The Federal Bureau of Investigation is advising travelers to avoid updating software while using hotel or other public Internet connections, warning that malicious actors are targeting travelers abroad through pop-up windows while they are establishing an Internet connection in their hotel rooms.
From the FBI’s advisory:
“Recently, there have been instances of travelers’ laptops being infected with malicious software while using hotel Internet connections. In these instances, the traveler was attempting to set up the hotel room Internet connection and was presented with a pop-up window notifying the user to update a widely used software product. If the user clicked to accept and install the update, malicious software was installed on the laptop. The pop-up window appeared to be offering a routine update to a legitimate software product for which updates are frequently available.”
The warning is a good opportunity to revisit some wireless safety tips I’ve doled out over the years. Avoid updating software while you’re using networks that are untrusted and public, whether they are wired or wireless. This generally means Wi-Fi networks like those available in hotels and coffee shops, and even wired connections at hotels. The only exception I make to this rule is when I have a device that is tethered to the 3G connection on a mobile phone. But even this can be dicey, because many laptops and mobile devices will switch over to available Wi-Fi networks in the event that the 3G signal dies.
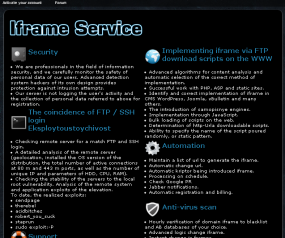
 There are a number of free attack tools that can be used to spoof software update prompts, and these are especially effective against users on small local networks. Bear in mind that false update prompts don’t have to involve pop-ups. I’ve written at least two blog posts about EvilGrade, a toolkit that makes it simple for attackers to install malicious software by exploiting weaknesses in the auto-update feature of many popular software titles. The deviousness of this tool is that it can be used to hijack the legitimate updaters built into software already installed on your computer.
There are a number of free attack tools that can be used to spoof software update prompts, and these are especially effective against users on small local networks. Bear in mind that false update prompts don’t have to involve pop-ups. I’ve written at least two blog posts about EvilGrade, a toolkit that makes it simple for attackers to install malicious software by exploiting weaknesses in the auto-update feature of many popular software titles. The deviousness of this tool is that it can be used to hijack the legitimate updaters built into software already installed on your computer.
If you must update while on the road, make sure that you initiate the update process. Avoid clicking pop-up prompts or anything that looks like it was launched from an auto-updater. When in doubt, always update from the vendor’s Web site. Most importantly — and Rule #1 of Krebs’s 3 Basic Rules for Online Safety covers this nicely — “if you didn’t go looking for it, don’t install it!” Also, using an update tracker, such as Secunia‘s Personal Software Inspector or File Hippo‘s Update Checker, can help you stay on top of the latest security patches for widely-used software, and make it easier for you to plan your software updates ahead of time.