On Dec. 18, 2013, KrebsOnSecurity broke the news that U.S. retail giant Target was battling a wide-ranging computer intrusion that compromised more than 40 million customer payment cards over the previous month. The malware used in the Target breach included the text string “Rescator,” which also was the handle chosen by the cybercriminal who was selling all of the cards stolen from Target customers. Ten years later, KrebsOnSecurity has uncovered new clues about the real-life identity of Rescator.

Rescator, advertising a new batch of cards stolen in a 2014 breach at P.F. Chang’s.
Shortly after breaking the Target story, KrebsOnSecurity reported that Rescator appeared to be a hacker from Ukraine. Efforts to confirm my reporting with that individual ended when they declined to answer questions, and after I declined to accept a bribe of $10,000 not to run my story.
That reporting was based on clues from an early Russian cybercrime forum in which a hacker named Rescator — using the same profile image that Rescator was known to use on other forums — claimed to have originally been known as “Helkern,” the nickname chosen by the administrator of a cybercrime forum called Darklife.
KrebsOnSecurity began revisiting the research into Rescator’s real-life identity in 2018, after the U.S. Department of Justice unsealed an indictment that named a different Ukrainian man as Helkern.
It may be helpful to first recap why Rescator is thought to be so closely tied to the Target breach. For starters, the text string “Rescator” was found in some of the malware used in the Target breach. Investigators would later determine that a variant of the malware used in the Target breach was used in 2014 to steal 56 million payment cards from Home Depot customers. And once again, cards stolen in the Home Depot breach were sold exclusively at Rescator’s shops.
On Nov. 25, 2013, two days before Target said the breach officially began, Rescator could be seen in instant messages hiring another forum member to verify 400,000 payment cards that Rescator claimed were freshly stolen.
By the first week of December 2013, Rescator’s online store — rescator[.]la — was selling more than six million payment card records stolen from Target customers. Prior to the Target breach, Rescator had mostly sold much smaller batches of stolen card and identity data, and the website allowed cybercriminals to automate the sending of fraudulent wire transfers to money mules based in Lviv, Ukraine.
Finally, there is some honor among thieves, and in the marketplace for stolen payment card data it is considered poor form to advertise a batch of cards as “yours” if you are merely reselling cards sold to you by a third-party card vendor or thief. When serious stolen payment card shop vendors wish to communicate that a batch of cards is uniquely their handiwork or that of their immediate crew, they refer to it as “our base.” And Rescator was quite clear in his advertisements that these millions of cards were obtained firsthand.
FLASHBACK
The new clues about Rescator’s identity came into focus when I revisited the reporting around an April 2013 story here that identified the author of the OSX Flashback Trojan, an early Mac malware strain that quickly spread to more than 650,000 Mac computers worldwide in 2012.
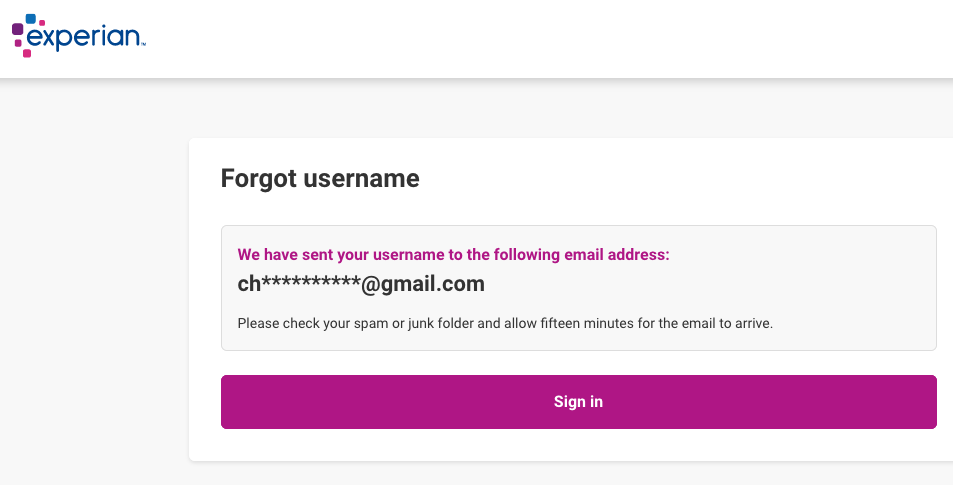
That story about the Flashback author was possible because a source had obtained a Web browser authentication cookie for a founding member of a Russian cybercrime forum called BlackSEO. Anyone in possession of that cookie could then browse the invite-only BlackSEO forum and read the user’s private messages without having to log in.
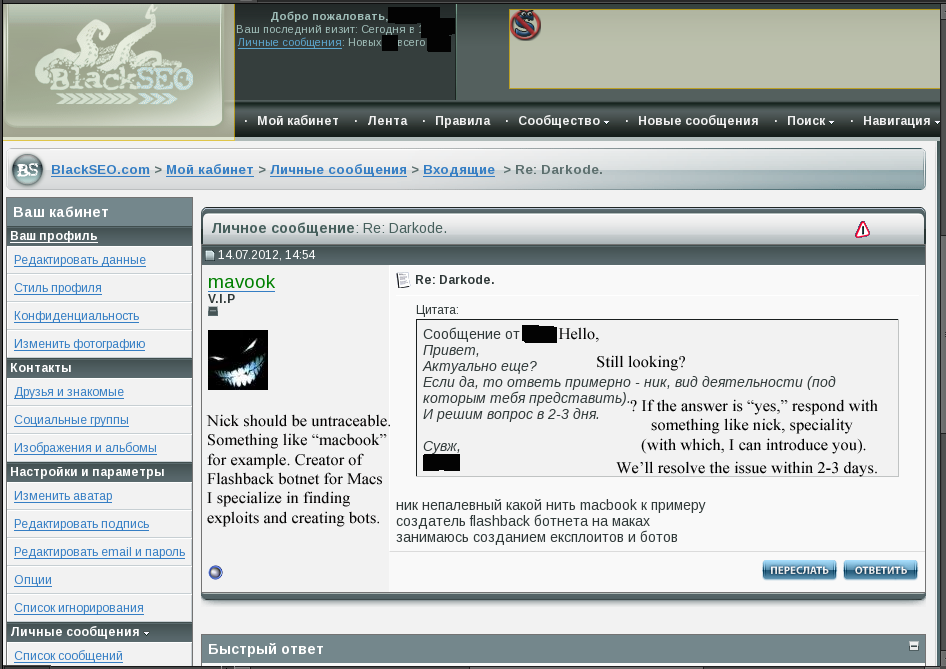
BlackSEO.com VIP member “Mavook” tells forum admin Ika in a private message that he is the Flashback author.
The legitimate owner of that BlackSEO user cookie went by the nickname Ika, and Ika’s private messages on the forum showed he was close friends with the Flashback author. At the time, Ika also was the administrator of Pustota[.]pw — a closely-guarded Russian forum that counted among its members some of the world’s most successful and established spammers and malware writers.
For many years, Ika held a key position at one of Russia’s largest Internet service providers, and his (mostly glowing) reputation as a reliable provider of web hosting to the Russian cybercrime community gave him an encyclopedic knowledge about nearly every major player in that scene at the time.
The story on the Flashback author featured redacted screenshots that were taken from Ika’s BlackSEO account (see image above). The day after that story ran, Ika posted a farewell address to his mates, expressing shock and bewilderment over the apparent compromise of his BlackSEO account.
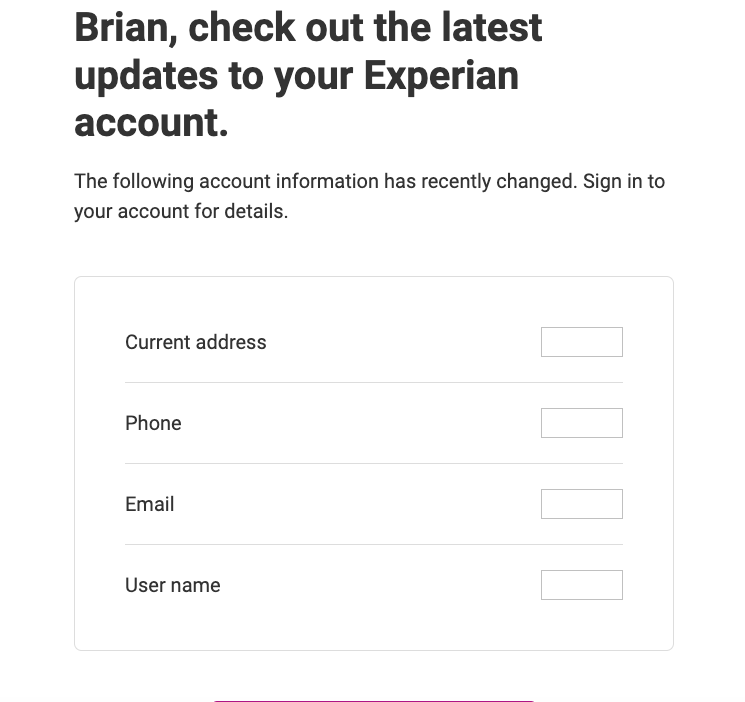
In a lengthy post on April 4, 2013 titled “I DON’T UNDERSTAND ANYTHING,” Ika told Pustota forum members he was so spooked by recent events that he was closing the forum and quitting the cybercrime business entirely. Ika recounted how the Flashback story had come the same week that rival cybercriminals tried to “dox” him (their dox named the wrong individual, but included some of Ika’s more guarded identities).
“It’s no secret that karma farted in my direction,” Ika said at the beginning of his post. Unbeknownst to Ika at the time, his Pustota forum also had been completely hacked that week, and a copy of its database shared with this author.
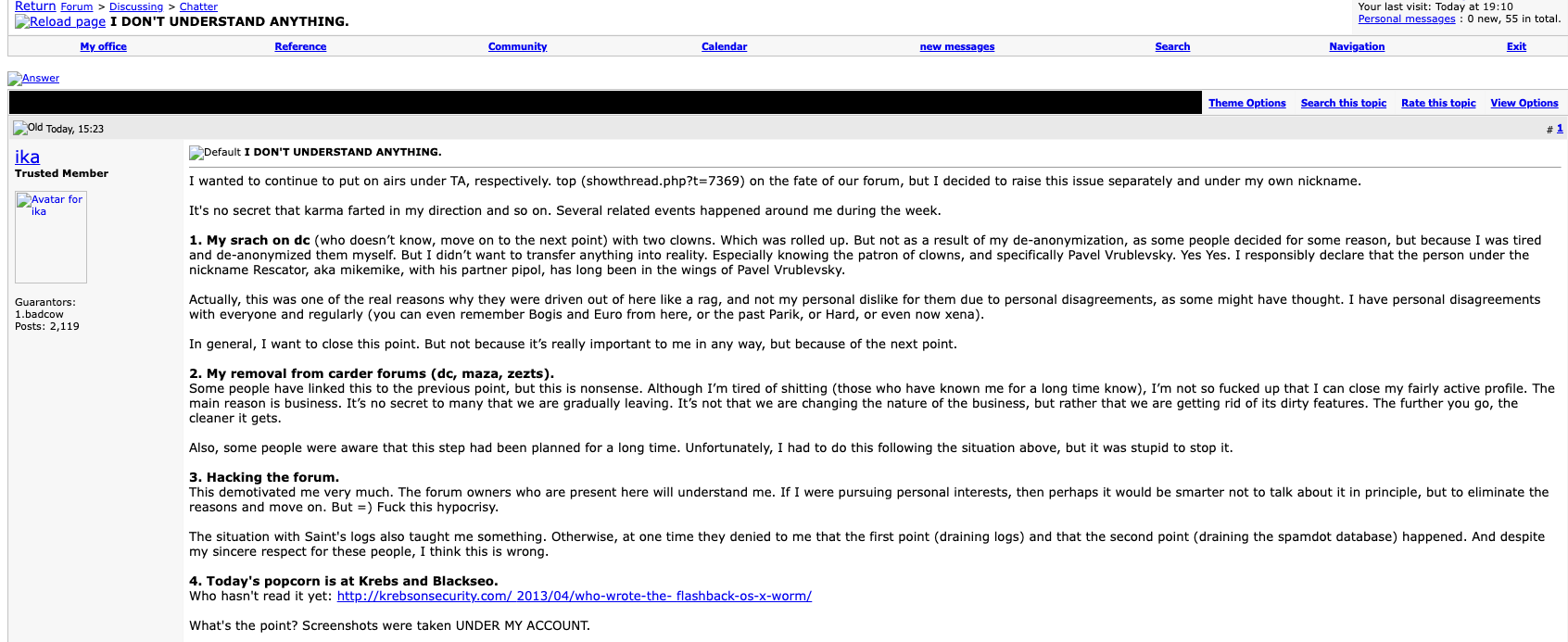
A Google translated version of the farewell post from Ika, the administrator of Pustota, a Russian language cybercrime forum focused on botnets and spam. Click to enlarge.
Ika said the two individuals who tried to dox him did so on an even more guarded Russian language forum — DirectConnection[.]ws, perhaps the most exclusive Russian cybercrime community ever created. New applicants of this forum had to pay a non-refundable deposit, and receive vouches by three established cybercriminals already on the forum. Even if one managed to steal (or guess) a user’s DirectConnection password, the login page could not be reached unless the visitor also possessed a special browser certificate that the forum administrator gave only to approved members.
In no uncertain terms, Ika declared that Rescator went by the nickname MikeMike on DirectConnection:
“I did not want to bring any of this to real life. Especially since I knew the patron of the clowns – specifically Pavel Vrublevsky. Yes, I do state with confidence that the man with the nickname Rescator a.k.a. MikeMike with his partner Pipol have been Pavel Vrublevsky’s puppets for a long time.”
Pavel Vrublevsky is a convicted cybercriminal who became famous as the CEO of the Russian e-payments company ChronoPay, which specialized in facilitating online payments for a variety of “high-risk” businesses, including gambling, pirated Mp3 files, rogue antivirus software and “male enhancement” pills.
As detailed in my 2014 book Spam Nation, Vrublevsky not-so-secretly ran a pharmacy affiliate spam program called Rx-Promotion, which paid spammers and virus writers to blast out tens of billions of junk emails advertising generic Viagra and controlled pharmaceuticals like pain relief medications. Much of my reporting on Vrublevsky’s cybercrime empire came from several years worth of internal ChronoPay emails and documents that were leaked online in 2010 and 2011.

Pavel Vrublevsky’s former Facebook profile photo.







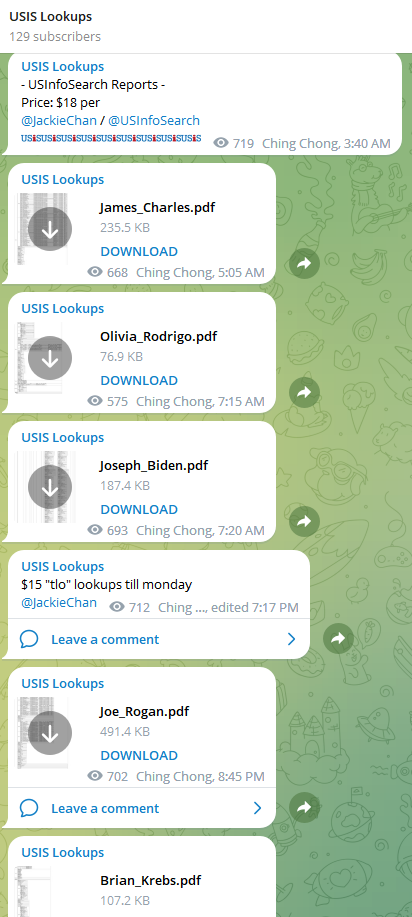 Since at least February 2023, a service advertised on Telegram called USiSLookups has operated an automated bot that allows anyone to look up the SSN or background report on virtually any American. For prices ranging from $8 to $40 and payable via virtual currency, the bot will return detailed consumer background reports automatically in just a few moments.
Since at least February 2023, a service advertised on Telegram called USiSLookups has operated an automated bot that allows anyone to look up the SSN or background report on virtually any American. For prices ranging from $8 to $40 and payable via virtual currency, the bot will return detailed consumer background reports automatically in just a few moments.