Adobe will pay just $1 million to settle a lawsuit filed by 15 state attorneys general over its huge 2013 data breach that exposed payment records on approximately 38 million people. In other news, the 39-year-old Dutchman responsible for coordinating an epic, weeks-long distributed denial-of-service attack against anti-spam provider Spamhaus in 2013 will avoid any jail time for his crimes thanks to a court ruling in Amsterdam this week.
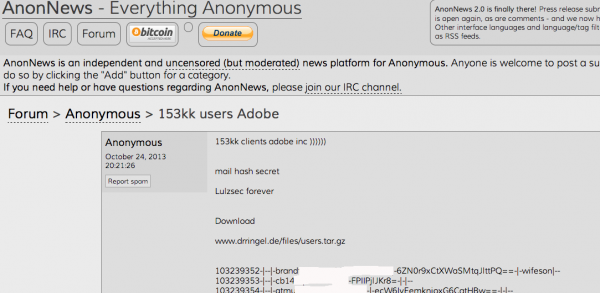
On Oct. 3, 2013, KrebsOnSecurity broke the story that Adobe had just suffered a breach in which hackers siphoned usernames, passwords and payment card data on 38 million customers. The intruders also made off with digital truckloads of source code for some of Adobe’s most valuable software properties — including Adobe Acrobat and Reader, Photoshop and ColdFusion.
On Monday, Nov. 11, North Carolina Attorney General Roy Cooper joined his counterparts in 14 other states in announcing a $1 million settlement with Adobe over the 2013 breach. According to Cooper, the hacked Adobe servers contained the personal information of approximately 552,000 residents of the participating 15 states. That works out to about $1.80 per victim across all 15 states.
According to a statement by Massachusetts Attorney General Maura Healey, “an investigation by the states revealed that in September 2013, Adobe received an alert that the hard drive for one of its application servers was nearing capacity. In responding to the alert, Adobe learned that an unauthorized attempt was being made to decrypt customer payment card numbers maintained on the server.”
“Adobe discovered that one or more unauthorized intruder(s) had compromised a public-facing web server and used it to access other servers on Adobe’s network, including areas where Adobe stored consumer data,” the statement from Healey’s office reads. “The intruder(s) ultimately stole consumer data from Adobe’s servers, including encrypted payment card numbers and expiration dates, names, addresses, telephone numbers, e-mail addresses, usernames (Adobe IDs), and passwords associated with the usernames.”
When I think of the Adobe breach I’m reminded of that scene out of the 1982 Spielberg horror classic “Poltergeist,” when Craig T. Nelson as “Steve Freeling” seizes the horrified neighborhood developer Mr. Teague by his coat collars and screams, “You son of a bitch! You moved the cemetery but you left the bodies, didn’t ya?! You left left the bodies and you only moved the headstones!! Why?!?!?! Whyyyyyyeeeiee??!?!?”

A scene from Poltergeist. Image: IMDB.
Likewise, Adobe had various storefronts for its various software products, but it eventually centralized many store operations. The main trouble was the company left copies of their customer records in multiple internal network locations that were no longer as protected as Adobe’s globally centralized storefront.
North Carolina’s Cooper said in a statement on the settlement that businesses and government must do more to protect consumer data. But if this settlement was meant as a deterrent to dissuade other companies from hosting customer payment data on public-facing Web servers, the fine might be more effective if it were more commensurate with the company’s size and the number of customers impacted.
As Digital Trends notes, such a breach under the new General Data Protection Regulation going into effect in 2018, would be quite a bit more costly. “Adobe could face fines of up to four percent of its annual global turnover,” wrote Jonathan Keane for DT. “Last we checked, Adobe’s previous quarterly earnings were $1.4 billion.”
Keane also notes that Adobe had previously settled a similar case in California where it settled for an undisclosed amount and $1.1 million in legal fees.
One interesting nugget tucked in at the end of the statement from the North Carolina AG’s office is this bit: More than 3,700 breaches impacting nearly 10 million North Carolinians have been reported since the state’s data breach notification law took effect in 2005, including 677 breaches reported so far in 2016. According to the United States Census Bureau, there were just over 10 million residents in North Carolina as of July 2015. Continue reading






![TitaniumStresser[dot]net, as it appeared in 2014.](https://krebsonsecurity.com/wp-content/uploads/2016/11/titaniumstresser-580x689.png)