers in India? Why didn’t anyone in Treasury perform a NIST 800-115 assessment on them? Data discovery and data flow mapping is the first vulnerability assessment required under NIST 800-115. Taxpayers should stop funding cybersecurity in the Federal and State Governments, until they stop allowing this offshoring of our sensitive data – because it is a ridiculous notion to think that offshored data can be secured when India and China outlaw encryption. Data traveling to India from the US first lands in China.
Obama’s 2010 Executive Order about Classified Uncontrolled Information – is data sensitive to US National Security. Since consumer data is exploited to compromise employers and also steal from the Government, aside from the fact that First American has VA, Fannie and Freddie data in it – it is most certainly CUI. CUI is not allowed to leave the USA nor be accessed by non-American Citizens. $400B was stolen from Treasury due to these data leaks. $400B is Medicaid’s annual budget. Do you think that Americans won’t suffer due to this?
We also need a federally sponsored IT apprenticeship program in the US. Most IT roles do not require an a college degree. Most foreign workers arrive with no relevant experience. They receive on-the-job training. If Big Tech is serious about lack of diversity in tech — they should stop importing unskilled labor and instead turn to unemployed Americans. We are the only developed nation in the world that allows our sensitive data to be offshored. The CMMC-AB has the potential to stop this — but we cannot wait 4 years. We need it now across the entire public and private regulated sector. We need centralized Cybersecurity in the US. And no self-attestation. Zero Trust is Zero Trust.
Solving our Cybersecurity simply takes will. Not more money. There’s presently no will.
The SEC did a great job prosecuting Sudhakar Reddy Bonthu and Jun Ying the former CIO of Equifax. The SEC Ying Complaint tells you all you need to know about what really happened at Equifax. Not uncommon in my experience. Brian are you aware that the Appeals court approved the Equifax Consolidated Class Action the other day which doesn’t require Equifax to remediate any of the vulnerabilities identified in Republicans-oversight.house.g ov report (which was more informative than the Dems report), nor the Senate’s Homeland Security report? The GOP House Oversight report on page 95-96 under recommendations it speaks about how Equifax is CUI data and subject to additional restrictions (not allowed to leave the US but it did). It also notes that Equifax provides identity verification for SSA, USPS and IRS. They also own the Work Number which has 225+ million employment verification records. Maybe Jeff Bezos or Warren Buffet should consider suing them for leaking access to their tax returns. Because once Equifax pays out the $380 Million to the Class Action attorneys, there won’t be any remote possibility of Cybersecurity for any American. Equifax doesn’t have enough cash for the fine. So they will sell our data that’s sitting offshore outside of US jurisdiction. Congress already knows that this is happening. Look at Wyden’s “Do Not Sell Our Data” bill.
Hey you guys, give the company a break, will ya? FAF (and others) already pay a lot – year in and year out – supporting our [strike]politicians[/strike] freedom and democracy!!
When one company makes it so abundantly clear that it cannot be trusted to competently safeguard so much data, it should be split up to prevent such spectacular failures. That’s a consequence that ought to really serve as a deterrent (far more so than any fine could ever do) AND if implemented, simultaneously prevent such widespread future issues. If it were split into 52 totally unrelated companies, one for each state plus D.C. and the territories, any such breach would be 1/52 the size of this one.
Except California, which would be a breach about 1/8th the size.
Why do people keep voting for the same old (most are both old in age and in incumbency) politicians and the same two (failed) political parties, and expect change? The loonies are you–the people who vote–not the continually re-elected politicians, not the Chinese, not the Russians, not the Blue Man (oops, person) from Mars. Vote for people who will change the law to more heavily fine companies and who will confirm judges who will impose the fines. 2/4/6 people!
I think way too many people have succumbed to the notion that their party and candidates might be losers – but the other side is far worse. And so each side continues to “support” their respective losers! The result: you don’t need to have integrity, wisdom, conviction or even ability. You just need to echo your party’s fav taglines with charm and charisma – and have money – or the ability to raise money.
https://fivethirtyeight.com/features/why-the-two-party-system-is-wrecking-american-democracy/
Mwah- party loyalty above God family and county , how do you change that ..
We’re supposed to believe that a competent vulnerability tester rated this only a medium, and then accidentally it was set to low? I have worked with many people who do this work for a living. The one thing ALL of them have in common is pride in finding big, stupid flaws. No way one of them allows this to be a medium. And low?….forget about it. Unless the testing is completely outsourced and they have “risk mgmt” people deciding severity, no way this is how it went down.
Fines further erode Cybersecurity. Treasury doesn’t address root cause that caused the breach. Nor do they validate that root cause was remediated. The fines paid to Treasury and other government agencies just go back into their budget to pay examiner salaries. Meanwhile First American will have to cut budgets to appease shareholders resulting in more offshoring and more theft from Americans. After Equifax was fined and sued they sent American data entirely offshore to avoid any regulatory scrutiny. Meanwhile CNBC reported that the Equifax data never resurfaced on the dark web. How was $400 Billion in unemployment fraud perpetrated? Wouldn’t Equifax and First American stolen data be useful to execute the scale of unemployment theft from US Treasury that took place? It was executed so quickly that it had to be organized by insiders. The Federal and State Government shouldn’t fine corporations. This is criminal. Violators should go to jail and the MSP/IT companies repeatedly involved should be barred from the USA.
There is little commercial incentive for any corporation maintaining large databases of sensitive information to spend the funds to take reasonable steps to protect the information from criminals, with the exception of protecting from ransomware due to the real cost. After Brian’s informative posts about SMS vulnerability, one would think that authenticator apps & tokens would become more common MFA alternatives. But while Apple touts itself as the paragon of privacy and security, Authenticator/token-based MFA is not yet available even for iCloud mail. None of my banks or credit card companies have it either.
What is needed is a Sarbanes-Oxley type law that comes with both civil, and where flagrant, criminal penalties holding CEOs and key IT executives personally responsible for not taking reasonable “best practice” cybersecurity steps within their purview. Until that happens, cybersecurity enforcement is little but “Talk”.
Title insurance is a typical insurance industry scam. No substantive investigation is done until a claim is filed. When such a claim is filed, the title insurance investigators devote a lot of time into investigating the home owner for a fraudulent investigation in the hope that even a technical homeowner mis-statement will leave the title insurance company with no obligation to pay.
After I bought a home just after completing business law courses for a Real Estate BBA, I noticed some irregularities by doing my own “title search” using public records (court records, register of deed records, etc.). When I sent to documentation to the title insurance company, they simply shrugged off the information. Insurance companies make their profits by investing the incoming cash-flow (premiums) and paying off as little as possible.
For most insurance incidents that affect you (including auto accidents), promptly hire your own lawyer and task that lawyer with accumulating every bit of evidence that you may use to negotiate with the insurance company (hint – experience has shown that insurance companies do not keep track of evidence, especially that which may benefit you or not the insurance company).
Watch out for the fine print in title insurance contracts that says all they do is one simple check of leins recorded at the government records office, and other than guarantying they correctly gave you the results of that one check, the title insurance covers nothing else. You can do that check yourself in a few minutes and save hundreds.
I was a programmer/developer in the title insurance industry once upon a time, largely before online troves of data. It’s protection for the mortgagor (lender) interest — not the property owner’s, and the mortgagee pays the premium. They deal in volume and is quite lucrative in terms of claims paid to premium revenue collected,, and are late-comers to automation. Sounds like there’s about as much data protection concern here as there is for credit reporting agencies, which is pretty sad state of affairs.
NYDFS Financial Services Cybersecurity Regulations https://ccl.yale.edu/sites/default/files/files/New%20York%20State%20Department%20of%20Financial%20Services%20-%20Cybersecurity%20Requirements.pdf
Require that that a CISO and Cybersecurity staff be qualified and that a Senior Officer (CISO) or Board Member sign off on their security compliance. Lying to the Government is 20 years in jail, and 23 NYCRR 500 is an adjunct to existing Federal Financial Services Cyber laws. It gives NYS the right to protect New Yorkers, but it doesn’t have the ability to supersede a Federal law which provides consumers with more protections.
Here’s another NYDFS case that involved the Federal Gov and a financial institution lying to regulators. https://www.nytimes.com/2012/08/15/business/standard-chartered-settles-with-new-york-for-340-million.html
The CISO and Information Security personnel at First American have long term tenure. After the Equifax breach a lot of attention was on the CISO and that she majored in Fine Arts and didn’t have a technological or cybersecurity experience required for the position.
First American’s CISO was educated to be a Mortician. Sarbanes Oxley law passed in 2002, yet she claims she began auditing technology in 2003. Did she forget to put her Accounting Degree and CPA license on her LI? Or did other financial institutions and Deloitte let her perform audits without either? If she is CPA, doesn’t making a material misrepresentation of an audit criminal?
First American is a public company, therefore the CISO not only has to attest to NYDFS about Cyber but she also has to make the same annual attestation to her Board of Directors and it is reported to the SEC. If the CISO lied about Cybersecurity in the years of the leak, isn’t that 20 years in prison for each time she did that? Why would NYS just accept a fine in lieu of prison?
New York regularly sends people to jail for lying to regulators. But maybe that law just applies to citizens who aren’t wealthy enough for top lawyers. Benjamin Lawsky the father of NY’s Cyber law, the former Superintendent of NYDFS was driven from office for doing his job well. On his Wikipedia it says “He is noted for targeting individuals within the financial sector who commit wrongdoing, and not merely handing out fines to the companies they work for, an approach he explains as follows: “Corporations are a legal fiction. You have to deter bad individual conduct within corporations. People who did the conduct are going to be held accountable.”
Since NYS takes Federal funds, they have to comply with FISMA and CUI regulations. They also have a responsibility to find those Unemployment funds stolen from Treasury. Rushing to fine First American or Equifax before this Treasury unemployment fraud investigation is complete is wrong. If this emanated from overseas, it could be a terror attack in which case it is highly inappropriate for NYS or the courts to render any determination at this time. This investigation needs to remain open and the data flows discovered by entities capable of doing so.
In my experience bad Cybersecurity is intentional and it can always be attributed to CISO’s and Cyber staff that aren’t qualified for their jobs. It is common these days for Cyber staff to not have any technological background. It’s no different than the proliferation of snake oil salesman in medicine at the turn of the last century.
Except California, which would be a breach about 1/8th the size in the area too.
I when I read “clerical error” associated with a title insurance company I was horrified. Clerical Errors could indicate errors in title insurance or other aspect First America. Title insurance company’s should have the best clerical people in the industry. They should dot all the i’s and cross all the T’s and double check every cog in the process. The odor is getting bad at the SEC. A commenter brought up “Class Action” so if there are any lawyer types here can Fist America and all or some of its subsidiaries be sued in a class action lawsuit?
Lots of news involving the SEC this week.
When someone dies you owe it to them to echo the truth. Are any other Cyber experts brave enough?
https://twitter.com/officialmcafee/status/1400482858741948424
Irrespective of what you thought about this guy, he was a Cybersecurity pioneer.
We see 3-4 First American scam emails a month that purport to have a real estate closing statement attached to entice us to open the attachment.
I don’t know if this is part of the document breach or if the fraudster assumes that any idiot will open an email from First American.
After Brian’s disclosure of the breach in 2019, I can’t imagine the circumstances that would make me open one of these attachments. In my neck of the woods we don’t deal directly with First American so it is a given that the email is a scam.
Infrequently, we get similar emails from other title companies. 95% of the scam emails come from “First American”.
As to your “Seller Information” screen shot, that version omits the obvious information the settlement agent wants — the Social Security Numbers for the IRS reporting. And at some point we want your bank account information so we can wire your proceeds. ☺
What a country!
First American management has instilled a culture of kill the messenger so no one wants to notify anyone senior officials any issues. FA management also directs minimal compliance with regulations – don’t want to “waste” money. Management follows the mafia approach with having a lot of “buffers” around senior management so they have plausible deniability. Someone expendable will go down but not those truly responsible. FA used to have a culture of honesty and integrity. Not any more. Too bad – especially for those who get thrown under the bus.
This is the new wrongdoing binge we are seeing heighten with these programmers/troublemakers and it’s expanded 300%. Everybody needs to awaken in light of the fact that this will keep on deteriorating cause the results don’t rise to the measure of cash and information that are being taken/gathered.
Wow, it’s very helpful blog for comments. Will try to follow all these stuff!