A new phone-based phishing scam that spoofs Apple Inc. is likely to fool quite a few people. It starts with an automated call that display’s Apple’s logo, address and real phone number, warning about a data breach at the company. The scary part is that if the recipient is an iPhone user who then requests a call back from Apple’s legitimate customer support Web page, the fake call gets indexed in the iPhone’s “recent calls” list as a previous call from the legitimate Apple Support line.
Jody Westby is the CEO of Global Cyber Risk LLC, a security consulting firm based in Washington, D.C. Westby said earlier today she received an automated call on her iPhone warning that multiple servers containing Apple user IDs had been compromised (the same scammers had called her at 4:34 p.m. the day before, but she didn’t answer that call). The message said she needed to call a 1-866 number before doing anything else with her phone.
Here’s what her iPhone displayed about the identity of the caller when they first tried her number at 4:34 p.m. on Jan. 2, 2019:
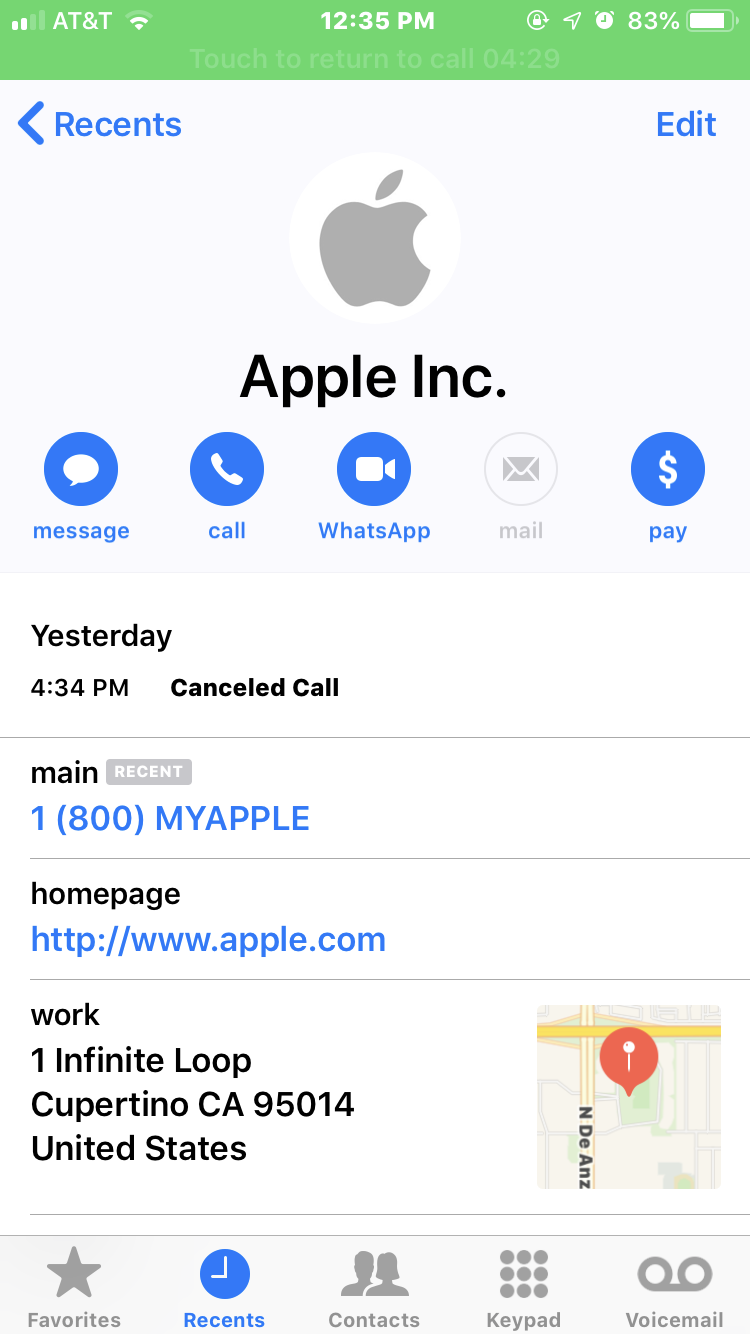
What Westby’s iPhone displayed as the scam caller’s identity. Note that it lists the correct Apple phone number, street address and Web address (minus the https://).
Note in the above screen shot that it lists Apple’s actual street address, their real customer support number, and the real Apple.com domain (albeit without the “s” at the end of “http://”). The same caller ID information showed up when she answered the scammers’ call this morning.
Westby said she immediately went to the Apple.com support page (https://www.support.apple.com) and requested to have a customer support person call her back. The page displayed a “case ID” to track her inquiry, and just a few minutes later someone from the real Apple Inc. called her and referenced that case ID number at the start of the call.
Westby said the Apple agent told her that Apple had not contacted her, that the call was almost certainly a scam, and that Apple would never do that — all of which she already knew. But when Westby looked at her iPhone’s recent calls list, she saw the legitimate call from Apple had been lumped together with the scam call that spoofed Apple:
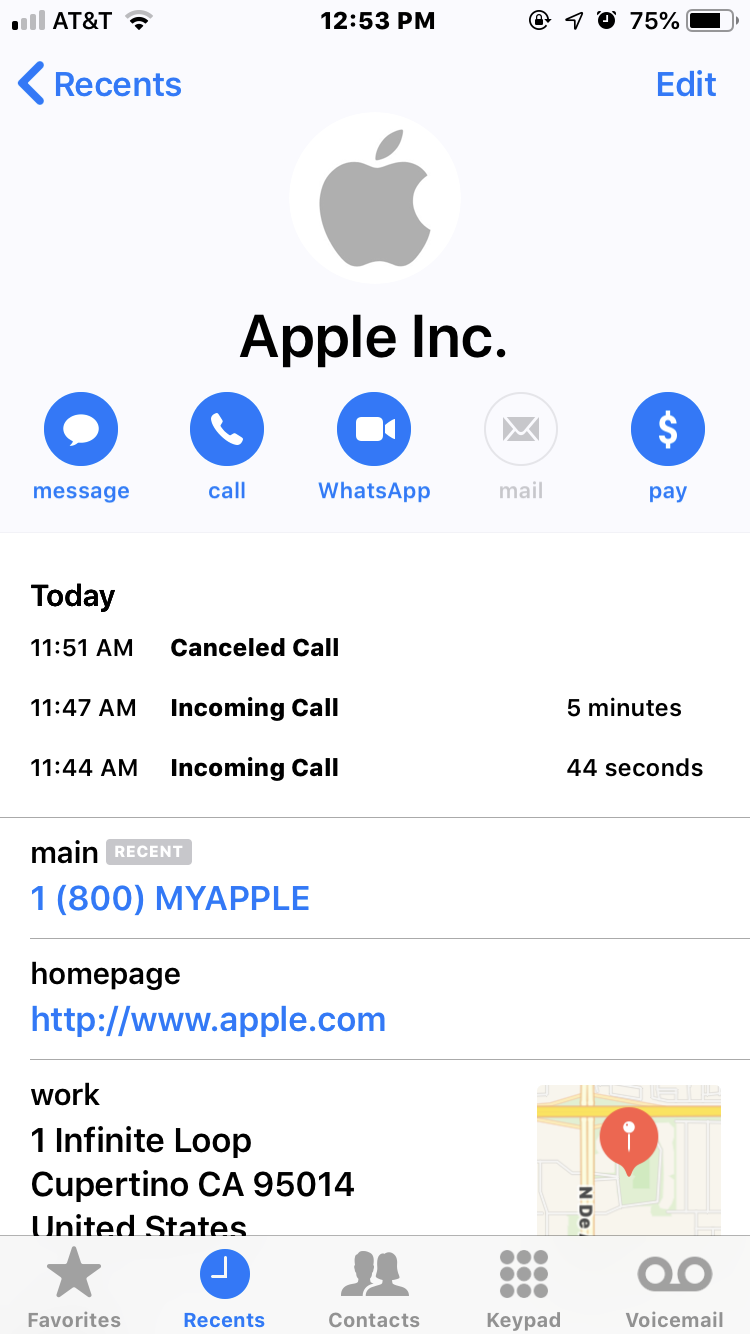
The fake call spoofing Apple — at 11:44 a.m. — was lumped in the same recent calls list as the legitimate call from Apple. The call at 11:47 was the legitimate call from Apple. The call listed at 11:51 a.m. was the result of Westby accidentally returning the call from the scammers, which she immediately disconnected.
The call listed at 11:51 a.m. was the result of Westby accidentally returning the call from the scammers, which she immediately disconnected.
“I told the Apple representative that they ought to be telling people about this, and he said that was a good point,” Westby said. “This was so convincing I’d think a lot of other people will be falling for it.” Continue reading




 This past year featured some
This past year featured some 
 The software giant
The software giant 
 At least nine of the bugs in the Microsoft patches address flaws the company deems “critical,” meaning they can be exploited by malware or ne’er-do-wells to install malicious software with little or no help from users, save for perhaps browsing to a hacked or booby-trapped site.
At least nine of the bugs in the Microsoft patches address flaws the company deems “critical,” meaning they can be exploited by malware or ne’er-do-wells to install malicious software with little or no help from users, save for perhaps browsing to a hacked or booby-trapped site.