When you’re planning to rob the Russian cyber mob, you’d better make sure that you have the element of surprise, that you can make a clean getaway, and that you understand how your target is going to respond. Today’s column features an interview with two security experts who helped plan and execute last week’s global, collaborative effort to hijack the Gameover Zeus botnet, an extremely resilient and sophisticated crime machine that helped an elite group of thieves steal more than $100 million from banks, businesses and consumers worldwide.
Neither expert I spoke with wished to be identified for this story, citing a lack of permission from their employers and a desire to remain off the radar of the crooks inconvenienced by the action. For obvious reasons, they were also reluctant to share details about the exact weaknesses that were used to hijack the botnet, focusing instead on the planning and and preparation that went into this effort.
GAMEOVER ZEUS PRIMER
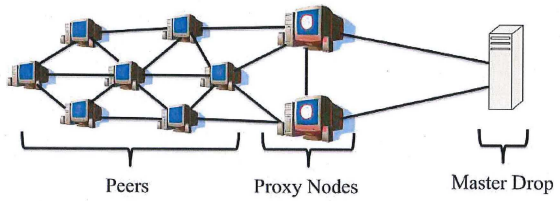
A quick review of how Gameover works should help readers get more out of the interview. In traditional botnets, infected PCs report home to and are controlled by a central server. But this architecture leaves such botnets vulnerable to disruption or takeover if authorities or security experts can gain access to the control server.
Gameover, on the other hand, is a peer-to-peer (P2P) botnet designed as a collection of small networks that are distinct but linked up in a decentralized fashion. The individual Gameover-infected PCs are known as “peers.” Above the peers are a select number of slightly more powerful and important infected systems that are assigned roles as “proxy nodes,” meaning they were selected from the peers to serve as relay points for commands coming from the Gameover botnet operators and as conduits for encrypted data stolen from the infected systems.
The Gameover botnet code also includes a failsafe mechanism that can be invoked if the botnet’s P2P communications system fails, whether the failure is the result of a faulty malware update or because of a takedown effort by researchers/law enforcement. That failsafe is a domain generation algorithm (DGA) component that generates a list of 1,000 domain names each week (gibberish domains that are essentially long jumbles of letters) combined with one of six top-level domains; .com, .net, .org, .biz, .info and .ru. In the event the infected Gameover systems can’t get new instructions from their peers, the code instructs the botted systems to seek out domains from the latest list of 1,000 domains generated by the DGA until it finds a site with new instructions.
HUNDREDS OF ‘WEB INJECTS’
The Gameover malware was designed specifically to defeat two-factor authentication used by many banks. It did so using a huge collection of custom-made scripts known as “Web injects” that can inject custom content into a Web browser when the victim browses to certain sites — such as a specific bank’s login page. Web injects also are used to prompt the victim to enter additional personal information when they log in to a trusted site. An example of this type of Web inject can be seen in the video below, which shows an inject designed for Citibank customers.
One of the most common Web injects used by ZeuS (including the Gameover variant discussed in this post) will intercept the one-time token code used by many banks as a second authentication factor, then redirect the victim to fake page falsely stating that the bank’s site is temporarily down for maintenance; all the while, the thieves are using the victim’s username, password and stolen one-time code to log in and move money out of the account.
According to CSIS Security Group, a Danish security firm, the crooks in control of Gameover had approximately 1,500 unique Web injects at their disposal that were custom-made to manipulate the display of more than 700 financial institution Web sites around the globe. CSIS shared that complete list, available here as a PDF and here as CSV. One thing you’ll notice is the conspicuous and complete absence of banks in Russia and in the former Soviet satellite countries.
READY PLAYER ONE
In the interview below, this author is “BK”; the interviewees, we’ll call them “Ready Player 1,” and “Ready Player 2,” or RP1 and RP2 for short.
BK: For this takedown to work, you guys had to…
RP1: It’s not a takedown. It’s a takeover. We’re taking control over the botnet.
BK: Right. So how did you all go about taking over the P2P portion of Gameover?
RP2: We don’t want to disclose too much of that because it’s theoretically possible they could regain control. But basically, you have to somehow manipulate the peer list and redirect traffic to yourself. That’s what we’re doing on the proxy node layer and on the P2P layer. And right now we’re controlling that. The [bad guys] can’t propagate updates or control it anymore.
BK: So you guys had to basically disrupt the P2P network and then take the domain names generated by the DGA out of the picture, correct?
RP2: Yes, the DGA is the fallback channel. So, just to be on the safe side, every bot checks in like twice a week and pulls a new list from the DGA. All attacks against P2P networks are pointless if you don’t take care of the DGA as well.
BK: I noticed the Russian top-level domain (TLD) .ru was among the the TLDs from which the takeover effort had to get cooperation. Was that difficult?
RP1: Dot-ru is always a challenge. But in the DNS community…people know each other and that was helpful.
BK: Have you ever seen a case in which the Gameover Zeus botmasters invoked the DGA component after losing control over their botnet?
RP1: This happened a few times in the past. At one point there was a broken version of Gameover, and they registered a few of the domains in the DGA list. There was a bug in version 2 that prevented them from updating it over P2P. I don’t know if the main botnet guy was on vacation that day or what, but something didn’t work right and they were for a while there relying only on the DGA.
BK: This is not the first attempt at takeover Gameover Zeus. Previous efforts didn’t work so well. What makes you think this takeover is going to last?
RP1: In previous P2P poisoning attacks against this botnet, we didn’t fully understand it. The first attack against it, we were not aware of the proxy layer, and that the bots were still able to communicate with the back-end [controller] through that layer. But we’ve been studying this botnet for two-and-a-half years now, so we know it pretty well.
BK: But they made improvements each time a takeover attempt was made right?
RP1: Defending a system that is as complex as this one is very hard. Complexity is the enemy of security. I won’t go into specifics, but let’s just say there are examples in the code where they clearly overreacted and introduced features that we could later use against them. The guys who built this are probably the elite guys in the cybercrime world, and so they really tried to build a botnet that was resilient to takeovers. But the Zeus guys didn’t get it right. They were pretty close to that, but they didn’t get it completely right.
BK: Well, one criticism of these takeovers and takedowns is that the bad guys don’t go away, they just get mad, learn from their mistakes and build a better mousetrap the next time. Don’t these actions merely poke the bear, and encourage them to innovate in ways that could bring us far more potent threats?
RP1: That’s certainly what we’ve seen in the past. They studied our attacks and the stuff that people published about the attacks, and they hardened the botnet. It takes a scientist or a skilled researcher to build a truly resilient P2P network, and these guys are criminals. They built it for stealing, and they don’t have endless resources to study the state-of-the-art, and that’s why they make mistakes.
BK: Were you guys surprised by anything in this takeover? Did anything happen that you weren’t expecting?
RP1: There can always be surprises. But I was a little surprised that they didn’t fight back. We were prepared for that. You have to be prepared for the unexpected, but that didn’t happen in this case.
BK: What have you noticed now that you have control over this botnet?
RP1: They were very active in using it. You’ve heard about cryptolocker. They had a very professional infrastructure set up so that most of this stuff was automated. The maintenance of the botnet was automated for the most part, and they also worked hard to keep the number of infected machines high over time. In order to stay in the game, they had to reinfect new machines all the time. And they did that with spam campaigns. It was a very professional organization.
BK: Right, they primarily used Cutwail to spread Gameover, correct?
RP2: Correct, and there’s been almost no Cutwail spam since last Friday.
BK: So, from your perspective, how did the Gameover guys use the data-theft component of this botnet, aside from the well-known financial attacks and account takeovers that reportedly netted them more than $100 million?
RP1: This was an information-gathering botnet. Everyone hears Zeus and they automatically think banking Trojan. But they were harvesting more than that.
BK: Have you all seen signs that the guys running this botnet were looking for stuff on infected machines that went beyond financial data?
RP1: I saw some, yes, but I can’t really talk about that. They were definitely looking for proprietary information in some cases.
BK: So the attack on Gameover began late last week, but how long was it before you guys felt like you had control over it, so that the botmasters couldn’t get it back.
RP1: Attacks against P2P networks usually take some time, depending on the specific implementation of the protocol. And at some point you own a critical mass and then it’s under your control. But it’s hard for us to tell when that happened.
BK: Why’s that?
RP1: It’s not trivial to monitor these things. You don’t have visibility into the entire botnet. Your view might be limited, but if you don’t see any changes over certain period of time, you can be sure the botnet is stable.
So far, the takeover appears to be holding steady. According to RP1 and RP2, a number of ISPs worldwide have begun notifying affected customers and trying to help with the cleanup process. For now, the number of new infections from Gameover Zeus have dropped to zero, according to Heimdal Security, a Danish security firm.




Thanks as always for the good information.
Imagine if they used TOR for the DGA, not so easy to take over those domain names.
I’m sure it’s been considered heh … great post BK, thanks!
I see no point in using domains at all. DNS is a bottleneck for the whole architecture. Why building P2P-network if there is still some DGA at the end?.. Why not just use some Russian/Chinese/Ukrainian /etc IPs for back-end and let the peers cache/exchange the ip-list. Am I missing something?
The DGA is only used if the peer-to-peer infrastructure goes down. If the peer network is down, then how else would the botnet retrieve new instructions if not through a sudo-random DNS? It can’t just have a hard-coded list of IP address, and it can’t talk to other peers for more information.
True, I completely missed the point that DGA was just a fallback channel. But malware can actually have few hardcoded IPs as a second fallback channel. It also can just scan the networks of the major Russian providers to receive a proper response. Anyway, how the RPs was able to disrupt the P2P network – is what really interesting here.
sudo-random? You’ve spent too much time with Unix.
So could the researchers with control of the botnet not push an update down to the peers that disables the infection?
No, in most countries this would be an illegal modification of a piece of equipment the relevant party (ISP, AV vendor, LEA etc) has no right to manipulate.
It’s nothing to do with legality, if it were possible some grey hat would have probably done it. Nearly all P2P botnets use asymmetric encryption to sign commands (only botmaster has the private key). When they say they “have control” of the botnet, what they really mean is the botnet infrastructure is under their control, but they have no control over the bots.
Would make a good episode of: NUMBERS.
I get confused with the ” failsafe is a domain name generation (DGA) component that generates a list of 1,000 domain names each week (gibberish domains that are essentially long jumbles of letters) combined with one of six top-level domains; .com.net, .org, .biz, .info and .ru. ”
How do the criminals sign up the .com.net, .org, .biz, .info and .ru. domains, so quickly and why doesn’t the T.L.D. register’s realize what is going on with all the gibberish names. Are the domain names paid with stolen credit cards?
Based on the interview, it sounds like they only registered the domain names if there was a glitch they were trying to resolve, and even then, they only had to register a subset of the 1000 names.
The names are picked using an algorithm that takes the current date (usually) as the seed, and generates a set of domain names for that day. The method used to turn the date into a domain name is known only by the bots and the botmasters. This means that on any given day, the botmasters will know which random-seeming domain name(s) the bots will fall back to on that particular day. For example, today’s domains might be sngkshdfhs.com and xljhtgfodls.net, and tomorrows a different set
To the registrars, all domain names are equal; no-one manually reviews them and generating semi-random, throw-away domains is reasonably common for uses other than botnet control. Yes, the domains will be paid for using stolen cards, but they only need to be live for 24 hours and I would imagine the controllers have an “a-list” of cards that they’re fairly sure will be accepted for important jobs like this one.
As long as the method for turning dates into domains is known only by the botnet controllers, it’s *very* difficult to stop this system working; and you have to succeed with all the domains, every day – a single missed domain allows the virus to be updated (potentially with a new domain generation algorithm) and renders the exercise pointless
Some of the information I already knew because of the randomness of creating domain names is used in phishing scams to seed malware (banking Trojans)
I read on a research whitepaper a while back how the domain name generation part of the Bot Net creates the needed random T.L.D. to connect back to the C & C server.
Thanks for filling in the blanks , it’s starting to make sense to me now. Much appreciated !
Couldn’t that be defeated by asking/requiring that all domain registrars put a 7-day hold on every new domain they register? Perfectly legitimate businesses can handle waiting periods; it’s only these hackers that require domains generated immediately. Right?
@Reader, Not really. Just because the bot creates the domain name list on a certain day, doesn’t mean that the domain name will have to be used for that day. The algorithm could be set to use any particular one created on any day before. It could also be set up to choose a previously created domain name based on the date and time, if the bot is keyed to the C2 (think RSA token). With that, the malefactors could set up the domains months in advance, let alone 7 days. Yes, there would be hurdles to overcome. For example, anyone with control of the output of a bot would then have foreknowledge of the potential domain name, but that would be a lot of leg work, and there are ways around that too. Encryption, say…
Thank you for the reply. Makes sense.
That is the main problem their is no real control over signing up of new domain names.
What would be an example of a legitimate use of a gibberish domain name?
something like sllljlhhiiowwllssl.com
Hosting something?
One language’s Gibberish is perfect words in other languages. For example, marschrhythmus is a perfect word in German,
strčprstskrzkrk is a perfect sentence in Czech (missing just a couple of spaces),
llanfairpwllgwyngyllgogerychwyrndrobwyll-llantysiliogogogoch.info is a website about the town with that very name (except for the .info) in Wales, there’s Tsinamdzghvriantkari in Croatia, etc.
Not even talking about abbreviations. One German TV show was advertised as “SSDSDSSWEMUGABRTLAD”.
Not to mention many legitimate web operations (e-commerce) pass off part of their processing to other domains with less than obvious domain names. Watch the domain names in the address bar of your browser as you conduct e-commerce, oline banking, or other transactions.
Many places that sell domains and hosting have access to bulk buy (or basically register free) any domains they want that are open. I’d be willing to bet they either sell domains/host them and that’s why they can make that many or have some sort of hookup. That or they’ve hacked a place that sells those domains and do it that way. Which is entirely possible.
Good report, Brian! Covering the sensitive matter in the nice way,
” The guys who built this are probably the elite guys in the cybercrime world, and so they really tried to build a botnet that was resilient to takedovers.”
Takedovers — small typo there. (Unless it is an amalgamation of takdown and takeover.)
Great read, Mr. Krebs. Visiting this site is becoming a daily habit!
What got me is its reported they stole 100 million dollars! With those deep pockets that can put a lot of resources to bring this network back up. The limiting factor is not money, but rather raw talent. It seems this is where authorities have to concentrate their efforts. In the spy business a dossier of those working in the field is the best asset.
Two things come to mind:
Why not name the researchers but name a security firm involved (Zeus guys could attack it)?
The Zeus guys are having the same complexity problem that enables malware writers to be successful–now it works against them!
Regards,
+1
I don’t understand why the security firms were named
They were named because they wanted to be.
Perhaps they wanted to enhance their reputation and gain clients.
its like a video, but its really a gif :/
A very good interview. And I agree with their not wanting to discuss details.
The only thing I disagree with is: “It takes a scientist or a skilled researcher to build a truly resilient P2P network”.
Speaking as a scientist and a skilled researcher, who’s also in particular thought about the problem, its really really hard, especially the recovery/rendevous problem on how to rejoin the botnet in case of disruption.
I might be confused but the two statements seem to be in agreement.
This is a really great article, well written, and fascinating to read. Thank you!
Cant the botmasters infect/find a local node, and “hijack” its traffic to make it seem like it comes fra a proxy node? And this way send an updated list of proxy nodes to the p2p network, hence regaining control of the bots?
Since the botmasters are in control of the RSA and RC4 keys they should be able to inject new commands into the bots?
Great work taking down a notorious botnet, but without getting the perps it’s like pulling weeds but not the roots. They will be right back at it in no time.
And with the West and Russia at odds – they might not have gotten the perps anyways. I doubt Russia will be handing over any of its citizens to the West any time soon.
Great article Brian!
Awesome insight into the takedown, I wish they could publish more of the details, perhaps when you out the bad guys………..
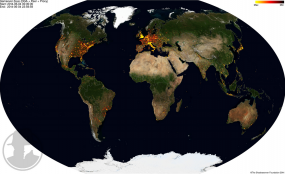
It’s distressing to see that, even after at least somewhat accounting for the population disparity, the US leads in bot infections by a healthy margin (source: The SecureWorks report linked in the “Operation Tovar” thread – http://www.secureworks.com/cyber-threat-intelligence/threats/The_Lifecycle_of_Peer_to_Peer_Gameover_ZeuS/). I’m left wondering how much of that is simply because English is one of the few languages common to so many countries vs. whether a lot of the initial infection vectors are written with the intent of deliberately targeting Americans.
WOW!
Man, I remember around 2005, when the gov’t couldn’t even takedown, the winmx p2p network no matter how hard they tried… After frontcode abandoned it and got served a cease and desist, 10 days later it was back online. There were three different hacker groups fighting it out. then it turned into only two groups, with diff peer caches, (winmxworld vs. mxpie) one group demanded extra bandwidth from users(without notifying them) for the good of the network and forced them to use blacklists, the other group didn’t believe that was moral or honest and believe it should be volunteered. They would attack each other, lol, but then they eventually united, and it still runs to this day.
But P2Ps have been dead and unpopular, not because of gov’ts efforts, but because rapidshare sites and bitorrents are so much faster. But its just a shame how less social and community oriented file sharing is now…. or how vile almost any chatroom or forums onine are now. And how there are just no whitehats, or family oriented help sites that are popular anymore, which is how many people, like me, learned about pc’s in the first place.
Now who are these kids learning from and talking to, and getting influenced by online?
What part of using Bittorrent or filehosts that involves a community based around a website do you think is less social than typing a search query into a box like you would with WinMX exactly?
You appear to be reminiscing about something that wasn’t social at all and inferring that it is more social than p2p systems that are unavoidably social.
Remember browsing someone’s music library on SoulSeek, and then opening a chat line with him or her to talk about your shared interest in music and finding new branches that you hadn’t been down yet?
Or was that just me and OP?
I still use it Jason, except barely anyone speaks english anymore hahaha. The German guy who ran soulseek also got a cease and desist letter a while ago, he asked for donations for legal fees for a couple years, and now Someone else has taken it over…its a little shady now, but it is still used by many around the world, including me.
@ Neej, All those Mommies and Daddies running their own chatrooms in winmx, just like IRC, who taught many people how to use a pc, and p2ps like them, is why hackers banned together, and the gov’t could never shut them down….
There is nothing social about filesharing sites now, Most of them just give you viruses nowadays if you click the wrong link. And All bitorrents have is vile comments about bootleg movies, and more links for viruses. Not really any hacking white hat role models to be found like in old IRC and Winmx chatrooms. Or online anywhere….
note to RP1:
without scale complexity is meaningless, thus it’s complexity with scale that is the enemy of security.
indeed, in determination of when operational control was obtained, you point out it was the scale that presented the issue, not it’s complexity.
i realize that folks often lump scale into complexity, but i think folks might be better served by viewing them separately, as they have different characteristics.
anyway, good job and my thanks to you and those who we can’t express our thanks to openly. sometimes you have results that can be acknowledged, more often not, but the work you all do is appreciated… even ‘grandma’ approves.
and bk, thanks for another great story/blog post.
“That’s certainly what we’ve seen in the past. They studied our attacks and the stuff that people published about the attacks, and they hardened the botnet. It takes a scientist or a skilled researcher to build a truly resilient P2P network, and these guys are criminals. They built it for stealing, and they don’t have endless resources to study the state-of-the-art, and that’s why they make mistakes”
Seems very callous.
So…. The investigators are supposed to be “polite” when speaking about the hackers ? Lets say your cards/ bank account were a victim, I would imagine you’d be spitting fire at the criminals….
Its cold, hard, realistic issues… treat it as such. If it was delivered with Rose Colored Glasses, people would not pay as much attention to it, nor see the alarms associated with the content.
I think its meant as a wake up call. I can see things getting better on the “good side” but only if people stop to think, rather than hitting “next, next, next” flying through prompts or simply not checking to see if the site seems legit.
“in the DNS community…people know each other and that was helpful.”
Imagine if they had friends in the ‘DNS community’ and could just redirect traffic as they saw fit.
‘Pretend inferiority and encourage his arrogance.’ -Sun Tzu
The U.S should allow American hackers to hack banks and the people in Russia and the former Soviet satellite countries. That should get their banks and citizens upset. The U.S government cracks down on us when the Russian government cracks down on their hackers. Until then, it should be open season on Russian banks and citizens.
Then, they would be subject to hacking overseas and the foreign country laws. Plus its like being a do-as-I-say-not-as-I-do kind of mediocre act. One country yanks people out of foriegn countries and then says its OK to hack? Thats ludicrous.
Its simply better to put an embargo on the offending country stating that all consumer banking between the country #1 and country #2 is ceased until these particular conditions are met (specific network activity takedown / takeovers)…..even that legally is a nightmare.
Its really not that simple. These P2P botnets have at least “two ends” and its very difficult to maintain control. We’re talking about cyber crime, sort of a mafia style “family” tree of well trenched in people who obviously pay well for good talent. They also are rich – think about this – if THIS particular botnet got them 100 Million buckaroos, what about the botnets that are yet undiscovered or aren’t in this equation yet. Why do they continue to do it if they are bloddy rich ? Its simple – they simple dislike the people they are stealing from, and the monies that get, they probably could fund their own country/ countries…or are they?
I skimmed through a Microsoft White Paper 2013 report reviewing incidents of Malware, viruses and the like. The countries with the most number of incidents included Brazil, China, and Russia. So even though these criminals appear to be located in Russia, Russia has a problem with infected computers.
Taking a companies data hostage by encrypting it and asking for ransom, I remember reading years ago, is common in Russia.
Which is why i was a little confused about the media making it out to be something new, I guess the question is what took so long for it to start happening in the USA and why is anyone surprised.
Your post seems candid but you fail to consider 2 aspects:
– would be highly immoral to turn a blind eye when innocent Russian citizens’ money are stolen, just as immoral it is when Russian government allows their black hats operate with impunity.
– what makes you believe that if one government allows hackers to thrive and steal monies from Russia and Eastern Europe it can also control them and crack down on them when the Russian government responds in kind ? I find more likely an Afganistan or Iraq scenario where Western World armed and trained those guys to fight Russia or Iran just to realize one decade later that the people they trained have turned into terrorists threatening free world.
Great article Brian! I’m fascinated by botnets!
Not to be nit-picky but there seems to be a typo in the fifth response from RP1 in the fourth sentence at the end. I believe this should be ‘takeovers’ and not ‘takedovers.’
It’s a cross between takedown and takeover.
Thanks for the warning. I’ve had a “down for temporary maintenance” experience with Citibank sites. One credit card site (no bank account connected with it) posted that. I emailed support and got an odd good-vibes unhelpful response. There were no instructions in the page showing “down for maintenance,” but I clicked on the “ok” button, which took me to an ostensibly Citibank site that let me log in. The card amount was right, but I decided to pay it by telephoning support. The site prompted me a couple of times to pay by direct access to a bank account. I’m probably lucky I don’t use that username for anything else, nor that password, which I’d changed, anyway. I guess being hacked is now as inevitable as death and taxes.
Hi there! This is my first visit to your blog! We are
a team of volunteers and starting a new project in a community in the
same niche. Your blog provided us beneficial information to work on. You have done a wonderful job!
Why the “complete absence of banks in Russia” in the web inject list – could someone please enlighten me?
The criminals behind the botnet are Russians themselves. As long as their botnet doesn’t commit a crime in Russia, the idea is, the Russian police force won’t (be able to) go after them.
Regarding registration of these domain names, could one way to stop these domain name registrations be to:
1. request a domain name and provide a card number – this would in effect reserve the domain name
2. 7 days later the domain would be paid for using the card number provide in step 1. Any stolen cards would hopefully have been cancelled by this time and the transaction would not go through.
My low-tech thought … when I look at the Citi example I wonder how anyone could have possibly thought that providing all of that info is what the real Citi would require. The hackers can set up the traps but it takes overly trusting (the nicest term that I can use) people to step into them. We see this time and time again.
Thanks for another magnificent post. Where else may just anybody get that kind of info in such a perfect manner of writing? I have a presentation next week, and I’m at the look for such information. afkfkakdefee
Uh yeah you’re going to be nice. I can’t elaborate. All I can say… And I say this because I am in this situation, have been since March and I have take every step out there and more and it won’t stop. It would blow your mind the things that can and do eventually happen. No gov agency has been able to help my husband and I yet and because we tried to fight back aggressively (hand to hand combat essentially when first made contact) this made life a whhoooole lot worse. This started in March. I am risking even posting but I am desperately grasping at straws now after every extreme attempt has been made.
Yes. What you say under “the master” – my real thoughts can’t be conveyed St this moment – will be seen eventually and punishment (I call it) will happen.
No one gets the severity. It’s not about “data loss ” aka the vague blank concept – but serious problems like phone tapping, pics and recordings on all devices, getting your bios fried, losing all identifiers on iPads, your Apple I’d being deleted therefore locking you out of your iPhone. Bless your heart if you work at home for Apple. You just lost your job you had for 4 years bc you no longer have an efficient adequate work environment … Not without your Apple I’d or the fact that it’s the 3rd Mac apple has sent due to something putting administration rights on your work Mac, locking you out. If you want to call losing a job and all aspects of privacy “data loss” then by all means, go for it. Until it happens to you.
Not saying it happened to me…
Omg it went through!! If anyone has any advice for me, I’d appreciate it. Here’s a post that failed that I wrote earlier. I’m taking advantage of the small window I have to get through… All consequences be damned. They have the worst to me it feels. Here you go…
Someone wanted a profile of a typical victim…. My husband’s pc was infected Mid March and then obviously hit every device in our home and it’s now almost July and surprise – we are still under the botnet from hell despite numerous remedies, help from police, fbi, and even secret service. The disruption was a nice lull but now it’s quietly gaining momentum . The kicker? My husband works tier 2 in tech support for a company with the name of a certain food. The bad actors deleted his work ID when he caught them loading all of his data onto 4 peer sharing sites. Fighting back did more harm than good. My husband is very smart and we are over protected to the point of paranoia. We thought we were above intrusions and infections. Ha. I am 27 and a teacher and have considered myself an infosec buff. My husband is a computer wiz and is 30 and as previously stated, lives, breathes all things os x/linux/Windows. We have been in the botnet trap since MARCH. After changing our numbers, numerous routers, new ips dumping the iPads completely due no kernel access and numerous puk changes and fails, new numbers, countless Sim card changes, completely unplugging a now emulated pc and 3 emulated Macs, getting new dvrs (yes, our freaking dish dvrs got hit), 7 new androids, following every sites guide for removal nothing has worked so far. We have private govt agencies stepping in at this point. We have a honeypot and so far the tcp count/dump services is astronomical (over 70,000).
I am getting a tad pissed at this point considering our phone bill was $1500 due to burning through 30gb of data in one week. Ha. We only have 2 phones on our plan and we don’t use a lot of data. I will probably get punished for even posting this. (yes any step we take when trying to create awareness or trying to stop getting sent to a sinkhole is rewarded with more data loss or ddos attacks on our network… Which at this point my Internet is at a crawl due to being blacklisted by Cbl for our Ip being detected as part of zues.
There ya go….
Attempting to send but due to an awesome DNS changer and puppet master it is “timing out.”
I am praying this submits….