Egyptian citizens calling for besieged President Hosni Mubarak to step down may have been cut off from using the Web, but spammers have been busy cutting the government off from its own Internet address space: Earlier this month, junk e-mail artists hijacked a large swath of Internet addresses assigned to Mubarak’s wife.
 According to Spamhaus.org, well known spammers commandeered a chunk of more than 4,000 IP addresses that were assigned years ago to Suzanne Mubarak and the Suzanne Mubarak Science Exploration Center. Spamhaus reports that those addresses have been used recently to promote a variety of dodgy Web businesses, and that the hijacked block is under the control of an organization that has ties to alleged spammer Michael Lindsay and iMedia Networks. iMedia did not respond to requests for comment.
According to Spamhaus.org, well known spammers commandeered a chunk of more than 4,000 IP addresses that were assigned years ago to Suzanne Mubarak and the Suzanne Mubarak Science Exploration Center. Spamhaus reports that those addresses have been used recently to promote a variety of dodgy Web businesses, and that the hijacked block is under the control of an organization that has ties to alleged spammer Michael Lindsay and iMedia Networks. iMedia did not respond to requests for comment.
The high profile land grab is the latest example of how spammers are becoming more brazen in their quest for non-blacklisted Internet address space from which to send spam, said Rod Rasmussen, president and chief technology officer of Internet Identity.
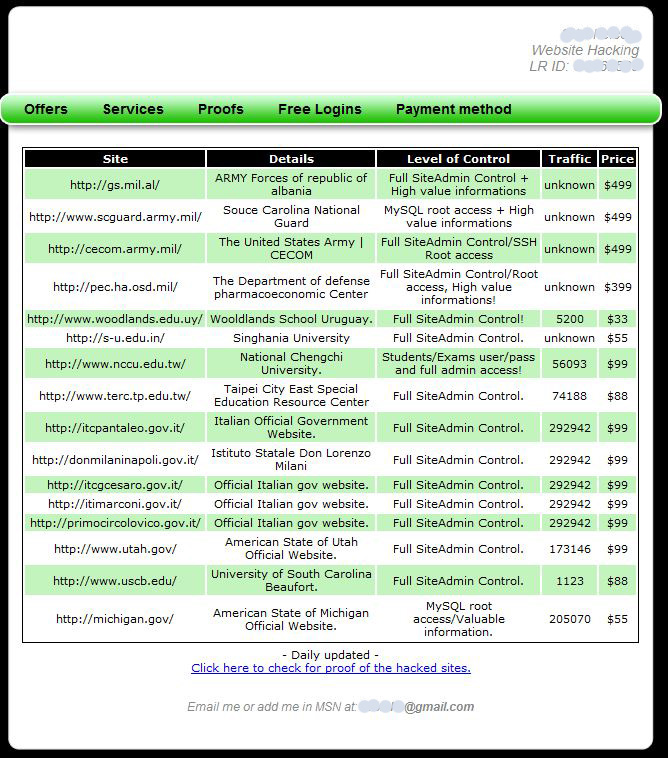
Rasmussen said Internet address space hijackers tend to target chunks of addresses assigned to governments and defense contractors, because those allocations are less likely to be reported missing, and very few of them are blocked by anti-spam tools.
“The spammers doing this look for chunks of [Internet] space that are dormant, but most of all blocks of IP addresses that are whitelisted,” by anti-spam groups, Rasmussen said. “Their spam gets through anti-spam filters nicely after that, or least until the hijacking is detected.”
Sometimes, the scammers are able to hijack IP space by snatching up expired domain names that were used to register the addresses years earlier. The attackers then send an e-mail from that domain to the regional Internet registry that assigned the block of IP, requesting whatever changes they need to assume control over the addresses.In other cases, spammers use forged letters and bogus corporate fronts to impersonate the rightful owner of the addresses.
Another chunk of addresses that Spamhaus found were recently hijacked by spammers — 255 IPs originally assigned in 1994 to the now defunct Claremont Technology Group — appears to have been stolen sometime after the organization let its domain claretech.com lapse. That domain now redirects to Falls Church, Va. based government contractor Computer Sciences Corp (CSC), which acquired Claremont in 1998.
Rasmussen believes we are likely to see a spike in this type hijacking activity as global supply of unassigned IPv4 addresses continues to dwindle and unallocated blocks become more valuable. Experts disagree on exactly when the pool of IPv4 addresses will be drained: Some says as mid- to late 2011, and others claim it’s only a few more days.