Online dating giant eHarmony has begun urging many users to change their passwords, after being alerted by KrebsOnSecurity.com to a potential security breach of customer information. The individual responsible for all the ruckus is an Argentinian hacker who recently claimed responsibility for a similar breach at competing e-dating site PlentyOfFish.com.
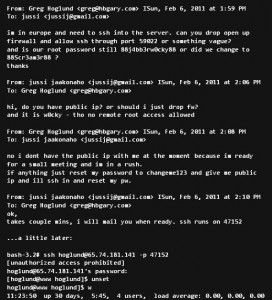
Late last year, Chris “Ch” Russo, a self-styled “security researcher” from Buenos Aires, told me he’d discovered vulnerabilities in eHarmony’s network that allowed him to view passwords and other information on tens of thousands of eHarmony users.
Russo first alerted me to his findings in late December, right after he said he first began contacting site administrators about the flaw. At the time, I sent messages to several of the administrative eHarmony e-mail addresses whose passwords Russo said he was able to discover, although I received no response. Russo told me shortly thereafter that he’d hit a brick wall in his research, and I let the matter drop after that.
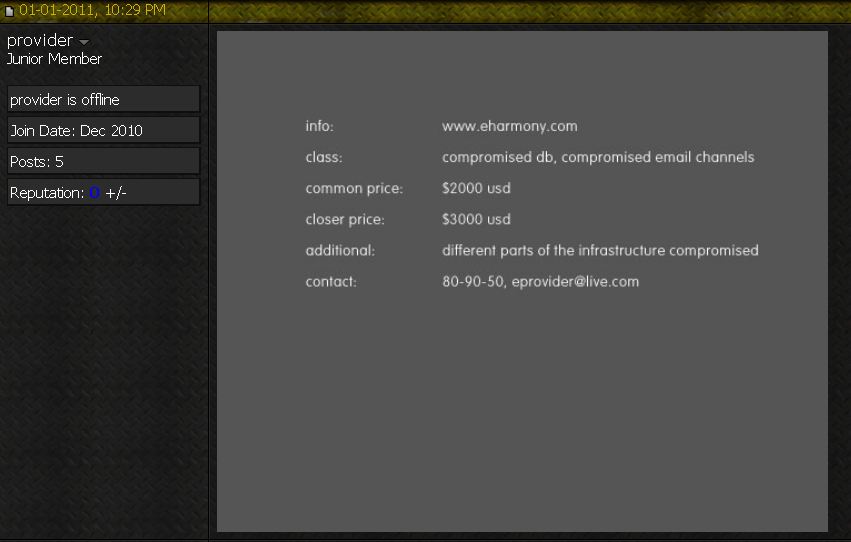
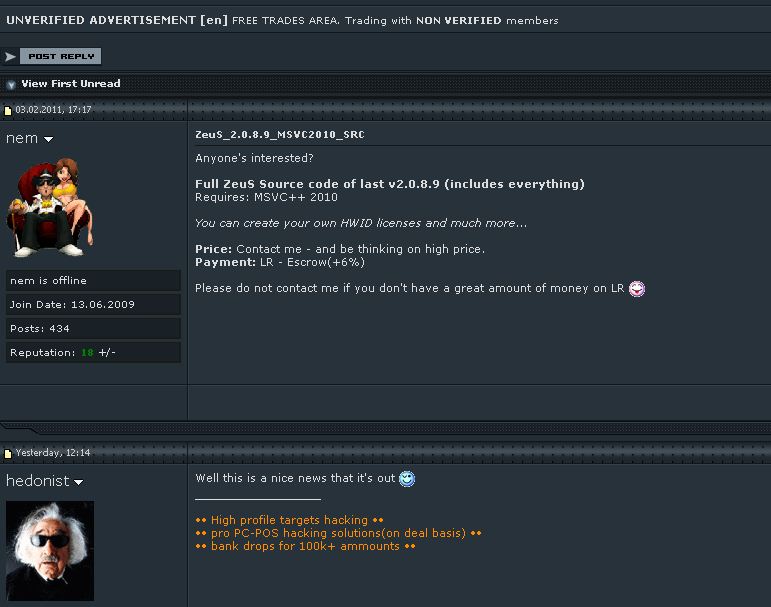
Then, about a week ago, I heard from a source in the hacker underground who remarked, “You know eHarmony got hacked, too, right?” I quickly checked several fraud forums that I monitor, and soon found a curious solicitation from a user at Carder.biz, an online forum that enables cyber crooks to engage in a variety of shady transactions, from buying and selling hacked data and accounts to the purchase and/or renting of criminal services, such as botnet hosting, exploit packs, purloined credit card and consumer identity data. The seller, using the nickname “Provider” and pictured in the screen shot below, purported to have access to “different parts of the [eHarmony] infrastructure,” including a compromised database and e-mail channels. Provider was offering this information for prices ranging from $2,000 to $3,000.
When I contacted Russo about this development, he initially said that he never did anything with his findings, although later in the conversation he conceded it was possible that an associate of his who also was privy to details of the discovery may have acted on his own. At that point, I contacted eHarmony’s corporate offices and shared a copy of the screen shot and information I’d obtained from Russo.
Joseph Essas, chief technology officer at eHarmony, said Russo found a SQL injection vulnerability in one of the third party libraries that eHarmony has been using for content management on the company’s advice site – advice.eharmony.com. Essas said there were no signs that accounts at its main user site — eharmony.com — were affected.