ATM “jackpotting” — a sophisticated crime in which thieves install malicious software and/or hardware at ATMs that forces the machines to spit out huge volumes of cash on demand — has long been a threat for banks in Europe and Asia, yet these attacks somehow have eluded U.S. ATM operators. But all that changed this week after the U.S. Secret Service quietly began warning financial institutions that jackpotting attacks have now been spotted targeting cash machines here in the United States.
To carry out a jackpotting attack, thieves first must gain physical access to the cash machine. From there they can use malware or specialized electronics — often a combination of both — to control the operations of the ATM.
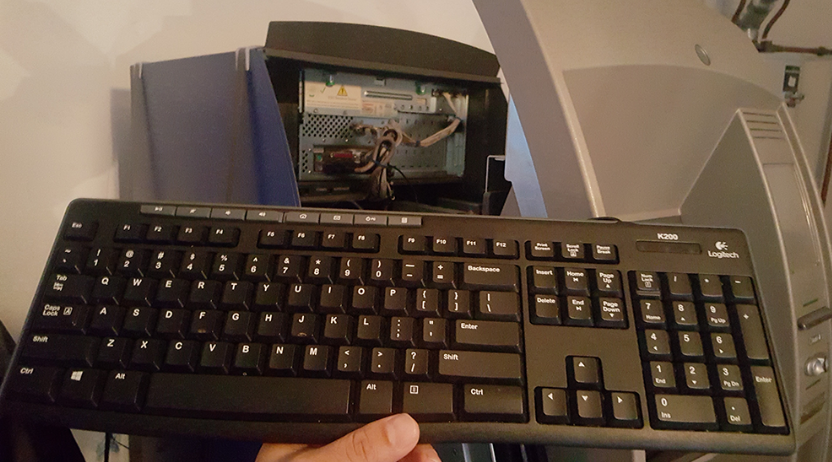
A keyboard attached to the ATM port. Image: FireEye
On Jan. 21, 2018, KrebsOnSecurity began hearing rumblings about jackpotting attacks, also known as “logical attacks,” hitting U.S. ATM operators. I quickly reached out to ATM giant NCR Corp. to see if they’d heard anything. NCR said at the time it had received unconfirmed reports, but nothing solid yet.
On Jan. 26, NCR sent an advisory to its customers saying it had received reports from the Secret Service and other sources about jackpotting attacks against ATMs in the United States.
“While at present these appear focused on non-NCR ATMs, logical attacks are an industry-wide issue,” the NCR alert reads. “This represents the first confirmed cases of losses due to logical attacks in the US. This should be treated as a call to action to take appropriate steps to protect their ATMs against these forms of attack and mitigate any consequences.”
The NCR memo does not mention the type of jackpotting malware used against U.S. ATMs. But a source close to the matter said the Secret Service is warning that organized criminal gangs have been attacking stand-alone ATMs in the United States using “Ploutus.D,” an advanced strain of jackpotting malware first spotted in 2013.
According to that source — who asked to remain anonymous because he was not authorized to speak on the record — the Secret Service has received credible information that crooks are activating so-called “cash out crews” to attack front-loading ATMs manufactured by ATM vendor Diebold Nixdorf.
The source said the Secret Service is warning that thieves appear to be targeting Opteva 500 and 700 series Dielbold ATMs using the Ploutus.D malware in a series of coordinated attacks over the past 10 days, and that there is evidence that further attacks are being planned across the country.
“The targeted stand-alone ATMs are routinely located in pharmacies, big box retailers, and drive-thru ATMs,” reads a confidential Secret Service alert sent to multiple financial institutions and obtained by KrebsOnSecurity. “During previous attacks, fraudsters dressed as ATM technicians and attached a laptop computer with a mirror image of the ATMs operating system along with a mobile device to the targeted ATM.”
Reached for comment, Diebold shared an alert it sent to customers Friday warning of potential jackpotting attacks in the United States. Diebold’s alert confirms the attacks so far appear to be targeting front-loaded Opteva cash machines.
“As in Mexico last year, the attack mode involves a series of different steps to overcome security mechanism and the authorization process for setting the communication with the [cash] dispenser,” the Diebold security alert reads. A copy of the entire Diebold alert, complete with advice on how to mitigate these attacks, is available here (PDF).
The Secret Service alert explains that the attackers typically use an endoscope — a slender, flexible instrument traditionally used in medicine to give physicians a look inside the human body — to locate the internal portion of the cash machine where they can attach a cord that allows them to sync their laptop with the ATM’s computer.

An endoscope made to work in tandem with a mobile device. Source: gadgetsforgeeks.com.au
“Once this is complete, the ATM is controlled by the fraudsters and the ATM will appear Out of Service to potential customers,” reads the confidential Secret Service alert.
At this point, the crook(s) installing the malware will contact co-conspirators who can remotely control the ATMs and force the machines to dispense cash.
“In previous Ploutus.D attacks, the ATM continuously dispensed at a rate of 40 bills every 23 seconds,” the alert continues. Once the dispense cycle starts, the only way to stop it is to press cancel on the keypad. Otherwise, the machine is completely emptied of cash, according to the alert.
An 2017 analysis of Ploutus.D by security firm FireEye called it “one of the most advanced ATM malware families we’ve seen in the last few years.”
“Discovered for the first time in Mexico back in 2013, Ploutus enabled criminals to empty ATMs using either an external keyboard attached to the machine or via SMS message, a technique that had never been seen before,” FireEye’s Daniel Regalado wrote.
According to FireEye, the Ploutus attacks seen so far require thieves to somehow gain physical access to an ATM — either by picking its locks, using a stolen master key or otherwise removing or destroying part of the machine.
Regalado says the crime gangs typically responsible for these attacks deploy “money mules” to conduct the attacks and siphon cash from ATMs. The term refers to low-level operators within a criminal organization who are assigned high-risk jobs, such as installing ATM skimmers and otherwise physically tampering with cash machines.
“From there, the attackers can attach a physical keyboard to connect to the machine, and [use] an activation code provided by the boss in charge of the operation in order to dispense money from the ATM,” he wrote. “Once deployed to an ATM, Ploutus makes it possible for criminals to obtain thousands of dollars in minutes. While there are some risks of the money mule being caught by cameras, the speed in which the operation is carried out minimizes the mule’s risk.”
Indeed, the Secret Service memo shared by my source says the cash out crew/money mules typically take the dispensed cash and place it in a large bag. After the cash is taken from the ATM and the mule leaves, the phony technician(s) return to the site and remove their equipment from the compromised ATM.
“The last thing the fraudsters do before leaving the site is to plug the Ethernet cable back in,” the alert notes.
FireEye said all of the samples of Ploutus.D it examined targeted Diebold ATMs, but it warned that small changes to the malware’s code could enable it to be used against 40 different ATM vendors in 80 countries.
The Secret Service alert says ATMs still running on Windows XP are particularly vulnerable, and it urged ATM operators to update to a version of Windows 7 to defeat this specific type of attack.
This is a quickly developing story and may be updated multiple times over the next few days as more information becomes available.




I must be missing something – If they use a master key or other technique to gain physical access to attach their device, can’t they just remove the cash at that point?
No .. keys provide access to the area the ATM is in. The cash is in a vault not opened by keys.
Good job by fbi to report this to banks.
Glad to hear the fbi is continuing to be forward leaning and sharing information during this difficult time.
Clyde, I can’t tell if you’re trying to needle the Secret Service or if you didn’t read the story, but the FBI was not involved here as far as I know.
I didn’t mention it in the story, but perhaps I should have: The original mission of the Secret Service when it was created in the 1800s was to safeguard the U.S. currency from counterfeiters. Only after a few presidents were assassinated did their mission grow to include protection of the president and other dignitaries. Both are their dual roles today.
https://www.secretservice.gov/about/history/events/
The Hacker Crackdown is an excellent book that goes into the jurisdiction of the Secret Service and a whole lot of other interesting things.
https://en.m.wikipedia.org/wiki/The_Hacker_Crackdown
I wish I was even half as smart as the people who are able to create these kinds of electronic thievery devices. (As the grown child of a mother who spent most of her life in prison, I also have absolutely no desire to follow her life path.)
Why? So you could prevent it? O
hi Brian
I wonder how challenging it is to physically plug in an external keyboard. I know most ATM’s have multiple cameras watching, but must still take some time for the mules to do this?
Do you think they coverup the security cameras while using the endoscope looking for where to plug in the keyboard? or is the entire process so quick they do this in a matter of minutes and run?
Great investigation….thanks again
Scott Schober
Author of Hacked Again
http://www.ScottSchober.com
I know of some banks that have secondary security cameras not inside the ATM.
Almost certainly they’d cover the cameras as those ATM cameras are nearly always record only – not monitored – so the chance of getting caught in the act for that are pretty much zero.
I found a “NY Times” article by MARC SANTORA, on MAY 9, 2013 interesting. He reported that thieves starting on Feb 19, 2013 struck 2904 ATMSs in New York city alone over a 10-hour period. Their take was $2.4 million.
My question is not simple: is it a variant of what you’re writing of here or was it done differently?
I work in ATM infosec at a regional bank in the MidAtlantic market: we were contacted directly by the Secret Service (not FBI). We also have a Task Force in the area fighting these Romanian skimming rings. They’re cashing out millions every month up here and funding terrorism with it.
These ATMs still running XP are also missing other encryption protocols at the cash dispenser that can be compromised by the Diebold exploit revealed this past summer.
Diebold has been a steady & trustworthy ATM OEM for years, and now they also own the software side with the Wincor merger. But lately their security track record is pretty abysmal. If DN (Diebold-Nixdorf) doesn’t get their act together banks are going to be dropping them in favor of Hyosung’s newly aggressive push. BoA just ordered hundreds of Hyosungs instead of DN for this reason alone.
Why would Romanian skimming rings fund terrorism? Surely they would just keep the cash!
Quick question,
With the risk of this situation, especially over 4 + yrs, why aren’t software patches just pushed?
Also, seems simple enough that if one ATM is hit, it’s immediate significant loss of cash should notify other Atms in the network and begin notifying the alarm companies central station as if someone threw a brick at a window.
This seems easy to resolve. I find it ridiculous. What am I missing?
Most Windows builds supplied by NCR or Diebold are custom jobs. Skinny thin-client, enterprise style versions. They don’t even have a version of Internet Explorer or any other browser on there. They’re not connected to the internet, but connected to a VPN that’s encrypted from the ATM back to the host systems.
They run a custom ATM terminal software on top of that which is what customers interface with in order to make transactions.
Additionally there are a lot of customized software components that connect to the cash dispenser, depository module, and other functions of the ATM that are certainly not just a generic Windows software update. Those are supplied by the hardware manufacturers.
It takes the perfect recipe, an alphabet soup, to run an ATM and not run into problems with all those different components.
So Banks don’t push regular updates because updates tend to break the terminal software unless they do a lot of testing or customization to the patches themselves. Instead normally the updates are installed on a quarterly basis. And there’s no need to update anything for Microsoft Office or any other components software because they’re not installed in the ATM. Remember, these are not full fledged consumer versions of Windows running on these machines. They strip out the unnecessary DLL’s.
Add in the terminal security software that are out there on the ATMs, and you have both intrusion protection and white listing of executable software. Add hard drive encryption, router encryption & PIN pad encryption and Bob’s your uncle, most Bank ATMs are pretty damn secure. It’s the idjits not running HDE & WinXP that are the most vulnerable to this specific attack. Or don’t have Diebold’s cash dispenser encryption update (and many US machines don’t).
Now … Take the Independent Business operators who own their own ATMs, they are responsible for updating them individually. Not Microsoft not the manufacturer. Most of those machines are Windows CE, but not all. And most of those folks don’t invest in those ATMs and don’t load much cash and don’t have security on them. Updating or patching those things is almost unheard of. Yet these are the folks who charge the highest fees. In the poorest communities. Which is why you should never use an independent ATM.
not only they are funding terrorism, they also funded Trump’s campaign and helped make America great again!
I think that’s about the same thing, at the end of the day. Trump is a traitor to the people, the nation, and the Constitution and should face the firing squad. People like him do way more damage to the country than any “terrorist” ever possibly could.
It’s people like you that hijack a conversation and make it political that make America worst again.
It was who, who started this with an unverified accusation of terrorist-funding by romanian criminals?
It the new all-purpose weapon to blame everything on terrorists.
Our task force literally arrested 2 Romani’s on Friday. They are directly tied to terrorism, so says the Secret Service & FBI who are in the Homeland Security task force. These aren’t assumptions or an attacking of any specific kind of people, these are blatant provable, facts.
Interesting that your statements are followed up with fake newsters.
Wait, are we talking about Romanians or Roma? The first is a nationality. The second, commonly (but incorrectly) called Gypsies, is an ethnicity. Romanians are from Romania, while Roma are from many countries.
So, which is it? Are these Romanian gangs or Roma gangs?
http://www.theadvocate.com/baton_rouge/news/crime_police/article_00f8f9ca-045e-11e8-a48a-3bbac0562f81.html
Romanians. Not Roma (who are historically linked to Pakistan, actually)
http://www.theadvocate.com/baton_rouge/news/crime_police/article_00f8f9ca-045e-11e8-a48a-3bbac0562f81.html
Romanians.
Roma is also historically linked to India & Pakistan.
“They are directly tied to terrorism, so says the Secret Service & FBI” is only proof that that is what the Secret Service and FBI told you, it is not proof the crimes are related to terrorism.
Your name says it all.
Why are you so defensive of these scum?
http://www.business-review.eu/news/romanian-citizen-detained-for-isis-propaganda-suspected-of-terror-plot-141734
http://jamaica-gleaner.com/article/lead-stories/20170418/atm-users-being-warned-about-romanian-scammers
Getting skewered by truthful accuracy is a bit embarrassing, isn’t it…?
Ah, Godwin’s Law in motion. Actually, the subroutine
quick, trot out the “terrorism” angle…try to get some free sympathy and maybe either free government services, protection or out and out a full refund from the taxpayers!
banks are all the same…happy as hell to stick it to the common man with insane fees, all kinds of rules about what customers can do with their own money, customer service that can leave you on hold for hours, banks with with nothing but idiot tellers and machines, …yet at the first sign of trouble, they want the government to bail them out and cover all their mistakes. leeches, pure and simple. cryptocurrencies are on the way to save mankind from your tyranny, so you better go back to school
I’m ashamed to say I’ve been thinking the same thing every time I hear about this…… As long as it’s not hurting a direct customer, I’m sort of shrugging. They waste no time sticking it to the little guy for profits so…..
Just like any other for profit business, banks are in business to make a profit. If you want a service/product from any other company you find what works best for you and you buy it. If you want easy and safe access to your money get a bank account, otherwise bury it in the backyard.
Indirectly it does affect you.
Anything that makes it more expensive (i.e. reduces profits) of business, those costs are passed onto their customers. Increased bank fees, lower interest rates on deposits/investments in the banks, higher interest rates on credit from the banks, higher ATM fees, and so on.
Bad guys “Funding Terrorism” seems to be the popular mantra for all these govt agencies to get federal homeland security funding. My little city has had a “gang problem” from a totally non existent gang (8 guys sent to prison decades ago), yet this gang shows up in federal database and the local PD gets task force funding for it. I wish law enforcement would at least try to be HONEST when fighting dishonesty. Instead they are part of the problem.
Any company that is still running XP Embedded on ATMs is guilty of gross negligence, period. Hopefully their insurance underwriters will realize this, and not cover their losses due to these attack’s. Stupid, stupid, stupid.
So while everyone is tripping on immigration, we allowed how many WHITE Russians and eastern Europeans into our country, and believe me there was a lot of them reading up on everything Jewish so they could get into America. And now they run the biggest organized crime syndicate since La cosa nostra in our country. We are a young country in comparison to theirs and they just said ” oh ,are you kidding me this is like taking candy from a baby” (with a Russian accent) and this is exactly what they’ve done! Now don’t get me wrong, my husband is first generation Russian , when they still had horse and carriages in the streets of N.Y. But and this is a big BUT, this does not surprise me. I remember a 60 minute expose about how these people ran out the owner of a gas station. Took it over, and would add 1 or 2 cents to the price of gas. If my memory serves me right. somehow (remember this is N.Y.) they figured out a way to do it so the skimming wasn’t detected for years . Koreans in L.A. turn over mkts. within a certain time so they don’t have to report their earnings.. and just trade them back and forth. A woman who had children who grew up with my kids, had a independent meat mkt.. in her store in the marina, sold their store and told the buyer the meat mkt. was part of the deal. We are ripe pickings for certain immigrants but alas the buffoon we have as pres. seems to think that it’s only Black and Brown that are a detriment to our society. NNo, It’s people who are greed sloths like him! Just saying.
Anybody else aghast that ATMs are running Windows? An attack surface area like that combined with a bad track record…. Are embedded OS’s not a thing any more?
Absolutely ridiculous that any cash dispensing machine is running an operating system such as XP that has been past end of life for years! With the amount of bank (no pun intended) financial institutions have, you would think that they would invest money in developing a secure OS that is not easily amenable to hacking. It’s hard not to get into conspiracy theory trying to understand the management decisions that go into that lack, and why of all OS available, they choose Windows… [rolleyes]
The MTA MetroCard system uses Window XP, but it is a completely closed system – not connected to the internet at all.
Doesn’t matter, the problem is physical access. There are so many ways to get into NT-based Windows when you have physical access. And it’s not very easy to setup full encryption either, most solutions are tied to a network service (don’t get me started).
I’ve had to deal with this solution using Linux for the past decade and a half. It’s not flawless either, but it is a heck of a lot easier to lock-down, encrypt and other things. There is just not the boot-time flexibility in NT that one has with Linux, not even Embedded NT.
Many ATMs Ron Windows CE. There are absolutely 0 ATM that run Linux or any other operating system besides Windows proper, or Windows CE.
And yes there are thousands out there running Windows XP. Many small businesses own their own ATMs that have never upgraded them. Bank-owned ATMs, however, are all upgraded for the most part. Windows 10 won’t hit them until 2020. Not a single software provider for ATMs has a Windows 10 build ready.
Windows CE is long dead. Microsoft finally moved to an object build Windows NT model nearly a good decade. Unfortunately NT was never made very portable, because 85%+ of the Visual Studio base libraries are 32-bit x86-only. So it’s essentially a PC solution for the most part.
Again, the first, post-OS/2 ATMs were Linux-based. Both Diebold and IBM made those investments. The entire set-top market and most other embedded had gone either BSD (often VxWorks in the late ’90s and early ’00s, after NASA’s successes) or GNU/Linux as well (often Montavista HardHat throughout the ’00s, who based their builds off of the popular Red Hat releases). But it was the regional and smaller banks that balked at adopting Linux, believing Windows was easier to support.
Although both Diebold and IBM sold a number of Linux-based ATMs, they both jumpstarted Windows efforts, and they eventually took over, leaving little reason to keep Linux. Many were full up consumer Windows releases, and not even Embedded NT or, later, XP initially. And that right there is the biggest issue, because taskmgr.exe and other services are still running.
Anyone who has done Kiosk development with both ‘generic’ Windows and Linux can attest how limited anyone can block various services of the former, while having complete control of the latter. I remember one “household name” retail customer of mine (when I was with Red Hat Services, one of their few embedded engineers still left) gave me a list of requirements and I built out a customized build in just 36 hours. When non-techie executives came in, they kept asking, “How did you that?” They even brought techie assistants to try to ‘break into’ the kiosk I locked downed and completely skinned (right down to the boot screen) literally overnight.
The irony here is that I was one person, and not the 400 MS IE/Windows coders/scripters they had. And that’s the biggest problem I always ran into. It’s not that they didn’t have the ability to support Linux, but they didn’t want to have to learn new skills. And with Microsoft always ready to ‘throw money’ at any customer to ‘keep them,’ most of the time, all my work was just to help the customer get concessions from Microsoft.
SIDE NOTE: The most infamous of this was the London Stock Exchange (LSE), which became the ‘last bastion of Windows’ in the trading industry, where Microsoft was subsidizing the integrator, Accenture (that finally capitulated in 2008 — long story).
I cost Microsoft well into 9 figures in just 2008-2009 alone, and was on one of their lists. I.e., if I walked into a customer, it went to VP level at Microsoft. It was the added politics I had to deal with, and the more technical success I had, the worse it got for me.
This is just how the world works. As Garner put it best way back in 2000 … “No vendor will offer a way out of lock-in. Customers have to choose it.” Customers have to want to have a solution, and there are plenty of vendors who have money — and especially when non-Open Source solutions cost 10x more than Open Source — to do a lot of things for them now, so they can hold on to them later.
NCR Kalpanna runs, “Android”, shudders
If you think it’s ridiculous that XP is embedded in all these ATMs, what do you think of Minix being embedded in Intel CPUs?
https://itsfoss.com/fact-intel-minix-case/
Regarding why Windows is used, I had this discussion with both Diebold and IBM in the early ’00s. At the time, OS/2 was the dominate operating system, and both Diebold and IBM initially offered Linux-based ATMs, like much of the consumer set-top and other markets had moved to. But the overwhelming majority of regional and smaller banks wanted Windows, under the assumption it was “easier to support,” even though the devices are — essentially — blackbox appliances, and Linux was easier to service in both Diebold and IBM studies. So despite the reliability and serviceability, the regional and smaller banks dictated Windows, and wth the lack of orders, both Diebold and IBM finally dropped Linux-based ATMs.
Many banks develop their own consumer interface and mid level SW. As they dev in a MS environment, the target is most often the same.
Most just license the same kits and use the same templates from the same providers. They hardly do much development in-house.
This is what always gets me. In fact, a lot of unnecessary, wasteful and ons-off development is done to justify continued employment.
It doesn’t take any development to add a few themes and skins, and use the same APIs to common, industry trading and backend solutions.
RJ-11 and WWAN based stand-alone units have always had horrible policy and software. The software typically comes out of UK or South Asia with US based QA(really just language and UI checks).
In the early two-thousands in the US people who had inside knowledge were changing configuration on site via hidden management panels and jackpotting.
Even without software the cartridges are typically only protected by a weak steel cabinet with a plastic door that is eight pin tubular, and then a key or combo on the metal door.. No concrete or epoxy or kevlar layer on the cabinet, so anything can cut it. They typically have $3,000-$14,000. Same for EU too..
You’ll probably never see jackpotting on US bank branch site ATMs unless some insider assists. In the early two thousands Bank Of America intranet was wormed and it was revealed they use custom encrypted protocols and strong cabinet security over windows xp embedded that you have no attack surface for unless you physically break in to a data center or switch station and MITM for RCE or impersonation etc..
All, like a retail POSi, go to a gateway which goes to a processor which go to issuer. All back-ends use that same ISO with SWIFT for international..
TL;DR; It’s never branch ATMs just the cheap hand-trucked units..
It makes you wonder what they could accomplish with an endoscope behind the curtain of a Diebolt voting machine.
Many Diebold voting machines were consumer desktops, with Windows, Office and using spreadsheets with SQL connections. They were total hacks, and not true vertical (much less real DB) services.
The state of Florida wasted so much money on those systems in so many counties, only to reverse course by 2008+, and just re-install what half of the state already had back by the late ’80s … ink-scan machines.
I grew up and lived in Seminole County and it’s all we used. The ‘hanging chad’ issue in various counties was because they failed to adopt the ink-scan machines in the ’80s like we did.
We had a series is such incidents in serial hacks across ATMs in a few districts in north India
https://economictimes.indiatimes.com/industry/banking/finance/banking/sbi-atm-in-odisha-spews-out-cash-automatically-bank-suspects-malware-attacks/articleshow/58072863.cms
USB “endoscopes” (simple camera devices) are common and inexpensive, and most Android devices with OTG support them.
Paying top dollars for ATMs with a PC running Windows instead of a strengthened and customized sub-version of Unix in an embedded industrial grade critical machine of custom built hardware does tell you everything about how prepared is the traditional banking industry to make it in an environment where technology change is redefining whole industries.
http://www.bbc.com/news/av/technology-40655653/how-easy-is-it-to-hack-a-cash-machine
barnaby jack gave a talk almost a decade ago exposing this. you would think Diebold, one of the biggest atm vendors, would have heard about it. lol windows xp idiots. you get what you deserve suckers!
Why am I so unsurprised that Diebold was involved? In my opinion the company has zero interest in security.
The entire retail sphere is circling the drain anyway, these El-Cheapo ATMs getting broken into are residing in many retail establishments that are likely to be gone in 20 years, a victim of online commerce. You have to ask yourself – what type of business out there insists on taking cash and forcing their customers to use an ATM next to the cash register to get it instead of just taking a credit card. I can think of a few – strip joints, redneck bars, marijuana shops, cigarette sales shops, lottery ticket shops, tow company impound lots – the kinds of places that are essentially exploitative. And every one of these “remote ATMs” has a jacked up transaction fee with a good chunk of it going to the retailer.
I was shocked when I went to a popular restaurant in Estero FL and learned they took only cash and I had to get money from a cheesy ATM in the bar. Why are they running an all cash business? I smell tax fraud.
awww…too bad… i guess it is time for them to start earning their ungodly fees a little bit. a week’s worth of business at the corner 7-11 surely would cover a hit like this. so big deal! anyone that cries for the greedy banks and other ATM machine operators is a tool.
7-11 had all their God-awful Cardtronic machines removed in 2017.
But I have far bigger problems to worry about, with hiring illegal immigrants.
As for the big Banks and their fees, the big Banks don’t charge the ’big’ fees. It’s the little banks that do that. Or the convenience stores who are run by a bunch of shady people in the first place. ATMIA research. Get your facts straight.
Do yourself a favor and check out Barnaby Jack’s (RIP) 2010 “Jackpotting ATM” talks at BlackHat and DEFCON.
This attack, compared to Barnaby’s is really crude…
Does it matter? Style points don’t count if it works.
The point is that more sophisticated attacks lie ahead. Defcon points the way, and – over time – cyber-crime follows !
Not until the easy way doesn’t work anymore. Generic keys and windows XP. Everyone gets worked up about sophistication etc. the more sophisticated the attack the less people who can pull it off. Fix the easy stuff first then worry about more complex ways to rob the bank.
But, like the voting machine hacks, defcon shows it can be done. And shows how unsafe machines that are a local needed device, can be highjacked.
There is one man, that the feds already know of, in Springfield, federal home for wayward citizans, that had a legal ATM key. He was the brother of the big 3 in crime. Shucks, that was years ago. So, unless a network was replaced, all the Mobo checked, all the inbedded parts changed, why would anyone say the network was secure? In any country. And then now to replace with a unknown machine from a foreign country? So, is there a mob in that country? Or a unfriendly government, or or a friendly government? Should you trust that machine?
I have always wondered how Diebold voting machines are so notoriously insecure, while the atm’s seem fine. Accurately dispensing $20 bills seems more complicated than counting votes in a “democracy”.
I guess I have my answer…interesting that stolen elections are a yawn, but stolen cash gets attention.
Imagine the company who brought you the election 2000 voting machine debacle stumbling over jackpot. What a surprise.
why in usa? why eu is fraud free? we hear only in usa?
i guess too much KGB has controll in usa
What on earth gave you the idea that the EU is fraud free? Why would you even deny corruption is the norm?
“The Secret Service alert says ATMs still running on Windows XP are particularly vulnerable, and it urged ATM operators to update to a version of Windows 7 to defeat this specific type of attack.”
Windows? Seriously? For a secured system?
2018 and systems still running Windows XP in the wild… hmph, these institutions deserve to be hacked, period.
“The Secret Service alert explains that the attackers typically use an endoscope” – Is the Secret Service going through lists of possible rogue proctologists?
secret service as always is neck deep in.
it means secret service is the one who organize those things.
people offcourse dont belive this.
but that how it is.
even is u know this as the fact..then? what u gona do? nothing right?
everthing is just so corrupted anyways.
They are stealing the bank’s money for a change and not the customers money. Of course, this will motivate the ATM owner or bank to fix it very quickly.
You don’t even need physical access. Plug in to an adjacent network drop or plug in a linksys router, arp spoof the machine, and re-write the C&C messages between the ATM and the central server. Flat network and unencrypted coms, unauthenticated text based messaging protocol.
I’ve done this multiple times for various banks over the last 7 years. I’ve waned them of the dangers every time. As usual they don’t implement the recommendations because the attacks we warned about were “theoretical” even though we demonstrated them in the lab and in the field.
In Brazil the situation is much worse. The cases I saw (Working for big banks for the past decade) are envolving “hubbing” the ATM with a raspberry pi device that compromises the ATM and its neighbors. Since all ATMs in the same bank are in the same DMZ, the crook can make the malware reach hundreds of ATMs at same time. Using a r. Pi device, you can also connect a 4G modem and make the little device to call home and update. Now you have a rogue device in your network doing: atm jackpot, lateral movement, privileged credential sniffing, card clonning, PIN capture and in case the 4G stops for some reason, the crook parks his car close to the bank and update the raspberry through wi-fi. Millions have been stolen from a single bank in these attacks with phases 1, 2, 3 and 4. The malware even managed to find a port to deploy more packages to the banks office local manager (where the initial ATM was installed). Now the banks are discovering basic stuff like “yeah we need NAC or at least 802.1x on ATMs network drops”. Some banks listed more than 50 urgent actions to remediate and prevent similar attacks in the future. The code we found was partially developed in Russia and other parts in Brazil, meaning the crooks are getting good in building stuff from different “suppliers”.
Many large international banks w/ either European or US ownership decided not to move to Win7 from XP when XP support was discontinued………why? COST!
Say a branch an ATM costs $30k (dispenses cash & accepts check and cash deposits), depreciated out over 7 years…….so you replace an ATM, it cost you $30k and 18 months later you have to upgrade the ATM guts to support a new OS………say $3k for the upgrade, an 18 month old ATM “now” has a longer depreciation cycle…….but when you multiple this out on 1,000’s of ATM’s the expense becomes HUGE b/c of depreciation.
For the folks talking about voting machines, do the research Diebold bought the company that made the machines, they did not develop them……..
> “The last thing the fraudsters do before leaving the site is to plug the Ethernet cable back in,” the alert notes.
The article never talks about unplugging the Ethernet cable. Also, seems strange their needs to be a third trip to the atm after the thief steals the cash.
*there*