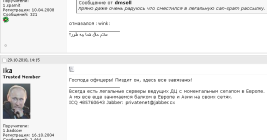
Meet Ika & Sal: The Bulletproof Hosting Duo from Hell
In 2020, the United States brought charges against four men accused of building a bulletproof hosting empire that once dominated the Russian cybercrime industry and supported multiple organized cybercrime groups. All four pleaded guilty to conspiracy and racketeering charges. But there is a fascinating and untold backstory behind the two Russian men involved, who co-ran Russia’s most popular spam forum for years.