Analysis of open source information on the cybercriminal infrastructure likely used to siphon 80 million Social Security numbers and other sensitive data from health insurance giant Anthem suggests the attackers may have first gained a foothold in April 2014, nine months before the company says it discovered the intrusion.
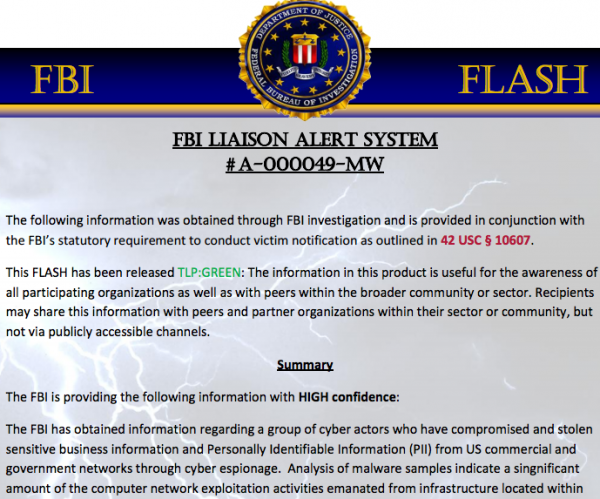
The Wall Street Journal reported last week that security experts involved in the ongoing forensics investigation into the breach say the servers and attack tools used in the attack on Anthem bear the hallmark of a state-sponsored Chinese cyber espionage group known by a number of names, including “Deep Panda,” “Axiom,” Group 72,” and the “Shell_Crew,” to name but a few.
Deep Panda is the name given to this group by security firm CrowdStrike. In November 2014, Crowdstrike published a snapshot of a graphic showing the malware and malicious Internet servers used in what security experts at PriceWaterhouseCoopers dubbed the ScanBox Framework, a suite of tools that have been used to launch a number of cyber espionage attacks.
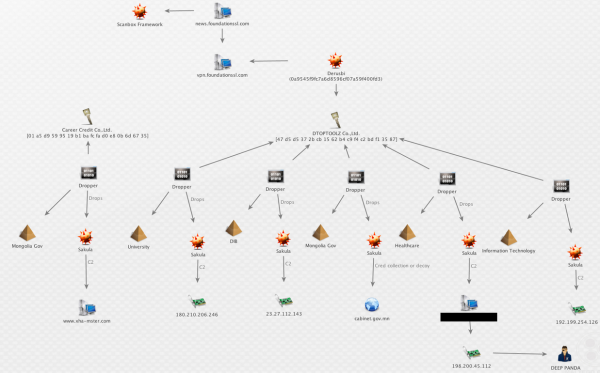
A Maltego transform published by CrowdStrike. The graphic is intended to illustrate some tools and Internet servers thought to be closely tied to a Chinese cyber espionage group that CrowdStrike calls “Deep Panda.”
Crowdstrike’s snapshot (produced with the visualization tool Maltego) lists many of the tools the company has come to associate with activity linked to Deep Panda, including a password stealing Trojan horse program called Derusbi, and an Internet address — 198[dot]200[dot]45[dot]112.
CrowdStrike’s image curiously redacts the resource tied to that Internet address (note the black box in the image above), but a variety of open source records indicate that this particular address was until very recently the home for a very interesting domain: we11point.com. The third and fourth characters in that domain name are the numeral one, but it appears that whoever registered the domain was attempting to make it look like “Wellpoint,” the former name of Anthem before the company changed its corporate name in late 2014.
We11point[dot]com was registered on April 21, 2014 to a bulk domain registration service in China. Eight minutes later, someone changed the site’s registration records to remove any trace of a connection to China.
Intrigued by the fake Wellpoint domains, Rich Barger, chief information officer for Arlington, Va. security firm ThreatConnect Inc., dug deeper into so-called “passive DNS” records — historic records of the mapping between numeric Internet addresses and domain names. That digging revealed a host of other subdomains tied to the suspicious we11point[dot]com site. In the process, Barger discovered that these subdomains — including myhr.we11point[dot]com, and hrsolutions.we11point[dot]com – mimicked components of Wellpoint’s actual network as it existed in April 2014.
“We were able to verify that the evil we11point infrastructure is constructed to masquerade as legitimate Wellpoint infrastructure,” Barger said.
Another fishy subdomain that Barger discovered was extcitrix.we11point[dot]com. The “citrix” portion of that domain likely refers to Citrix, a software tool that many large corporations commonly use to allow employees remote access to internal networks over a virtual private network (VPN).
Interestingly, that extcitrix.we11point[dot]com domain, first put online on April 22, 2014, was referenced in a malware scan from a malicious file that someone uploaded to malware scanning service Virustotal.com. According to the writeup on that malware, it appears to be a backdoor program masquerading as Citrix VPN software. The malware is digitally signed with a certificate issued to an organization called DTOPTOOLZ Co. According to CrowdStrike and other security firms, that digital signature is the calling card of the Deep Panda Chinese espionage group. Continue reading