The man arrested in Armenia last week for allegedly operating the massive “Bredolab” botnet — a network of some 30 million hacked Microsoft Windows PCs that were rented out to cyber crooks — appears to have generated much of his clientele as an affiliate of Spamit.com, the global spamming operation whose members are blamed for sending a majority of the world’s pharmaceutical spam.
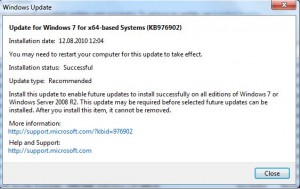
 Armenian authorities arrested 27-year-old Georg Avanesov on suspicion of being the curator of Bredolab, a botnet that infected an estimated 3 million PCs per month through virus-laden e-mails and booby-trapped Web sites. The arrest resulted from a joint investigation between Armenian police and cyber sleuths in the Netherlands, whose ISPs were home to at least 143 servers used to direct the botnet’s activities. In tandem with the arrest and the unplugging of those servers, Dutch service providers began redirecting local Internet users to a disinfection and cleanup page if their PCs showed signs of Bredolab infections.
Armenian authorities arrested 27-year-old Georg Avanesov on suspicion of being the curator of Bredolab, a botnet that infected an estimated 3 million PCs per month through virus-laden e-mails and booby-trapped Web sites. The arrest resulted from a joint investigation between Armenian police and cyber sleuths in the Netherlands, whose ISPs were home to at least 143 servers used to direct the botnet’s activities. In tandem with the arrest and the unplugging of those servers, Dutch service providers began redirecting local Internet users to a disinfection and cleanup page if their PCs showed signs of Bredolab infections.
Investigators allege that Avanesov made up to US$139,000 each month renting the botnet to criminals who used it for sending spam and for installing password-stealing malicious software. Avanesov, who is thought to have made millions over a career spanning more than a decade, was arrested after hopping a flight from Moscow to his home in Yerevan, Armenia’s capital.
Pim Takkenberg, team leader for the Netherlands Police Agency’s High Tech Crime Unit, said Avanesov frequently used the hacker aliases “padonaque” and “Atata,” and for many years used the e-mail address “i.am@padonaque.info.” The domain padonaque.info has long been associated with a variety of malicious software families, and the malware that once called home to it reflects the varied clientele that investigators say Avanesov attracted over the years.
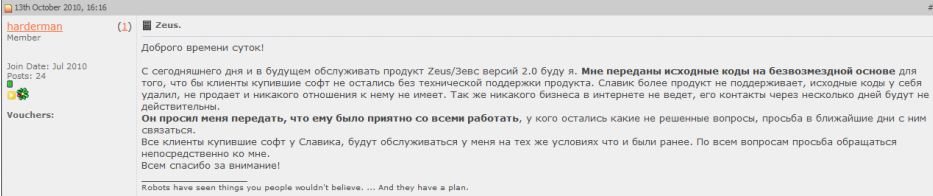
According to information obtained by KrebsOnSecurity, that e-mail address and Atata nickname were used to register at least two affiliate accounts at spamit.com. With online pharmacy sales generating him less than $2,000 each month over the last several years, Atata wasn’t pulling in anywhere near as much as the top earners in the program, some of whom earned six figures monthly promoting counterfeit pills via spam. But Takkenberg and others say it is likely that Atata used Spamit as a place to sign up new customers who were interesting in renting his Bredolab botnet to promote their pharmacy sites.
“The main thing he did was build this botnet — mainly using a lot of hacked Web sites,” Takkenberg said. “Then he sold parts of that botnet to other clients of his, who could upload their own malware loaders, FTP [password] grabbers, whatever they wanted.”