You may have heard that today’s phone fraudsters like to use caller ID spoofing services to make their scam calls seem more believable. But you probably didn’t know that these fraudsters also can use caller ID spoofing to trick your bank into giving up information about recent transactions on your account — data that can then be abused to make their phone scams more believable and expose you to additional forms of identity theft.
Last week, KrebsOnSecurity told the harrowing tale of a reader (a security expert, no less) who tried to turn the tables on his telephonic tormentors and failed spectacularly. In that episode, the people impersonating his bank not only spoofed the bank’s real phone number, but they were also pretending to be him on a separate call at the same time with his bank.
This foiled his efforts to make sure it was really his bank that called him, because he called his bank with another phone and the bank confirmed they currently were in a separate call with him discussing fraud on his account (however, the other call was the fraudster pretending to be him).
Shortly after that story ran, I heard from another reader — we’ll call him “Jim” since he didn’t want his real name used for this story — whose wife was the target of a similar scam, albeit with an important twist: The scammers were armed with information about a number of her recent financial transactions, which he claims they got from the bank’s own automated phone system just by spoofing her phone number.
“When they originally called my wife, there were no fraudulent transactions on her account, but they were able to specify the last three transactions she had made, which combined with the caller-ID had mistakenly earned her trust,” Jim explained. “After we figured out what was going on, we were left asking ourselves how the crooks had obtained her last three transactions without breaking into her account online. As it turned out, calling the phone number on the back of the credit card from the phone number linked with the card provided the most recent transactions without providing any form of authentication.”
Jim said he was so aghast at this realization that he called the same number from his phone and tried accessing his account, which is also at Citi but wholly separate from his spouse’s. Sure enough, he said, as long as he was calling from the number on file for his account, the automated system let him review recent transactions without any further authentication.
“I confirmed on my separate Citi card that they often (but not quite always) were providing the transaction details,” Jim said. “I was appalled that Citi would do that. So, it seemed the crooks would spoof caller ID when calling Citibank, as well as when calling the target/victim.”
The incident Jim described happened in late January 2020, and Citi may have changed its procedures since then. But in a phone interview with KrebsOnSecurity earlier this week, Jim made a call to Citi’s automated system from his mobile phone on file with the bank, and I could hear Citi’s systems asking him to enter the last four digits of his credit card number before he could review recent transactions.
The request for the last four of the customer’s credit card number was consistent with my own testing, which relied on a caller ID spoofing service advertised in the cybercrime underground and aimed at a Citi account controlled by this author.
In one test, the spoofed call let KrebsOnSecurity hear recent transaction data — where and when the transaction was made, and how much was spent — after providing the automated system the last four digits of the account’s credit card number. In another test, the automated system asked for the account holder’s full Social Security number.
Citi declined to discuss specific actions it takes to detect and prevent fraud. But in a written statement provided to this author it said the company continuously monitors and analyzes threats and looks for opportunities to strengthen its controls.
“We see regular attempts by fraudsters to gain access to information and we are constantly monitoring for emerging threats and taking preventive action for our clients’ protection,” the statement reads. “For inbound calls to call centers, we continue to adapt and implement detection capabilities to identify suspicious or spoofed phone numbers. We also encourage clients to install and use our mobile app and sign up for push notifications and alerts in the mobile app.”
PREGNANT PAUSES AND BULGING EMAIL BOMBS
Jim said the fraudster who called his wife clearly already knew her mailing and email addresses, her mobile number and the fact that her card was an American Airlines-branded Citi card. The caller said there had been a series of suspicious transactions, and proceeded to read back details of several recent transactions to verify if those were purchases she’d authorized.
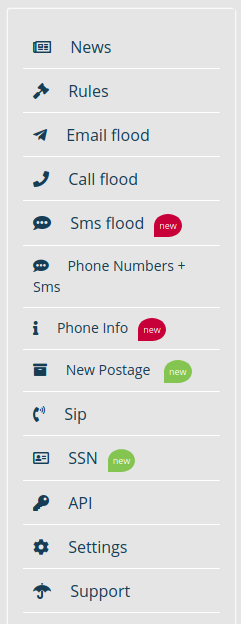
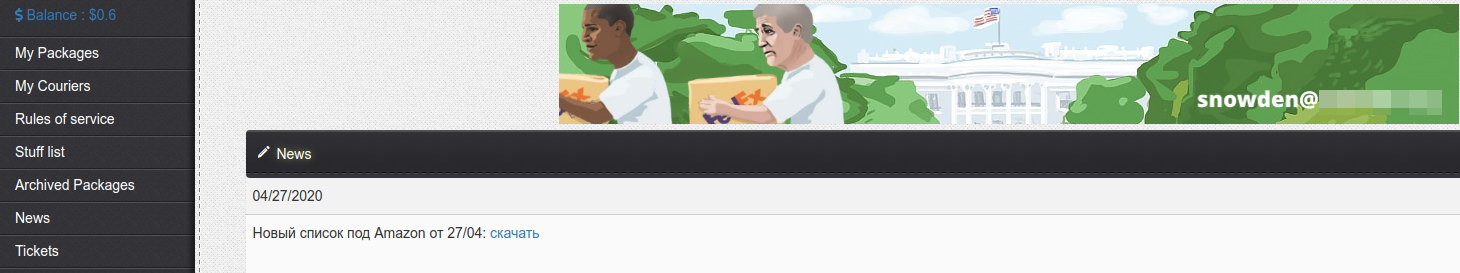
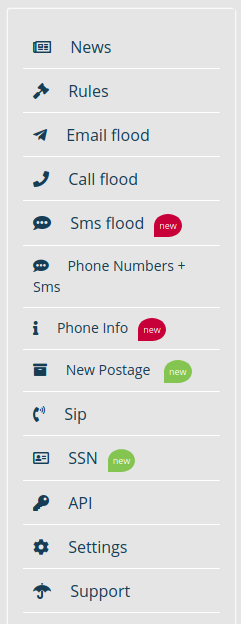
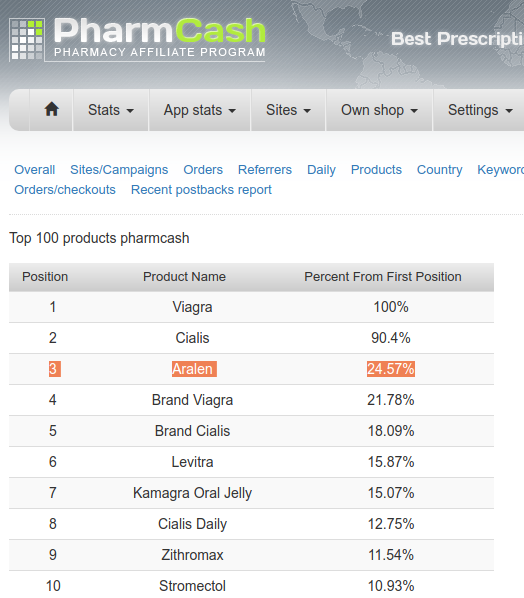
A list of services offered by one of several underground stores that sell caller ID spoofing and email bombing services.
Jim’s wife quickly logged on to her Citi account and saw that the amounts, dates and places of the transactions referenced by the caller indeed corresponded to recent legitimate transactions. But she didn’t see any signs of unauthorized charges.
After verifying the recent legitimate transactions with the caller, the person on the phone asked for her security word. When she provided it, there was a long hold before the caller came back and said she’d provided the wrong answer.
When she corrected herself and provided a different security word, there was another long pause before the caller said the second answer she provided was correct. At that point, the caller said Citi would be sending her a new card and that it had prevented several phony charges from even posting to her account.
She didn’t understand until later that the pauses were points at which the fraudsters had to put her on hold to relay her answers in their own call posing as her to Citi’s customer service department.
Not long after Jim’s spouse hung up with the caller, her inbox quickly began filling up with hundreds of automated messages from various websites trying to confirm an email newsletter subscription she’d supposedly requested.
As the recipient of several of these “email bombing” attacks, I can verify that crooks often will use services offered in the cybercrime underground to flood a target’s inbox with these junk newsletter subscriptions shortly after committing fraud in the target’s name when they wish to bury an email notification from a target’s bank.
‘OVERPAYMENT REIMBURSEMENT’
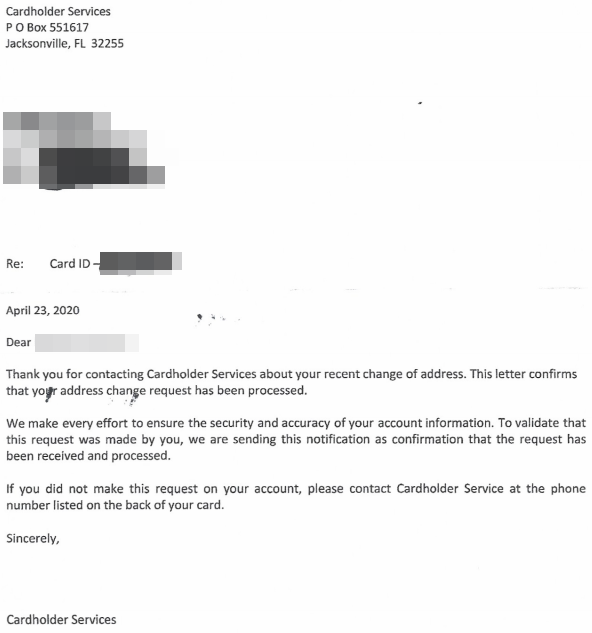
In the case of Jim’s wife, the inbox flood backfired, and only made her more suspicious about the true nature of the recent phone call. So she called the number on the back of her Citi card and was told that she had indeed just called Citi and requested what’s known as an “overpayment reimbursement.” The couple have long had their credit cards on auto-payment, and the most recent payment was especially high — nearly $4,000 — thanks to a flurry of Christmas present purchases for friends and family.
In an overpayment reimbursement, a customer can request that the bank refund any amount paid toward a previous bill that exceeds the minimum required monthly payment. Doing so causes any back-due interest on that unpaid amount to accrue to the account as well.
In this case, the caller posing as Jim’s wife requested an overpayment reimbursement to the tune of just under $4,000. It’s not clear how or where the fraudsters intended this payment to be sent, but for whatever reason Citi ended up saying they would cut a physical check and mail it to the address on file. Probably not what the fraudsters wanted, although since then Jim and his wife say they have been on alert for anyone suspicious lurking near their mailbox.
“The person we spoke with at Citi’s fraud department kept insisting that yes, it was my wife that called because the call came from her mobile number,” Jim said. “The Citi employee was alarmed because she didn’t understand the whole notion of caller ID spoofing. And we both found it kind of disturbing that someone in fraud at such a major bank didn’t even understand that such a thing was possible.” Continue reading →
 May marks the third month in a row that Microsoft has pushed out fixes for more than 110 security flaws in its operating system and related software. At least 16 of the bugs are labeled “Critical,” meaning ne’er-do-wells can exploit them to install malware or seize remote control over vulnerable systems with little or no help from users.
May marks the third month in a row that Microsoft has pushed out fixes for more than 110 security flaws in its operating system and related software. At least 16 of the bugs are labeled “Critical,” meaning ne’er-do-wells can exploit them to install malware or seize remote control over vulnerable systems with little or no help from users.



 Canton, Ohio-based Diebold [
Canton, Ohio-based Diebold [