Most people who operate DDoS-for-hire businesses attempt to hide their true identities and location. Proprietors of these so-called “booter” or “stresser” services — designed to knock websites and users offline — have long operated in a legally murky area of cybercrime law. But until recently, their biggest concern wasn’t avoiding capture or shutdown by the feds: It was minimizing harassment from unhappy customers or victims, and insulating themselves against incessant attacks from competing DDoS-for-hire services.
And then there are booter store operators like John Dobbs, a 32-year-old computer science graduate student living in Honolulu, Hawaii. For at least a decade until late last year, Dobbs openly operated IPStresser[.]com, a popular and powerful attack-for-hire service that he registered with the state of Hawaii using his real name and address. Likewise, the domain was registered in Dobbs’s name and hometown in Pennsylvania.

Dobbs, in an undated photo from his Github profile. Image: john-dobbs.github.io
The only work experience Dobbs listed on his resume was as a freelance developer from 2013 to the present day. Dobbs’s resume doesn’t name his booter service, but in it he brags about maintaining websites with half a million page views daily, and “designing server deployments for performance, high-availability and security.”
In December 2022, the U.S. Department of Justice seized Dobbs’s IPStresser website and charged him with one count of aiding and abetting computer intrusions. Prosecutors say his service attracted more than two million registered users, and was responsible for launching a staggering 30 million distinct DDoS attacks.
The government seized four-dozen booter domains, and criminally charged Dobbs and five other U.S. men for allegedly operating stresser services. This was the Justice Department’s second such mass takedown targeting DDoS-for-hire services and their accused operators. In 2018, the feds seized 15 stresser sites, and levied cybercrime charges against three men for their operation of booter services.
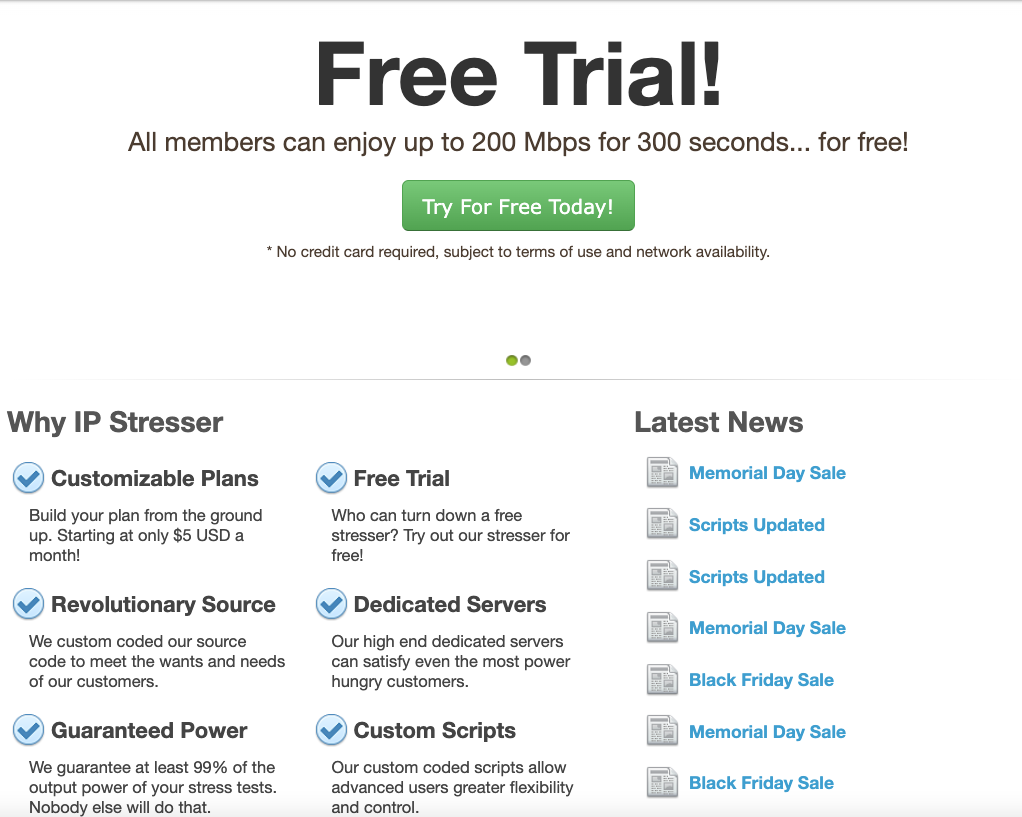
Dobbs’s booter service, IPStresser, in June 2020. Image: archive.org.
Many accused stresser site operators have pleaded guilty over the years after being hit with federal criminal charges. But the government’s core claim — that operating a booter site is a violation of U.S. computer crime laws — wasn’t properly tested in the courts until September 2021.
That was when a jury handed down a guilty verdict against Matthew Gatrel, a then 32-year-old St. Charles, Ill. man charged in the government’s first 2018 mass booter bust-up. Despite admitting to FBI agents that he ran two booter services (and turning over plenty of incriminating evidence in the process), Gatrel opted to take his case to trial, defended the entire time by court-appointed attorneys.
Prosecutors said Gatrel’s booter services — downthem[.]org and ampnode[.]com — helped some 2,000 paying customers launch debilitating digital assaults on more than 20,000 targets, including many government, banking, university and gaming websites.
Gatrel was convicted on all three charges of violating the Computer Fraud and Abuse Act, including conspiracy to commit unauthorized impairment of a protected computer, conspiracy to commit wire fraud, and unauthorized impairment of a protected computer. He was sentenced to two years in prison.
Now, it appears Dobbs is also planning to take his chances with a jury. On Jan. 4, Dobbs entered a plea of not guilty. Neither Dobbs nor his court-appointed attorney responded to requests for comment.
But as it happens, Dobbs himself provided some perspective on his thinking in an email exchange with KrebsOnSecurity back in 2020. I’d reached out to Dobbs because it was obvious he didn’t mind if people knew he operated one of the world’s most popular DDoS-for-hire sites, and I was genuinely curious why he was so unafraid of getting raided by the feds.
“Yes, I am the owner of the domain you listed, however you are not authorized to post an article containing said domain name, my name or this email address without my prior written permission,” Dobbs replied to my initial outreach on March 10, 2020 using his email address from the University of Hawaii at Manoa.
A few hours later, I received more strident instructions from Dobbs, this time via his official email address at ipstresser[.]com.
“I will state again for absolute clarity, you are not authorized to post an article containing ipstresser.com, my name, my GitHub profile and/or my hawaii.edu email address,” Dobbs wrote, as if taking dictation from a lawyer who doesn’t understand how the media works.
When pressed for particulars on his business, Dobbs replied that the number of IPStresser customers was “privileged information,” and said he didn’t even advertise the service. When asked whether he was concerned that many of his competitors were by then serving jail time for operating similar booter services, Dobbs maintained that the way he’d set up the business insulated him from any liability.
“I have been aware of the recent law enforcement actions against other operators of stress testing services,” Dobbs explained. “I cannot speak to the actions of these other services, but we take proactive measures to prevent misuse of our service and we work with law enforcement agencies regarding any reported abuse of our service.”
What were those proactive measures? In a 2015 interview with ZDNet France, Dobbs asserted that he was immune from liability because his clients all had to submit a digital signature attesting that they wouldn’t use the site for illegal purposes.
“Our terms of use are a legal document that protects us, among other things, from certain legal consequences,” Dobbs told ZDNet. “Most other sites are satisfied with a simple checkbox, but we ask for a digital signature in order to imply real consent from our customers.”
Dobbs told KrebsOnSecurity his service didn’t generate much of a profit, but rather that he was motivated by “filling a legitimate need.”
“My reason for offering the service is to provide the ability to test network security measures before someone with malicious intent attacks said network and causes downtime,” he said. “Sure, some people see only the negatives, but there is a long list of companies I have worked with over the years who would say my service is a godsend and has helped them prevent tens of thousands of dollars in downtime resulting from a malicious attack.”
“I do not believe that providing such a service is illegal, assuming proper due diligence to prevent malicious use of the service, as is the case for IPstresser[.]com,” Dobbs continued. “Someone using such a service to conduct unauthorized testing is illegal in many countries, however, the legal liability is that of the user, not of the service provider.”
Dobbs’s profile on GitHub includes more of his ideas about his work, including a curious piece on “software engineering ethics.” In his January 2020 treatise “My Software Engineering Journey,” Dobbs laments that nothing in his formal education prepared him for the reality that a great deal of his work would be so tedious and repetitive (this tracks closely with a 2020 piece here called Career Choice Tip: Cybercrime is Mostly Boring).
“One area of software engineering that I think should be covered more in university classes is maintenance,” Dobbs wrote. “Projects are often worked on for at most a few months, and students do not experience the maintenance aspect of software engineering until they reach the workplace. Let’s face it, ongoing maintenance of a project is boring; there is nothing like the euphoria of completing a project you have been working on for months and releasing it to the world, but I would say that half of my professional career has been related to maintenance.”
Allison Nixon is chief research officer at the New York-based cybersecurity firm Unit 221B. Nixon is part of a small group of researchers who have been closely tracking the DDoS-for-hire industry for years, and she said Dobbs’s claim that what he’s doing is legal makes sense given that it took years for the government to recognize the size of the problem.
“These guys are arguing that their services are legal because for a long time nothing happened to them,” Nixon said. “It’s difficult to argue something is illegal if no one has ever been arrested for it before.”
Nixon says the government’s fight against the booter services — and by extension other types of cybercrimes — is hampered by a legal system that often takes years to cycle through cybercrime cases.
“With cybercrime, the cycle between the crime and investigation and arrest can often take a year or more, and that’s for a really fast case,” Nixon said. “If someone robbed a store, we’d expect a police response within a few minutes. If someone robs a bank’s website, there might be some indication of police activity within a year.”
Nixon praised the 2022 and 2018 booter takedown operations as “huge steps forward,” but added that “there need to be more of them, and faster.”
“This time lag is part of the reason it’s so difficult to shut down the pipeline of new talent going into cybercrime,” she said. “They think what they’re doing is legal because nothing has happened, and because of the amount of time it takes to shut these things down. And it’s really a big problem, where we see a lot of people becoming criminals on the basis that what they’re doing isn’t really illegal because the cops won’t do anything.”
In December 2020, Dobbs filed an application with the state of Hawaii to withdraw IP Stresser Inc. from its roster of active companies. But according to prosecutors, Dobbs would continue to operate his DDoS-for-hire site until at least November 2022.
Two months after our 2020 email interview, Dobbs would earn his second bachelor’s degree (in computer science; his resume says he earned a bachelor’s in civil engineering from Drexel University in 2013). The federal charges against Dobbs came just as he was preparing to enter his final semester toward a master’s degree in computer science at the University of Hawaii.
Nixon says she has a message for anyone involved in operating a DDoS-for-hire service.
“Unless you are verifying that the target owns the infrastructure you’re targeting, there is no legal way to operate a DDoS-for-hire service,” she said. “There is no Terms of Service you could put on the site that would somehow make it legal.”
And her message to the customers of those booter services? It’s a compelling one to ponder, particularly now that investigators in the United States, U.K. and elsewhere have started going after booter service customers.
“When a booter service claims they don’t share logs, they’re lying because logs are legal leverage for when the booter service operator gets arrested,” Nixon said. “And when they do, you’re going to be the first people they throw under the bus.”




I agree with his position. If someone murders someone with a kitchen knife is the knife manufacturer or distributor liable? No as they should not be.
This is more like if you’re advertising a service where you shoot people, but making your customers sign a disclaimer that they’re not shooting people illegally.
You worded that terribly, Robert. More like you’re not shooting anyone that didn’t give permission! Get it right.
The issue is that there are plenty of legitimate services that do load/stress testing. They are setup differently, providing things such as error reporting, analytics, integration with third-party services, etc. If he had the intention of providing a legitimate service, it would offer such features. The way it present the service, it is only useful for nefarious activities. It simply does not provide what is necessary to perform a load/stress testing service for business use. So, it is clear that is was meant to be used for criminal activities.
It is like saying that you are a moving company that can find and move all small valuables from any house to a nearby truck. You are not offering a real moving company, you are offering to steal from an house.
If IPStresser implemented real verification of consent, it would have been a commercial failure. It’s a farce by design.
That is the same arm-chair legal advice that got Dobbs into trouble.
“the legal liability is that of the user, not of the service provider.”
This is not true. It “feels” like it could be true, and that’s enough for many people rotting in prison.
The analogy of kitchen knifes and guns is not applicable.
Tools are different from Services. Github has plenty of tools available for download that can be used illegally, but are themselves legal.
Offering a Service, means you are doing the crime. Regardless of whether you got paid, had a customer sign a contract, or is sharing liability for the crime. It’s still a crime.
I guess the best analogy is pentesters. Pentesters do things which are generally illegal, and can only be legal if they are done at the request of and with the permission of the target. Pentesters are scrupulous about this stuff: they require detailed contracts with clearly defined scope of work, signatures from multiple senior people, emergency contacts to use if there is any question about whether or not their actions are appropriate, etc. If you do that, you’re golden. If you don’t, you’re probably running an illegal booter service.
Pentesters tend to also point out that you need to tell your cloud or infrastructure provider what you’re up to (as in hiring them to do). You can’t approve a thing that might jeopardize someone else’s servers, even if you’re renting some capacity. There’s probably no illegality there per se (depending on how far you go), but the vendor would just yeet you out as per their ToS.
Couldn’t disagree more, analogy is more like a missile system that let’s you input any coordinates you want. It’ll then strike that area for “security testing” reasons without even caring to verify the user should be using this system or that they own the property they’re “testing”.
Point being, you’re giving something powerful to someone that otherwise couldn’t obtain it and taking no precautions to ensure it’s used safely. You have to employ some serious mental gymnastics to think the way you do.
Sorry but this is a terrible analogy.
Knives have lots of everyday uses, including making food, eating food, carpentry, etc.
I challenge you to name a single non-criminal/non-hostile use of a booter service. (Especially taking into account what they ARE used for.)
Incorrect. Donna runs a service that stabs people, in order to check how good their stab vests are, without any validation that they own one, or are expecting the stabbing….
Hopefully a jury kicks this case out of court. He built a tool. Criminals used it against some sites, but it was also useful for network stress testing. He wasn’t hiding because he didn’t do anything wrong. This is a valuable service. I don’t think tech illiterate prosecutors shouldn’t be able to file dumb cases like this without getting a committee of CS professors to sign off on them.
I agree with your reasoning, but the courts don’t seem to since The Pirate Bay’s case.
Even if you were right, that Dobbs just ‘built a tool’ (you are not) – this tool worked by abusing hundreds and thousands of criminally hijacked internet devices. It were not his customers who hijacked and abused this devices – that was he by himself.
If you sell stolen guns to mafia gangsters, you might (by your really low moral standards) not be responsible for the murders commited with that guns – but you still are a thief and a fence.
Not sure why you assume the devices were hijacked. It is not clear from the article. If the devices were spun up (say in AWS) and what Dobbs created is a C2 infrastructure, AND the customers are paying for the compute and bandwidth they are sending (to test their infrastructure) this could be a legitimate business.
sending malicious packets across the internet is a violation of AWS ToS. so no, he couldnt use AWS or any other cloud to do his dirty packet “business”. legally anyway.
if anyone is looking for an analogy its this: you hire the mob to keep people from going into the 7-11 because you want people going to your store next door. the mob puts 5 big guys out in front of 7-11’s doors and the mobsters lock arms, preventing people from going in. ddos is literally mobsters. so dumb.
in this analogy, 7-11 is just a website. or a game server. or some random guy. ddos are often used together with ransom demands or hacking attempts. “hey ubisoft, pay us $10000 and we’ll stop ddosing your game servers”. if you are ubisoft, do you pay $10k ransom or spend $30k in hardware firewalls, $30k in internet upgrades, $30k in overtime for system engineers and $500k lost sales because your game servers are down ?
if i bought a game and the servers were down, i’d ask for a refund.
that said , there are legit stress testing of website services. but they get actual legal contracts, with actual legal notarized documents, lawyers, proof of ownership of said website, etc. not just “pay here” and “checkbox if you are only using this for legitimate use”
But if you’re Ubisoft, you’ve probably heard of Cloudflare…
You are correct I was good friends with John around 5 years ago and another administrator of the site. They use many high bandwidth overseas commercial servers with scripts written by him. Sold by reputable websites too they know what he’s using them for so he just has to pay a “premium” no hijacked devices were ever involved. That’s why he got off pretty much Scott free from this.
Hopefully the jury finds him guilty, and he gets a long sentence. He knew what he was doing, and he knew it was wrong.
Tools are different from Services.
Github has plenty of tools available for download that can be used illegally, but are themselves legal.
Offering a Service, means you are doing the crime. Regardless of whether you got paid, had a customer sign a contract, or is sharing liability for the crime. It’s still a crime.
If Dobbs only provided the tools, the Denial of Service would not come from IP space owned by Dobbs. Rather, he provides the “service”, of firing actual packets himself.
Funny you say this because there are CS professors urging law enforcement to prosecute these sites.
This Dobb’s guy sounds like a narcissistic criminal always jjustfing their actions
These things are new to me. But it is really helpful. The way you explained it. Really fun to read.
I’m amazed at the comments section. Brian, are you tracking how many russian trolls are posting here?
How would anyone justify running a booter service? The mere notion that he was using a stolen compute time by installing malware on people’s computers – that in itself – will make it highly illegal. What is that analogy with the tool use. These trolls are seriously dumb.
There are a lot of folks for whom booting is a pretty normal thing, for reasons described in the story. Not shocked at all that many of those folks would disagree with the messaging here.
As a beginner it’s somehow difficult for me to get the whole idea but you have shared an informative stuff, keep going on and thanks for sharing such valuable content. I like to visit this beneficial site again for further updates like this and because of that I can increase my reading skills and knowledge.
I’m really wondering what’s wrong with this self-appointed Judge Nixon. What sort of psychology trick are those? Of course what we are doing is illegal, do we care? No. Can we say it out loud? No. That would make us guilty in the first place. What is he even thinking? What a sill boy this guy is.
Some of those posting are openly defending Dobbs’ for having criminal intent. Do they actually not comprehend Dobb’s behavior as unethical and duplicitous, or are their beliefs entirely derived from dishonesty? I’m betting on the latter.
some anonymus guy payed in bitcoin and sign a letter its all legal.
find the error.
Will be an interesting case since he never hid his business, and has been available to be told to Stop or be arrested for years. Which is also frustrating because he would have been an easy target by LE – to stop the malicious activity. Does this make LE also liable for allowing the (crimes/apparent crimes) to continue? Would they allow bank robber to keep robbing banks for years to get more charges to press while also creating more victims?
Very frustrating to see these legal games played out at people/cattle/consumer’s expense.
Probably no liability for LE. White collar crime has always taken years to prosecute. As Nixon put it, cyber crime is naturally longer to go from crime, to investigation, to prosecution.
Can’t compare to violent, in-person crimes where local law enforcement has the ability to recognize and stop a crime in progress.
Nixon, famous for knowing what he was talking about in those hallways.
“Allison Nixon is chief research officer at the New York-based cybersecurity firm Unit 221B. [SHE] is part of a small group of researchers who have been closely tracking the DDoS-for-hire industry for years.”
It was a joke there Holiday Inn Express Law LLC.
Lawyer-in-training can’t take a joke, it’s a pity.
The statute of limitations is what governs this, and if he had stopped providing services years ago he could have gotten away with it. But instead he kept the service running. He kept launching attacks. And each attack has it’s own statute of limitation. So everything he’s done within statute limitations he can now be charged with.
Very frustrating to see people not get out when the getting’s good but greed makes everyone a fool in the end.
I develop website-performance software. I sometimes find myself needing to load-test my stuff. That is, I need to hit the site under test with a lot of requests really fast to find the bottlenecks.
But I would never use a public network third-party service, legit or not, to do those tests. That’s just rude … tragedy of the commons, etc.
I’ll either do it entirely inside my LAN, or I’ll test some servers I rent from a cloud company to load-test other servers I rent from the same cloud company in the same data center. And I’ll give the cloud company a heads-up.
This kind of service has no legitimate purpose.
DDoS attacks require a large amount of directed compute and network power to generate significant volumes of “garbage” traffic. It is not clear if Dobb’s infrastructure was “legal” (i.e. compute and network he paid for) or part of a botnet that used a vulnerability to assemble said botnet.
I think this is a major point of distinction when looking at the legality of the service i.e. are the customers paying for compute and data transfer, or is it stolen by a malicious botnet
@Dennis
The article didn’t say he built an illegal botnet. It might be DOS as opposed to DDOS.
You can’t expect that to work can you? How many thousands of machines do you have access to?
It’s fascinating to glimpse inside the mind of a criminal going through every legal rationalization, doing mental gymnastics, and who obviously has never spoken to a real lawyer.
Liability cannot be passed to users with a terms of service. Digital signatures don’t enhance legal protections if you’re not identity proofing (submit driver’s license photo, notarize, etc.). All it can do is SHARE liability and make it a criminal conspiracy that gets multiple indictments.
There are legal ways verify ownership of IPs on the internet. But it looks like his DDOS service does not require validation such as dropping keys/tokens onto the servers being claimed. Instead Dobbs was so worried about, “digital signatures in order to imply real consent from our customers”… he never bothered to get consent from the actual targets.
Are you still pretending to be a lawyer? Give it up already, it’s hilariously pretentious.
This guy’s denial service sounds like a tire-slashing service that claims to only serve people who legitimately need to slash test their own tires.
Brian, can you find a single case of someone legitimately using such a service?
Hasn’t your site been targeted many times? And don’t most people just hire CloudFlare to defend their domains?
How do tech startups and larger companies test their own websites against attacks (I bet they don’t but use CloudFlare and similar services to handle defense) or stress test to simulate a giant surge in popularity (maybe internal testing of reads and writes suffices along with configuring automatic increases in server power at AWS or other similar service)?
I can’t imagine any legit company hiring one of these DDOS stress-testing sites. I’d like an example if one exists.
A small business is an unlikely to need to plan for a gargantuan surge in popularity.
Hardly any small or medium business is like Ticketmaster trying to handle a hugely popular artist’s tour that goes on sale at midnight.
I can’t remember the last time I visited a website and it was unreachable because it couldn’t handle the traffic. I’ve seen events sellout but not the website become unreachable.
It’s probably easy to figure this out after law enforcement gathers evidence. Did the people paying for the service target their own company or someone else’s? Case closed.
I believe the right analogy for this is when you own a warehouse. You rented out the warehouse to crooks doing illegal activities. Are you responsible as owner if the warehouse was raided for illegal activities? Some laws in other countries says you are responsible. You as the owner should know what is going on in your property. Providing services for illegal activities should be held responsible as service provider.
Not a good analogy. This isn’t a tool sold or rented, this isn’t real estate either.
This was NOT a cloud hosting platform that just rented out general use virtual machines, where the tenant has a reasonable expectation of privacy, and therefore could be doing either criminal activity or legit business.
This was a SERVICE.
A better fitting analogy would be hiring a repo man to tow away a car that you claim you own. That’s a legit business, but you have to prove you have ownership (lien) on the property. You can’t just give a repo guy a crisp hundred and expect him to show up an steal a car for you.
Wow all these clever analogies! To me the tire slashing service analogy was the best, but now here’s even a better one for ya:
Programmers are basically a bunch of tools (if not toolbags) who use tools and services to provide paid programming services of building tools and creating services for other tools (if not toolbags) who are either too lazy, too stupid and/or too smart to themselves build the tools and services required in order for them to best serve their need to make sure that their own needs are always met: getting their tools deeply and properly serviced regularly and routinely by their paying customers, who are in fact also tools (if not toolbags) who themselves need to be served in one way or another…
“You now have one extra little fact to tuck away in the millions of little facts you have to memorize because so many of the programs you depend on are written by dicks and idiots.”
– P. Welch, ‘Programming Sucks’, “Still Drinking”, Peter Welch, USA, 14 April 2014, https://www.stilldrinking.org/programming-sucks, (accessed 19 January 2023).
“Bitch!”
– Jesse Pinkman (by Aaron Paul), “Breaking Bad”, s1e1-s5e16, AMC, 2008-2013. _Netflix_.
Thanks for continuing to do-so-well throwing ne’r-do-wells down the well, CyberHero Krebs! 😀
Looks like we should also go after the maintainers of Kali.
Kali is a suite of tools. They don’t run pen testing as a service.
Since booter service has its positive side claimed by some guys here, the government should establish an organisation to people like Dobbs to register their businesses and submit their logs to see if they are used illegally. It’s just like marijuana, which is both evil and angle.
Yeah, well that’s just like, your opinion, man.
Dude Alex man I hate to be the bearer of bad tidings but — and believe you me, this is coming from someone who Snoop Dogg ain’t got nothin on – if you think that booter sites and marijuana embody evil angels then it sounds to me like it may be time for you to just go ahead and put the pipe down and grab a snack and a nap…
I’m sure that you might probably in any likelihood be OK though maybe right?
Alex, bruh, I hate to have to be the bearer of bad tidings but – and mind you this is coming from somebody who, believe you me, even Snoop Dogg ain’t got nothin on – if you think that both booter sites and marijuana are ruled by evil angel principalities, then it sounds to me like perhaps now might be an ideal time to just go ahead and set the pipe down, walk away, and grab a snack and a nap…
But I’m fairly sure you might end up probably being OK maybe though, right…?
“Dobbs wrote, as if taking dictation from a lawyer who doesn’t understand how the media works.”
Rawr, I do love it.
Brian: Are you poking today’s ‘PTC problems’ causing a total NE rail shutdown? My thought is that its a temper tantrum by the groups that just lost a ton of money because of exchange shutdowns.
The analogy of this story, all these guy’s are all crooks. They all kenw what they were doing was on unauthorized activities.
“I have been aware of the recent law enforcement actions against other operators of stress testing services,” Dobbs explained. “I cannot speak to the actions of these other services, but we take proactive measures to prevent misuse of our service and we work with law enforcement agencies regarding any reported abuse of our service.”
On the other hand Gatrel was convicted on all three charges of violating the Computer Fraud and Abuse Act, including conspiracy to commit unauthorized impairment of a protected computer, conspiracy to commit wire fraud, and unauthorized impairment of a protected computer. He was sentenced to two years in prison.
If these dumb CISOs who never programmed don’t get what this genius did, how can these non-techie prosecutors ever understand this case?
Next generation is going to be much better given lot of kids already learn some programming before even the high school!
It’s not exactly hard to make a tool that would require the validation of ownership. Of course in today’s environment you usually need more than your own permission to DDoS your own web property. I agree that there would be use cases for this, but running stuff in such a shady manner makes me think that legality was never the goal.