Over the past year, I’ve spent a great deal of time trolling a variety of underground stores that sell “dumps” — street slang for stolen credit card data that buyers can use to counterfeit new cards and go shopping in big-box stores for high-dollar merchandise that can be resold quickly for cash. By way of explaining this bizarro world, this post takes the reader on a tour of a rather exclusive and professional dumps shop that caters to professional thieves, high-volume buyers and organized crime gangs.
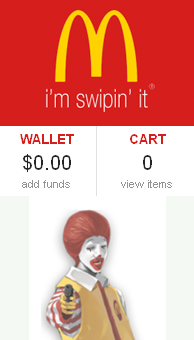 The subject of this post is “McDumpals,” a leading dumps shop that first went online in late April 2013. Featuring the familiar golden arches and the bastardized logo, “i’m swipin’ it,” the site’s mascot is a gangstered-up Ronald McDonald pointing a handgun at the viewer.
The subject of this post is “McDumpals,” a leading dumps shop that first went online in late April 2013. Featuring the familiar golden arches and the bastardized logo, “i’m swipin’ it,” the site’s mascot is a gangstered-up Ronald McDonald pointing a handgun at the viewer.
Nevermind that this shop is violating a ridiculous number of McDonald’s trademarks in one fell swoop: It’s currently selling cards stolen from data breaches at main street stores in nearly every U.S. state.
Like many other dumps shops, McDumpals recently began requiring potential new customers to pay a deposit (~$100) via Bitcoin before being allowed to view the goods for sale. Also typical of most card shops, this store’s home page features the latest news about new batches of stolen cards that have just been added, as well as price reductions on older batches of cards that are less reliable as instruments of fraud.
I’ve put together a slideshow (below) that steps through many of the updates that have been added to this shop since its inception. One big takeaway from this slideshow is that many shops are now categorizing their goods for sale by the state or region of the victim company.
This was a major innovation that we saw prominently on display in the card shop that was principally responsible for selling cards stolen in the Target and Sally Beauty retail breaches: In those cases, buyers were offered the ability to search for cards by the city, state and ZIP of the Target and Sally Beauty stores from which those cards were stolen. Experienced carders (as buyers are called) know that banks will often flag transactions as suspicious if they take place outside of the legitimate cardholder’s regular geographic purchasing patterns, and so carders tend to favor cards stolen from consumers who live nearby.
The slideshow may make more sense if readers familiarize themselves with a few terms and phrases that show up in the text:
GLOSSARY OF TERMS:
Base: An arbitrary name that a dumps shop assigns to a unique batch of cards stolen from a particular compromised merchant or a mix of merchants. Most often, bases are named after the state or region of the compromised merchant. Base names allow dumps shop owners to have a consistent naming convention when adding freshly stolen cards from a specific breached merchant. In addition, base names allow happy customers to have an easy way to come back to the shop and request more of the same cards; conversely, buyers who have little success “cashing out” cards from a particular base have a frame of reference with which to warn other potential buyers away from a specific batch of cards (a la “brown acid“).
BINs: Short for “Bank Identification Number,” this is the first six digits of any debit or credit credit cards, and it uniquely identifies the financial institution that issued the card. BINs are the primary method that card shops use to index wares for sale, and all buyers have their favorite BINs with which they’ve found success in the past. There are tens of thousands of BINs in use today, and few people legitimately employed in the banking industry have comprehensive BIN lists (which most banks consider proprietary). For that, you typically need to turn to the professional card shops, which track BIN usage quite closely.
Checker: A form of buyer’s insurance, this is an automated, optional service that dumps shop customers can use after purchasing cards to validate whether the cards they just bought are still active. Most advanced shops, including this one, have “moneyback” guarantees in place that will automatically refund the purchase price for any cards found to be invalid shortly after the cards are bought (usually a window of a few minutes up to a few hours), provided the customer pays the extra fee (usually 10-20 cents per card) to use the shop’s own checking service.
Dump: Refers to a string of data that is pulled (usually by malicious software that infects cash registers or point-of-sale devices inside compromised merchants) from the magnetic stripe on the back of cards. Buyers typically receive a text file that includes all of their dumps. Those individual dumps records — when encoded onto a new magnetic stripe on virtually anything the size of a credit card — can be used to purchase stolen merchandise in big box stores.
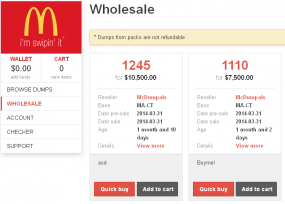
Packs: Large bundles of dumps (often from a variety of hacked merchants in a particular region) — sold at wholesale prices. As we can see from the screenshot above left, McDumpals sells dumps packs of more than 1,000 cards at a time. For example, in the screen shot above, the site is offering a pack of 1,245 cards stolen two months ago from stores in Massachusetts and Connecticut for the bargain price of USD $10,500.
First-hand base: A batch of cards stolen from a merchant breach in which the dumps shop proprietor himself played a key role. The multiple bases of some 40 million cards stolen in the Target breach and resold via rescator[dot]so is probably the biggest example I’ve seen of a first-hand base.
Reseller: Most dumps shops rely on multiple suppliers of stolen cards. Contrary to the conventional meaning of the word, these thieves are supplying cards that are not sold anywhere else; once a card is sold, it is removed from the marketplace, and any suppliers found to be double dipping are quickly banned from the dumps community. Rather, resellers are merely stealing the cards and then selling them to the dumps shop.
Valid rate: The dumps store’s best guess about the percentage of cards from a given base that will come back as valid versus canceled by the issuing bank. If a base is advertised at a 70 percent valid rate, customers can expect an average 3 out of every 10 cards they buy from that base to be worthless. Cards advertised at valid rates in excess of 90 percent typically demand the highest prices, and are a strong indicator of a breach that has only just been discovered by the breached merchant or some of the larger financial institutions. For more granular examples of how valid rates are closely tied to the price of stolen cards, see Fire Sale on Cards Stolen in Target Breach and Sally Beauty Hit By Credit Card Breach.
If the following slideshow is not visible, you may need to enable scripting on this page from knightlab.com, a Northwestern University joint initiative of Medill School of Journalism, Media, Integrated Marketing Communications and the Robert R. McCormick School of Engineering & Applied Science.
People often ask if I worry about shopping online. These days, I worry more about shopping in main street stores. McDumpals is just one dumps shop, and it adds many new bases each week. There are dozens of card shops just like this one in the underground (some more exclusive than others), all selling bases from unique, compromised merchants.




violating a ridiculous number of McDonald’s trademarks . Zzz you so funny Brian , like a funny guy from Coming to America .They have golden archers but we have golden gates, they have Big Mac but we have Big Muc .
i wonder how many laws did you violate Brian ?? i can name at list 10 right now . Do you want to hear them ??
i give you heads up
handling of stolen goods is one of them
They got the Golden Arches, mine is the Golden Arcs. They got the Big Mac, I got the Big Mick. We both got two all-beef patties, special sauce, lettuce, cheese, pickles and onions, but their buns have sesame seeds. My buns have no seeds.
I’m funny? That’s a laugh. So, enlighten me oh funny man: Which 10 laws did I violate?
Hey Brian… the bad guys (even the grammatically challenged) do read your blog… way to go!
Is English not your first language?
Nyet, Comrade.
Probably something about their terms of service?
The US does have some weird ideas about making the click-through agreements legally worth something, don’t they?
Would buying the numbers be illegal? Surely it would just be the use of them, & perhaps storing them insecurely. Not sure about data privacy and like protections.
Of course, I think it unlikely you’d have bought rather than simply browsed!
Ou yes he did ,He bought aLots of them — Knowingly that them cards are stolen that is facilitating organized crime activities.His money could be used in drug smuggling , human or guns trafficking or in any other illegal activity’s which is a crime on own . Even worse he could be helping a terrorists .
ahh the terrorists…..
I should’ve known.
“Contrary to the conventional meaning of the word, these thieves are supplying cards that are not sold anywhere else; once a card is sold, it is removed from the marketplace, and any suppliers found to be double dipping are quickly banned from the dumps community.”
I don’t see how this works. Sounds like all the players in the dumps community are anonymous and go by aliases, hidden by multiple IP redirects, so if you’re banned, just start over again with a new identity. It seems like these communities would all implode under the chaos caused by their own greed.
It works like any other component of the underground, which is entirely based on reputation. The dumps shop proprietor is only going to work with sellers who come recommended or vouched for by other trusted sellers. These card shop owners have plenty of ways to check on the validity of cards before they purchase them from resellers, but in any case they don’t buy them outright; most resellers get paid a percentage of whatever their cards sell for on the shop. So, if a bad seller wants to try to scam the card shop by selling him crap cards, he’s not going to make much money doing that because the customers will complain about valid rates that don’t match the advertised valid rates at all.
Brian You are not just a funny guy , you are hilariously funny guy . And yes i all ready told you one law which you broke ( 1 handling of stolen goods or stolen property ) buying stolen credit cards is a crime and you know it .
2 engaging in illegal activity’s
3 computer hacking
4 Underground banking
5 Tax evasion
6 possibly — Cyberwarfare
a so on ..
First, that’s not 10. Second, what you posted are not relevant sections of the U.S.C or any state crimes code. Please, speculate and assume some more – it’s what makes the internet lights stay on at night.
Pre-school grammar aside, this is hilarious.
-”engaging in illegal [activities]’ is not a specific crime any more than ‘being a criminal’ is. That’s like saying someone is stupid because they’re a moron.
-Visiting a website is not ‘computer hacking.’
-‘underground banking’ is a rather ambiguous term.
-‘Tax evasion’ – Got any details to go with that?
-‘Cyberwarfare’ – And what action has constituted cyberwarfare? Where’s the DoS attack or malware distribution?
Maybe get a grip on the English language first, then try claiming some knowledge about American and international law.
Congrats you have been promoted to Grammar Nazi! Got anything useful to tell us ?
He’s correcting logic not grammar. Grammar would be pointing out that “Congrats” is not a real word.
Andrew Felsher’s comments are hysterical, almost as funny as dump me if you can Goodfella’s…almost. Grammar nazi, Tom? It’s called humor, some of which some of us have. Oops a little crazy sentence structure right there. Catching up with Brian’s posts today. As usual, I am stunned by the number and breadth of bad actors and bad actions in the cyberfraud world. Keep up the good work, Mr. Krebs. As for Goodfella, ignore him, except as comic relief. He’ll be okay once he gets back on his meds…
You obviously have no idea what you’re talking about, so please let the rest of us get back to enjoying Brian’s great research and analysis.
The funny part about this is how upset all the cockroaches get when someone shines a light on them.
Dump me?
I’m not sure I follow your logic? If Brian buys the data from a stolen card (not the same as the physical card) the end use of the data is the question — and in this case that card is no longer in play, so the credit card owner is actually saved from potential harm. …but please show where Brian “bought” any cards — reporting that they are for sale is not the same as actually purchasing… ??
Engaging is *what* illegal activity. If you see a crime committed in front of your home and you tell me about it, is your telling me illegal? (hint: No.) Your point is lost on me.
Computer hacking: which computer did Brian hack? He followed links to publicly available websites that, he believes (only after visiting them) may be participating in illegal activities. Who was hacked? Not you, not me…not even the bad guys ?
Underground banking? What? I don’t know where that comes from, but really? What financial transaction did you see disclosed above? Are you contending that Brian provided financial services without a license? That he deposited money with a know-to-be-illegal bank? ??
Tax evasion. On what income? Sigh… Seems to be a pattern here… Are you sure you are being serious? …or are you trying to be funny?
“cyberwarfare refers to any action by a nation-state to penetrate another nation’s computer networks for the purpose of causing some sort of damage.” Are you suggesting Brain is a nation-state?
I am not sure I understand your issues here, but your comments are just silly. Sorry.
There is no logic; he’s just trolling. The poster is probably someone who uses dump shops himself and wishes they weren’t being publicized.
As far as hacking goes… I believe he thinks signing up for a website that engages in illegal activities counts as “hacking.” Because, you know, there’s no way Brian (or a source/partner) could have just signed up for the service like anyone else would, they had to break in to get access.
These guys use security as good as a screen door on a submarine, then scream hacking when the water starts flooding in.
Im not going to prove you or show you with anything its not my job , but i will explain . whre is the logic !!
1 – if you think that if you buy all the stolen credit cards in the world u will save the world from cc fraud or like u said ( owner is actually saved from potential harm ) then you just dont know what you talking about at all . Why banks dont do that ? its way cheaper to buy them in bulk from the source then wait for a fraud to occur . i tell you why — Cos its illegal to buy stolen goods especially if you know that they are stolen . or maybe Krebs undercover agent who got license to “kill ” ?? cos if i do it it will be illegal .Right ?
2 * illegal activity * — read first paragraph again .
3 * Computer hacking *- Unauthorized access to a computer system entails approaching, trespassing within and retrieving data or otherwise intercepting and altering computer resources without consent. It broadly falls into the term ‘computer hacking’, because it attempts to bypass the security mechanisms of a system.
4 *Underground banking * — using a false credentials to open a banks accounts or an e-wallets or “By hiring someone with a false credential, that’s a misrepresentation and it’s a form of deception .
5 *Tax evasion – again , Tax hasnt been paid for them e-wallets or bank accounts that have been open using a false credentials .
6 *cyberwarfare — well i must agree i have nothing on this one 🙂 but we will continue to monitor his movements :0
I’ll try not to be too blunt about it but it seems like you’re upset that somebody has put a spotlight on this operation. Please stop making unfounded claims and butchering the English language.
lol @ “underground banking” and “cyberwarfare”
Thanks for the laughs, funnyman. Seriously, you made my day.
One of the funniest comment threads I’ve read in a while! Why wasn’t “dump me if you can Goodfellas” included on Kreb’s interview with NPR?
Odds are that this server isn’t on US soil, so probably not much to worry about.
The snipes on the kid’s English are a little poor. His English is way better than my Russian.
Brian – the placement of this comment might make it seem like I was saying you were sniping, that’s not what I meant. (I was referring to other comments in the thread.)
Knowing that would you try to engage with a Russian audience in an attempt to convince them of something that is clearly not true? It’s hard to sell a pack of lies at the best of times, even more so in a language you can only just speak. The fact that they are attempting to do just that is pretty amusing.
I doubt this guy is a kid, probably he is in his late 30s . His comments about big mac are from Eddie Murphy’s coming to america dated back to 1988. Movie used to be extremely popular in Russia.
I just did “underground banking” myself… I gave 20$ to my daughter so she can buy her favorite candy bar.
The crimes you list are irrelevant and imaginary. Brian Krebs broke my fridge in 1998 and has yet to replace my yogurt, now that’s a crime
I paid him in 1932 to paint my chicken coop and he still hasn’t done it.
I think I see the next great internet meme. 🙂
To be fair, that was just a butchered quote from the simpsons.
7) dealing with trolls like yourself
Were you born a branleur or did you become one after you bought your first modem ?
Hey guys,
Not familiar with american law but doesn’t that Goodfella guy has a point about buying stolen credit cards?
How is that not a crime?
Didn’t they charged this guy who “hacked” AOL servers and then warned them about their breach?… So intent is clearly not a factor.
Thx.
Where in the article does the author state that he bought stolen credit cards? That’s not something I do.
Curious also answered his own question about the law, with the AOL case, it was the hacking that was the problem. It’s the cyber equivalent of breaking into someone’s home, office, or car. And we know that Brian would never do any of the above even for a story. Of course, he doesn’t need to with the crazies out there.
Oh, terribly sorry. The impression I got from the article combined with the comments led me to believe that normally some cards are/were beign purchased (Not necessarily in this instance but generaly for validity purposes, like an investigator who buys drugs so that the other party won’t claim that he was just joking), especially the guys who were arguing how buying said cards is a good thing since it takes them out of circulation…
Anyway, thank you for the response.
Good luck!
Shops like this have existed since the late 1990s, although primarily through private/encrypted chat services such as Internet Relay Chat. What’s astonishing is that black markets, such as this carding shop, Silk Road, and so forth, have a higher customer service rating than the nation’s top legitimate retailers.
All of the ‘bases’ are in the slideshow are from the English speaking world. Is this reflective of the market, or were they chosen to illustrate the market to us English speaking readers?
Oops. The above comment was supposed to refer directly to the article, not Richard Ward’s (intelligent) comment.
In the early 2000s/late 90s, it was almost strictly outside of the US. The few people I knew from the US that would buy these were caught. They would mail packages to drop locations (empty houses/etc). As far as Romanians, Russians, etc, I never heard of one getting in any kind of trouble from it. Then again, its been 14 years since I have talked to anyone in that community. The outside-US would typically sell to US buyers, because they couldn’t use the cards in their own countries anyways. I never understood the whole ordeal, too much risk with too little reward.
I only know of a few shops that are not in English. These tend to be *very* exclusive and invite-only, and in Russian.
I always enjoy your posts, and admit I find the commenting entertaining and often informative as well. As a layperson, it’s all a very user-friendly way to learn about cyber-security.
As for the McDumpals branding, it would be hilarious to see follow up posts detailing McD’s efforts going after the infringers. But otherwise – the “swipin’ it’ service mark receives 10 out of 10 stars on the Happiegrrl seal of approval, as I always appreciate wit and wordplay. However, the clown with a gun is a fail, IMO. Better would be Ronald with a serving tray of cards, alongside a burger fries and soda, perhaps. Or simply holding a stack of fanned cards as if offering goodies to the kids. The handgun, with it’s connotations of violence, is in extremely poor taste. That someone with the sense of humor to use the “I’m swipin’ it” tagline would also employ such base imagery gets no stars.
The site is selling stolen goods on a large scale and you’re worried about the connotations the image may project?
Worldly moral standard – +1 to Neej!
(NotHappie and Terrie are the same person) – Neej, I just happen to appreciate witty word usage, and have an interest in branding. I leave it up to investigative journalists like Krebs, and police authority types, to focus on what they do best – investigating, reporting and kicking asses. And yes, maybe I do have a little bit of ‘badboy’ in my bones, even if I am a girl.
I don’t condone the crimes being perpetrated, and I do my best to educate friends about buying electronics and luxe goods from online sources they cannot verify(such as Ebay “shops”). It’s amazing how many people have no idea whatsoever that they are part of the equation because they are purchasing the ill-gotten goods. So it may be that I am one step closer to being a “do right” than plenty of people who religiously abuse the cybercreeps in the comments section of these very posts.
Looks like “dump me if you can Goodfellas” knows about breaking laws and has a lot to say about it. I wonder why that is?
Great article by the way.
I prefer “Burger-Dump” , I get to have it my way, all the time :–)
It’s too bad that “dump me” didn’t use his time as a ‘guest of the state’ to work on his English writing skills.
Krebs,
Totally off topic but a new Java upgrade (Java 7 Update 60) is now available. Cue the usual blog post. 🙂
Yes, but I don’t believe this one has security updates. The next patch that includes security fixes should be the next quarterly patch update, which is due on July 15, 2014.
http://www.oracle.com/technetwork/topics/security/alerts-086861.html
Nice article, Brian.
“People often ask if I worry about shopping online. These days, I worry more about shopping in main street stores. McDumpals is just one dumps shop, and it adds many new bases each week. There are dozens of card shops just like this one in the underground (some more exclusive than others), all selling bases from unique, compromised merchants.”
Point-of-Sales malware gives me nightmares.
Ive gone back to cash because of stuff like this…. I feel so late 90s now
“Will that be 10,000 credit cards with extra large fries sir?”
Nice article, Brian, as usual 🙂
I’m wondering about POS systems: Target and the other (rather large) retailers you wrote about were running their own systems, or rather custom ones, connected to the shop network and IS as well as to the bank’s, AFAIK.
What about smaller, independent retailers who are using POS systems provided by their bank? Do you know about breaches on bank-issued POS systems (only connected to the bank servers)?
dump me if you can Goodfellas, is that you Rescator? Send us another selfie!
Best comment 🙂
Brian,
Thanks again for the research. Really appreciate all the effort you put in to this. I sure hope it worth the headache of a few knuckleheads out there.
Thanks, Michael
did you happen to check out their lame irish pub front?
htxxs://mcdumpals.me/#!/page_home
it’s like a Potemkin Village, what a bunch of ciganin’s
@dump me if you can Goodfellas
it’s so great over there, the only thing these little boys can do is steal and lie and cheat the world over.
the nice thing about beginnings is there is always an end to come.
I definitely notice a trend toward using Square instead of dedicated POS terminals, especially in smaller retailers. It seems like this is actually a positive trend, in that the underlying platform has more security built in. But I haven’t quite figured out the other security implications surrounding this technology. Any informed comments about this? Just curious.
We (still?) don’t see this deployed in Europe.
Most of POS systems at small retailers are dedicated physical devices, sometimes connected to a cashing/order machine, and linked through phone/ADSL to the server of the bank which provided it.
Interesting. It sounds like the POS wouldn’t be the weak link in an attack, in this case.
Screw the card dump sites. I dumped my card about a year past.
I Don’t miss it or any of the hassle that is bundled with having to deal with BoA..
Wouldn’t it make sense for some organization, say a credit card issuer coalition of some sort, to buy these dumps (or listings, whatever they are called) as they come available, do a lookup and put a hold on or cancel any valid cards found in them?
It seems to me that if we could reduce the time that valid card info is available to minutes instead of hours or days that would quell the market.
And why don’t we have cardholder pictures on the card like we have on Drivers Licenses?
If they can print up a new card, whats to stop them from changing the picture too?
Wouldn’t that amount to hackers just plain extorting/blackmailing the banks? Oh, you hacked a retailer, let me pay you 20$ per record for a thousand records. It may help determine the common point of origin more quickly, it might not. I’m not privy to the inner workings of bank anti-fraud departments.
Great post, Brian. And, I must admit that the surprise guest (Dump me) was quite the comedian, very Jose Jimenez from Ed Sullivan years ago. Keep ’em rolling. Mahalo from the islands (for now)!
Incredible article thank you for the insight. It’s interesting to read the network that had spun off and how they are policing their own. Interesting perspective that the stolen don’t want to get ripped off?!
No worries, the gubmint is creating an uber database with ALL your info that no one can break into, right?
http://washingtonexaminer.com/new-federal-database-will-track-americans-credit-ratings-other-financial-information/article/2549064
The hell with it lets just post or SS #s online. Not like it’s going to do a lot of us any good anyways. Yes, this is sad. Technology is going to change the way this world spins. I disagree with where the internet is taking us. Too many times have I considered putting less and less info up. In all reality the best way to protect is less participation. Nowadays all one needs is a Google or facebook login and they can sign into half the sites you use on a daily basis. When I call the bank and they ask me for the acct # I don’t know. They tell me the secret it’s on the top of your statement. Where is that statement??? Oh Yeah! I signed up for paperless it’s in my email which has been hacked into a few times in 10 years. Maybe we should start wasting paper again I don’t think anyone’s stolen my mail since the 80’s.
Great article as always. Slideshow is good. Do you have a version in PDF or Powerpoint ?
Thanks
Naive question here: once someone purchases a batch of stolen CC#s, how do they go about printing the cards to use them in a retail store? Or do they just shop at big box retailers online?
Thanks!
There are both underground stores of printed (for most US banks) and plain CCs ready for encoding. Engraving is probably homemade by the carders. At least device for CC engraving is pretty simple and available for legal purchase.
I formerly worked as an assembly engineer for one of the major embosser manufacturers. Equipment is equipment, just like the adage about a gun not being illegal (in the US) in itself. Kaneda is correct regarding legal avenues for obtaining used or obsolete – yet functional – embossers.
As to the card stock; how many times does a merchant ~actually~ look at your card? Especially at retailers such as Target, where you hold onto your own card while you swipe it. They never look at the back, and it’s easy enough to palm the front so they can’t see it. A smart carder would not shop at brick and mortars where they had to hand over a white blank.
Lastly, photos: It would raise the bar on capital needed to reproduce cards with a decent picture, but refer to my paragraph above. Training minimum wage hourly workers to become security monitors does not compute.
This is only getting worst. Down to gas pumps, ATM machines, cash registers. The funny part is the theft isn’t all that difficult. You could have a cashier plug a small device in from the credit reader to the register in seconds. At the end of an 8 he shift he probably has a few hundred cards. I would think the sale would be more difficult considering the risk on advertisement and time. I’ve trolled a few communities out there as well just to learn and understand. I will admit the internet is becomming more and more organized and as more good things come out of technology more methods to manipulate tend to pop up. As I always say, If you can write it and design it, you can manipulate or break it.
Aaron, same way Costco issues you a membership card lol. Dosent matter what kind of card it is it can be a hotel key card as long as it has a magnetic swipe they can load the data from a computer to the card. Another example the sameway a hotel clerk loads the data on a room to your key card. What these guys do isn’t hard or smart. It’s not rocket science. The world lacks understanding on computers and technology but as time progresses more and more people will understand and these types of crimes will happen more and more often.
More screenshots of the shop:
http://protectyournet.blogspot.com/2014/06/mcdumpals-im-swipin-it_5.html
Possession ( or the production) of stolen credit card numbers is unlawful, they are contraband, no different than CP.
I see that in this post Brian mentioned Rescator as having been directly involved in the Target heist (as First-Hand Base), but didn’t catch any previous mention of discovering that connection. I did miss reading a few posts in the last month – if that point was made, can someone point me to the post? Or, Brian, was this something you were able to verify well enough to satisfy your belief it was the case, but never posted about it?
Hrm. Maybe you missed the story about how the malware found on the compromised Target cash registers had the string “Rescator” in it? 🙂
http://krebsonsecurity.com/2014/01/a-closer-look-at-the-target-malware-part-ii/
I’m pretty sure there are other smoking guns, but I’m multi-tasking atm.
Oh yeah, I do remember that post. Thanks for taking the time to reply and link it.
Bah…..nothing but ne’er do well drivel
goodfella works for the cia, don’t you?
why don’t you roll over and give us a fall guy to prove you are relevant?
Working in LP at a store I like it when the bad guy uses an account from a local person: it’s a lot easier to get PD to go after the bad guy when the victim is local or a local institution than when they are across the country. I also like it when they use their own cars: car plates are great to have for a photo lineup, leads to a nice guilty plea.
Like your work, Brian, keep it up! I do some basic corporate data security but this stuff is fascinating.
I try to get some concise stuff out on my facebook, especially about ATM hacks and the like, don’t want my grandma getting ripped off, or the geeks I went to high school with either.