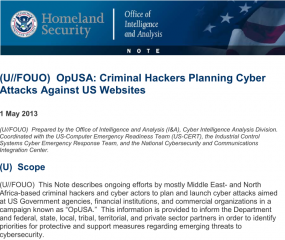
A 24-year-old Algerian man arrested in Thailand earlier this year on suspicion of co-developing and selling the infamous SpyEye banking trojan was extradited this week to the United States, where he faces criminal charges for allegedly hijacking bank accounts at more than 200 financial institutions.
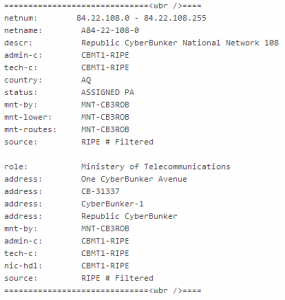
Hamza Bendelladj, who authorities say used the nickname “Bx1” online, is accused of operating a botnet powered by SpyEye, a complex banking trojan that he also allegedly sold and helped develop. Bendelladj was arraigned on May 2, 2013 in Atlanta, where he is accused of leasing a server from a local Internet company to help manage his SpyEye botnet.
A redacted copy of the indictment (PDF) against Bendelladj was unsealed this week; the document says Bendelladj developed and customized components of SpyEye that helped customers steal online banking credentials and funds from specific banks.
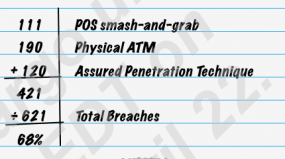
The government alleges that as Bx1, Bendelladj was an active member of darkode.com, an underground fraud forum that I’ve covered in numerous posts on this blog. Bx1’s core focus in the community was selling “web injects” — custom add-ons for SpyEye that can change the appearance and function of banking Web sites as displayed in a victim’s Web browser. More specifically, Bx1 sold a type of web inject called an automated transfer system or ATS; this type of malware component was used extensively with SpyEye — and with its close cousin the ZeuS Trojan — to silently and invisibly automate the execution of bank transfers just seconds after the owners of infected PCs logged into their bank accounts.
“Zeus/SpyEYE/Ice9 ATS for Sale,” Bx1 announced in a post on darkode.com thread dated Jan. 16, 2012:
“Hey all. I’m selling private ATS’s. Working and Tested.
We got IT / DE / AT / UK / US / CO / NL / FR / AU
Contact me for bank.
can develop bank ATS from your choice.”
The government alleges that Bx1/Bendelladj made millions selling SpyEye, SpyEye components and harvesting financial data from victims in his own SpyEye botnet. But Bx1 customers and associates on darkode.com expressed strong doubts about this claim, noting that someone who was making that kind of money would not blab or be as open about his activities as Bx1 apparently was.
In my previous post on Bx1, I noted that he reached out to me on several occasions to brag about his botnet and to share information about his illicit activities. In one case, he even related a story about breaking into the networks of a rival ATS/web inject developer named Symlink. Bx1 said he told Symlink to expect a visit from the local cops if he didn’t pay Bx1 to keep his mouth shut. It’s not clear whether that story is true or if Symlink ever paid the money; in any case, Symlink was arrested on cybercrime charges in Oct. 2012 by authorities in Moldova.
The redacted portions of the government indictment of Bendelladj are all references to Bx1’s partner — the author of the SpyEye Trojan and a malware developer known in the underground alternatively as “Gribodemon” and “Harderman.” In a conference call with reporters today, U.S. Attorney Sally Quillian Yates said the real name of the principal author of SpyEye was redacted from the indictment because he had not yet been arrested.








![After migrating the data from Exposed.su to Exposed.re, the curator added [Swatted] notations.](https://krebsonsecurity.com/wp-content/uploads/2013/04/Fotor0417131216-600x450.jpg)