The past few years have witnessed a rapid proliferation of cheap, Web-based services that troublemakers can hire to knock virtually any person or site offline for hours on end. Such services succeed partly because they’ve enabled users to pay for attacks with PayPal. But a collaborative effort by PayPal and security researchers has made it far more difficult for these services to transact with their would-be customers.
By offering a low-cost, shared distributed denial-of-service (DDoS) attack infrastructure, these so-called “booter” and “stresser” services have attracted thousands of malicious customers and are responsible for hundreds of thousands of attacks per year. Indeed, KrebsOnSecurity has repeatedly been targeted in fairly high-volume attacks from booter services — most notably a service run by the Lizard Squad band of miscreants who took responsibility for sidelining the Microsoft xBox and Sony Playstation on Christmas Day 2014.
For more than two months in the summer 2014, researchers with George Mason University, UC Berkeley’s International Computer Science Institute, and the University of Maryland began following the money, posing as buyers of nearly two dozen booter services in a bid to discover the PayPal accounts that booter services were using to accept payments. In response to their investigations, PayPal began seizing booter service PayPal accounts and balances, effectively launching their own preemptive denial-of-service attacks against the payment infrastructure for these services.
PayPal will initially limit reported merchant accounts that are found to violate its terms of service (turns out, accepting payments for abusive services is a no-no). Once an account is limited, the merchant cannot withdraw or spend any of the funds in their account. This results in the loss of funds in these accounts at the time of freezing, and potentially additional losses due to opportunity costs the proprietors incur while establishing a new account. In addition, PayPal performed their own investigation to identify additional booter domains and limited accounts linked to these domains as well.
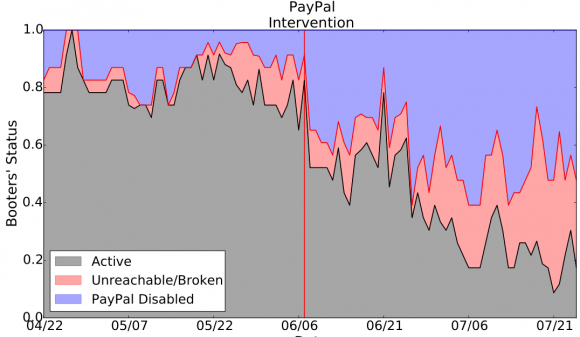
The efforts of the research team apparently brought some big-time disruption for nearly two-dozen of the top booter services. The researchers said that within a day or two following their interventions, they saw the percentage of active booters quickly dropping from 70 to 80 percent to around 50 percent, and continuing to decrease to a low of around 10 percent that were still active.
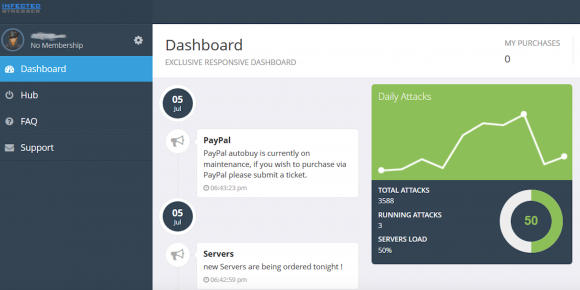
While some of the booter services went out of business shortly thereafter, more than a half-dozen shifted to accepting payments via Bitcoin (although the researchers found that this dramatically cut down on the services’ overall number of active customers). Once the target intervention began, they found the average lifespan of an account dropped to around 3.5 days, with many booters’ PayPal accounts only averaging around two days before they were no longer used again.
The researchers also corroborated the outages by monitoring hacker forums where the services were marketed, chronicling complaints from angry customers and booter service operators who were inconvenienced by the disruption (see screen shot galley below).
A booter service proprietor advertising his wares on the forum Hackforums complains about Paypal repeatedly limiting his account.
Another booter seller on Hackforums whinges about PayPal limiting the account he uses to accept attack payments from customers.
“It’s a shame PayPal had to shut us down several times causing us to take money out of our own pocket to purchase servers, hosting and more,” says this now-defunct booter service to its former customers.
As I’ve noted in past stories on booter service proprietors I’ve tracked down here in the United States, many of these service owners and operators are kids operating within easy reach of U.S. law enforcement. Based on the aggregated geo-location information provided by PayPal, the researchers found that over 44% of the customer and merchant PayPal accounts associated with booters are potentially owned by someone in the United States.
ROOTED BOOTERS
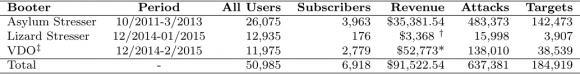
The research team also pored over leaked and scraped data from three popular booter services —”Asylum Stresser,” another one called “VDO,” and the booter service referenced above called “Lizard Stresser.” All three of these booter services had been previously hacked by unknown individuals. By examining the leaked data from these services, the researchers found these three services alone had attracted over 6,000 subscribers and had launched over 600,000 attacks against over 100,000 distinct victims.
Like other booter services, Asylum, Lizard Stresser and VDO rely on a subscription model, where customers or subscribers can launch an unlimited number of attacks that have a duration typically ranging from 30 seconds to 1-3 hours and are limited to 1-4 concurrent attacks depending on the tier of subscription purchased. The price for a subscription normally ranges from $10-$300 USD per a month depending on the duration and number of concurrent attacks provided.
“We also find that the majority of booter customers prefer paying via PayPal and that Lizard Stresser, which only accepted Bitcoin, had a minuscule 2% signup to paid subscriber conversion rate compared to 15% for Asylum Stresser and 23% for VDO 1, which both accepted PayPal,” they wrote.
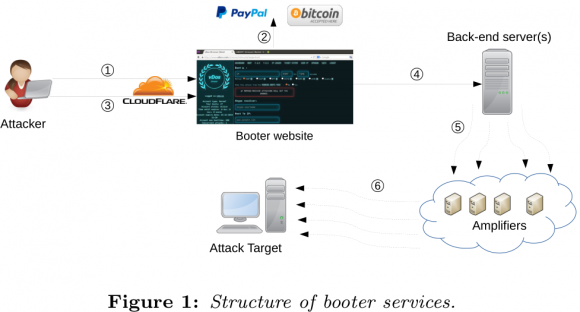
The research team found that some of the biggest attacks from these booter services take advantage of common Internet-based hardware and software — everything from consumer gaming consoles to routers and modems to Web site content management systems — that ships with networking features which can easily be abused for attacks and that are turned on by default.
Specific examples of these include DNS amplification attacks, network time protocol (NTP) attacks, Simple Service Discovery Protocol (SSDP) attacks, and XML-RPC attacks. These attack methods are particularly appealing for booter services because they hide the true source of attacks and/or can amplify a tiny amount of attack bandwidth into a much larger assault on the victim. Such attack methods also offer the booter service virtually unlimited, free attack bandwidth, because there are tens of millions of misconfigured devices online that can be abused in these attacks.
Finally, the researchers observed a stubborn fact about these booter services that I’ve noted in several stories: That the booter service front-end Web sites where customers go to pay for service and order attacks were all protected by CloudFlare, a content distribution network that specializes in helping networks stay online in the face of withering online attacks.
I have on several occasions noted that if CloudFlare adopted a policy of not enabling booter services, it could eliminate a huge conflict of interest for the company and — more importantly — help eradicate the booter industry. The company has responded that this would lead to a slippery slope of censorship, but that it will respond to all proper requests from law enforcement regarding booters. I won’t rehash this debate again here (anyone interested in CloudFlare’s take on this should see this story).
In any case, the researchers note that they contacted CloudFlare’s abuse email on June 21st, 2014 to notify the company of the abusive nature of these services.
“As of the time of writing this paper, we have not received any response to our complaints and they continue to use CloudFlare,” the paper notes. “This supports the notion that at least for our set of booters CloudFlare is a robust solution to protect their frontend servers. In addition, crimeflare.com has a list of over 100 booters that are using CloudFlare’s services to protect their frontend servers.”
A copy of the research paper is available here (PDF).




This was part of online life back in the day with Yahoo chatrooms. I guess it’s advanced a bit since those days. It still seems like a pointless childish thing to do though.
great work
Keep your friends close, but your enemies closer…
It just goes to show that these script kiddie like mentalities do not show any forward thinking what so ever. I won’t go into details, but the way they manage things shows their age or intellectual level. =X
So they don’t make any money, so they close shop. That’s half their worries. Will the Feds become interested in all of this documentation? Probably. These places also need to pay the IRS, and I highly doubt they do. This can get ugly for those that have operated a DDoS style website. The email addresses and payment locations and account data of the owners and users of these sites is a treasure trove of data. If it can be tied back to individual gamers, they should receive an account ban for participating in this activity.
If they paid to DoS website, they should have a visit by the authorities. I am sure the website would like some compensation from the losses incurred. Even though there is little chance to redeem such losses, it ties the crook up in the court system and disrupts their daily life. A little of their own crappy medicine comes back to bite them.
This world gets a teenie bit better each day when several sites like this get flushed down the crapper – where they belong.
Except your forgetting one big flaw, 90% of the owners running these services live in countries such as Russia or Israel. Nothing will happen to them.
This is simply not true. I can tell you just anecdotally that a great number of these are run by kids or young men in the United States. Search my site on several stories where I tracked a bunch of them down and interviewed them. Also, see that the researchers quoted in this story said based on PayPal data they estimate that at least 40 percent of the booters they looked at were run by people in the US.
Brian is absolutely correct. At crimeflare.com/cfusers.html there is a percentage breakdown by country of 750,000 direct-connect IP addresses we’ve recorded since 2012, that use CloudFlare nameservers. The entire list shows 151 countries. But all you need is the top of the list to tell the story, and it looks like this:
56.291 UNITED STATES
6.098 GERMANY
5.370 UNITED KINGDOM
4.917 NETHERLANDS
4.537 FRANCE
3.210 CANADA
1.851 SINGAPORE
1.768 AUSTRALIA
1.480 JAPAN
1.204 TURKEY
1.110 RUSSIA
0.897 IRELAND
0.834 VIETNAM
0.742 HONG KONG
…
For three years it has always looked like this. We recheck all of our data twice a month and delete any domains that no longer use CloudFlare nameservers.
If U.S. cybercrime fighters had their act together, the web would be in much better shape. And the rest of the world might be grateful.
I just skimmed over a portion of what is listed. It reads like a who’s who in the online spamming industry.
Thanks for a good read, Brian; btw the SSDP link is broken. (Found the story anyway.) 😉
Crimeflare.com has another page that shows over 400 “carder” domains that hide behind CloudFlare. And if booter sites and carder sites don’t float your boat, CloudFlare also protects several dozen sites that recruit for ISIS. CloudFlare’s CEO Matthew Prince refuses to take any action.
Cloudfair really have a lot to answer for, hiding behind the “who are we to say what is right from wrong” is just plain lazy…let alone unethical.
This stance just does not float…especially when they have such a clear conflict of interest!
What is “Cloudfair?”
I wonder what certain booter owners will do. Obviously the ones on Hackforums will be crippled but stuff on the deep web and upcoming stressers will manage. People like http://vstress.net/ are newer. Also vDos always does well. They have also been around for quite some time. Paypal is attempting to limit accounts but people will end up resorting to BTC because they have no choice.
Dear Brian, why you don’t write about your old friend Eugene who like to cheat his colleagues? It was a pity to learn about his fake antivirus from Reuters but not from my favourite blog
I think we need to be careful in pointing the finger at CloudFlare in this context.
Remember that their sign-up system is almost completely automated and they do not have a human being manually evaluating the legitimacy (or lack thereof), of applicants signing up for CloudFlare DoS protection (ironically, of course, some of the miscreants involved in the story are using CloudFlare, which is an anti-DoS service, to protect them from being DoS’ed themselves as they DoS their enemies… no honor among thieves, obviously).
For those of you who don’t like how CloudFlare is operating in this regard, I’d point out the example of how well YouTube’s “automated ‘infringing content’ removal system” — installed at the insistence of the U.S. entertainment industry — is working, with its many stupid false positives and utter failure to stop “copyright infringement”. An attempt to have services like CloudFlare implement some kind of AI-based screening mechanism of this type would inevitably lock many otherwise legitimate sites from accessing CloudFlare at all — which would simply encourage someone else to set up a competing anti-DoS service that wasn’t so inflexible.
Perhaps CloudFlare could do a better job of blacklisting these miscreants, once someone has made a specific (and credible) complaint against them (understanding, all the while, of the possibility of malicious complaints designed to DoS sites through abuse of that mechanism). But either way you are going to get into a game of Whack-A-Mole and that’s not the business that CloudFlare (or any cloud service) is really in.
Right,
And no ones reads your email but the NSA.
“…they do not have a human being manually evaluating the legitimacy (or lack thereof), of applicants signing up for CloudFlare DoS protection…”
exactly!
“…that’s not the business that CloudFlare (or any cloud service) is really in.”
That’s what they claim anyway.
————————————-
Your effort to deflect away from Cloudflare actually develops a basis for the argument against it.
Sure, the sign-up process is automated, but the reporting process can’t be. As in Brian & the security researchers contacted them about the clearly illegal services that are using their company’s services, and they have, so far, done little or nothing.
Their censorship defense seems specious at best, only a card carrying member of the birch society would believe it.
You can either play the whack-a-mole game and have an automated sign-up process, or you can have a human-based sign-up process and whack the moles before they’re signed up. There is no third option.
36k over a year and a half, sounds like crime doesn’t pay.
For that particular line item, I think its probably due to the “people in charge” utilizing free sources to DDoS something. It was probably low cost DoS’ing, since they could bring in the followers, even young kids to show they had some sort of following.
Its one of those NON-entrepreneur sites that have no direction or desire to become big, only their ego”testical” crowings and childish acts were important – to them.
Anybody knows what happens with the funds frozen by PayPal? (In that case)
I can’t see any conflict of interest for cloudflare, rather a strong correlation between keeping stresser etc sites online and their own business model.
As long as they do in fact respond to correctly filed legal demands for removal of a site, they’re going as far as the law requires, and they do, so why would they ever go further?
Seriously, These misguided guys need a lot of fresh air and yoga.
Cloudflare seems to be saying that they will knowingly harbor illegal activity, and until the police raid, will do nothing about it.
As I’ve related on similar cases in the past, it is like a bar owner knowingly allowing drug activity. They will end up having their property seized at some point, and yes, the legitimate customers, if any, will suffer just as much as a mob restaurant being seized.
A bar owner can’t use a defense that it wasn’t their business to stop known illegal activity, nor do i expect that it will work for cloudflare in the long run.
If cloudflare has a legitimate business model it appears to be grossly mismanaging the problem, and their response should concern their employees, stakeholders, investors, etc. due to the potentially catastrophic impact on their business. That said, if they feel supporting illegal activity is more important than staying in business then that says quite a bit about their business model (like the seedy bar that can’t stay in business without the drug deals in the back room).
So, if they do have a legitimate business model it’s a bit less than ‘business savvy’ to mess it up with miscreants in the back room just as a legit bar is poorly run if it puts a legit business at risk by knowingly allowing illegal activity.
Cloudflare making the case they are a neutral utility suggests they want to be regulated like a utility. Cloudflare should be careful or they may get what they are asking for with strict regulations…i doubt they want that…far more likely they want it both ways, no accountability and no regulations.
Lastly, it suggests that cloudflare isn’t what the psychology folks call ‘self actualized’. They don’t seem to be the company they think they are, which is all too common. Eg. I think i look like brad pitt, and i love how i look will be a problem if others simply don’t think i look like brad pitt, particularly with the girl at the bar that likes mr pitt.
Nobody should be surprised that Cloudflare is quite willing to help preserve the problem to which it sells a solution.
+1
So simple a solution and so late employed (reminds me of Brian´s accounts in “Spam nation”): Go after the money and cut them off from payments!
Also, if criminal investigators are not interested, contact customs/tax authorities? We have often found that the customs investigators (who also handle tax evasion) have more resources and more “bite” and even if one can´t get this scum on criminal charges, tax evasion is a very effective bat to clobber them with.
Booter owners will resort to verifying fake, international PayPal “stealth” accounts with VCCs and laundering the funds with Bitcoins or to more PayPal accounts.
Booters will never die.