Last week, hacktivists posted online 400 GB worth of internal emails, documents and other data stolen from Hacking Team, an Italian security firm that has earned the ire of privacy and civil liberties groups for selling spy software to governments worldwide. New analysis of the leaked Hacking Team emails suggests that in 2013 the company used techniques perfected by spammers to hijack Internet address space from a spammer-friendly Internet service provider in a bid to regain control over a spy network it apparently had set up for the Italian National Military Police.
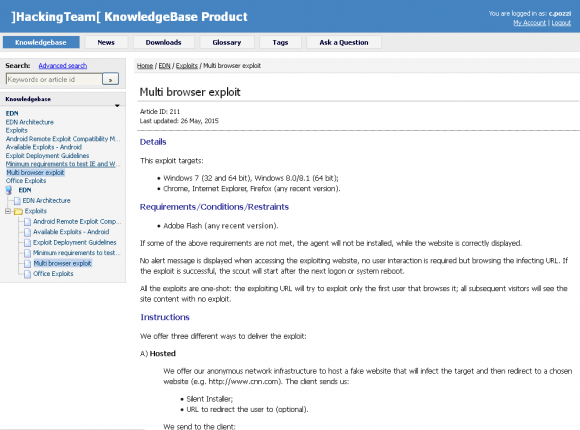
Hacking Team is in the business of selling exploits that allow clients to secretly deploy spyware on targeted systems. In just the past week since the Hacking Team data was leaked, for example, Adobe has fixed two previously undocumented zero-day vulnerabilities in its Flash Player software that Hacking Team had sold to clients as spyware delivery mechanisms.
The spyware deployed by Hacking Team’s exploits are essentially remote-access Trojan horse programs designed to hoover up stored data, recorded communications, keystrokes, etc. from infected devices, giving the malware’s operator full control over victim machines.
Systems infested with Hacking Team’s malware are configured to periodically check for new instructions or updates at a server controlled by Hacking Team and/or its clients. This type of setup is very similar to the way spammers and cybercriminals design “botnets,” huge collections of hacked PCs that are harvested for valuable data and used for a variety of nefarious purposes.
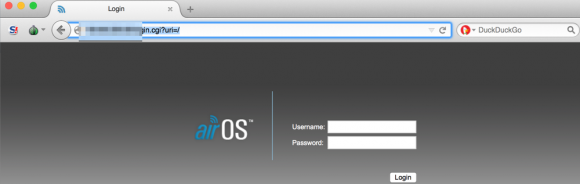
No surprise, then, that Hacking Team placed its control servers in this case at an ISP that was heavily favored by spammers. Leaked Hacking Team emails show that in 2013, the company set up a malware control server for the Special Operations Group of the Italian National Military Police — also known as the “Carabinieri” — an entity focused on investigating organized crime and terrorism. One or both of these organizations chose to position that control at Santrex, a notorious Web hosting provider that at the time served as a virtual haven for spammers and malicious software downloads.
But that decision backfired. As I documented in October 2013, Santrex unexpectedly shut down all of its servers, following a series of internal network issues and extensive downtime. Santrex made that decision after several months of incessant attacks, hacks and equipment failures at its facilities caused massive and costly problems for the ISP and its customers. The company’s connectivity problems essentially made it impossible for either Hacking Team or the Carabinieri to maintain control over the machines infected with the spyware.
According to research published Sunday by OpenDNS Security Labs, around that same time the Carabinieri and Hacking Team cooked up a plan to regain control over the Internet addresses abandoned by Santrex. The plan centered around a traffic redirection technique known as “BGP hijacking,” which involves one ISP fraudulently “announcing” to the rest of the world’s ISPs that it is in fact the rightful custodian of a dormant range of Internet addresses that it doesn’t actually have the right to control.
IP address hijacking is hardly a new phenomenon. Spammers sometimes hijack Internet address ranges that go unused for periods of time (see this story from 2014 and this piece I wrote in 2008 for The Washington Post for examples of spammers hijacking Internet space). Dormant or “unannounced” address ranges are ripe for abuse partly because of the way the global routing system works: Miscreants can “announce” to the rest of the Internet that their hosting facilities are the authorized location for given Internet addresses. If nothing or nobody objects to the change, the Internet address ranges fall into the hands of the hijacker. Continue reading