I recently published a piece that examined the role of several Ukrainian men likely responsible for making and marketing the Styx Pack malware exploit kit. Today’s post will show how this same enterprise is linked to a DDoS protection scheme and a sprawling cybercrook-friendly malware scanning service that is bundled with Styx-Crypt.
As I noted in a graphic accompanying a July 8 analysis of Styx, the $3,000 exploit pack includes a built-in antivirus scanning service that employs at least 17 antivirus products. The scanning service is “anonymous,” in that it alerts Styx customers whenever one of the antivirus tool detects their malware as such, but the service also prevents the antivirus products from reporting home about the new malware detections.When Styx customers click on one of these malware scanning reports from within the Styx pack panel itself, the full scanning results are displayed in a new browser window at the domain captain-checker[dot]com (see screenshot above). The Styx panel that I examined earlier this month was based at the Internet address 5.199.167.196, and was reachable only by appending the port number 10665 to the numeric address. At first, I thought this might be a standard port used by Styx installations but that turns out not to be the case, according to interviews with other researchers. I didn’t realize it at the time, but now I’m thinking it’s likely that the panel I examined was actually one run by the Styx Pack curators themselves.
I discovered that although captain-checker[dot]com is hosted at another address (46.21.146.130), it also had this 10665 port open. I noticed then that captain-checker shares that server with 12 other Web sites. All of those sites also respond on port 10665, each revealing a captain-checker login page. Among the 12 is uptimer[dot]biz, one of two sites that led to the identity of Alexander “Nazar” Nazarenko — one of the main marketers and sellers of Styx pack.
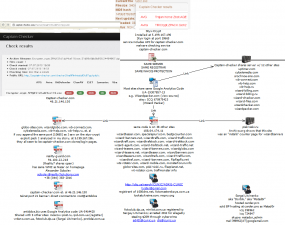 Not only are all of these sites on the same server, an Nmap scan of these systems shows that they all are on the same Windows workgroup — “Reality7.” This dovetails nicely with the other domain that I noted in that July 10 story as tied to Nazarenko — reality7solutions[dot]com.
Not only are all of these sites on the same server, an Nmap scan of these systems shows that they all are on the same Windows workgroup — “Reality7.” This dovetails nicely with the other domain that I noted in that July 10 story as tied to Nazarenko — reality7solutions[dot]com.
Many of the other domains on the server (see graphic to the left) use some variation of the word “wizard,” and share a Google Analytics code, UA-19307857. According to SameID.net, this code is embedded in the homepage for at least 38 different Web sites.
In my previous story on Nazarenko and his Styx Pack business partner — Max “Ikar” Gavryuk — I noted that both men were advertising “Reality Guard,” a service to help protect clients from distributed denial-of-service (DDoS) attacks designed to knock sites offline. I had a closer look at their site — reality-guard[dot]com — and learned several interesting things: For starters, the site also responds with a captain-checker[dot]com login page when you append “:10665” to the domain name. It also is on a Microsoft Windows workgroup called “Reality7”. Finally, the reality-guard[dot]com home page includes an icon for virtual currency Webmoney that when hovered over pops up Nazar’s Webmoney account (someone changed the name on this account from “Nazar” to “Lives” within hours after my July 10 story on the Styx Pack purveyors).
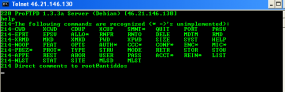 I noted in my previous story that Ikar apparently spoke highly of and even advertised a [competing?] anti-DDoS service called antiddos[dot]biz, and I discovered something curious about the server that hosts captain-checker[dot]com and those 12 other sites: If one attempts to connect to the open FTP server at that server’s address, it allows the connection and responds with the message “Direct comments to root@antiddos”.
I noted in my previous story that Ikar apparently spoke highly of and even advertised a [competing?] anti-DDoS service called antiddos[dot]biz, and I discovered something curious about the server that hosts captain-checker[dot]com and those 12 other sites: If one attempts to connect to the open FTP server at that server’s address, it allows the connection and responds with the message “Direct comments to root@antiddos”.
Who runs antiddos[dot]biz? The site and five others that share the same Google Analytics code UA-5414420 were the property of one Sergei Litvinenko, a Ukranian man who was reportedly arrested in Croatia in August 2012 for a host of alleged cyber crimes. Foreign media report that Litvinenko was sought by U.S. authorities for computer fraud worth $20 million, but initially I could find no federal charging documents that bore his name.
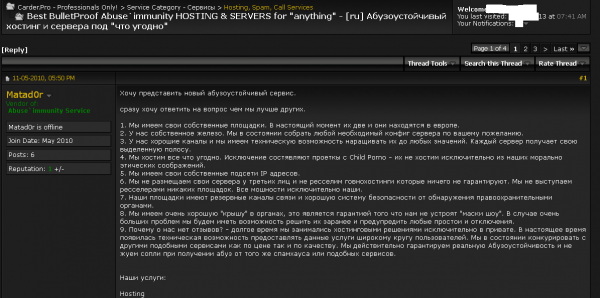
According to an unredacted version of this Justice Department document (PDF), Litvinenko is Defendant #20 in last year’s big Justice Department case targeting top members of carder[dot]su, at the time a major online fraud forum. According to U.S. authorities, Litvinenko – a.k.a. “Dorbik,” and “Matad0r,” sold bulletproof hosting services to hundreds of sites engaged in cybercrime activity, including carder[dot]su’s sister (and still very active) site carder[dot] pro. Below is a screen shot of Matad0r’s sales thread currently on carder[dot]pro.
If you enjoy reading these follow-the-breadcrumbs pieces, check out other stories like this one in the new KrebsOnSecurity.com content category, Breadcrumbs.



![Anonymous antivirus scanning service -- captain-checker[dot]com -- bundled with the Styx exploit pack.](https://krebsonsecurity.com/wp-content/uploads/2013/07/c-checker-285x93.png)

Very interesting read Brian!
Can i have some breadcrumbs please i so hungry .I almost got eaten by big ,fat , angry cat this morning but luckily i manage to get away from him .I have kids you know , who is going to look after them if i die ??
P.s It is what it is Brian and its nothing you can do about it . ыыыы
Started reading your columns when you wrote for the Washington Post and have continued since you went solo. Fun reads, good security tips, and fascinating insight into a very different world. Thanks.
Thanks, Barry. It’s fun to do much of this research, because I never know how far the trail of clues will lead and what connections will surface. But I’m frequently amazed at how little opsec most of these guys have. I attribute that to a pervasive attitude among these guys that they will never get caught. The sad part is they’re probably right.
I was thinking about pointing out that these guys ought to start randomizing some of their Web site and other identifying nomenclature to keep investigators from easily establishing the sorts of connections you routinely do in your articles. They should spread their operations around and not house them all in one black server.
Sorry – just made it harder for you! 🙂 Except you’re probably right, they won’t bother.
Without that attitude they probably wouldnt go criminal in the first place 😀
> I attribute that to a pervasive attitude among these guys that they will never get caught. The sad part is they’re probably right.
Let them think so 😉
You’r going well, Brian, tnx
Was that before or after Brian got recruited by KGB ?? 🙂
This one is for you Brian .
Я пришёл в ресторан, сжав червонец в руке,
Я смотрю в эти пьяные рожи.
Там у официантки узлы на чулке,
Видно, модный чулок, но заношен.
Хоть у лысого фраера слюни текут,
Он сморкает в платочек культурно,
Если в женском сортире ещё не блюют,
Значит, кончилась водка в “Лазурном”.
У зашторенных окон в высоком углу,
Взяв за талию, шепчет на ухо:
Приглашает летёха на стопку к столу
Молодую губастую шлюху.
Её полная грудь столько видела рук
И из этих же рук столько сотен,
Она знает по опыту и от подруг:
Офицеры скупы при расчёте.
Но сегодня здесь мелочь, и ей не фартит –
Зал прощупала опытным глазом:
“Надо хапать летёху, а то побежит
Через стол к белокурой заразе”.
Юбиляр всем хорош и шалит как школяр,
Льёт вино толстой даме на платье,
Завалился на стол, громко ржёт юбиляр,
Бултыхая медалью в салате.
Напоследок оркестр собрал всю толпу,
И последний заказ отыграли.
Я с червонцем стою, яблоко на снегу, –
Мне сегодня амнистию дали 🙂
“Молодую губастую шлюху”, interesting but off topic.
Sergei Litvinenko? It would appear that he is related to Alexander Litvinenko, the FSB guy who was poisoned with polonium-210 by Putin and his henchmen, but I wonder how close the relationship is.
Have you got any evidence of any relation? Sharing the same surname does not mean they are related.
Anyone spending time in Russia (or Ukraine or Belarus) quickly becomes acquainted with 20 Olgas, 20 Natalias, 20 Sergeis, etc, because there are actually not that many Russian first names (people from the Kavkaz often have different names than Russians, however). But last names are another story entirely.
Maybe the two Litvinenkos are not first or even second cousins, but I will wager that they are related.
Now, they will ddos krebs ;D
…again.
…and this would be unusual because…? 🙂
900 gigabit/sec should be more then enough if you ask me /
кребс, давай поинтереснее
а то хуйню какую-то стал постить в последнее время
ця стаття підкачала. але загалом нормал пишуть
Great work!, Excellent piece of journalism right there!
But won’t the creators of Styx Crypt find out about this post and start hiding their tracks?
Грузия. Горная дорога. На обочине голосует классический абрэк.
Останавливаются жигули. Абрэк достает из-под бурки обрез и
водителю:
– Дрочи!
Ничего не поделаешь – пришлось попотеть. Когда кончил – тот
ему снова:
– Дрочи!!
И так раз пять. Наконец, у совсем обессилевшего водилы в штанах
уже не “мужская гордость“, а жалкое зрелище.
Тогда абрэк поворачивается к придорожным кустам и кричит:
– Виходи, дочка – этот чэловэк подвэзет тебе до города .
Well, boys, I reckon this is it — nuclear combat toe to toe with the Rooskies.
We are against nuclear tests in atmosphere .Tsar Bomba (Russian: Царь-бомба; “Tsar Bomb”) is the nickname for the AN602 hydrogen bomb, the most powerful nuclear weapon ever detonated. Its October 30, 1961 test remains the most powerful artificial explosion in human history. It was also referred to as Kuz’kina Mat’ (Russian: Кузькина мать, Kuzka’s mother),referring to Nikita Khrushchev’s promise to show the United States a “Kuz’kina Mat'” at the 1960 United Nations General Assembly. The famous Russian idiom, which has been problematic for translators, literally meaning “to show somebody Kuzka’s mother”, equates roughly with the English “We’ll show you!” Developed by the Soviet Union, the bomb had the yield of 50 to 58 megatons of TNT (210 to 240 PJ). Only one bomb of this type was ever officially built and it was tested on October 30, 1961, in the Novaya Zemlya archipelago, at Sukhoy Nos .When detonation occurred the Tu-95V fell one kilometer from its previous altitude due to the shock wave of the bomb .
“The famous Russian idiom, which has been problematic for translators, literally meaning ‘to show somebody Kuzka’s mother'”
You mean, translators do not merely say “We will demonstrate for you, figuratively-speaking, the second generation of the largest nuclear weapon ever exploded by mankind”?
Yes, I can understand how translators might have a problem with that idiom.
P.S. Did you click on my name on my post? Major T. J. “King” Kong was a character in a very famous American film. And speaking of hydrogen bombs dropping, his last scene in that movie is rather memorable.
“Dr. Strangelove, Or How I Stopped Worrying and Learned To Love The Bomb.”
Джимми Святой, завязавший с преступным миром преступник, живущий в Денвере, занимается собственной фирмой («Загробные советы»: видеозаписи с советами умерших людей их близким). Однако, он должен главе преступной группировки, и в качестве выплаты долга парализованный ниже шеи главарь предлагает Джимми простое дело: найти одного ортодонта, который нынче встречается с бывшей девушкой сына главаря, и припугнуть его (сын, расставшись с девушкой, скатился до педофилии, главарь надеется на примирение с девушкой). Джимми пытается отказаться, но ему угрожают, и он соглашается.
Джимми выбирает себе в помощь четырёх человек из старых знакомых: Куска, больного проказой и нынче работающего в кинотеатре, демонстрирующем порнофильмы, байкера Франчайза, Критического Билла, безумца, работающего в похоронном бюро и избивающего трупы, и негра по имени Ветерок. Их план состоит в том, что Кусок и Билл, одевшись полицейскими, останавливают машину парня и доводят до Джимми и Франчайза, задача которых — запугать его; Ветерок подстраховывает. Однако, парень проявляет недоверие, обращает внимание на болезнь Куска, выводит из себя Билла, отчего погибает сам. Из машины выскакивает девушка, та, в которую влюблён сын главаря; Кусок, у которого был на взводе направленный на Билла пистолет, стреляет и убивает и её.
Главарь приговаривает всех пятерых к смерти, даёт Джимми 48 часов на то, чтобы покинуть Денвер. Джимми остаётся, пытаясь спасти подельников, встречаясь с красивой девушкой, улаживая дела знакомой проститутки. Джимми пытается вымолить прощение для семьянина Франчайза, пытается уговорить остальных уехать. Кусок выбирает — остаться, спокойно встречает быструю смерть от пули профессионального убийцы Молчуна. Следующим умирает Ветерок, спрятанный у должников Джимми, но выданный усилиями того же убийцы. Несмотря на мимолётное обещание главаря, погибает и Франчайз; Критический Билл же убивает убийцу, но Молчун успевает застрелить его. Главарь вызывает для убийства Джимми троих братьев из Мексики.
В последние дни своей жизни Джимми дарит обручальное кольцо девушке, с которой встречался, со словами, что он смертельно болен и желает ей выйти замуж за другого; убивает сына главаря, из-за которого всё началось, лишая смысла жизни самого парализованного главаря; спит с проституткой, которая хотела получить от него ребёнка. Он оставляет ребёнку видеозапись со своими напутствиями.
Во время фильма главные герои прощаются напутствием «За синее море»; рассказчик говорит о том, что оно является символом места встречи после смерти. В последних кадрах все пятеро подельников с главарём располагаются на палубе яхты, плывущей по морю.
Wow, Brian has really hit the big time! This thread alone has had at least three spam comments, with the last being everyone’s favorite, sex.
“Crebs, its your fault.”
Brian – You should have been working on the hunt for bin Laden. You could have saved us from two wars and trillions in debt.
I don’t understand why DOSing someone in this situation (or most situations) would give anyone the least amount of satisfaction. Even if you could take the site down it would be the non-digital equivalent of prank calling someone at 3am to ask if their refrigerator was running. Yeah, that’ll show Brian to report on cyber crime!