A 20-year-old from Vancouver, Washington was indicted last week on federal hacking charges and for allegedly operating the “Satori” botnet, a malware strain unleashed last year that infected hundreds of thousands of wireless routers and other “Internet of Things” (IoT) devices. This outcome is hardly surprising given that the accused’s alleged alter ego has been relentless in seeking media attention for this global crime machine.

Schuchman, in an undated photo posted online and referenced in a “dox,” which alleged in Feb. 2018 that Schuchman was Nexus Zeta.
The Daily Beast‘s Kevin Poulsen broke the news last week that federal authorities in Alaska indicted Kenneth Currin Schuchman of Washington on two counts of violating the Computer Fraud and Abuse Act by using malware to damage computers between August and November 2017.
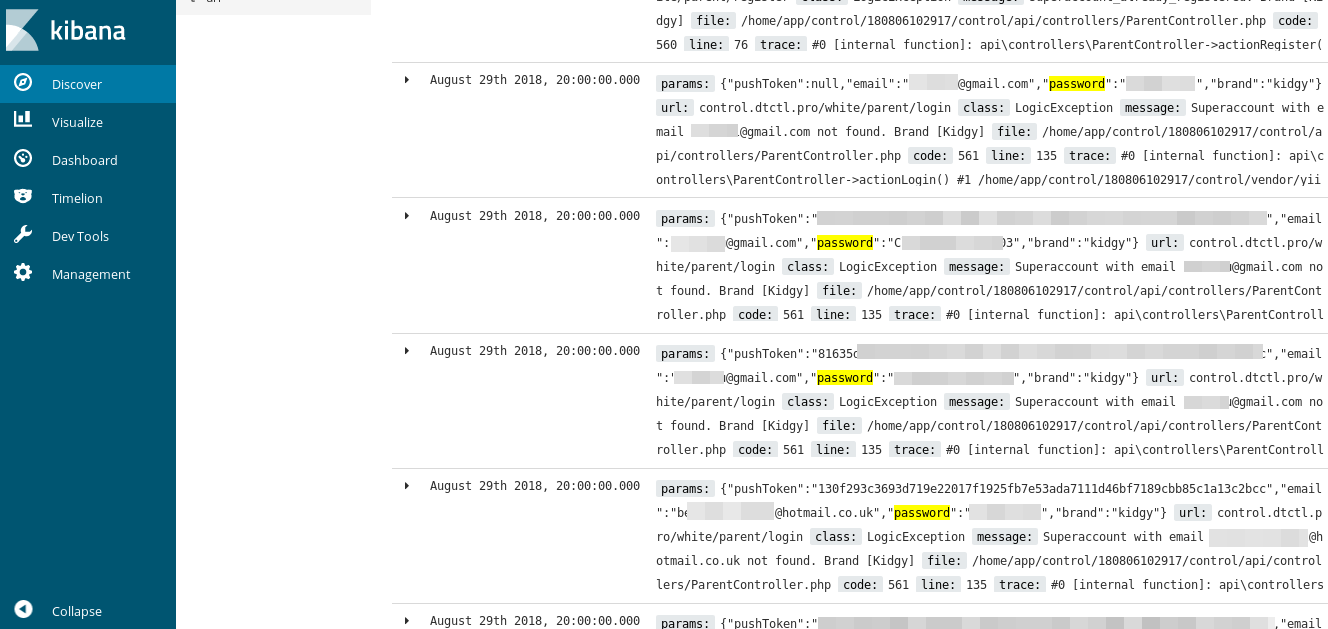
The 3-page indictment (PDF) is incredibly sparse, and includes few details about the meat of the charges against Schuchman. But according to Poulsen, the charges are related to Schuchman’s alleged authorship and use of the Satori botnet. Satori, also known as “Masuta,” is a variant of the Mirai botnet, a powerful IoT malware strain that first came online in July 2016.
“Despite the havoc he supposedly wreaked, the accused hacker doesn’t seem to have been terribly knowledgeable about hacking,” Poulsen notes.
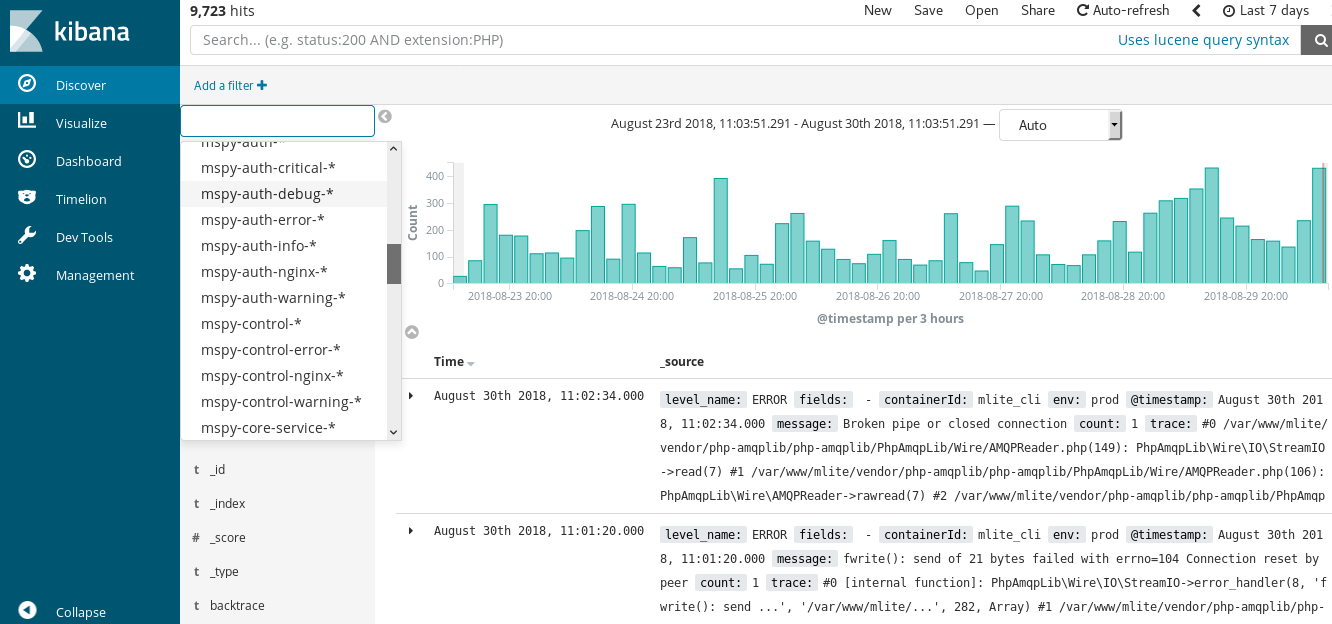
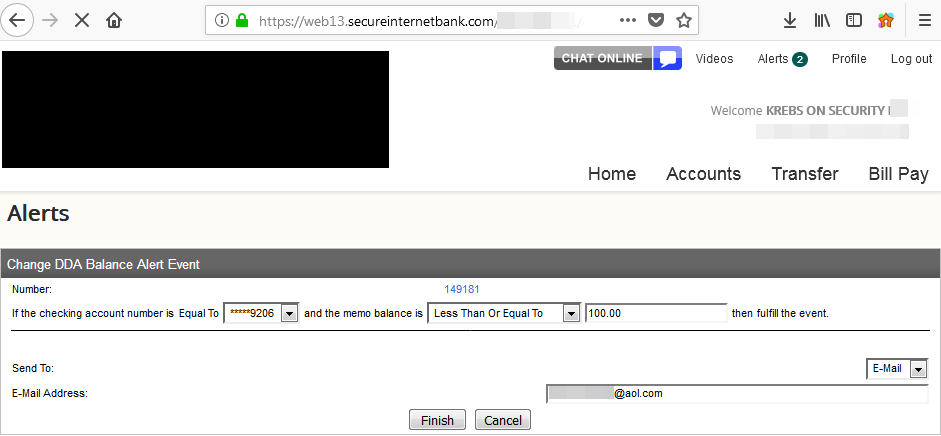
Schuchman reportedly went by the handle “Nexus Zeta,” the nickname used by a fairly inexperienced and clumsy ne’er-do-well who has tried on multiple occasions to get KrebsOnSecurity to write about the Satori botnet. In January 2018, Nexus Zeta changed the login page for his botnet control panel that he used to remotely control his hacked routers to include a friendly backhanded reference to this author:

The login prompt for Nexus Zeta’s IoT botnet included the message “Masuta is powered and hosted on Brian Kreb’s [sic] 4head.” To be precise, it’s a 5head.
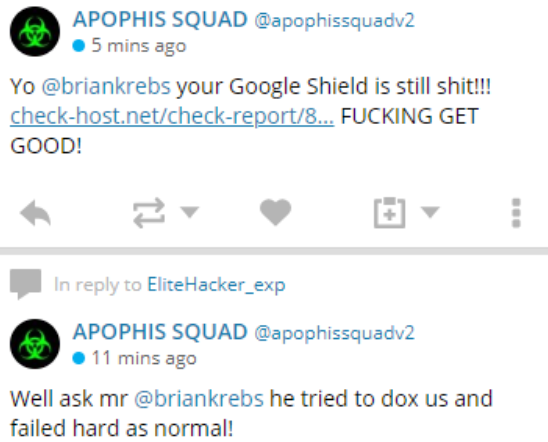
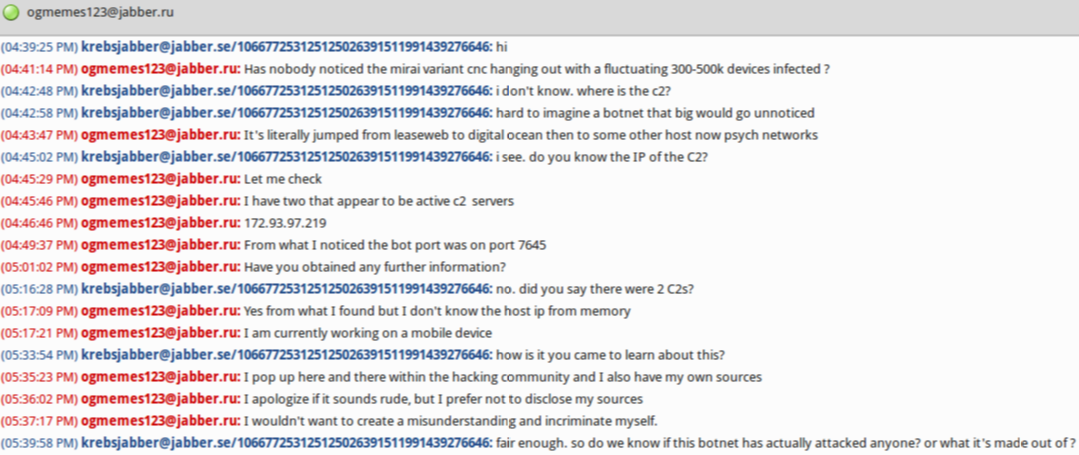
This wasn’t the first time Nexus Zeta said hello. In late November 2017, he chatted me up on on Twitter and Jabber instant message for several days. Most of the communications came from two accounts: “
9gigs_ProxyPipe” on Twitter, and
ogmemes123@jabber.ru (9gigs_ProxyPipe would later change its Twitter alias to Nexus Zeta, and
Nexus Zeta himself admitted that 9gigs_ProxyPipe was his Twitter account.)
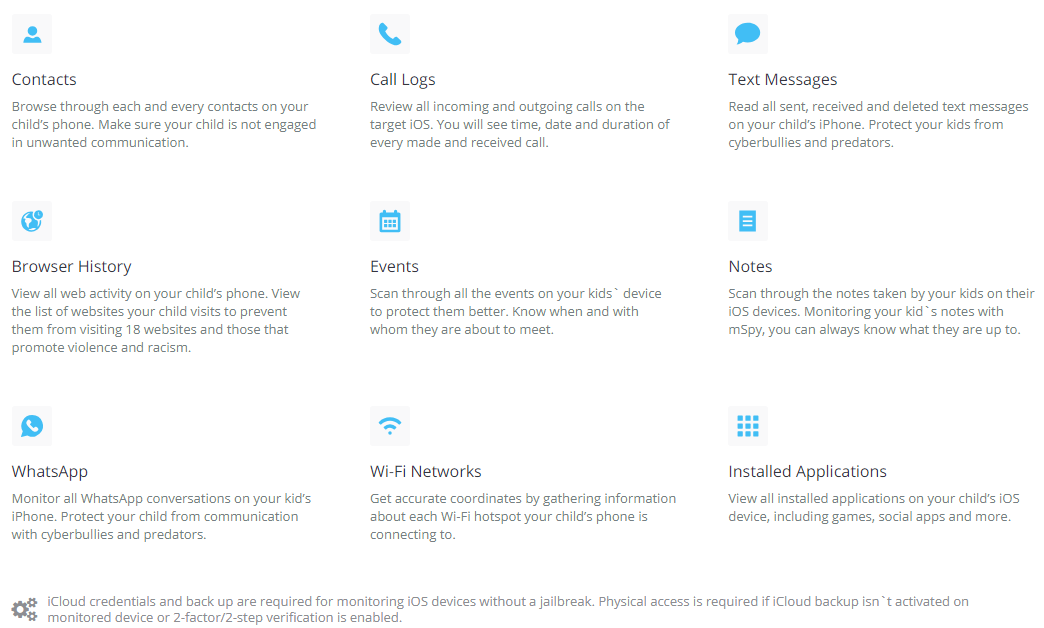
In each case, this person wanted to talk about a new IoT botnet that he was “researching” and that he thought deserved special attention for its size and potential disruptive impact should it be used in a massive Distributed Denial-of-Service (DDoS) attack aimed at knocking a Web site offline — something for which Satori would soon become known.
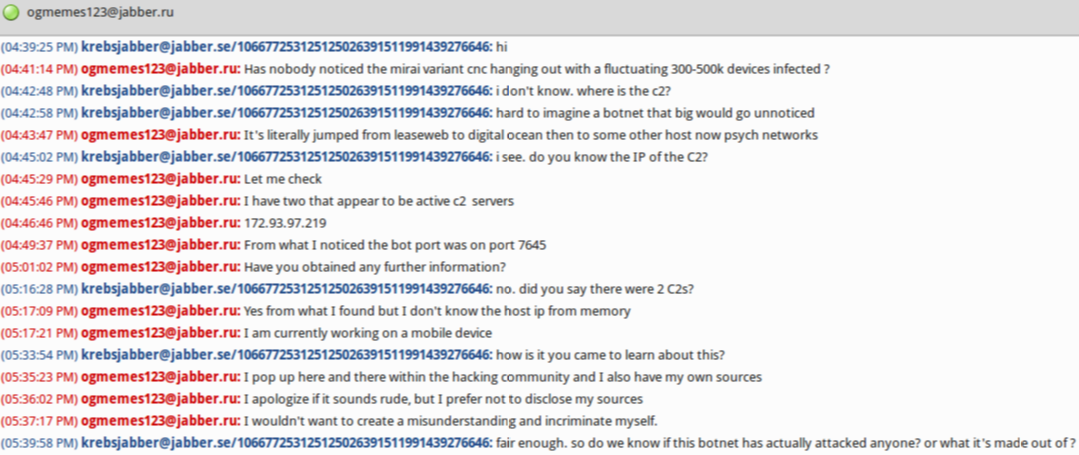
A Jabber instant message conversation with Nexus Zeta on Nov. 29, 2017.
Nexus Zeta’s Twitter nickname initially confused me because both 9gigs and ProxyPipe are names claimed by Robert Coelho, owner of ProxyPipe hosting (9gigs is a bit from one of Coelho’s Skype account names). Coelho’s sleuthing was quite instrumental in helping to unmask 21-year-old New Jersey resident Paras Jha as the author of the original Mirai IoT botnet (Jha later pleaded guilty to co-authoring and using Mirai and is due to be sentenced this month in Alaska and New Jersey). “Ogmemes” is from a nickname used by Jha and his Mirai botnet co-author.
On Nov. 28, 2017, 9gigs_ProxyPipe sent a message to the KrebsOnSecurity Twitter account:
“I have some information in regards to an incredibly dangerous IoT botnet you may find interesting,” the Twitter message read. “Let me know how you would prefer to communicate assuming you are interested.”
We connected on Jabber instant message. In our chats, Ogmemes123 said he couldn’t understand why nobody had noticed a botnet powered by a Mirai variant that had infected hundreds of thousands of IoT devices (he estimated the size of the botnet to be about 300,000-500,000 at the time). He also talked a lot about how close he was with Jha. Nexus Zeta’s Twitter account profile photo is a picture of Paras Jha. He also said he knew this new botnet was being used to attack ProxyPipe.
Less than 24 hours after that tweet from Nexus Zeta, I heard from ProxyPipe’s Coelho. They were under attack from a new Mirai variant. Continue reading →