Many readers are asking what they should be doing in response to Yahoo‘s disclosure Wednesday that a billion of its user accounts were hacked. Here are a few suggestions and pointers, fashioned into a good old Q&A format.

Image: eff.org
Q: Was my account hacked?
A: Experts I’ve spoken to believe Yahoo has about a billion active accounts. So, yes, it’s very likely your account’s password is compromised, and probably most of the other information you at one point entrusted to Yahoo. According to a statement from the company, the stolen user account information may have included names, email addresses, telephone numbers, dates of birth, hashed passwords (using MD5) and, in some cases, encrypted or unencrypted security questions and answers.”
Q: I’m not sure if I have a Yahoo account. How do I find out?
A: This is a surprisingly complex question. Thanks to the myriad mergers and business relationships that Yahoo has forged over the years, you may have a Yahoo account and not realize it. That’s because many accounts that are managed through Yahoo don’t actually end in “yahoo.com” (or yahoo. insert country code here).
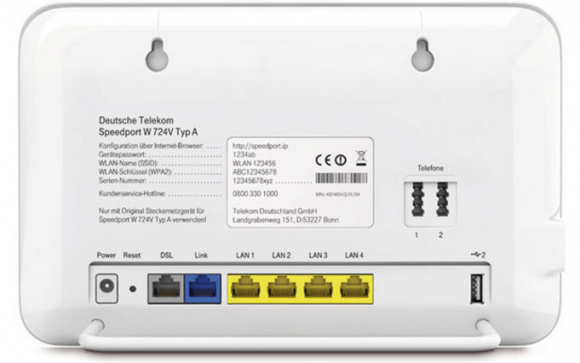
For example, British telecom giant BT uses Yahoo for their customer email, as did/do SBCGlobal, AT&T and BellSouth. Also, Verizon.net email addresses were serviced by Yahoo until AOL took over. Up in Canada, Rogers customers may also have Yahoo email addresses. I’m sure there are plenty of others I’m missing, but you get the point: Your Yahoo account may not include the word “yahoo” at all in the address.
Q: I created a Yahoo account a few years ago, but Yahoo says it doesn’t exist anymore. What’s going on here?
A: Yahoo has a policy of deactivating or deleting accounts that remain dormant for more than a year. If you haven’t touched your account in years, that’s probably why.
Q: Why would someone want to hack my email account? What could they do with it?
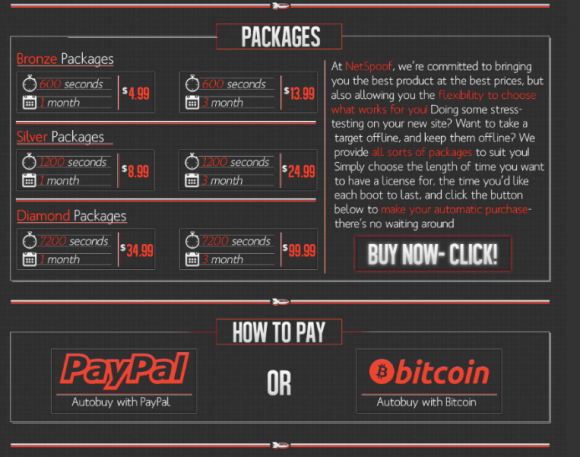
A: Spam, spam, and spam. Oh, and spam. They want to spam your contacts with malware and ads for dodgy products and services. Also, it gives the bad guys direct access to any account that you have signed up for using that email address. Why? Because if the crooks have access to your inbox, they can request a password reset link be sent to your inbox from any Web site you’ve signed up with at that email address.
For more detail on why these lowlifes might want control over your inbox and how they can monetize that access, see one of the most-read pieces on this blog — The Value of a Hacked Email Account. NB: Accounts that are hijacked for use in spam campaigns may also be suspended or deleted by Yahoo. Continue reading









 “The private sector and the Administration should collaborate on a roadmap for improving the security of digital networks, in particular by achieving robustness against denial-of-service, spoofing, and other attacks on users and the nation’s network infrastructure,” reads the first and foremost cybersecurity recommendation for President-elect Donald Trump. “The urgency of the situation demands that the next Administration move forward promptly on our recommendations, working closely with Congress and the private sector.”
“The private sector and the Administration should collaborate on a roadmap for improving the security of digital networks, in particular by achieving robustness against denial-of-service, spoofing, and other attacks on users and the nation’s network infrastructure,” reads the first and foremost cybersecurity recommendation for President-elect Donald Trump. “The urgency of the situation demands that the next Administration move forward promptly on our recommendations, working closely with Congress and the private sector.”