Much digital ink has been spilled in this blog detailing the activities of so-called “money mules,” willing or unwitting individuals here in the United States who are lured into laundering money for international organized cyber crime gangs. The subject almost always generates fierce debate among readers about whether these mules should be prosecuted, and the debate usually hinges on whether the mules knew that they were contributing to a crime.
Of course, ignorance of the law is no excuse, and this blog entry is in no way meant to defend the mules. But I did want to shed more light on the efforts that some mule recruitment gangs take to help potential mules believe they are in fact working for a legitimate company.
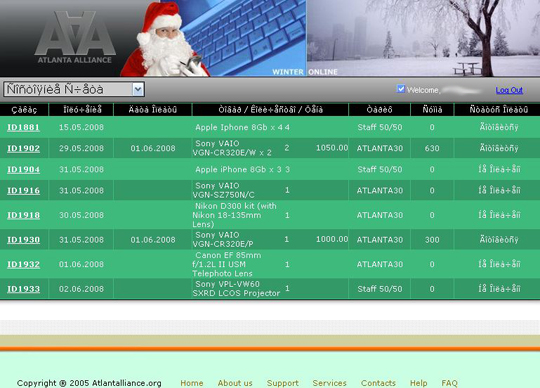
Take, for example, the efforts of what we’ll call the “Back Office,” mule recruitment gang — so named because the Web sites used to recruit and manage these folks almost always include the term “backoffice”. Potential Back Office mules are recruited via e-mail, with a message stating that the employer found the recipient’s resume on a job search site and would he or she be interested in working as a financial agent in an international finance company?
Those who respond are directed to create an account at a Back Office site, and from there the new recruits are processed through a series of interviews. According to conversations with multiple mules recruited by the Back Office gang, the process normally starts with a lengthy telephone interview, wherein the recruit is asked about his or her work history, ethics and attitudes.
Following the verbal interview, mules are asked to complete a lengthy questionnaire that asks roughly three dozen questions, including many that one might expect to find in a legitimate interview for a professional position.
“How do you evaluate success?”
“What classes or seminars have you taken on your own during the last three years to advance your careers and personal growth?