Fiserv, Inc., a major provider of technology services to financial institutions, just fixed a glaring weakness in its Web platform that exposed personal and financial details of countless customers across hundreds of bank Web sites, KrebsOnSecurity has learned.
Brookfield, Wisc.-based Fiserv [NASDAQ:FISV] is a Fortune 500 company with 24,000 employees and $5.7 billion in earnings last year. Its account and transaction processing systems power the Web sites for hundreds of financial institutions — mostly small community banks and credit unions. According to FedFis.com, Fiserv is by far the top bank core processor, with more than 37 percent market share.

Two weeks ago this author heard from security researcher Kristian Erik Hermansen, who said he’d discovered something curious while logged in to an account at a tiny local bank that uses Fiserv’s platform.
Hermansen had signed up to get email alerts any time a new transaction posted to his account, and he noticed the site assigned his alert a specific “event number.” Working on a hunch that these event numbers might be assigned sequentially and that other records might be available if requested directly, Hermansen requested the same page again but first edited the site’s code in his browser so that his event number was decremented by one digit.
In an instant, he could then view and edit alerts previously set up by another bank customer, and could see that customer’s email address, phone number and full bank account number.
Hermansen said a cybercriminal could abuse this access to enumerate all other accounts with activity alerts on file, and to add or delete phone numbers or email addresses to receive alerts about account transactions.
This would allow any customer of the bank to spy on the daily transaction activity of other customers, and perhaps even target customers who signed up for high minimum balance alerts (e.g., “alert me when the available balance goes below $5,000”).
“I shouldn’t be able to see this data,” Hermansen said. “Anytime you spend money that should be a private transaction between you and your bank, not available for everyone else to see.”
Hermansen said he told his bank about what he found, and that he tried unsuccessfully to get the attention of different Fiserv employees, including the company’s CEO via LinkedIn. But he wasn’t sure whether the flaw he found existed in all bank sites running on Fiserv’s ebanking platform, or just his bank’s installation.
Naturally, KrebsOnSecurity offered to help figure that out, and to get Fiserv’s attention, if warranted. Over the past week I signed up for accounts at two small local banks that each use Fiserv’s online banking platform.
In both cases I was able to replicate Hermansen’s findings and view email addresses, phone numbers, partial account numbers and alert details for other customers of each bank just by editing a single digit in a Web page request. I was relieved to find I could not use my online account access at one bank to view transaction alerts I’d set up at a different Fiserv affiliated bank.
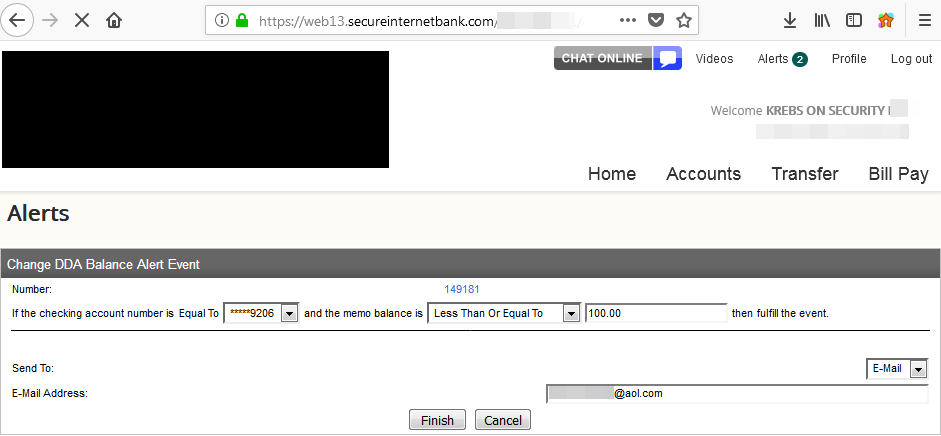
A single digit changed in a Web browser request caused someone else’s alerts to pop up in my account at this small local bank in Virginia.
But it was not difficult to find hundreds of other Fiserv-affiliated banks that would be just as vulnerable. If a bank is using Fiserv’s platform, it usually says so somewhere at the bottom of the bank’s home page. Another giveaway is that most of the bank sites using Fiserv display the same root domain name in the browser address bar after login: secureinternetbank.com.
Fiserv said in a statement that the problem stemmed from an issue with “a messaging solution available to a subset of online banking clients.” Fiserv declined to say exactly how many financial institutions may have been impacted overall. But experts tell KrebsOnSecurity that some 1,700 banks currently use Fiserv’s retail (consumer-focused) banking platform alone.
“Fiserv places a high priority on security, and we have responded accordingly,” Fiserv spokesperson Ann Cave said. “After receiving your email, we promptly engaged appropriate resources and worked around the clock to research and remediate the situation. We developed a security patch within 24 hours of receiving notification and deployed the patch to clients that utilize a hosted version of the solution. We will be deploying the patch this evening to clients that utilize an in-house version of the solution.”
This author confirmed that Fiserv no longer shows a sequential event number in their banking sites and has replaced them with a pseudo-random string.
Julie Conroy, research director with market analyst firm Aite Group, said the kinds of banks that use Fiserv’s platform mostly are those that can’t afford to build and maintain their own.
“These financial institutions use a core banking provider like Fiserv because they don’t have the wherewithal to do it on their own, so they’re really trusting Fiserv to do this on their behalf,” Conroy said. “This will not only reflect on Fiserv’s brand, but also it will impact customer’s perception about their small local bank, which is already struggling to compete with the larger, nationwide institutions.”
Allen Weinberg, partner and co-founder at Glenbrook Partners LLC, said the ability of fraudsters to edit account transaction alerts somewhat negates the value of these alerts in helping consumers fight fraud tied to their online banking accounts.
“If a fraudster can just turn off the alerts, there’s one less protection that consumers think they have,” Weinberg said. “I think consumers do rely in large part on these alerts to help them detect fraudulent activity.”
The weaknesses in Fiserv’s platform is what’s known as an “information disclosure” vulnerability. While these are among the most common types of security issues with Web sites, they are also perhaps the most preventable and easily fixed.
Nevertheless, disclosure flaws can be just as damaging to a company’s brand as other more severe types of security errors. Other notable security incidents involving recent information disclosure issues include a weakness at Panera Bread’s site that exposed tens of millions of customer records, and a bug in identity protection service LifeLock’s site that revealed email addresses for millions of customers.
Update, 12:22 p.m. ET: Updated the second paragraph to include a link to information about Fiserv’s #1 market share. Also updated the story to reflect screen shots shared with KrebsOnSecurity indicating Hermansen was able to see full customer account numbers in his bank’s implementation of Fiserv’s platform. The account numbers I saw in both Virginia banks used in my testing were truncated to the last four digits.




You people in usa dont you get sick of this scams frauds and cortuption ??
Why you.people in usa accepting this ??
Its just grazy i think i how much fraud and scams are in usa !!
And you peole dont do nothing ? Just accepting this nonsesne
dont you get sick of this scams frauds and cortuption ??
Yes, which is why we arrest people.
Why you.people in usa accepting this ??
We don’t, we fix these things, see it’s fixed now.
Its just grazy i think i how much fraud and scams are in usa !!
LOL, you should see what they deal with in India, EU, Russia and Brazil, Fraud is a global thing, and we don’t have the worst of it. We make it better all the time.
And you peole dont do nothing ? Just accepting this nonsense
No, we do things, see above.
Do you do programing? Can you rewrite all FI software so there are no bugs and never needs updating? you should do that..
+1
Uk use to be number one country.
But now the soca stopped uk is safe.
Banking trojans even not wroking over uk.
But people in criminal world target usa, always the list is endlrss…like romance scams, banking trojans, ceo frauds, even stock frauds.
Usa credit cards are still without chip so who to blame for this?
Look in eu cards have chips, and no frauds.
My opinion is simple, if govermemt want they can stop this fraud right to way.
We are not even talk about bitcoin or other type of cryptocurrency related frauds are going on in usa.
Simlply usa goverment going the way tonot stop fraud but they rather hiring security compnaies who will just sell to people all this fear like homeland security, and endless computer protection softwares.
It is much more cheaper to prevent fraud happening first place !
Something here dosnt make sense at all.
And you got no idea what you talking, if you steal in russia or scam some company out of money then the company ceo will kill you and thats it.
Over here not some alice wonderland russia and europe is not cartoon land its real life real people
Well, “Tom”, fraud, scams, and corruption run rampant throughout the world. You are a fool if you believe this does not happen anywhere else in the world. No matter what program is used, where it used, or how it used, there is always a risk of compromise in some way.
For example, Japan reported over 6,000 cyber related incidents in 2017, Vietnam, China, Russia, England, France, and so on all have the same problems Americans do.
I urge you to do a little more research before making a claim that will be torn down. It is plain ignorant to assume America is the only country where this happens.
Indeed mate, the situation in US of A is horrible. They’re all so hooked on saving a buck, they’ll do anything but are too thick to realise that in the end they’re just wasting money. Instead of only taking holydays on ‘the old continent’ they’d better learn some bussiness practices from them.
You forgot the word USA in last sentence.
I work for a Bank that uses Fiserv as our Core Provider and hosts the Bank’s online banking. The Fiserv application with the vulnerability is called “Event Manager”. Coincidentally, Fiserv presented our Bank recently with a “brand new” version on event manager with a different name… Fiserv dud not notify our bank of this previous vulnerability either.
Better core processor that cares with latest technology give us a call
This is why I read your site every morning.
Fortunately for our FI we don’t provide customer data to them. However being dependent on companies like this is one of my biggest concerns. We run a very tight ship, and although we do have reports and audits of our vendors like this, it is still a major concern to me. Every vendor is a risk, the more vendors the more risk. I get frustrated when management thinks going to “cloud infrastructure” is safer than in house. I know what we have in house, we can watch and manage all data. I have no control over cloud vendors, which is usually dependent on multiple vendors themselves. Sure we have insurance, but insurance won’t protect your reputation if your customers data is exposed. Can hardly wait to retire,,,,,
My point exactly!
The SVP CIO of Bank Solutions at fiserv Keith Fulton posted this about the incident on their slack site. Was given a screenshot of it. “ I should clarify that the article is written for drama and effect. Our version of the same event would be much drier and make it (accurately) seem much smaller than what krebs does here.
I gave Fiserv every opportunity over several days to answer my questions about the scope of this issue, and they declined to respond to any of those questions. All I can do is outline the size of the potential problem and include their statement. If the company wants to share more details, I’m happy to update the story.
Do not doubt you. He doesn’t understand that information disclosure are not insignificant. This information can be used for phishing or social engineering attacks. I wonder what would happen if you used that information calling a banks vru or help line. The we have with tech companies hiring CIO who do not know how to do there job.
C level execs always downplay the impact of major events. Its what they do. They will never tell you how severe an event really is, ever. They have shareholders to think of and customers to keep calm.
The article implies that only smaller banks use Fiserv products. However, Fiserv’s customer list includes Bank of America, Bank United, Capitol One, Charter Financial, Citigroup, Mastercard Inc., Morgan Stanley, Toyota Motor Credit Corp., United Bankshares, USBank, Visa, Wells Fargo, and many more. No way of knowing who uses this particular product.
FiServ likely serves almost all banks, with at least 1 of their products. This article focuses on the banks that use their online banking/alerting platform. Smaller banks often use that, because there is no way they have the resources to develop and maintain a complex banking website.
For the big banks that you mentioned, they almost assuredly do have their own development teams, and likely use custom code/websites (not the Fiserve platform). But some of the other FiServ products? It’s a very strong possibility they use those.
I work with many of these banking vendors on a daily basis in an IT capacity. There are many other banking vendors out there, Fiserv is certainly one of the larger ones though. From experience I would say Fiserv is probably one of the more secure vendors out of the lot though. There are a couple smaller ones that come to mind whose security is shockingly bad, or nearly non-existent.
From the release notes of version 1.5 of Premier Messenger Module (aka Event Manager, the module with the flaw)…
Premier Messenger Module User Interface (PMM1171)
We have updated the program to not allow the user to modify the globally unique identifier (GUID) reference number that the program attaches to an account. This ensures that the user does not obtain information for which they do not have access.(1.5.1.1)
This was an update published in 2016. Either the release notes describe a different issue than was discovered in the last few weeks, or the issue was known and said to be fixed, but not actually fixed 2 years ago.
The article is misleading in identifying ‘hundreds of banks’ that could be just as vulnerable. Just because a site is hosted on a Fiserv server does not mean that the bank is running Event Manager, and even if they are, it doesn’t mean they decided to forego best practices and configure their alerts to display unmasked account numbers and other unnecessary information. Event Manager is essentially at end of life, and has been replaced with a product called Notifi. I don’t know how many banks are actually still even running it, but the bank I work for was contacted well over a year ago to let us know that it was being sunset and we have since implemented Notifi for alerts. So, yeah, we are on that server, but no, we aren’t ‘just as vulnerable’.
It’s not misleading at all. Fiserv could say exactly how many banks this impact(ed) if they wanted to. They chose not to provide that requested information.
I don’t know how many banks Brian tried to setup an account at, sounds like it was 2 for 2. Two banks attempted, both banks had the vulnerability.
On a hosted solution, bank customers don’t have the option to not update – as the Fiserv announcement says. So lacking a more complete comment from Fiserv, sounds like ALL hosted customers had this vulnerability for awhile (two years?).
As I understand it, both hosted and in-house clients that run Event Manager (a transaction alert product that is separate from online banking) are affected by the vulnerability. The degree of information at risk of disclosure depends on how the alerts are configured (masked vs. unmasked, included fields, etc). It is not clear whether the vulnerability is in a particular version of EM, or is present in all versions. Banks that don’t run EM don’t have this vulnerability.
It’d be nice if Fiserv would clarify, but I’m not holding my breath.
Has it occurred to anyone else that this company misspelled its name? Left some letters out? Just sayin.
Interesting digression: Milwaukee just opened a new basketball arena for its NBA Team, The Bucks.
The name of the stadium: Fiserv Forum.
https://www.nba.com/bucks/video/2018/08/28/2235149/1535481517409-180828-Block-Party-Recap—Klements-2235149
Based on Fiserv’s demonstrated approach to security, I suspect the arena and ticket holder db will be hacked up, down, left and right. If you ever have the misfortune to be in Wisconsin and go to Fiserv Forum, make sure to pay cash for your ticket and food.
Fiserv and Wisconsin are perfect for each other.
Interesting to know though general expectation is that such flaws should be captured during the various testing phases before implementing the solution. Also somehow couldn’t be satisfied with pseudorandom id generation alone as a solution, a hacker is not going to stop in one attempt and who knows might be using algos to generate numbers.. I am not going purely technical, and logically feel, isn’t there any other way to share the alert id (eg only to customer’s regd email or phone?).
I just wanted to clarify the type of vulnerability. This is know as Insecure Direct Object Reference (IDOR)
https://www.owasp.org/index.php/Testing_for_Insecure_Direct_Object_References_(OTG-AUTHZ-004)
or CWE-639: Authorization Bypass Through User-Controlled Key https://cwe.mitre.org/data/definitions/639.html
IDOR is when you can modify data. Information disclosure is when you can only read them. You can guess which is more critical.
And changing to a psuedo-random string helps but it is NOT the correct/total fix.
+1
All URLs should be considered public, if a URL isn’t associated with an account, its data shouldn’t be returned…
If a user isn’t authenticated, then before returning data, the user should be forced to authenticate…
Hello, Also somehow couldn’t be satisfied with pseudorandom id generation alone as a solution, a hacker is not going to stop in one attempt and who knows might be using algos to generate numbers.. I am not going purely technical, and logically feel, isn’t there any other way to share the alert id (eg only to customer’s regd email or phone?).
Banks need to focus on moving away from the legacy multi tenant architecture to a single tenant with managed services. The risk for the smaller community banks – they don’t have the security expertise and the cost of the single tenant is 2 to 3 times higher, however if they have a data breach the repetition risk, or a run on the bank ,can wipe them out. GDPR compliance and banks that use multi tenant are at higher for non compliance. To the point of cost over risk, most all online banking platforms for smaller community banks and credit unions are multi tenant.
There isn’t a single “Fiserv Platform”, they are a big company and have acquired many other similar companies over the years, each giving them at least one new product and sometimes entire suites or entire bank platforms with existing market share, etc. Not every Fiserv serviced bank is going to be vulnerable, it really depends what platform suite is vulnerable to this and the list banks on that specific platform.
Didn’t Auernheimer do exactly what you two just did?
Yowza.
Bharani
“information disclosure” . I love the short-hand IDOR. (indirect obect reference).
I wonder if it was in a cookie? Hopefully not in the URL.
At what point does the company have a fiduciary duty/regulatory requirement to relay this breach to the public? Next earnings report?
A incredible variety of all of our Pocket T-cheap ttee shiets custom [4r.gamethuhn.vn].