Most Internet users know to watch for the telltale signs of a traditional phishing attack: An e-mail that asks you to click on a link and enter your e-mail or banking credentials at the resulting Web site. But a new phishing concept that exploits user inattention and trust in browser tabs is likely to fool even the most security-conscious Web surfers.
 As Mozilla Firefox creative lead Aza Raskin describes it, the attack is as elegant as it is simple: A user has multiple tabs open, and surfs to a site that uses special javacript code to silently alter the contents of a tabbed page along with the information displayed on the tab itself, so that when the user switches back to that tab it appears to be the login page for a site the user normally visits.
As Mozilla Firefox creative lead Aza Raskin describes it, the attack is as elegant as it is simple: A user has multiple tabs open, and surfs to a site that uses special javacript code to silently alter the contents of a tabbed page along with the information displayed on the tab itself, so that when the user switches back to that tab it appears to be the login page for a site the user normally visits.
Consider the following scenario: Bob has six or seven tabs open, and one of the sites he has open (but not the tab currently being viewed) contains a script that waits for a few minutes or hours, and then quietly changes both the content of the page and the icon and descriptor in the tab itself so that it appears to be the login page for Gmail.
In this attack, the phisher need not even change the Web address displayed in the browser’s navigation toolbar. Rather, this particular phishing attack takes advantage of user trust and inattention to detail, or what Raskin calls “the perceived immutability of tabs.” Then, as the user scans their many open tabs, the favicon and title act as a strong visual cue, and the user will most likely simply think they left a Gmail tab open.
“When they click back to the fake Gmail tab, they’ll see the standard Gmail login page, assume they’ve been logged out, and provide their credentials to log in,” Raskin explained. “After the user has enter they have entered their login information and sent it back your server, you redirect them to Gmail. Because they were never logged out in the first place, it will appear as if the login was successful.”
Raskin includes a proof-of-concept at his site, which is sort of creepy when you let it run. In fact, at least once while composing this blog post in Firefox I went to click on the tab that had my Gmail inbox open, only to discover I’d accidentally clicked on Raskin’s page, which had morphed into the fake Gmail site in the interim.
It’s important to keep in mind that this attack could be used against any site, not just Gmail. Also, Raskin includes a few suggestions about how this attack could be made far sneakier — such as taking advantage of CSS history attacks.
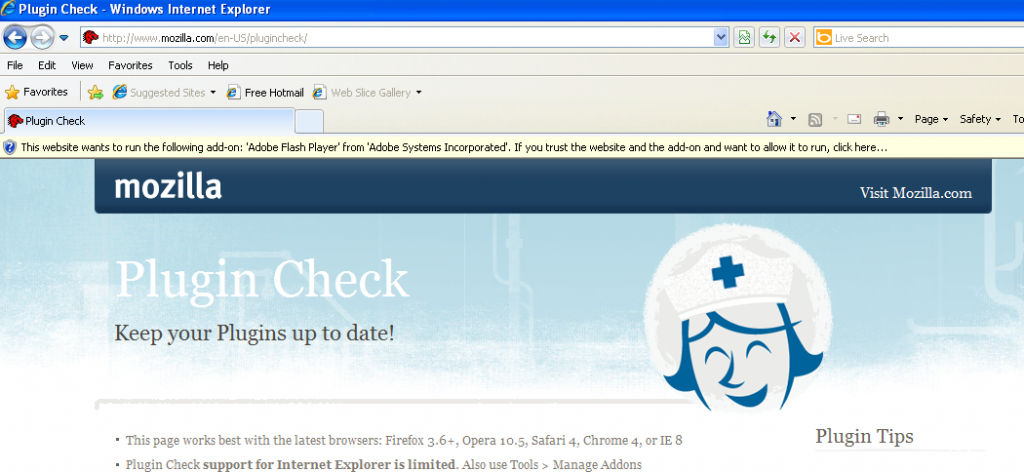
Of course, if you are browsing with the excellent “Noscript” add-on and this is a site you have not allowed to run javascript, the proof-of-concept won’t work until you allow javascript on the page. It did not work completely against the Safari browser on my Mac (no favicon), and the test page failed completely against Google Chrome. [Update: As several readers have correctly pointed out, this attack does in fact work against Chrome, although it doesn’t seem to change the favicon in Chrome tabs].
I’m left wondering what this new form of phishing will be called if it is ever adopted by the bad guys. Tabnabbing? Tabgrabbing? See if you can coin a better phrase in the comments below.
Update, May 25, 7:55 p.m. ET: Researcher Aviv Raff has posted an interesting proof-of-concept of his own that shows how this attack can work against Firefox even when users have the Noscript add-on installed and in full paranoid mode. Raff crafted his page, which is a mock up of this blog post, to morph into an image of the Gmail login page, and it will reload every 20 seconds but will only change to the sample phish page if you move to another tab with your mouse, or after 10 reloads (in case you moved with the keyboard). So it will change only after 3 minutes or so, unless you move to another tab with your mouse.
“I was trying to find a way to work around the javascript need for the [proof-of-concept],” Raff said in an instant message. “First I was able to do this without knowing if the user moved to a new tab. Now I can almost be sure of that.”
Update, May 27, 11:41 p.m. ET: For Firefox users with the Noscript plugin, there is an update to the program that can block these types of tabnabbing attacks.
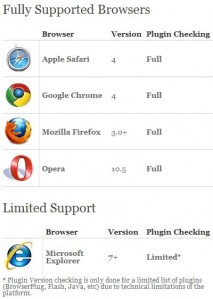
![]() In its largest patch push so far this year, Microsoft today released 10 security updates to fix at least 34 security vulnerabilities in its Windows operating system and software designed to run on top of it. Separately, Apple has shipped another version of Safari for both Mac and Windows PCs that plugs some four dozen security holes in the Web browser.
In its largest patch push so far this year, Microsoft today released 10 security updates to fix at least 34 security vulnerabilities in its Windows operating system and software designed to run on top of it. Separately, Apple has shipped another version of Safari for both Mac and Windows PCs that plugs some four dozen security holes in the Web browser. Microsoft notes that Office XP users may not be able to install one of the needed updates; Rather, Redmond is releasing what it calls a “shim,” or essentially and point-and-click “FixIt” tool that apparently does the job. If you use Office XP, go ahead and click the “FixIt” icon at this link when you’re done installing the rest of the updates.
Microsoft notes that Office XP users may not be able to install one of the needed updates; Rather, Redmond is releasing what it calls a “shim,” or essentially and point-and-click “FixIt” tool that apparently does the job. If you use Office XP, go ahead and click the “FixIt” icon at this link when you’re done installing the rest of the updates.